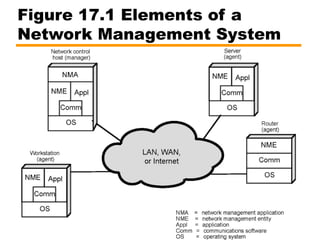
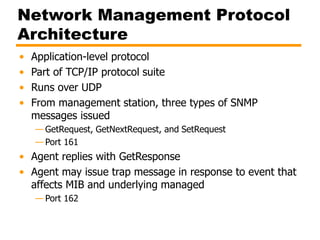
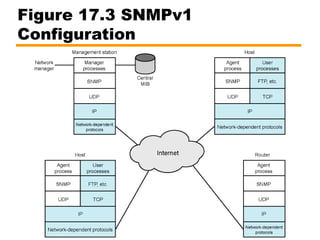
This document provides an overview of network management and the Simple Network Management Protocol (SNMP). It discusses the key elements of network management including fault, accounting, configuration, performance, and security management. It also describes the components of SNMP including the management station, agent, management information base (MIB), and SNMP versions 1, 2, and 3. SNMP allows a network administrator to monitor and control network devices, configure devices, and review performance and security statistics to manage the network.