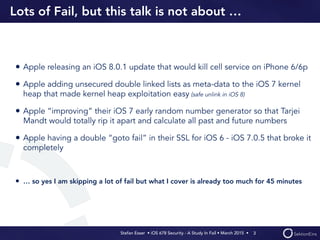
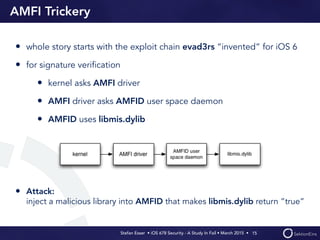
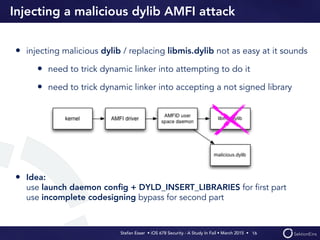
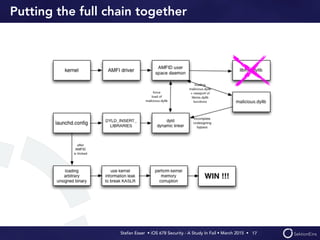
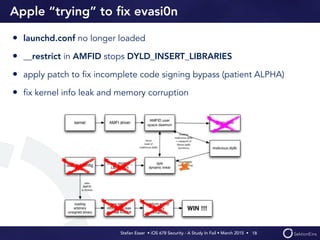
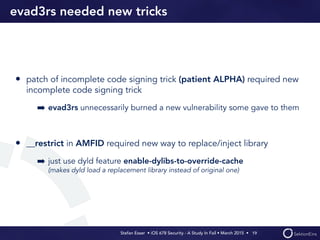
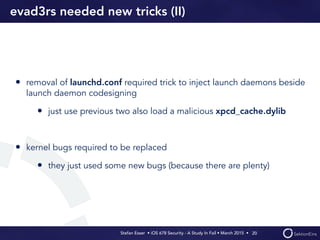
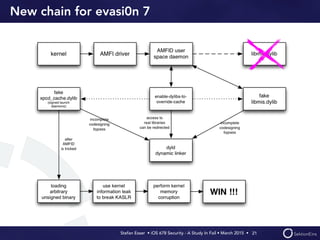
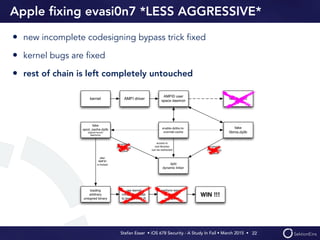
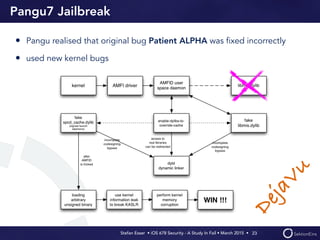
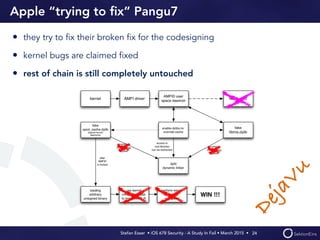
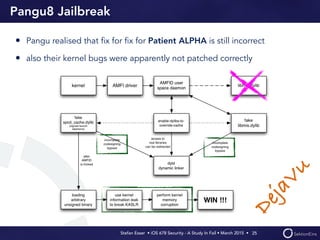
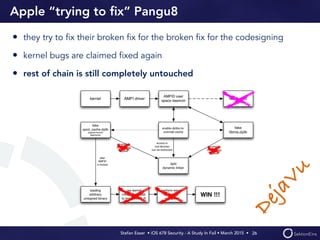
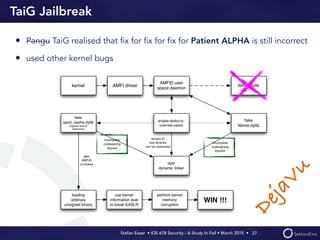
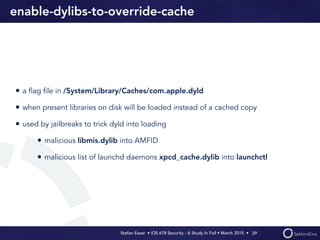
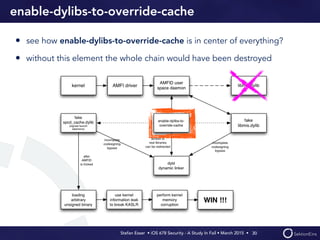
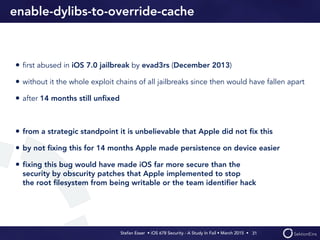
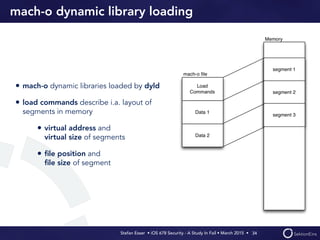
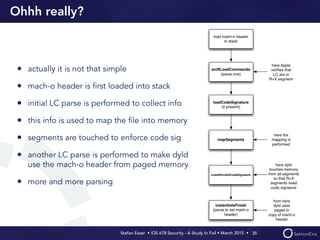
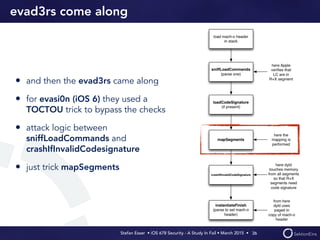
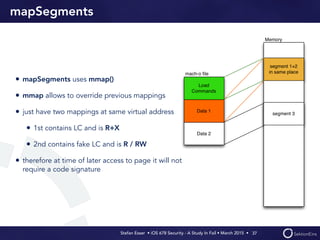
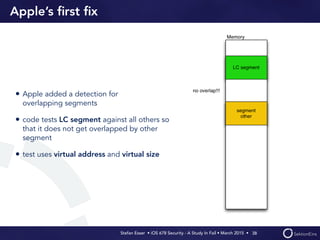
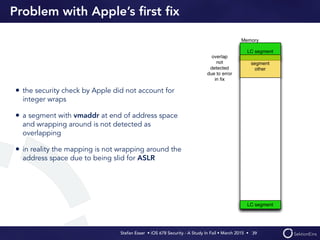
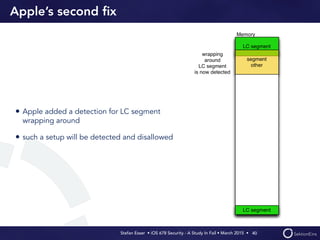
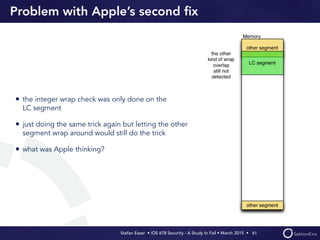
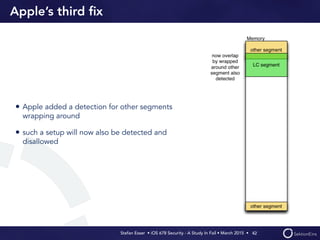
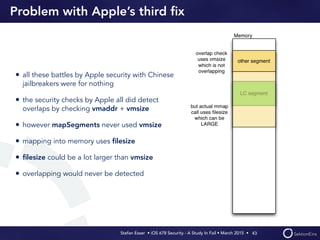
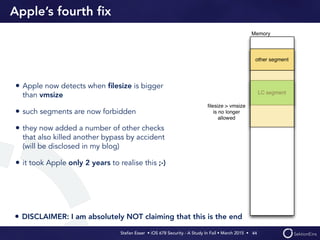
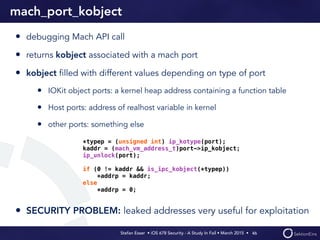
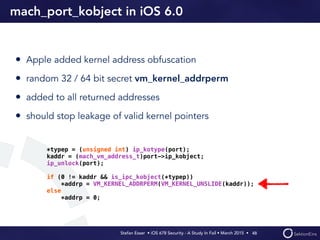
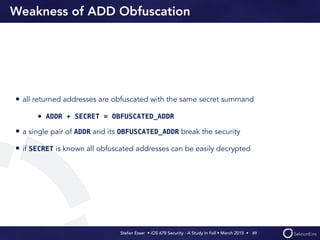
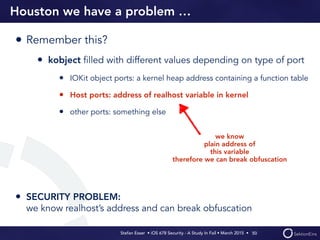
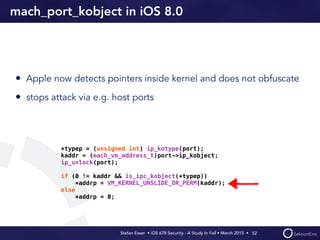
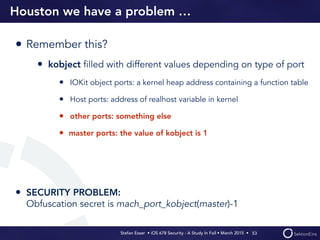
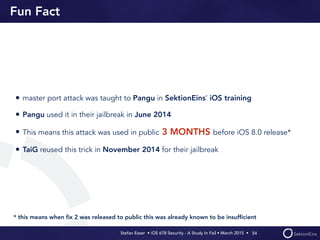
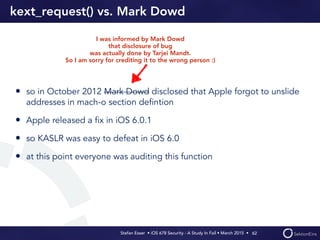
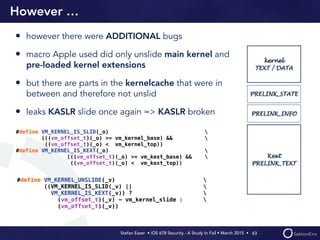
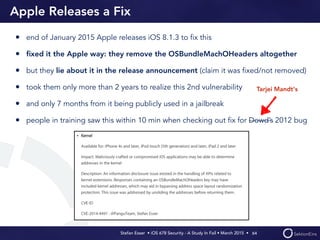
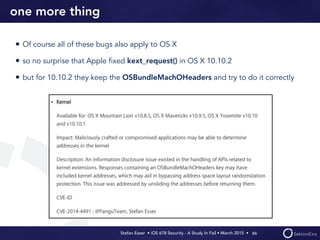
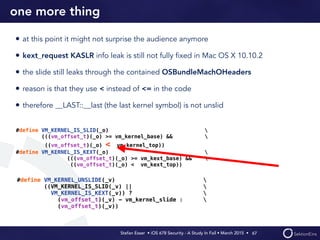
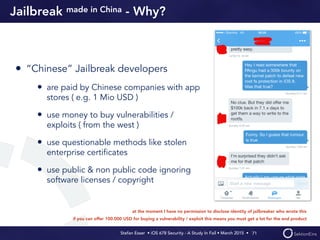
The document discusses various security failures in Apple's iOS versions 6 to 8, focusing on issues that have arisen from jailbreaks and Apple's attempts to fix them. Key points include the vulnerabilities exploited by jailbreak developers and Apple's inadequate responses to these security flaws, which made it easier for users to maintain jailbreak persistency. The author emphasizes the significance of specific vulnerabilities and the lack of effective fixes by Apple over time.