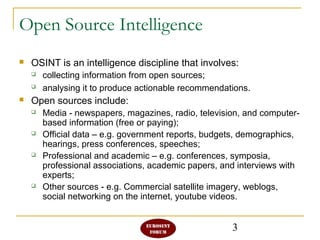
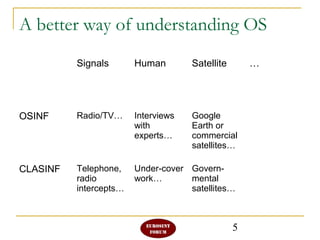
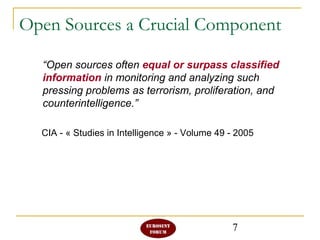
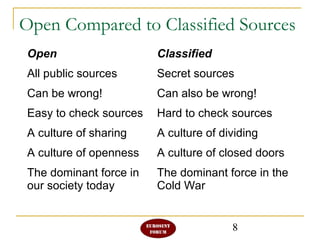
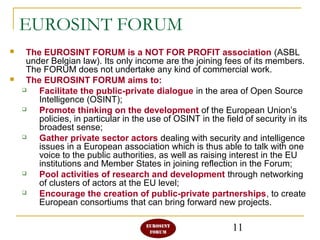
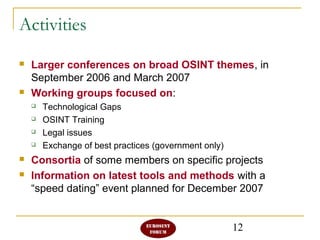
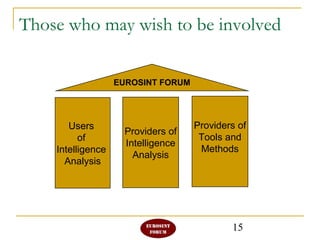
The Eurosint Forum is a non-profit association focused on promoting open source intelligence (OSINT) and facilitating dialogue between public and private sectors regarding its use in security. OSINT involves gathering and analyzing information from publicly accessible sources to provide actionable recommendations, and the forum aims to enhance EU policy development and foster public-private partnerships. Activities include conferences, working groups on various topics, and collaboration among members such as law enforcement and research institutions.