Wireshark network analysing software
•Download as PPTX, PDF•
1 like•826 views
it is a PPT on cyber security. one software Wireshark witch is use for the analyse the network protocols or packages.
Report
Share
Report
Share
Recommended
More Related Content
What's hot
What's hot (20)
Similar to Wireshark network analysing software
Similar to Wireshark network analysing software (20)
Packet analyzing with wireshark-basic of packet analyzing - Episode_01

Packet analyzing with wireshark-basic of packet analyzing - Episode_01
Analysis of network traffic by using packet sniffing tool wireshark

Analysis of network traffic by using packet sniffing tool wireshark
For your final step, you will synthesize the previous steps and la

For your final step, you will synthesize the previous steps and la
ANALYZING NETWORK PERFORMANCE PARAMETERS USING WIRESHARK

ANALYZING NETWORK PERFORMANCE PARAMETERS USING WIRESHARK
Practical 7 - Using Wireshark Tutorial and Hands-on

Practical 7 - Using Wireshark Tutorial and Hands-on
Wireshark Lab Getting Started v6.0 Supplement to Co.docx

Wireshark Lab Getting Started v6.0 Supplement to Co.docx
More from dharmesh nakum
More from dharmesh nakum (7)
Braking and multi-quadrant operation of VSI drives,Cycloconverter based indu...

Braking and multi-quadrant operation of VSI drives,Cycloconverter based indu...
Analysis of unsymmetrical faults using the bus impedance matrix, Faults throu...

Analysis of unsymmetrical faults using the bus impedance matrix, Faults throu...
Recently uploaded
Process of Integration the Laser Scan Data into FEA Model and Level 3 Fitness-for-Service Assessment of Critical Assets in Refinery & Process IndustriesFEA Based Level 3 Assessment of Deformed Tanks with Fluid Induced Loads

FEA Based Level 3 Assessment of Deformed Tanks with Fluid Induced LoadsArindam Chakraborty, Ph.D., P.E. (CA, TX)
Welcome to the April edition of WIPAC Monthly, the magazine brought to you by Water Industry Process Automation & Control.
In this month's edition, along with the latest news from the industry we have articles on:
The use of artificial intelligence and self-service platforms to improve water sustainability
A feature article on measuring wastewater spills
An article on the National Underground Asset Register
Have a good month,
OliverWater Industry Process Automation & Control Monthly - April 2024

Water Industry Process Automation & Control Monthly - April 2024Water Industry Process Automation & Control
From customer value engagements to hands-on production support, our Services span across every stage of our customers digital transformation journey, to help ensure that every customer is successful in their adoption of our solutions.
• Implementation, Upgrade, Migration, and Maintenance Services
• On-Premises and On-Cloud
• COTS Training Services; On-Site and Virtual
• Software Support Services; Legacy and 3DEXPERIENCE
• Value Engagement & Blueprinting
• Specialized Consulting and Support Services
• Customized Training Services
• Automation and Configuration Services
• Technical Resource Augmentation Services
• Project Management
• Know-how Training (mentoring) and Resource AugmentationNavigating Complexity: The Role of Trusted Partners and VIAS3D in Dassault Sy...

Navigating Complexity: The Role of Trusted Partners and VIAS3D in Dassault Sy...Arindam Chakraborty, Ph.D., P.E. (CA, TX)
Call girls in delhi ✔️✔️🔝 9953056974 🔝✔️✔️Welcome To Vip Escort Services In Delhi [ ]Noida Gurgaon 24/7 Open Sex Escort Services With Happy Ending ServiCe Done By Most Attractive Charming Soft Spoken Bold Beautiful Full Cooperative Independent Escort Girls ServiCe In All-Star Hotel And Home Service In All Over Delhi, Noida, Gurgaon, Faridabad, Ghaziabad, Greater Noida,
• IN CALL AND OUT CALL SERVICE IN DELHI NCR
• 3* 5* 7* HOTELS SERVICE IN DELHI NCR
• 24 HOURS AVAILABLE IN DELHI NCR
• INDIAN, RUSSIAN, PUNJABI, KASHMIRI ESCORTS
• REAL MODELS, COLLEGE GIRLS, HOUSE WIFE, ALSO AVAILABLE
• SHORT TIME AND FULL TIME SERVICE AVAILABLE
• HYGIENIC FULL AC NEAT AND CLEAN ROOMS AVAIL. IN HOTEL 24 HOURS
• DAILY NEW ESCORTS STAFF AVAILABLE
• MINIMUM TO MAXIMUM RANGE AVAILABLE.
Call Girls in Delhi & Independent Escort Service –
CALL GIRLS SERVICE DELHI NCR
Vip call girls in Delhi
Call Girls in Delhi, Call Girl Service 24×7 open
Call Girls in Delhi Best Delhi Escorts in Delhi
Low Rate Call Girls In Saket Delhi
X~CALL GIRLS IN Ramesh Nagar Metro
best Delhi call girls and Delhi escort service.
CALL GIRLS SERVICE IN ALL DELHI …
(Delhi) Call Girls in (Chanakyapuri)
Hot And Sexy Independent Model Escort Service In Delhi Unlimited Enjoy Genuine 100% Profiles And Trusted Door Step Call Girls Feel Free To Call Us Female Service Hot Busty & Sexy Party Girls Available For Complete Enjoyment. We Guarantee Full Satisfaction & In Case Of Any Unhappy Experience, We Would Refund Your Fees, Without Any Questions Asked. Feel Free To Call Us Female Service Provider Hours Opens Thanks.
Delhi Escorts Services 100% secure Services.Incall_OutCall Available and outcall Services provide.
We are available 24*7 for Full Night and short Time Escort Services all over Delhi NCR.
Delhi All Hotel Services available 3* 4* 5* Call Call
Delhi Escorts Services And Delhi Call Girl Agency 100% secure Services in my agency. Incall and outcall Services provide.
We are available 24*7 for Full Night and short Time Escort Services my agency in all over New Delhi
Delhi All Hotel Services available my agency
SERVICES [✓✓✓]
Housewife
College Girl
VIP Escort
Independent Girl
Aunty
Without a Condom sucking )?
Sexy Aunty.DSL (Dick Sucking Lips)?
DT (Dining at the Toes English Spanking)
Doggie (Sex style from no behind)??
OutCall- All Over Delhi Noida Gurgaon 24/7
FOR APPOINTMENT Call/Whatsop / 9953056974Call Girls in Netaji Nagar, Delhi 💯 Call Us 🔝9953056974 🔝 Escort Service

Call Girls in Netaji Nagar, Delhi 💯 Call Us 🔝9953056974 🔝 Escort Service9953056974 Low Rate Call Girls In Saket, Delhi NCR
Recently uploaded (20)
Top Rated Call Girls In chittoor 📱 {7001035870} VIP Escorts chittoor

Top Rated Call Girls In chittoor 📱 {7001035870} VIP Escorts chittoor
Call Girls In Bangalore ☎ 7737669865 🥵 Book Your One night Stand

Call Girls In Bangalore ☎ 7737669865 🥵 Book Your One night Stand
VIP Call Girls Palanpur 7001035870 Whatsapp Number, 24/07 Booking

VIP Call Girls Palanpur 7001035870 Whatsapp Number, 24/07 Booking
Call Girls Pimpri Chinchwad Call Me 7737669865 Budget Friendly No Advance Boo...

Call Girls Pimpri Chinchwad Call Me 7737669865 Budget Friendly No Advance Boo...
FEA Based Level 3 Assessment of Deformed Tanks with Fluid Induced Loads

FEA Based Level 3 Assessment of Deformed Tanks with Fluid Induced Loads
Cara Menggugurkan Sperma Yang Masuk Rahim Biyar Tidak Hamil

Cara Menggugurkan Sperma Yang Masuk Rahim Biyar Tidak Hamil
Water Industry Process Automation & Control Monthly - April 2024

Water Industry Process Automation & Control Monthly - April 2024
Double Revolving field theory-how the rotor develops torque

Double Revolving field theory-how the rotor develops torque
Navigating Complexity: The Role of Trusted Partners and VIAS3D in Dassault Sy...

Navigating Complexity: The Role of Trusted Partners and VIAS3D in Dassault Sy...
Hazard Identification (HAZID) vs. Hazard and Operability (HAZOP): A Comparati...

Hazard Identification (HAZID) vs. Hazard and Operability (HAZOP): A Comparati...
Call Girls in Netaji Nagar, Delhi 💯 Call Us 🔝9953056974 🔝 Escort Service

Call Girls in Netaji Nagar, Delhi 💯 Call Us 🔝9953056974 🔝 Escort Service
Wireshark network analysing software
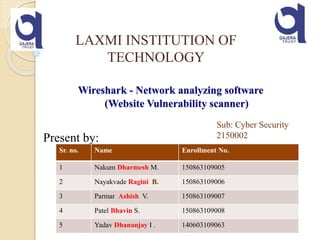
- 1. Wireshark - Network analyzing software (Website Vulnerability scanner) Present by: LAXMI INSTITUTION OF TECHNOLOGY Sr. no. Name Enrollment No. 1 Nakum Dharmesh M. 150863109005 2 Nayakvade Ragini B. 150863109006 3 Parmar Ashish V. 150863109007 4 Patel Bhavin S. 150863109008 5 Yadav Dhananjay I . 140603109063 Sub: Cyber Security 2150002
- 2. Content What is Wireshark Where it use How it works Some practical things
- 3. What is Wireshark? - Network packet/protocol analyzer - One of the best open source packet analyzers available today for UNIX and Windows
- 4. You could think of a network packet analyzer as a measuring device used to examine what’s going on inside a network cable, just like a voltmeter is used by an electrician to examine what’s going on inside an electric cable (but at a higher level, of course). Wireshark is perhaps one of the best open source packet analyzers available today.
- 5. Where it use? - Network Administrators use it to troubleshoot network problems - Network security engineers use it to examine security problems - Testers use it to detect defects :) - People use it to learn network protocol internals.
- 6. WireShark – Sample Demo
- 7. A vulnerability scanner is a computer program designed to assess computers, computer systems, networks or applications for weaknesses. They can be run either as part of vulnerability management by those tasked with protecting systems - or by black hat attackers looking to gain unauthorized access. Website Vulnerability Scanner:
- 8. The following are some of the many features Wireshark provides: •Available for UNIX and Windows. •Capture live packet data from a network interface. •Open files containing packet data captured with tcpdump / WinDump, •Wireshark, and a number of other packet capture programs. •Import packets from text files containing hex dumps of packet data. •Display packets with very detailed protocol information. •Save packet data captured. •Export some or all packets in a number of capture file formats. •Filter packets on many criteria. •Search for packets on many criteria. •Colorize packet display based on filters. •Create various statistics. ... and a lot more! . Features:
- 9. How it works? For Windows - download (http://www.wireshark.org/download.html) - install - use
- 11. Open Wireshark. Click the "Capture" menu, then click "Interfaces." A small window with all of your networking interfaces will appear. If you use any network traffic, you will start to see packets coming in.
- 15. Status Bar 15
- 16. HTTP Analysis
- 17. HTTP Analysis – Load Distribution Click “Create Stat” button You can add “filter” to only Show selected traffic
- 18. HTTP Analysis – Packet Counter
- 19. HTTP Analysis – Requests
- 20. Each line represents a packet, and there are 7 columns that provide information about it is number column shows the order of the packet when you start recording network traffic. This is to provide you with number reference so that you can easily identify particular packet. The time is in seconds, up to 6 decimals, when the packet was received after you started to record network traffic. The source includes the Internet Protocol (IP) address of the packet's origin. The destination IP records where a particular packet is going. The protocol the packet uses. The most common are TCP, UDP and HTTP. Examine each packet's information.
- 22. Video
- 23. The End