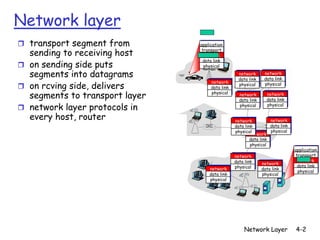
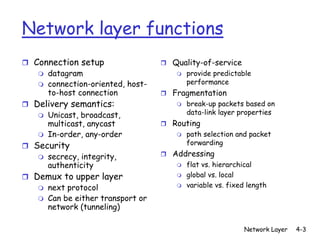
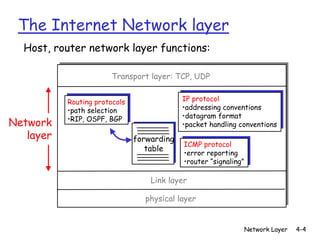
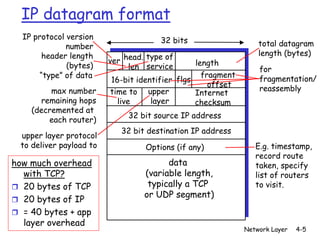
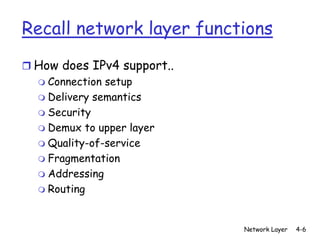
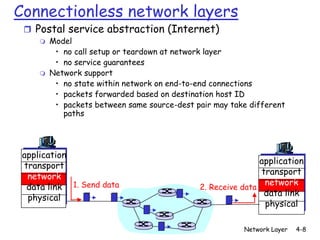
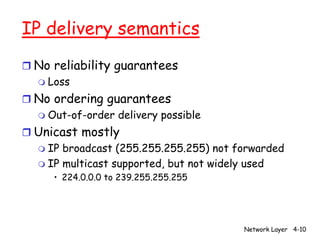
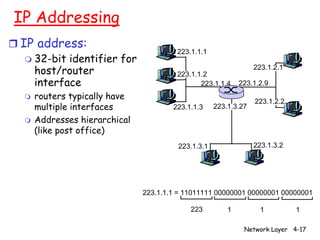
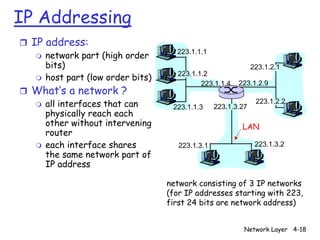
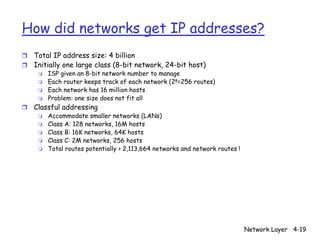
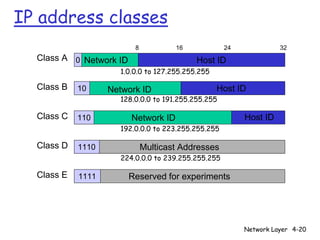
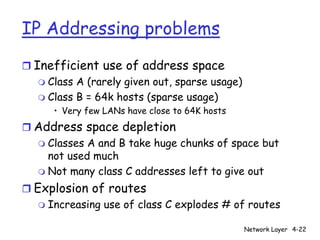
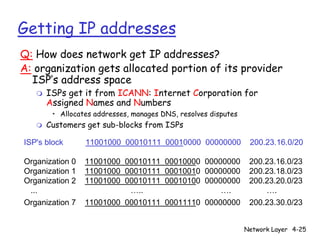
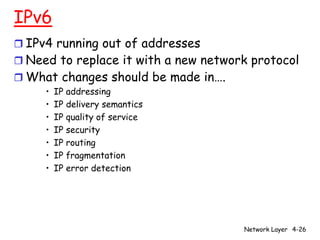
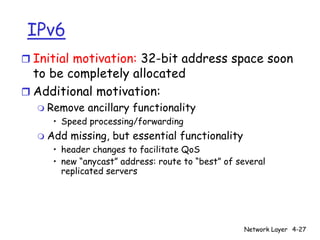
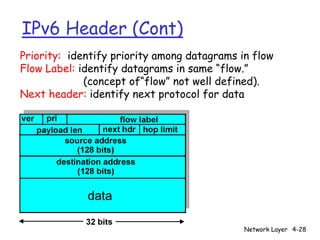
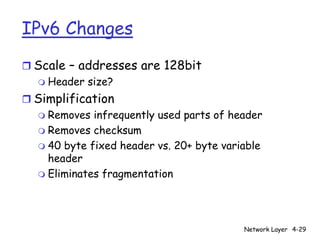
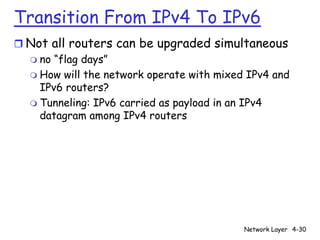
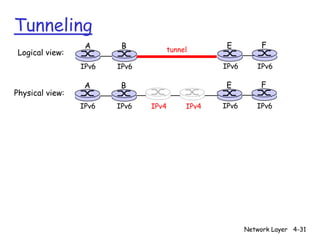
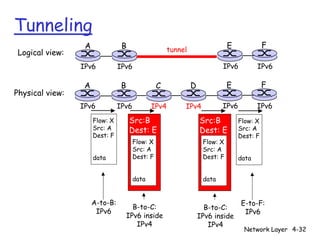
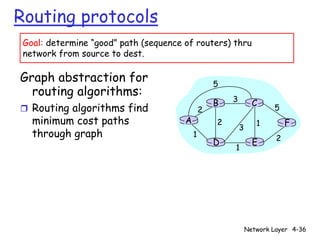
The network layer is responsible for transporting data between hosts on different networks. It handles tasks like addressing, routing, fragmentation, and quality of service. The main network layer protocol is IP, which uses addresses and routing to deliver packets in an unreliable, connectionless manner. IPv6 was created to replace IPv4 due to its limited address space and remove unnecessary features to simplify processing. During the transition, IPv6 can be tunneled inside IPv4 packets to allow communication between IPv6 and IPv4 networks.