ENMG 602 Homework Assignment 1 Problem 1 Observation.docx
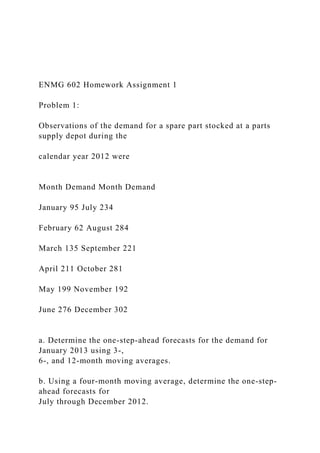
- 1. ENMG 602 Homework Assignment 1 Problem 1: Observations of the demand for a spare part stocked at a parts supply depot during the calendar year 2012 were Month Demand Month Demand January 95 July 234 February 62 August 284 March 135 September 221 April 211 October 281 May 199 November 192 June 276 December 302 a. Determine the one-step-ahead forecasts for the demand for January 2013 using 3-, 6-, and 12-month moving averages. b. Using a four-month moving average, determine the one-step- ahead forecasts for July through December 2012.
- 2. c. Compute MAD, MSE, MAPE for the forecasts obtained in b. Problem 2: Observed weekly sales of ball peen hammers at the town hardware store over a ten-week period have been 13, 11, 26, 21, 32, 13, 21, 22, 30, and 26. a. Suppose that five-week moving averages are used to forecast sales. Determine the one-step-ahead forecasts for weeks 6 through 10. b. Suppose that exponential smoothing is used with a smoothing constant of α = 0.15. Find the exponential smoothing forecasts for weeks 6 through 10 (start the forecasting process from week 1). c. Based on the MAD, which forecast method is better? Problem 3: The sales of a tablet computer in a popular electronic store during the calendar year 2012 were Month Demand Month Demand
- 3. January 103 July 199 February 119 August 208 March 131 September 221 April 149 October 237 May 172 November 252 June 184 December 268 a. Using 3-month simple moving average and exponential smoothing (with α = 0.10 and 0.20), determine the one-step-ahead forecasts for July 2012 through January 2013. ENMG 602 Homework Assignment 1 b. Using 3-month double moving average (using base level and trend), determine the one-step-ahead forecasts for July 2012 through January 2013. c. Compute MAD, MSE, and MAPE for the above forecasts. d. Based on the MAPE, which forecast method is the best? Problem 4:
- 4. Compile a list of major system life-cycle activities. For each activity on the list, try to find the related supply chain activities. Present your finding in a table with the system life-cycle stage in the first column, system life-cycle activities in the second column and the related supply chain activities in the third column. CYBER SECURITY IN E-BUSINESS 1 CYBER SECURITY IN E-BUSINESS 2 Cyber Security in E-Business Abstract Technological advancement has resulted in the significant simplicity of carrying out activities and processes in many areas. The business world has attained a significant benefit from this advancement. Through it, e-businesses have emerged, where individuals and organizations can electronically carry out business activities, thus without the need to be physically present at the point and time of transacting. According to Furnell (2004), e-business refers to a model of doing business or a segment of a larger model that allows commercial transactions to be undertaken throughout an electronic network
- 5. such as the Internet. A major challenge is, however, facing electronic business entities, where the majority of them are facing network insecurity (Furnell, 2004). Through these insecurities, business organizations and individuals lose significant amounts of money to highly skilled but ill- intentioned individuals who manage to hack into the networks and attain unauthorized access to business and individual resources. This paper evaluates the issue of insecurity within the e-business world and provides effective methods through which these issues can be resolved. Introduction Statement of the problem Despite the fact that e-businesses possess numerous opportunities for growth and development, convenience, and simplicity, there is increased security concerns and risks involved. With the increased pool of users and interested parties, the need for information protection is even more amplified. Cybercriminals pose an immeasurable threat to online business space. Threats to e-business are largely multi- faceted and are largely manifested as privacy and confidentiality, integrity and non-repudiation, authenticity, access control, cost and availability (Scott, 2004). E-businesses are faced with the complex challenge of protecting details of their customers from unauthorized access as well as security in transmission and storage. Cybercriminals are continuously exploring means and ways of executing credit card theft and information mining. It is therefore imperative that personal and confidential information from customers remain secured and accessible to only authorized personnel. Another major security concern for e-business platforms is authenticity. With millions of Internet users worldwide e-business risk identity theft and malicious presence with an aim of gaining a
- 6. financial advantage or causing havoc. E-commerce participants are therefore needed to establish that a person is who the real claim to be, (Lowry et.al, 2001). Definition of terms The following provides the description of the main terms used in the study for better understanding of the research i. E-business - a model of doing business or a segment of a larger model that allows commercial transactions to be undertaken throughout an electronic network such as the Internet. ii. E-commerce - refer to buying and selling of goods and services via an electronic network. iii. Cybercrime - refers to criminal activities that are carried out through the utilization of computer networks with or without the inclusion of the internet. iv. Spoofing – it refers to a form of hoax or trick, which hackers utilize to trick the system and gain unauthorized access. v. Data mining – refers to the process through which individuals examine data and manage to generate new information from the data. vi. Credit card fraud – refers to criminal activities where a credit card of an individual is accessed without his or her authorization and utilized to steal money from that individual. vii. Encryption – Refers to the process of encoding a message or some information to ensure that only individuals who are authorized can gain access. viii. Cybersecurity – refers to the protection of systems that are internet connected to prevent access from individuals that are not authorized ix. Hacker - refers to a skilled computer expert who utilizes his or her knowledge to overcome or cause a problem in a computer network. Methodology
- 7. The research study is mainly based on obtaining data from primary sources regarding the issue of carrying out business activities electronically or other topics related to the topic of e- businesses and cybersecurity, analyzing the data and utilizing it to prepare a study and research results on this topic. The research study analysis involves the evaluation of the results obtained by different researchers and using their findings to compile a comprehensive explanation on the issue of e- commerce state of insecurity and effective methods and means that can be utilized to effectively succeed in The significance of the study E-business is gradually turning out to be an integral part of businesses process and operations. Almost every business today has some form of e-business undertaking ranging from complex web systems and application to simple social networking. Studies estimate that the e-commerce industry is currently worth upwards of $2 trillion. With such humongous capital and transaction outlay, it is imperative that we take a concerted effort in ensuring e-business security is at its premium. Failures to do so may lead to catastrophic losses and outages of general and critical services for the general population. Body Technology adaptation in e-businesses E-businesses are based on technology. Without the current technological advancement, e-businesses would not exist. It is for this reason that electronic businesses recently emerged in the late 19th century when the internet became applicable in the business world and most people attained devices that could provide them with internet access. Over time, gradual changes have occurred with most improvements making it extremely easy for individuals and organizations to carry out business
- 8. activities easily despite being physically in different geographical regions. Business activities have thus increased their reliability to technology. Currently, some business organizations simply cannot exist without technology. A good example is a business organization like Facebook, which is currently one of the largest companies in the world. Such a business entirely relies on technology and the need for people to socialize with others. Many other businesses offer services and manufactured products but completely rely on technology to carry out their services smoothly (Velmurugan, 2009). Technology has thus provided businesses with significant capabilities, which have provided them with a significant competitive advantage compared to their competitors who may not be using the technology. In the first stage of establishing a business organization, businesses use technology to establish effective business plans and carry out research to determine the viability of their plans. After the business has been established, technology is also utilized to help in the recruitment plans for the business employees. The organization then automates its manufacturing or service providing process, still using technology. In the marketing section, technology plays a major role in helping business organizations manage to reach their targeted customers and inform them, of the products and services that they are offering and the means through which those products will provide value for them. The organizations then still use technology to transact with the customers in the section on e- commerce. With this understanding, technology is completely implemented and adapted to the business world, from the stage where a business is established to the point where it makes sales of its products to the customers. The more effectively a business manages to take advantage of technology, the more capable the business organization becomes in gaining profits (Smith, & Rupp, 2002). In the e-business section, business organizations make it
- 9. possible for clients to make purchases of products through the internet without having to physically visit an organizational store. Many businesses have currently adopted this model of doing business. Different types of payment methods are used to transact through the internet. A number of significantly large organizations have attained their current status and rank from carrying out business through this strategy. A good example includes organizations like e-bay, Alibaba, and Amazon. Amazon is currently a large organization that operates worldwide. The organization began with the utilization of the store method where it sold books from its stores among other products. As technology was advancing, the organization also kept implementing the technological advancements to its operations. Currently, the organization makes most of its sales through the internet. The organization has a complex website, where customers can explore the products that it offers and then using the website to make purchases of the products. The website is maintained on a daily basis and all the new products that the organization is offering are updated into the organizational product collection. It also has readily available customer service, where customers can obtain further assistance on the products and have their inquiries addressed immediately (Smith, 2004). After organizational customers pay for the products, the organization then delivers them to an area where the customers can access them. With this method, the organization does not have to make any form of expansions to certain geographical areas in order to expand to those markets. As long as the individuals can access the organization’s website through an internet capable device, then they can make purchases of the products that the organization offers. These aspects make the organization one of the most successful retail organizations operating through the internet. Other organizations like e-bay and Alibaba also use this model to carry out their business activities.
- 10. Types of cybercrimes in e-businesses Cyber-crimes are among the main challenges that business organizations that utilize electronic methods to complete transactions face. Cyber-crimes refers to criminal activities that are carried out through the utilization of computer networks with or without the inclusion of the internet. Criminal activities that are thus carried out within the network of e-businesses are thus considered to be cybercrimes. There are different types of cybercrimes that are carried out within the e-business process. The first type of such cybercrimes is identity theft (Pettit, 2012). In order to complete an e-business transaction, the organization offering a product requires the customer to make certain payments. The payments can currently be made through a large number of options among which include credit cards or electronic methods of fund transfers. Through these methods, a customer is able to send money from his or her account to the organization from which he or she is making a purchase. The process that takes place in order to have the money transferred is that the organization collects data from the credit card for the customer and then uses that data to claim the agreed-upon amounts of money from the organization that stores money for the organization., this may be a bank or any other money storing online organization like Paypal or Skrill among others. With this data, an individual can manage to access funds from the accounts of the customer. If an individual is thus able to obtain the data from the credit of the customer without the customer knowing that the same has occurred, then he or she could also access the money of the customer using his or her credentials. His access is however unauthorized and thus it becomes the criminal activity referred to as identity theft. If the details or information is utilized to carry out a transaction, the transaction is said to have been carried out by the original
- 11. owner of the details (Nabi, 2005). The other type of cybercrime that individuals utilize which can significantly impact the process of e-business is Cyber extortion. Business organizations that utilize e-commerce rely on the internet band their servers to carry out business-oriented operations. With this regard, in a case where their servers became operational, they would lose a significant number of customers and in the process attain significant losses. With a clear understanding of this fact, ill-intentioned individuals capitalize on hacking the systems of these organizations to cause their servers to malfunction. They also ensure that the damage they make to these servers, they are the only ones capable of altering their changes and making the servers operate normally again. When they succeed, they then contact the organizations and demand for money in order to have the servers function normally again. In many occasions, the organizations are forced to pay the money requested since without their servers operations they may lose significant amounts of money, much higher than the ransom that criminals request (Kesan, Majuca, & Yurcik, 2005). Another major type of a cyber-crime that many organizations are significantly afraid of being subjected to, is data mining. When electronic methods of making payments are made, business organizations collect customer data and information with the aim of keeping a record of the sales and purchases made. This data includes credit card numbers and names for the customers who make purchases of products and goods from their organizations. Data mining is when some ill-intentioned individuals who are also highly skilled in computer networking hack these organizations and collect this data. When they obtain success, they cause significant problems for both the organization and the customers. With this data, the individuals can manage to access the accounts for different customers and even withdraw their credit card money. This form of crime can
- 12. result in significant loses for the organization through processes like having their reputation tarnished and compensating the customers whose data was fished from them (Karake Shalhoub, 2006). Case studies of massive cybercrimes in e-businesses In the e-business organizations, massive cybercrimes have taken place where a large number of organizations have been subjected to becoming victims of cyber-criminal activities. One of the largest cybercrime that took place is the target- Organization data fishing cyber-crime. Target organization is one of the largest retail organization in the United States after Walmart. In the year 2013, the organization experienced one of the largest data breach challenge, where hackers managed to fish more than 40 million debit and credit card information from the organization’s system. The hack began earlier before the Christmas evening when there was certainty that many people would make purchases of Christmas gifts among other products from the organization. From this attack, Target has been facing a significant challenge since then to ensure that its customers begin trusting that the organization is capable of protecting their data and at the same time due to the significant loses the organization made compensating those whose data was fished by the hackers. Another significantly large and massive cyber-attack that recently occurred is the 2016 attack on one of the DNS provider organization Dyn. This attack caused a large number of an e- commerce based organization like Twitter, Netflix, the guardian and Reddit among others to stop functioning. The purpose of this attack was simply for the hackers to reveal that they are capable of carrying out such an attack. The disruption, however, caused these organizations not to operate for more than a day and thus through it, they managed to lose a significant amount of money. An organization like Netflix, for example, gains significant amounts of money through its website services, where individuals are able to stream movies and attain other
- 13. services for a fee. The disruption thus caused a significant amount of loss and inconvenience for the organizations that it affected (Furnell, 2004). Another well recognized and significant cyber-attack that took place is the 2015 global banks hack. In the year 2015, hackers managed to infiltrate different bank’s network and gained data from a large number of institutions around the world. With this data, the hackers attained the ability to impersonate bank staff and thus managed to steal more than 650 million euros. They gained access through which they could even order an ATM to dispense cash without being provided with a bank cash. This hack was significant and targeted the banks that had the ability to carry out any form of e-commerce activities. From these case studies, it is thus clear that the challenge of cyber-crimes is significant in the e-business world. Statistics showing cybercrime activities in e-businesses Statistically, cyber-crime has caused a significant negative impact on a large number of individuals and organizations all over the world. To begin with, recent studies reveal that a number of companies that operate online are currently in loss of over 5 million dollars through the stolen data. There are also other organizations whose losses through this channel exceed 100 million dollars. Millions of consumers that utilize the services of these organizations have their bank account details being compromised and thus hackers can easily manage to access their accounts and withdraw their money easily. The activities that have been taking place in the world which revolve around cyber-criminal activities reveal that by the year 2019, the world will have lost more than 2.1 trillion dollars through cybercrimes. With this understanding, it is essential to ensure that certain measures have been put in place which will play part in making sure that organizations succeed in securing their business activities from cybercriminals (Bosworth, & Kabay, 2002). Mitigation of cybercrimes in e-businesses
- 14. Business organizations also have attained a clear understanding of the open threat that they are facing through cyber-criminal activities. With this understanding, there are certain measures that have been put in place, which are aimed at helping the business organizations manage to remain secure and capable of protecting their operations and customer data from ill- intentioned and skilled hackers. To begin with, there are highly capable anti-malware programs that business organizations currently utilize, which are aimed at detecting any form of abnormal activities within the computer networks which could easily be malware. These programs help the business organizations manage to identify different forms of cyber- attacks before they happen and thus they stay alert to prevent the attacks from occurring. A simple anti-malware program is however not sufficient in keeping hackers out of a network. With this understanding, large business organizations have considered making purchased of complex cyber-security programs capable of detecting any form of activities that hackers may involve in. a good example of such a program is the FireEye. This program is able to detect any form of malware of hack before it manages to break an organization’s security. It is also the program that could have helped the target organization manage to completely minimize the impact of the attack that the organization experienced in the year 2013. With this regard, the organization is taking caution by investing in cyber-security measures to avoid attaining losses which may occur through hackers. Taking these measures is thus one of the main ways through which the e-business organizations are utilizing to address the data breach challenges that they are facing (Akhter, & Kaya, 2008). Conclusion E-businesses have recently become major entities and effective ways of earning for many business organizations. Through them, many organizations have attained the ability to remain
- 15. completely effective in their operations and increase the gains that they obtain on a daily basis. These business organizations and their ways of carrying out business operations are currently being threatened by the challenge of cyber-crimes. Many organizations have faced adverse negative challenges caused by hackers, through which their systems and ways of doing business has been disrupted and threatened. Business organizations are currently implementing measures to address this issues, by investing in network security resources and programs that can help them identify and completely eliminate an attack (Scott, 2004). An effective way to ensure that cyber- attacks do not occur is thus for an organization to remain prepared for one and ready to challenge the hackers with an effective security system. References Akhter, F., & Kaya, L. (2008, March). Building secure e- business systems: technology and culture in the UAE. In Proceedings of the 2008 ACM symposium on Applied computing (pp. 1474-1475). ACM. Bosworth, S., & Kabay, M. E. (Eds.). (2002). Computer security handbook. John Wiley & Sons. Furnell, S. (2004). E-commerce security: a question of trust. Computer Fraud & Security, 2004(10), 10-14. Karake Shalhoub, Z. (2006). Trust, privacy, and security in electronic business: the case of the GCC countries. Information Management & Computer Security, 14(3), 270-283 Kesan, J., Majuca, R., & Yurcik, W. (2005, June). Cyber insurance as a market-based solution to the problem of cybersecurity: a case study. In Proc. WEIS (pp. 1-46).
- 16. Lowry, Paul Benjamin; Cherrington, J. Owen; Watson, R. J. (2001). E-Business Handbook. Boca Raton, FL: CRC Press. Nabi, F. (2005). Secure business application logic for e- commerce systems. Computers & Security, 24(3), 208-217. Pettit, R. (2012). Learning From Winners: How the ARF Ogilvy Award Winners Use Market Research to Create Advertising Success. Psychology Press. Scott, J. E. (2004). Measuring dimensions of perceived e- business risks. Information systems and e-Business Management, 2(1), 31-55. Smith, A. D. (2004). Cybercriminal impacts on online business and consumer confidence. Online Information Review, 28(3), 224-234. Smith, A. D., & Rupp, W. T. (2002). Issues in cybersecurity; understanding the potential risks associated with hackers/crackers. Information Management & Computer Security, 10(4), 178-183. Velmurugan, M. S. (2009). Security and Trust in e-Business: Problems and Prospects. International Journal of Electronic Business Management, 7(3) Assignment 2. Cyber Research Proposal (Due at the End of Week Six: 30% of Grade)
- 17. Within INTL 647 you are required to design a line of research around an assessment of specific cyber issue. In this case, you can select the issue that you identified in your Cyber White Paper assignment (Assignment #1). You are encouraged to refer to Belcher, Wendy Laura. 2009. "Editing Your Sentences" In Writing Your Journal Article in 12 Weeks. A Guide to Academic Publishing Success. Sage. This resource has an excellent step-by-step process for enhancing your writing. The goal of this assignment is to present a clear research proposal. Your research proposal should be between 5-6 pages in length not including your preliminary source list and references. You will need to: 1) Identify a cyber incident or an international situation that contains significant cyber issue. Assess and provide some contextual information that helps demonstrate your understanding of the nature of the issue or case. 2) Clearly state your research question. 3) Explain why this issue is important to investigate. What can
- 18. we learn from this situation? How will the knowledge we gain through your research help our understanding of cognition, information processing errors and/or decision-making errors? 4) Discuss your theoretical framework. Here you will summarize/synthesize some of the theories/models and concepts you'll use to investigate the intelligence/decision-making failures such as consistency theory, balance theory, bolstering, groupthink and etc. 5) Discuss your research design. Your research design should discuss how you plan to carry out your analysis. Heath and Tynan have a short but insightful article on “Crafting a Research Proposal,” which can be accessed at: http://www.nottingham.ac.uk/business/nexus/Documents/MaMS c/Dissertation/PereiraTynan- CraftingaResearchProposalTMR_2010.pdf 6) Identify a list of 8 preliminary sources, 6 of which must be from peer-reviewed journals. These should be listed using Turabian References style formatting.
- 19. Format. Your proposal should include a title page, proposal body, reference page, and a preliminary source list (title, references page, and source list are not included within the page count). Your paper should have 1-inch border on all four sides, use Times New Roman-12 http://www.nottingham.ac.uk/business/nexus/Documents/MaMS c/Dissertation/PereiraTynan- CraftingaResearchProposalTMR_2010.pdf http://www.nottingham.ac.uk/business/nexus/Documents/MaMS c/Dissertation/PereiraTynan- CraftingaResearchProposalTMR_2010.pdf point font, be double spaced, and not have an extra space in between paragraphs. All references and citations are in Chicago Turabian format. This information is from the Master's Capstone Manual and it should help you develop your research proposal. Students taking the capstone option are required to submit a 5 page research proposal prior to moving forward on their research. These are some of the sections they are required to include within their proposal, they have been included in these instructions as they directly relate to the goals of this assignment.
- 20. Introduction. Identifies your specific research question and sets the general context for the study. • Statement of the problem and context leading to a clear statement of the specific research question. • Background and contextual material justifying why we should study this case or topic. • Purpose statement. Theoretical Framework. The theoretical framework section develops the theories or models to be used in the study and shows how you have developed testable research hypotheses. • Introduction discussing gaps in the literature, how this study will help fill some of those gaps, and justification for theory or model to be used in study. • Summary of the theory or model to be used in the study, including a diagram of the model if appropriate. • Statement of hypotheses to be tested. Research Design. Describes how you will test the hypothesis and carry out your analysis. It
- 21. describes the data you will use to test your hypothesis, how you will operationalize and collect data on your variables, and the analytic methods that you will use, noting potential biases and limitations to your research approach. It should include. • Identification and operationalization (measurement) of variables. • Sampling plan (i.e., study population and sampling procedures, if appropriate). • Justification of case studies used. • Data Collection/Sources (secondary literature, archives, interviews, surveys, etc.). • Summary of analysis procedures (pattern-matching, etc.). • Limitations of study and bias discussion. Preliminary Source List. List of at least eight sources you plan to utilize within your paper, six of which must be from the peer reviewed literature. Reference List. Reference the works that you have cited (direct quotes or paraphrases) in the text. This must be in the school’s prescribed format. [In INTL this means Turabian format, either
- 22. using the author-date method or the bibliography-notes method] Submission Instructions. The research proposal must be submitted as a Word Document Attachment in the Assignments section of the classroom by Sunday, 11.55pm EST at the end of Week 6.