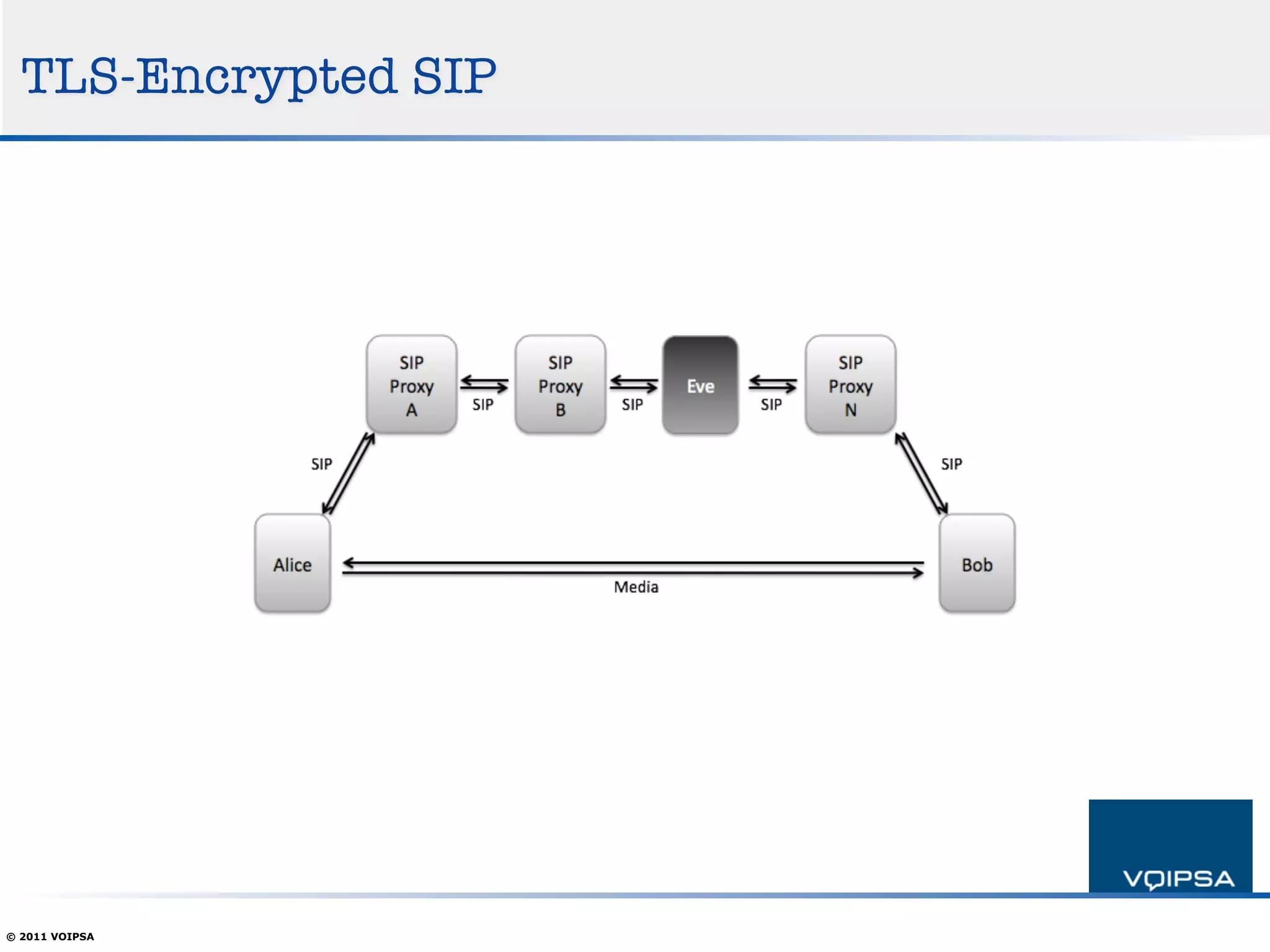
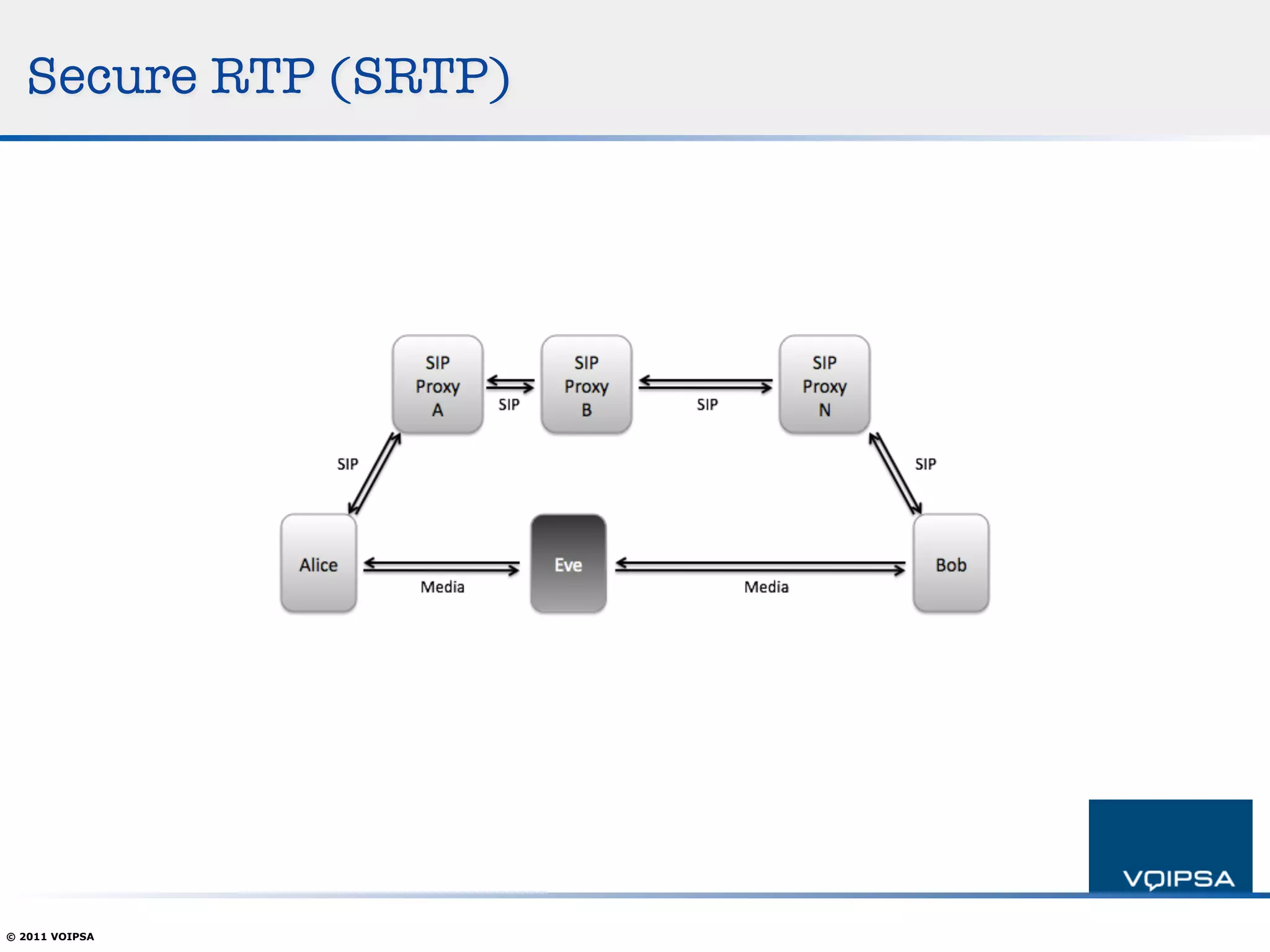
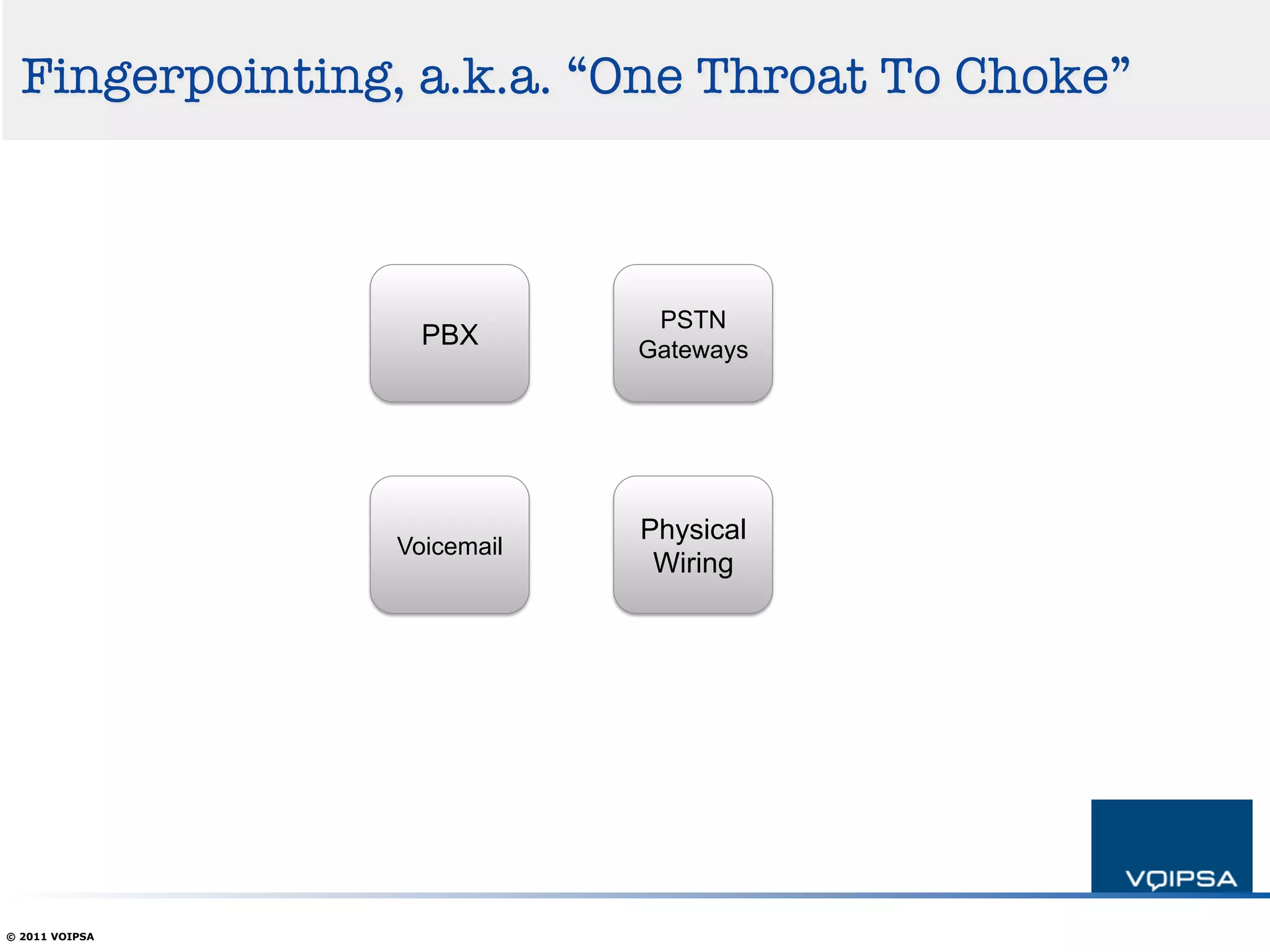
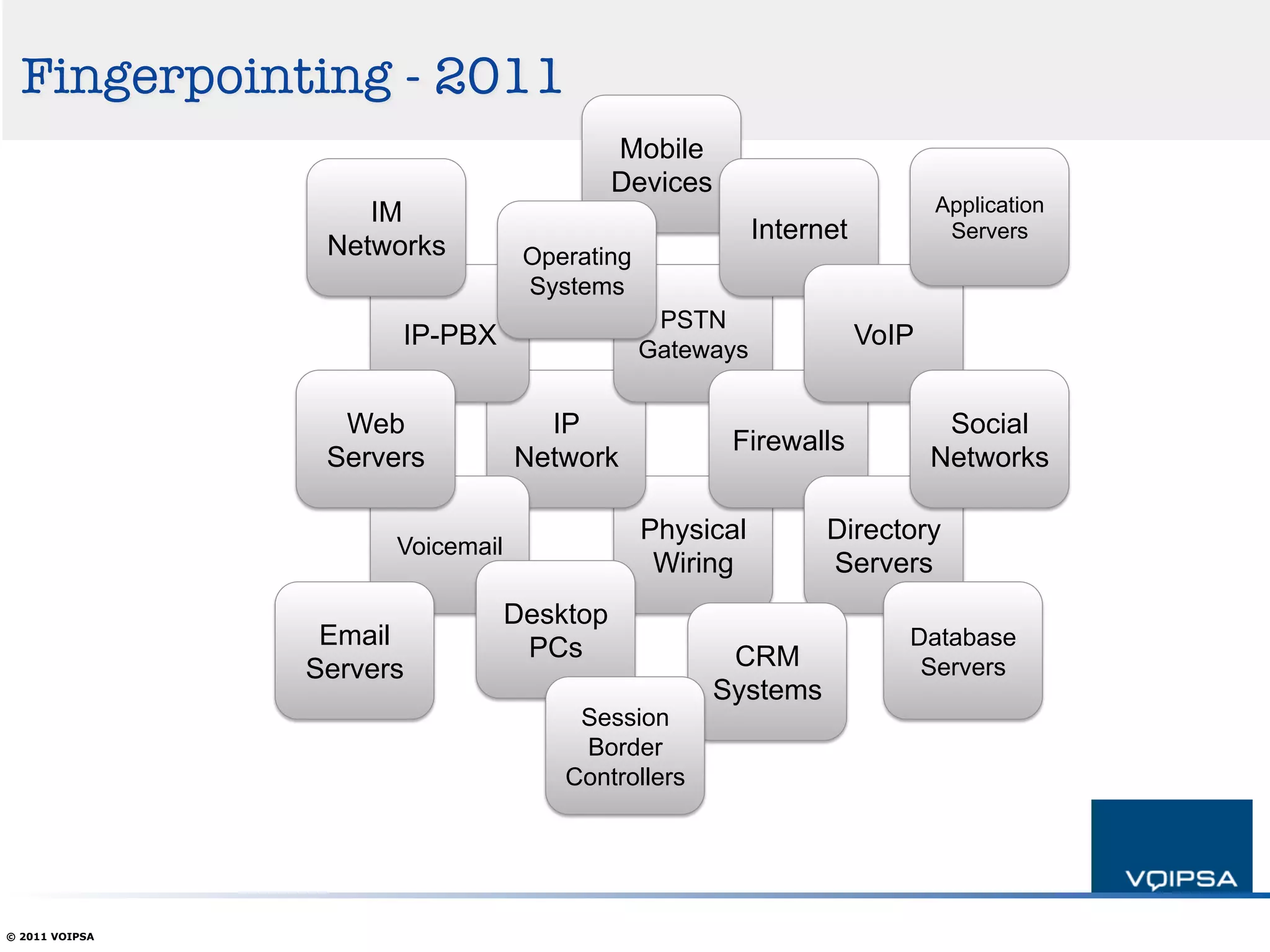
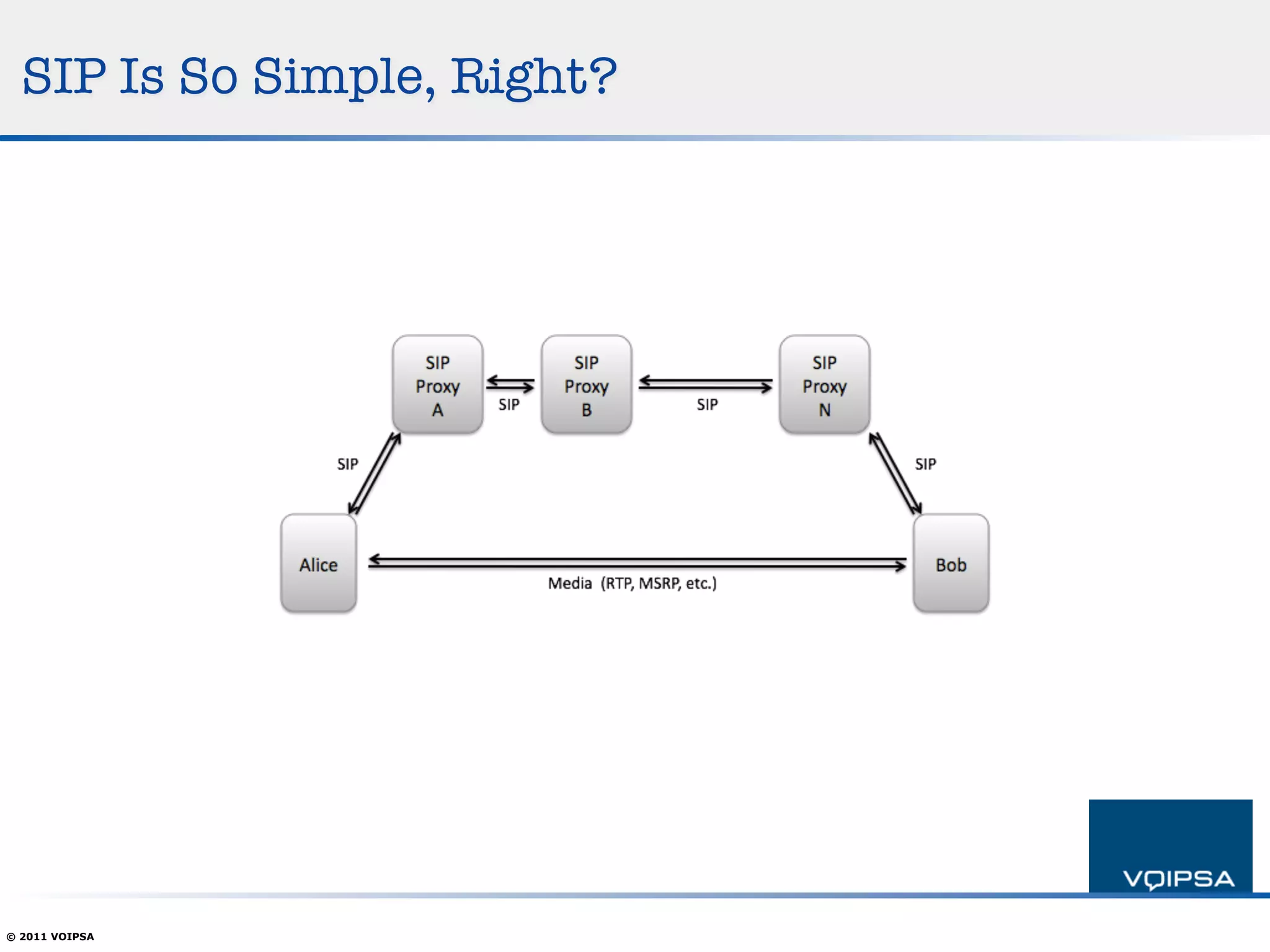
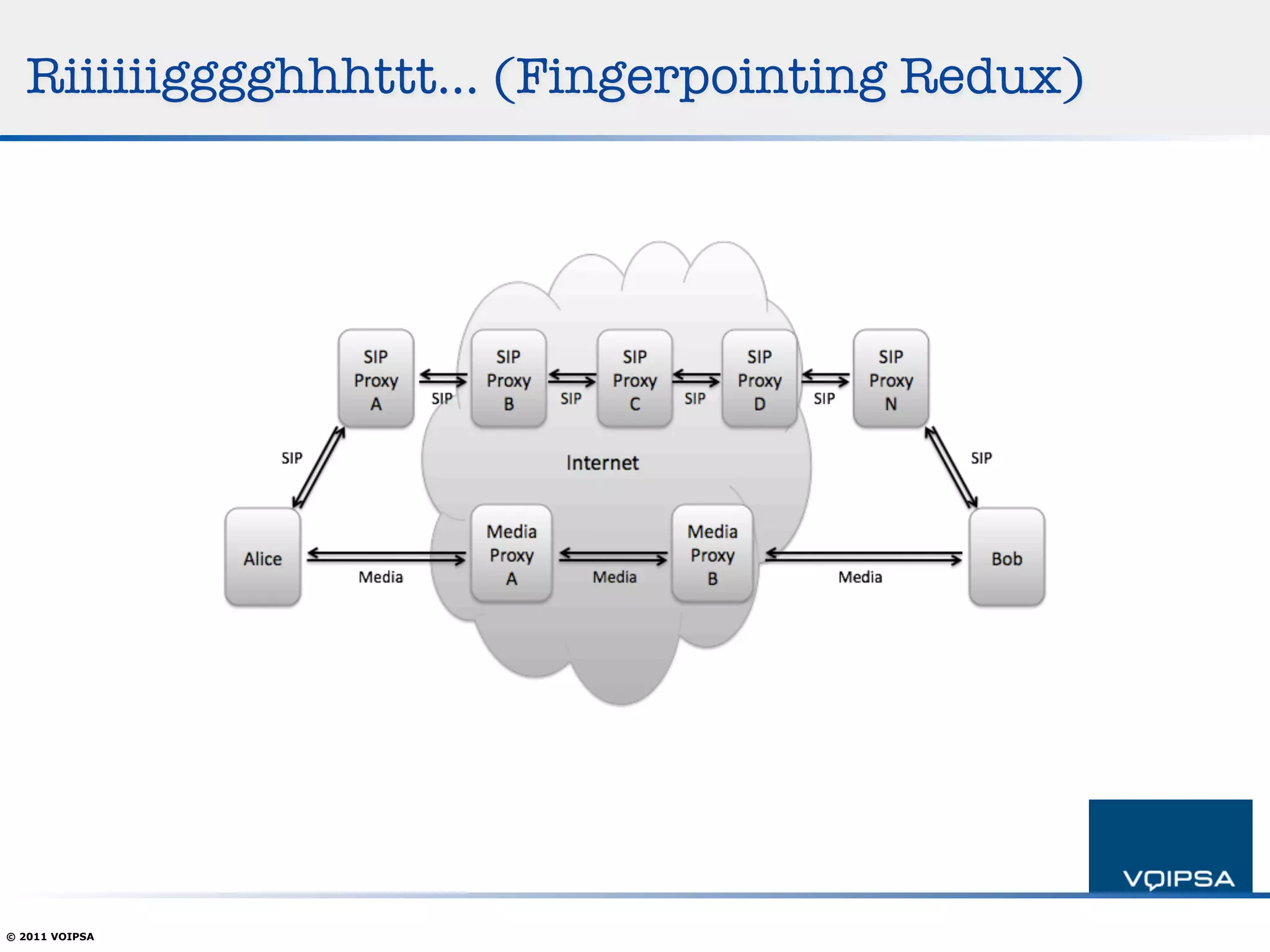
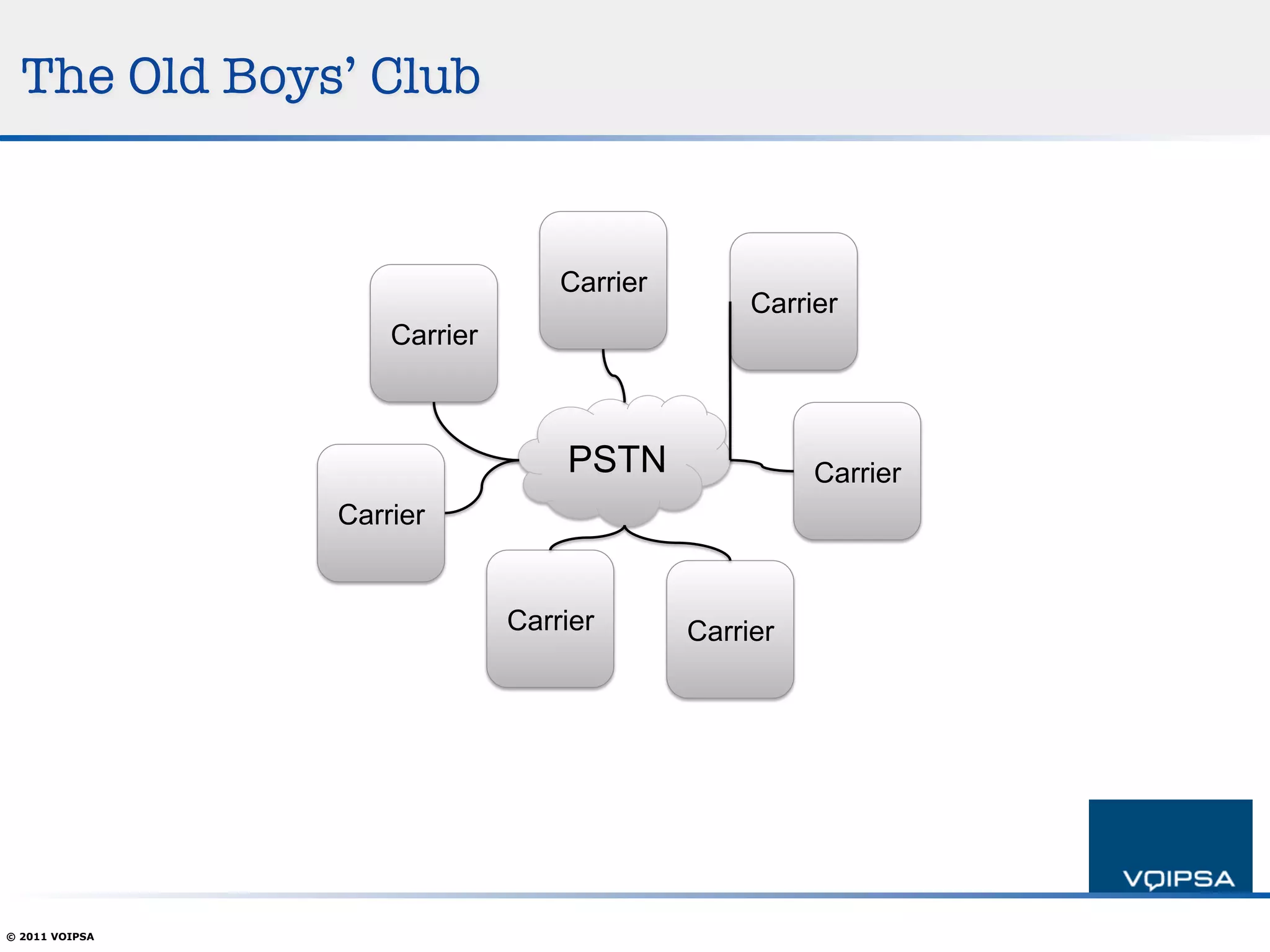
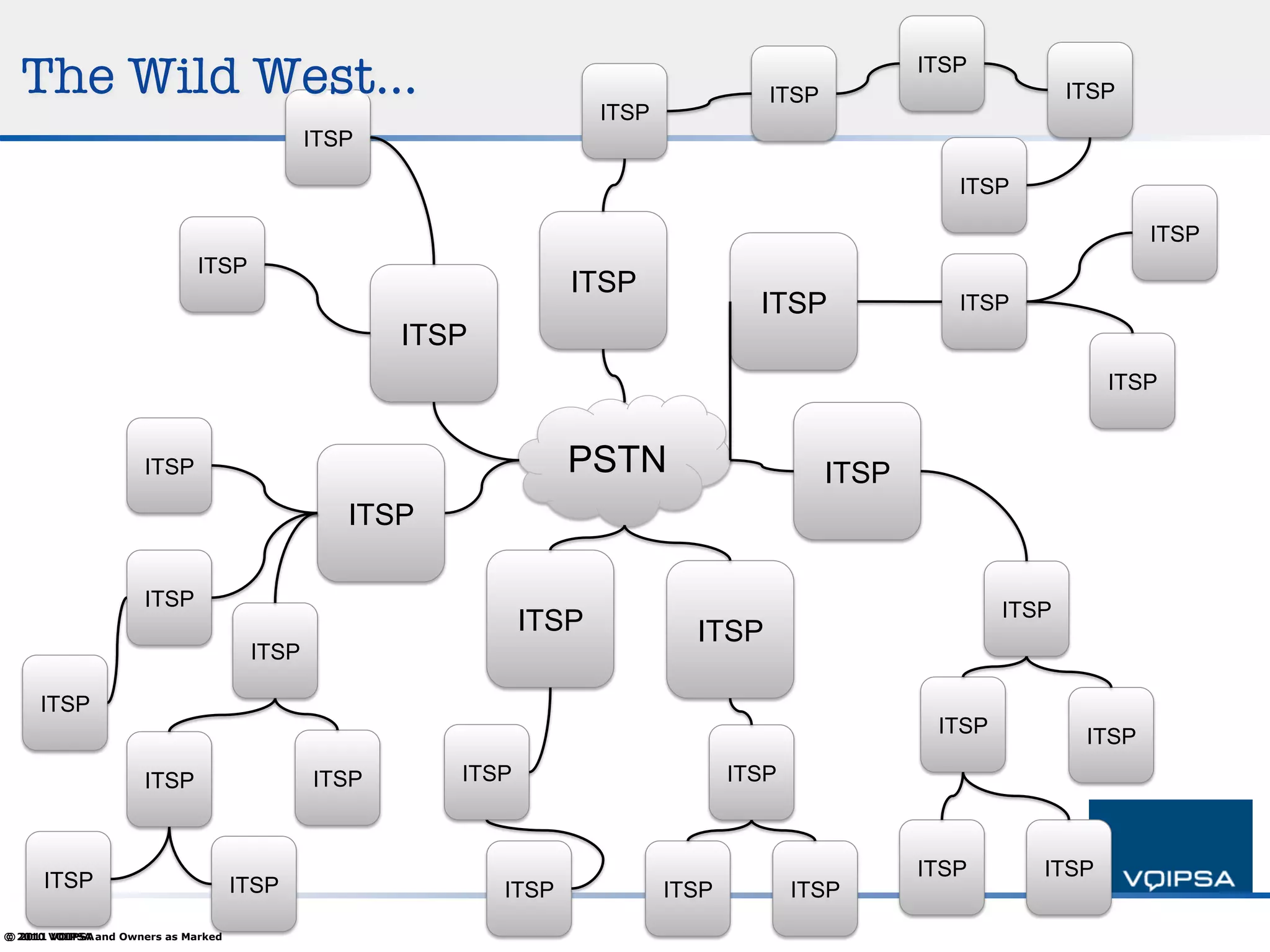
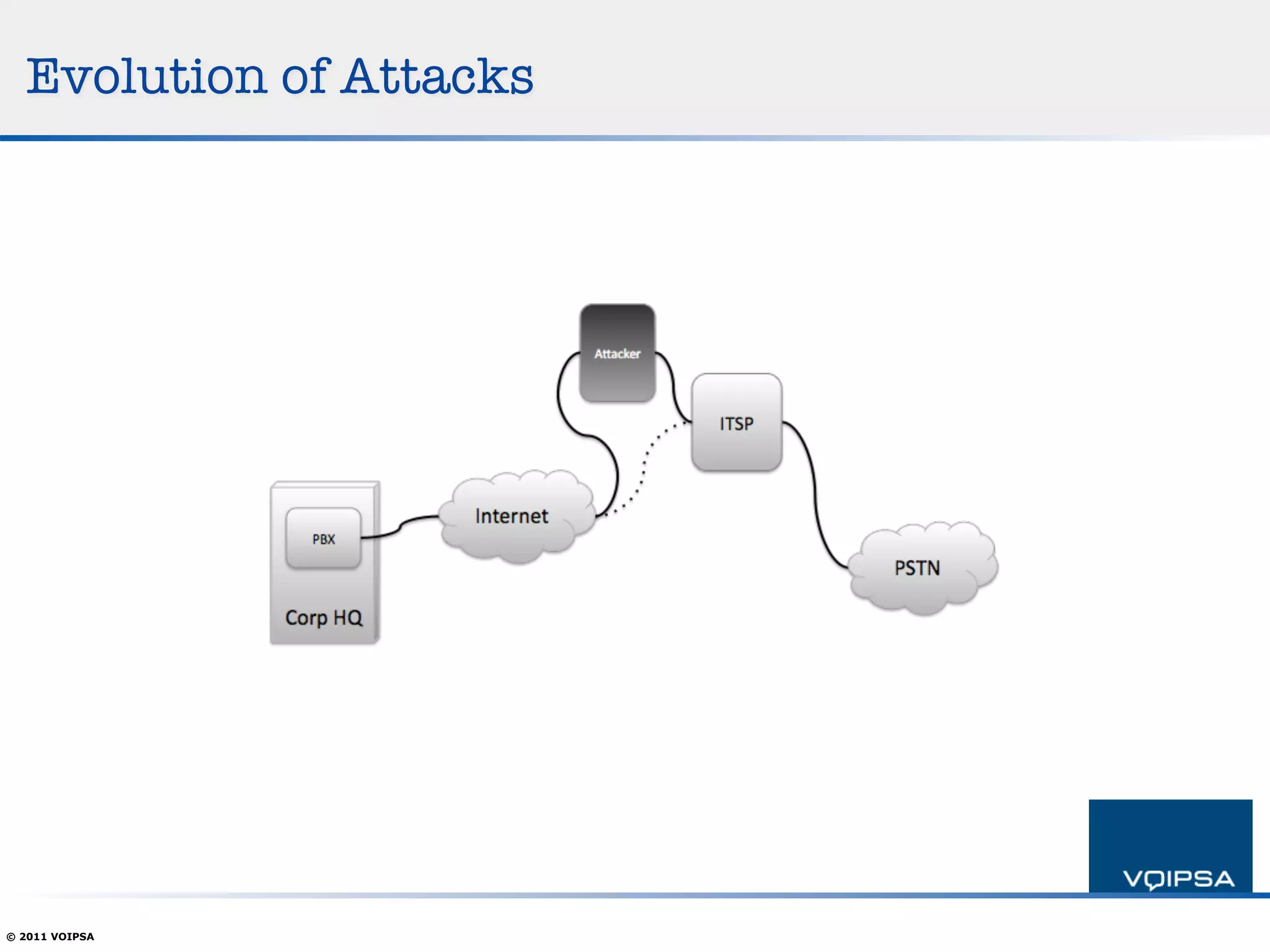
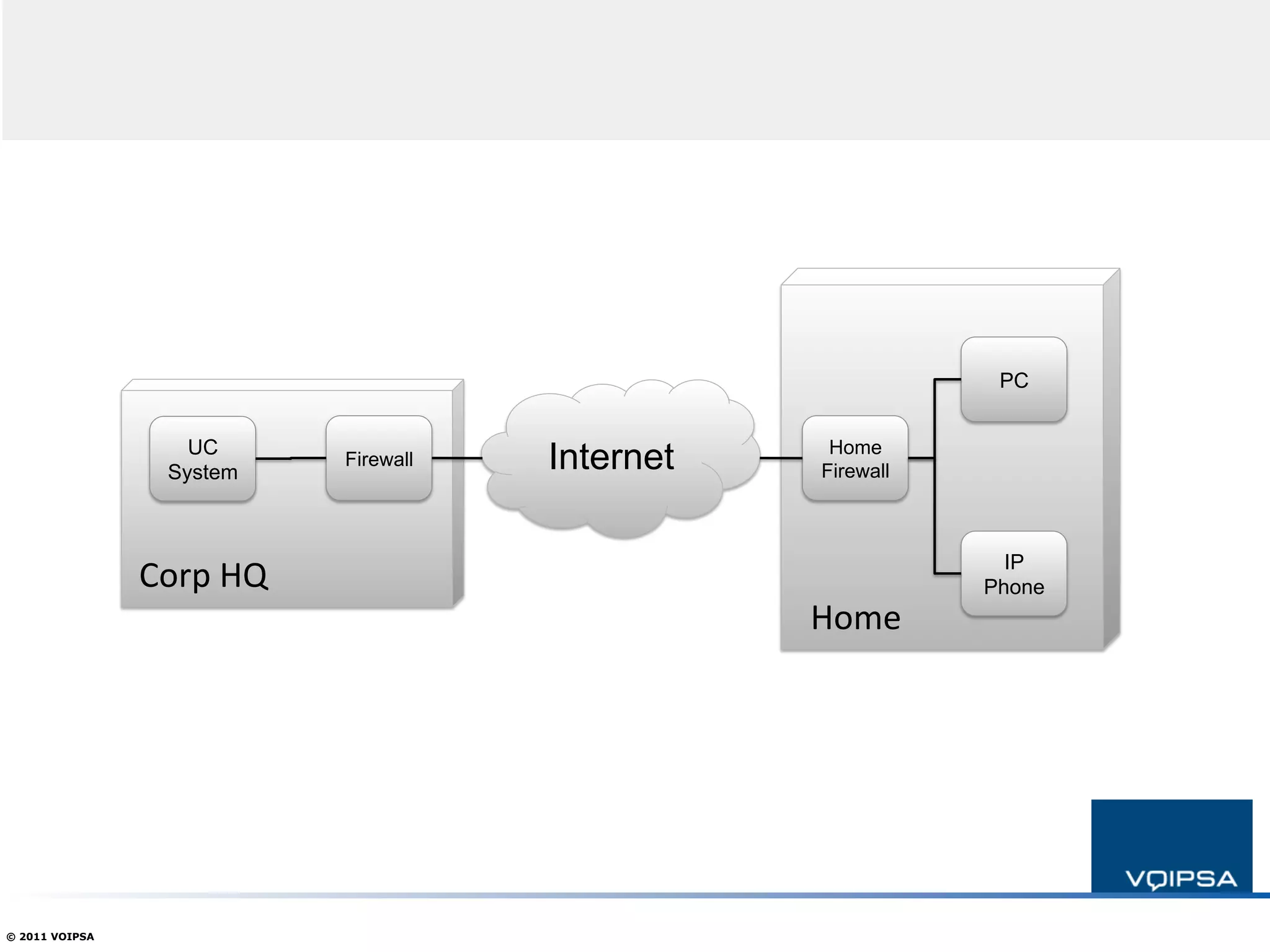
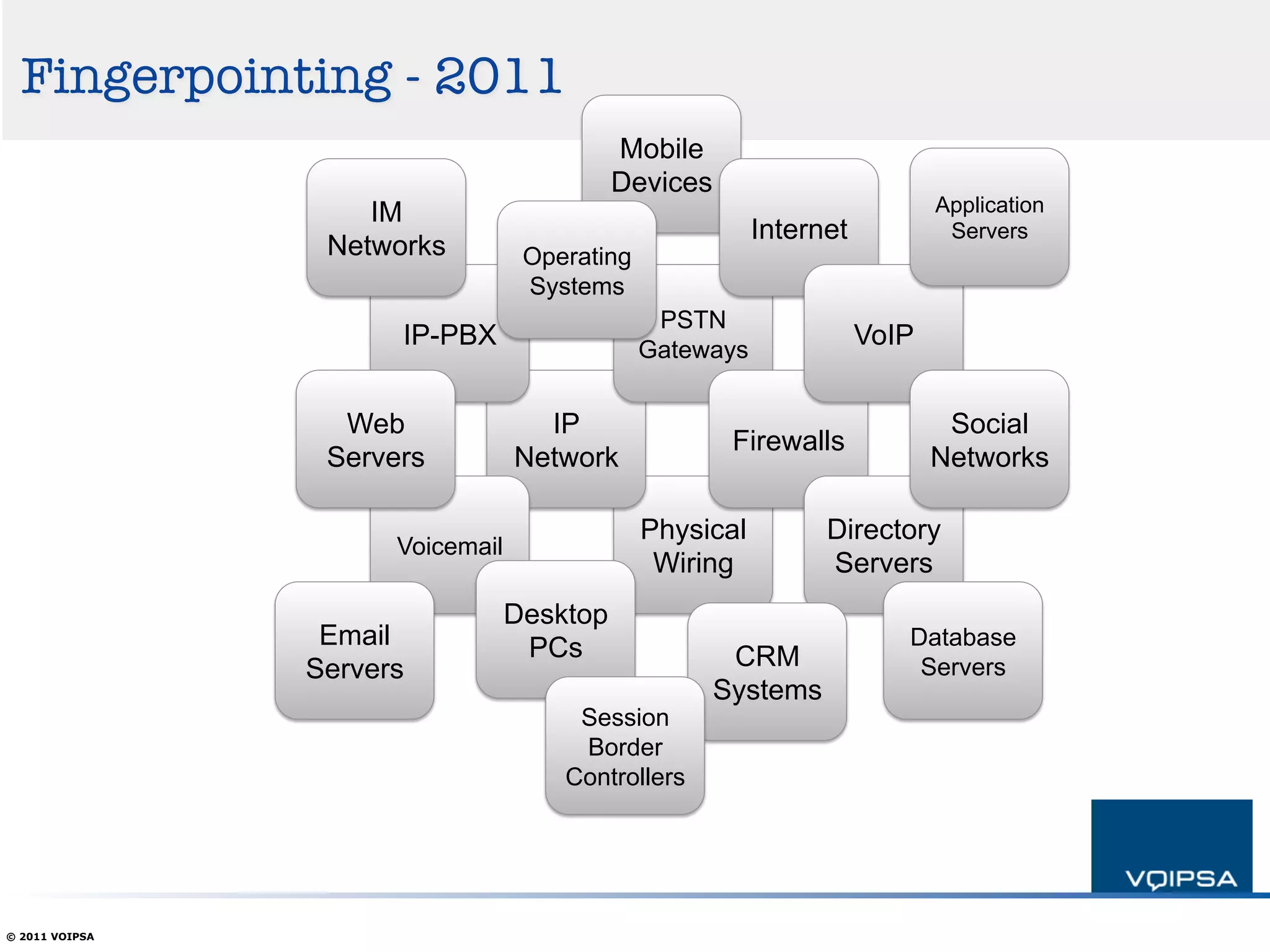
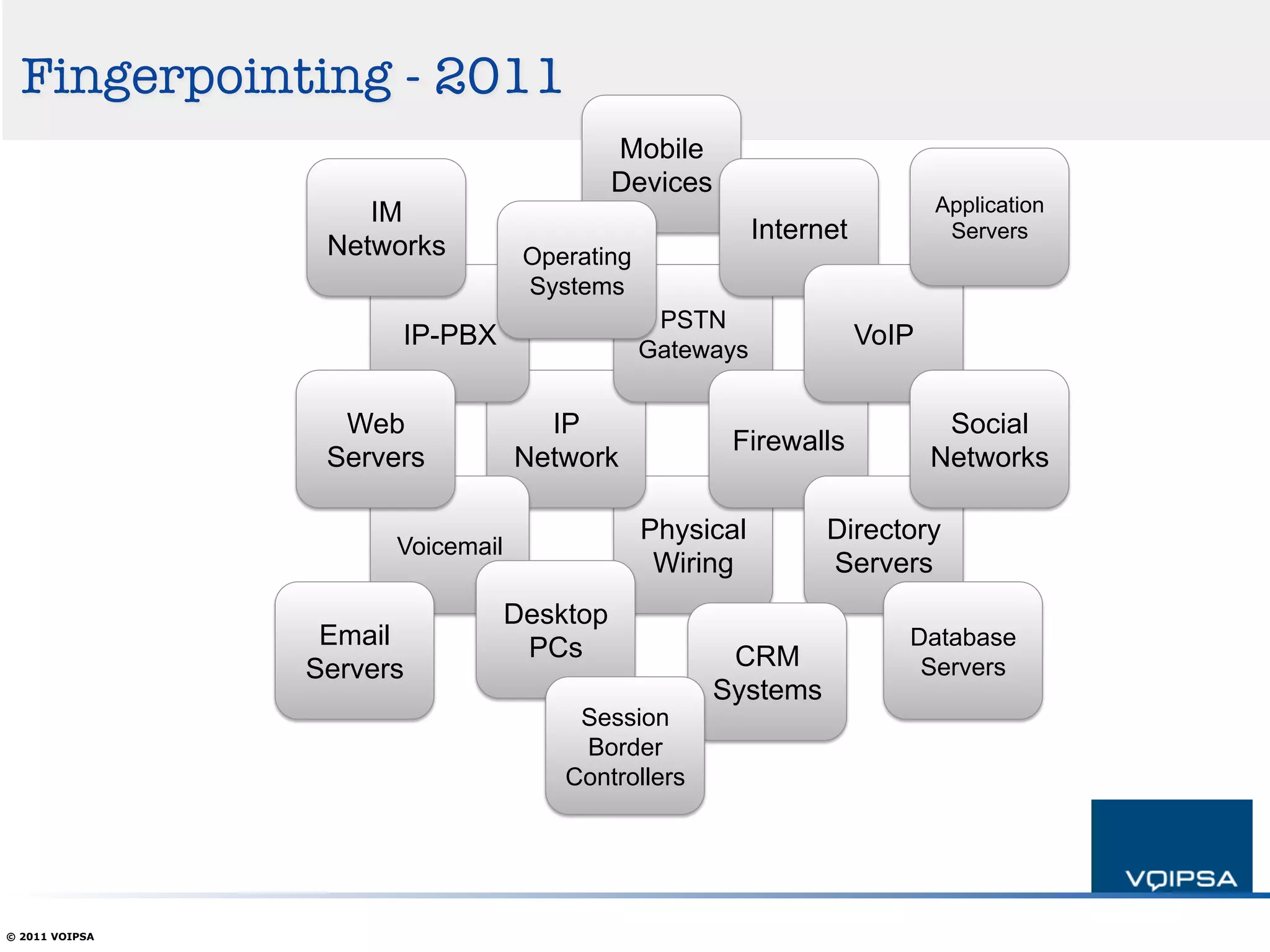
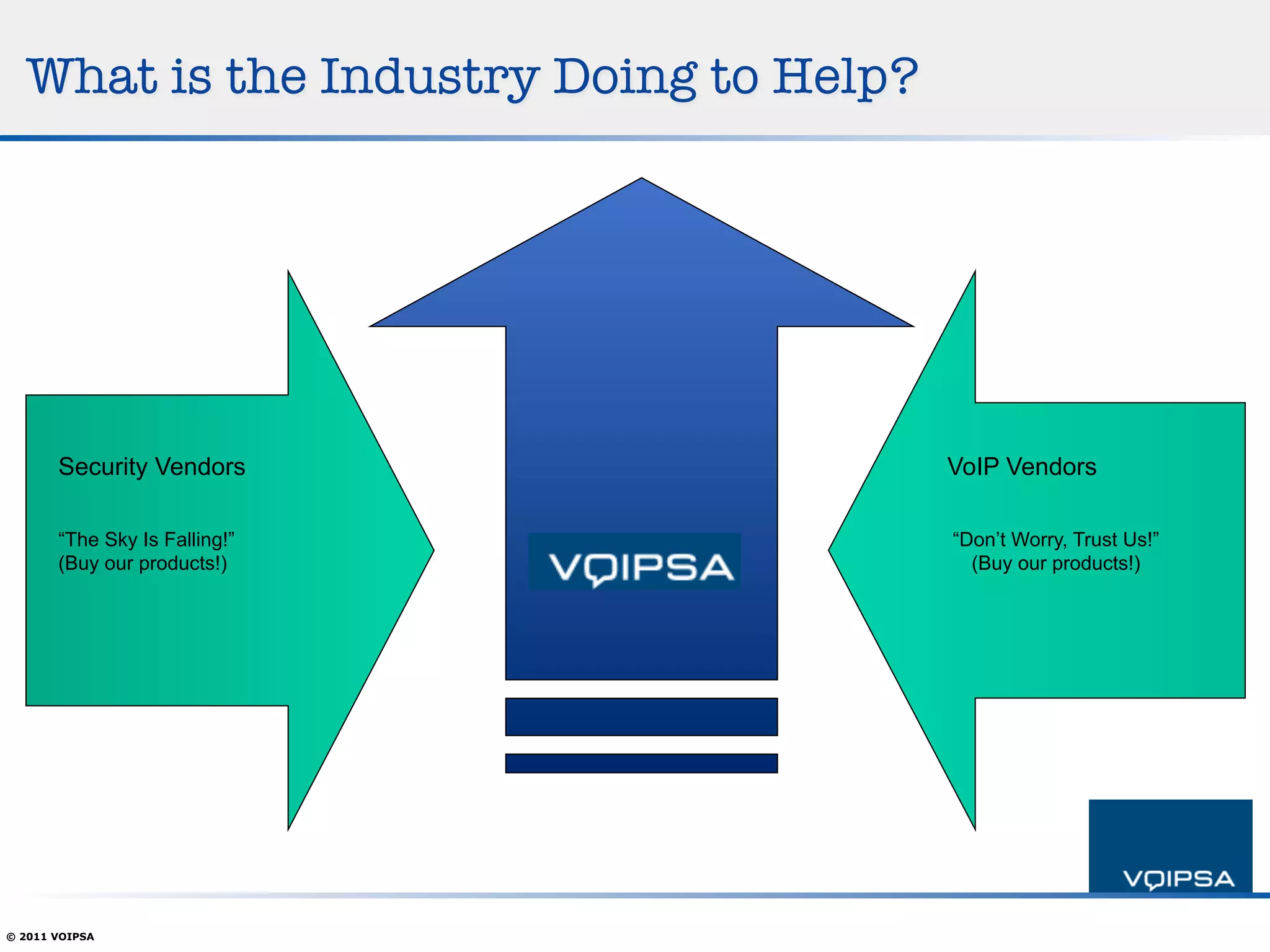
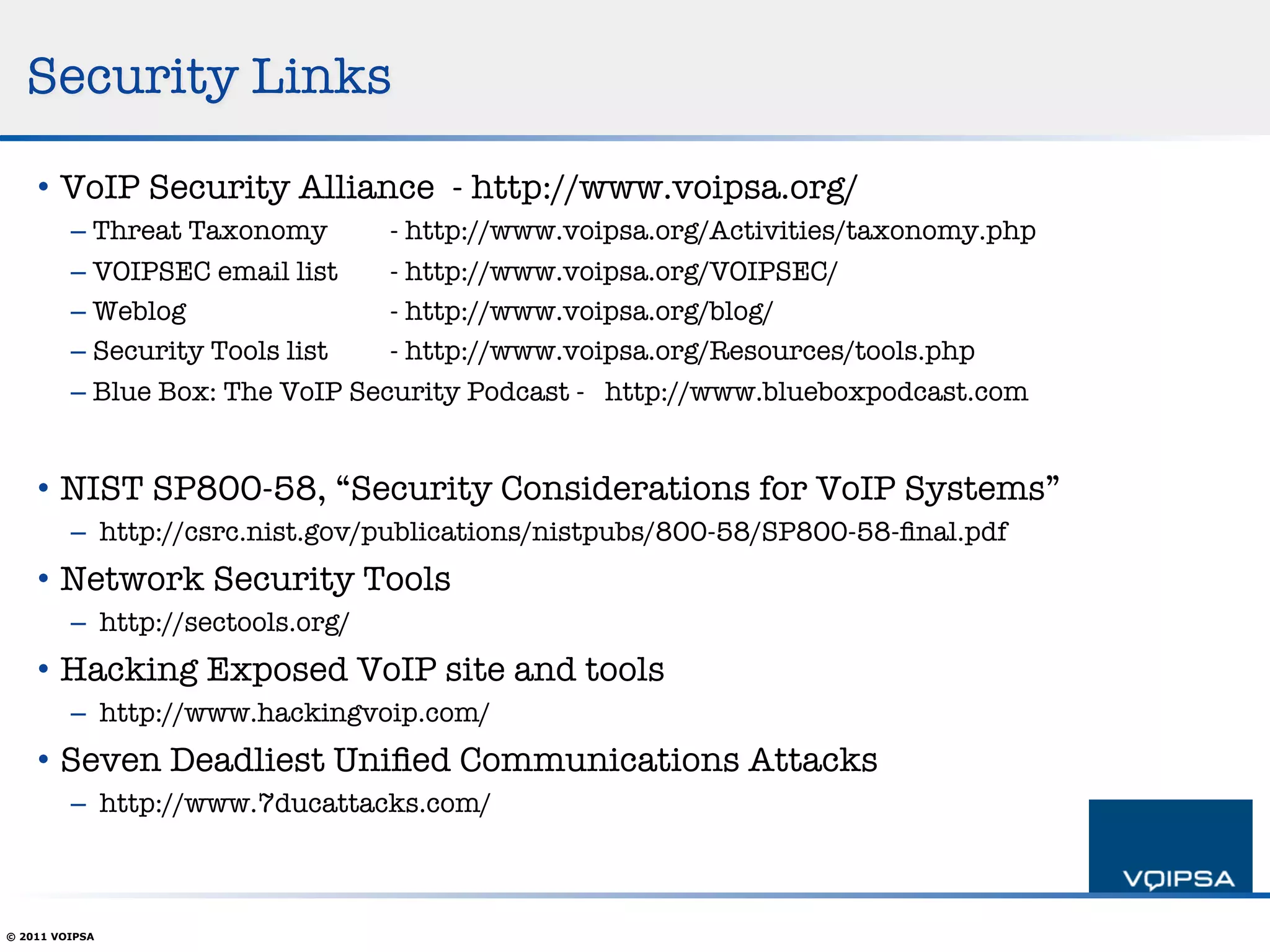
The document discusses the current state of VoIP security, highlighting a general lack of concern among users despite the presence of security measures like TLS and SRTP. It addresses the complexity and finger-pointing in troubleshooting and identifies challenges such as toll fraud and the evolution of attacks. The author emphasizes the need for improved security practices, user education, and proactive measures in the industry to enhance VoIP security.