Effective Vulnerabilities Management in Simple Ten Steps
•Download as PPTX, PDF•
0 likes•21 views
Effective Vulnerabilities Management in Simple Ten Steps
Report
Share
Report
Share
Recommended
More Related Content
What's hot
What's hot (20)
OSB160: Trust Your Apps. See How with Ivanti Application Control

OSB160: Trust Your Apps. See How with Ivanti Application Control
Enemy from Within: Managing and Controlling Access

Enemy from Within: Managing and Controlling Access
Dronesafe™ Flyer - Simply connect, stream and comply

Dronesafe™ Flyer - Simply connect, stream and comply
The Role of Application Control in a Zero-Day Reality

The Role of Application Control in a Zero-Day Reality
Cybersecurity Best Practices for 3rd Party Supply Chain

Cybersecurity Best Practices for 3rd Party Supply Chain
How to cure yourself of antivirus side effects @ReveeliumBlog

How to cure yourself of antivirus side effects @ReveeliumBlog
It's Your Move: The Changing Game of Endpoint Security

It's Your Move: The Changing Game of Endpoint Security
10 Steps to Building an Effective Vulnerability Management Program

10 Steps to Building an Effective Vulnerability Management Program
201512 - Vulnerability Management -PCI Best Practices - stepbystep

201512 - Vulnerability Management -PCI Best Practices - stepbystep
Web Application Security Vulnerability Management Framework

Web Application Security Vulnerability Management Framework
Viewers also liked
Viewers also liked (17)
Criterios de resecabilidad de las metástasis hepáticas - Cáncer digestivo

Criterios de resecabilidad de las metástasis hepáticas - Cáncer digestivo
Rol del Ministerio de Agricultura en el registro de Indicaciones Geográficas ...

Rol del Ministerio de Agricultura en el registro de Indicaciones Geográficas ...
Similar to Effective Vulnerabilities Management in Simple Ten Steps
Similar to Effective Vulnerabilities Management in Simple Ten Steps (20)
Insightful Research: The State of Mobile Application Insecurity 

Insightful Research: The State of Mobile Application Insecurity
IMPAKT: Verdediging aangaan t.o.v. (on)bekende ransomware:

IMPAKT: Verdediging aangaan t.o.v. (on)bekende ransomware:
State of Web Application Security by Ponemon Institute

State of Web Application Security by Ponemon Institute
Intelligence on the Intractable Problem of Software Security

Intelligence on the Intractable Problem of Software Security
SANS 2013 Critical Security Controls Survey Moving From A.docx

SANS 2013 Critical Security Controls Survey Moving From A.docx
Why Patch Management is Still the Best First Line of Defense

Why Patch Management is Still the Best First Line of Defense
Edgescan vulnerability stats report 2019 - h-isac-2-2-2019

Edgescan vulnerability stats report 2019 - h-isac-2-2-2019
Recently uploaded
Recently uploaded (20)
Kotlin Multiplatform & Compose Multiplatform - Starter kit for pragmatics

Kotlin Multiplatform & Compose Multiplatform - Starter kit for pragmatics
FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi

FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi
Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation

Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation
Designing IA for AI - Information Architecture Conference 2024

Designing IA for AI - Information Architecture Conference 2024
SQL Database Design For Developers at php[tek] 2024![SQL Database Design For Developers at php[tek] 2024](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![SQL Database Design For Developers at php[tek] 2024](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
SQL Database Design For Developers at php[tek] 2024
Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365

Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365
Breaking the Kubernetes Kill Chain: Host Path Mount

Breaking the Kubernetes Kill Chain: Host Path Mount
The Codex of Business Writing Software for Real-World Solutions 2.pptx

The Codex of Business Writing Software for Real-World Solutions 2.pptx
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
"LLMs for Python Engineers: Advanced Data Analysis and Semantic Kernel",Oleks...

"LLMs for Python Engineers: Advanced Data Analysis and Semantic Kernel",Oleks...
New from BookNet Canada for 2024: BNC BiblioShare - Tech Forum 2024

New from BookNet Canada for 2024: BNC BiblioShare - Tech Forum 2024
Unlocking the Potential of the Cloud for IBM Power Systems

Unlocking the Potential of the Cloud for IBM Power Systems
Effective Vulnerabilities Management in Simple Ten Steps
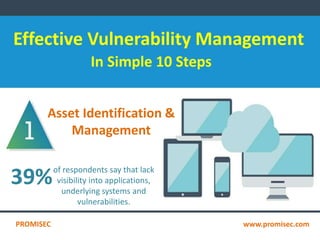
- 1. Effective Vulnerability Management In Simple 10 Steps Asset Identification & Management 39%of respondents say that lack visibility into applications, underlying systems and vulnerabilities. PROMISEC www.promisec.com
- 2. Vulnerability Identification of the 15,435 vulnerabilities discovered in 2014, 11% were reated "Highly Critical" and just 0.3% as "Extremely Critical" Consistent Vulnerability Management Less Than 40% of organizations their entire network with active vulnerability scan more than once per quarter. PROMISEC www.promisec.com
- 3. Risk Management Risk management are used to identity, estimate, and prioritize risk to organizations. Change Management 60% of incidents can be attributed to errors by system administrators and other internal staff. PROMISEC www.promisec.com
- 4. Patch Management 99.9% of the exploited vulnerabilities had been compromised more than a year the associated CVE(Common Vulnerabilities and Exposure) was published. Mobile Device Management of respondents believe their mobile endpoints have been the target of malware over the past 12 months. PROMISEC www.promisec.com
- 5. Mitigation Management Secunia recorded 15,435 software vulnerabilities in 3870 applications during 2014 a 55% increase in the five trend an 18% increase from 2013. PROMISEC www.promisec.com
- 6. Incident Response 1 out of 5 Security Operations Centres are not minimally prepared to respond to, much less detect, cyber threats affecting their organization. Automation 33% of respondent organizations manually remediate infected hosts- an approach which carries with an increased "time of exposure" and, therefore, increased potential for data theft and other forms of damage. PROMISEC www.promisec.com
