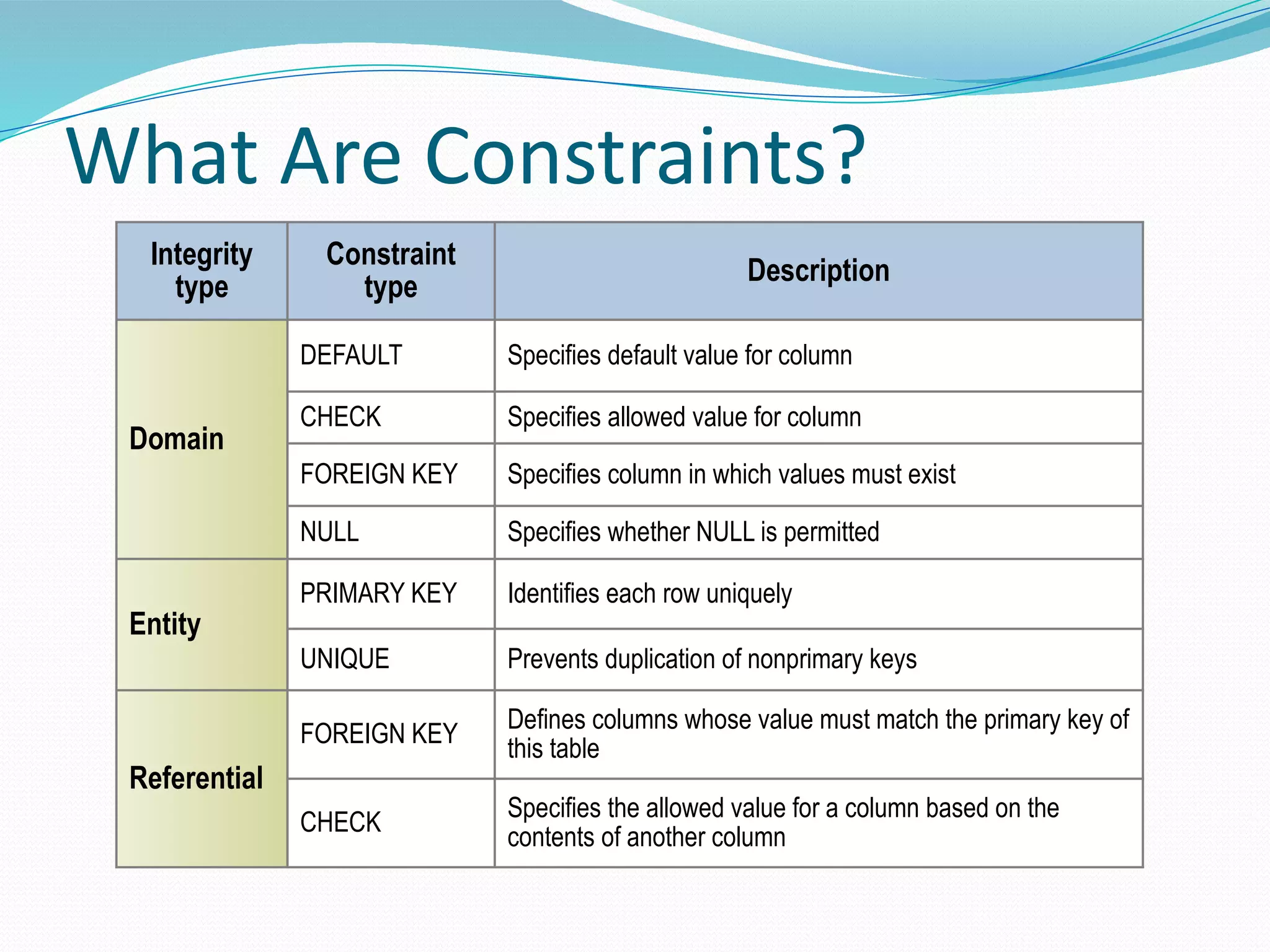
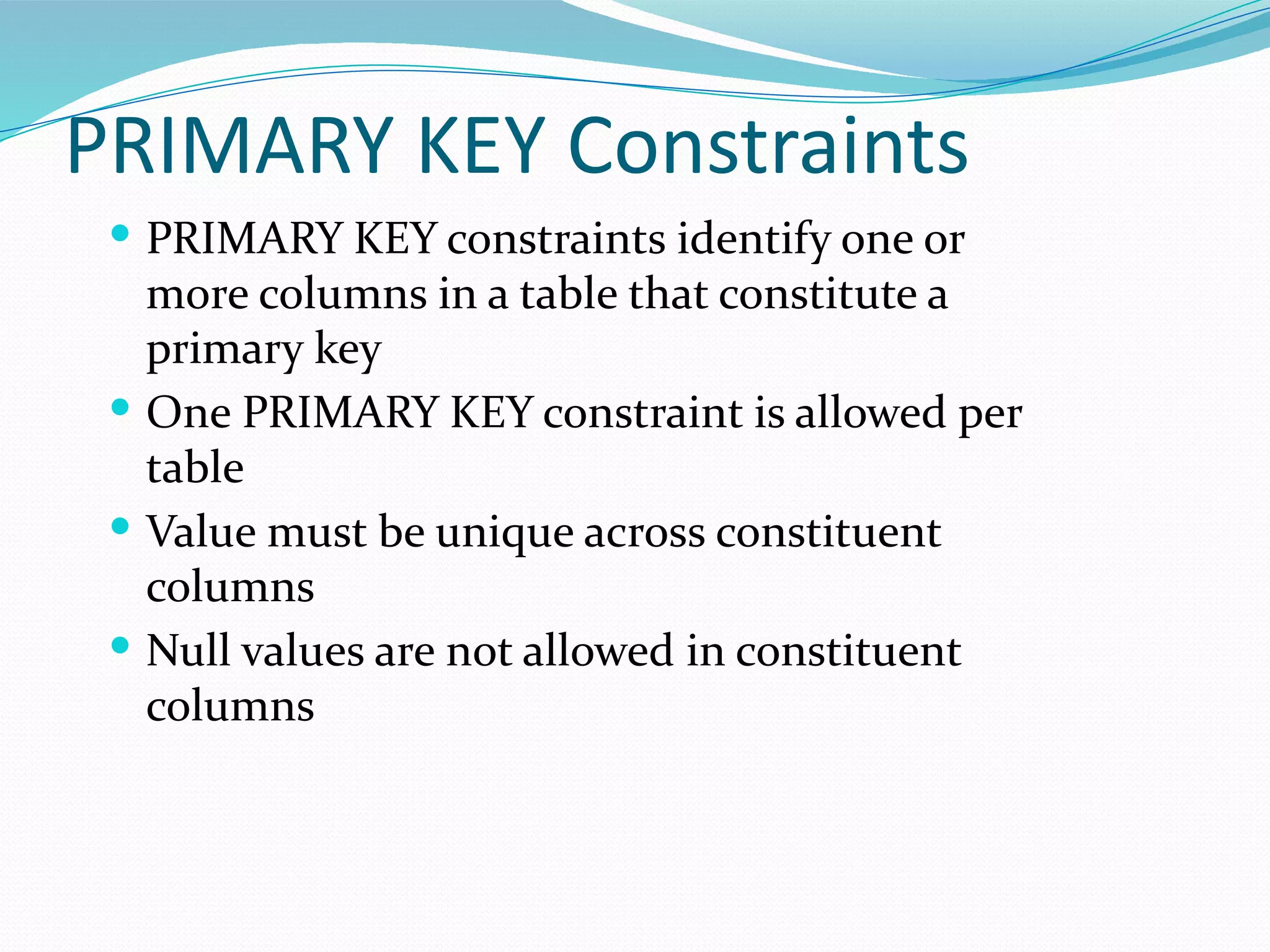
The document discusses various types of constraints in Microsoft SQL Server, including domain integrity, entity integrity, and referential integrity. It details different constraint types such as primary key, unique, default, check, and foreign key constraints, emphasizing their purposes and applications in database design. Additionally, it covers considerations for constraint management, including naming conventions, performance optimization, and alternative data integrity methods like triggers.
![Constraint Scope
CREATE TABLE [dbo].[Customers] (
[CustomerID] [int] IDENTITY (1, 1) NOT NULL PRIMARY KEY ,
[CustomerEmail] [varchar] (30) NULL ,
[CustomerState] [varchar] (5) NULL
) ON [PRIMARY]
GO
ALTER TABLE [dbo].[Products] ADD
CONSTRAINT [PK_Products] PRIMARY KEY CLUSTERED
(
[ProductID],
[ProductName]
) ON [PRIMARY]
GO
• Column Level
• Table Level](https://image.slidesharecdn.com/03constraints-last-221215095630-c0346e2d/75/03Constraints-last-pdf-4-2048.jpg)
![PRIMARY KEY Constraints
CREATE TABLE [dbo].[DEPARTMENTS](
[DNO] [int] IDENTITY(1,1) PRIMARY KEY,
[DNAME] [nvarchar](20) NULL
) ON [PRIMARY]
CREATE TABLE [HumanResources].[Department](
[DepartmentID] [smallint] IDENTITY(1,1) NOT NULL,
[Name] [dbo].[Name],
…
CONSTRAINT [PK_Department_DepartmentID] PRIMARY KEY CLUSTERED
([DepartmentID] ASC) WITH (IGNORE_DUP_KEY = OFF) ON
[PRIMARY]
)](https://image.slidesharecdn.com/03constraints-last-221215095630-c0346e2d/75/03Constraints-last-pdf-6-2048.jpg)
![Default Constraints
DEFAULT constraints define a default column
value when no value is provided
Only one DEFAULT constraint per column
Only applicable to INSERT statements
Some system supplied functions allowed
CREATE TABLE [Production].[Location](
...
[Availability] [decimal](8, 2) NOT NULL CONSTRAINT
[DF_Location_Availability] DEFAULT (0.00),
[ModifiedDate] [datetime] NOT NULL CONSTRAINT
[DF_Location_ModifiedDate] DEFAULT (getdate())
)](https://image.slidesharecdn.com/03constraints-last-221215095630-c0346e2d/75/03Constraints-last-pdf-7-2048.jpg)
![Check Constraints
CHECK constraints restrict the values that can
be entered into a column on INSERT or
UPDATE.
Can define multiple CHECK constraints per
column.
Can reference columns in the same table.
Cannot contain subqueries.
ALTER TABLE [HumanResources].[EmployeeDepartmentHistory]
WITH CHECK
ADD CONSTRAINT [CK_EmployeeDepartmentHistory_EndDate] CHECK
(([EndDate]>=[StartDate] OR [EndDate] IS NULL))](https://image.slidesharecdn.com/03constraints-last-221215095630-c0346e2d/75/03Constraints-last-pdf-8-2048.jpg)
![Disabling Constraints
Bad Data During Constraint Creation?
ALTER TABLE [dbo].[Products]
WITH NOCHECK
ADD CONSTRAINT [CK_Products_No_Nissan]
CHECK ([Productname] <> 'nissan sentra')
Temporarily During Data Load
ALTER TABLE Products
NOCHECK
CONSTRAINT CK_Products_No_Nissan](https://image.slidesharecdn.com/03constraints-last-221215095630-c0346e2d/75/03Constraints-last-pdf-9-2048.jpg)
![UNIQUE Constraint
UNIQUE constraints ensure that every value in a
column is unique
Only one null value allowed in a unique column
Can include one or more columns
CREATE TABLE [HumanResources].[Employee](
[EmployeeID] [int] IDENTITY(1,1) NOT NULL,
[NationalIDNumber] [nvarchar](15) NOT NULL UNIQUE
NONCLUSTERED,
…
)](https://image.slidesharecdn.com/03constraints-last-221215095630-c0346e2d/75/03Constraints-last-pdf-10-2048.jpg)
![FOREIGN KEY Constraints
FOREIGN KEY constraints ensure referential
integrity between columns in same or
different tables
Must reference a PRIMARY KEY or UNIQUE
constraint
User must have REFERENCES permission on
referenced table
ALTER TABLE [Sales].[SalesOrderHeader] WITH CHECK
ADD CONSTRAINT
[FK_SalesOrderHeader_Customer_CustomerID]
FOREIGN KEY([CustomerID])
REFERENCES [Sales].[Customer] ([CustomerID])](https://image.slidesharecdn.com/03constraints-last-221215095630-c0346e2d/75/03Constraints-last-pdf-11-2048.jpg)