5556125WhiteHLSS154Midterm.docxby freddie whiteSubmis.docx
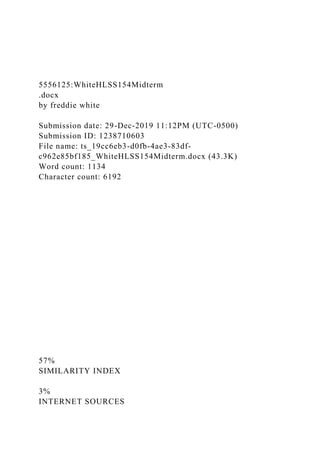
5556125:WhiteHLSS154Midterm .docx by freddie white Submission date: 29-Dec-2019 11:12PM (UTC-0500) Submission ID: 1238710603 File name: ts_19cc6eb3-d0fb-4ae3-83df-c962e85bf185_WhiteHLSS154Midterm.docx (43.3K) Word count: 1134 Character count: 6192 57% SIMILARITY INDEX 3% INTERNET SOURCES 2% PUBLICATIONS 57% STUDENT PAPERS 5556125:WhiteHLSS154Midterm.docx ORIGINALITY REPORT MATCH ALL SOURCES (ONLY SELECTED SOURCE PRINTED) 59% Submitted to American Public University System Student Paper 31% Submitted to American Public University System on 2015-02-22 31% Submitted to American Public University System on 2016-05-26 26% Submitted to American Public University System on 2016-10-31 22% Submitted to American Public University System on 2018-10-22 19% Submitted to American Public University System on 2015-11-02 19% Submitted to American Public University System on 2018-01-01 6% Submitted to American Public University System on 2017-07-03 4% Submitted to American Public University System on 2015-04-26 4% Submitted to American Public University System on 2015-11-26 4% Submitted to American Public University System on 2016-03-27 4% Submitted to American Public University System on 2016-05-29 4% Submitted to American Public University System on 2019-09-01 4% Submitted to American Public University System on 2016-10-02 3% Submitted to American Public University System on 2016-03-27 3% Submitted to American Public University System on 2017-06-24 3% Submitted to American Public University System on 2015-12-22 3% Submitted to American Public University System on 2018-10-29 3% Submitted to American Public University System on 2018-09-30 3% Submitted to American Public University System on 2016-08-28 3% Submitted to American Public University System on 2016-03-28 3% Submitted to American Public University System on 2016-06-21 3% Submitted to American Public University System on 2015-02-01 3% Submitted to American Public University System on 2016-01-31 3% Submitted to American Public University System on 2017-05-01 2% Submitted to American Public University System on 2018-04-01 2% Submitted to American Public University System on 2016-12-04 2% Submitted to American Public University System on 2016-01-31 2% Submitted to American Public University System on 2016-01-03 2% Submitted to American Public University System on 2015-07-26 1% Submitted to American Public University System on 2015-11-24 1% Submitted to American Public University System on 2016-05-01 1% Submitted to American Public University System on 2016-04-30 1% Submitted to American Public University System on 2015-11-01 1% Submitted to American Public University System on 2015-11-29 1% Submitted to American Public University System on 2015-03-24 1% Submitted to American Public University System on 2016-07-31 Exclude quotes Off Exclude bibliography Off Exclude matches Off 5556125:WhiteHLSS154Midterm.docx PAGE 1 Missing "," Rev ...
Recommended
Recommended
More Related Content
Similar to 5556125WhiteHLSS154Midterm.docxby freddie whiteSubmis.docx
Similar to 5556125WhiteHLSS154Midterm.docxby freddie whiteSubmis.docx (20)
More from blondellchancy
More from blondellchancy (20)
Recently uploaded
Recently uploaded (20)
5556125WhiteHLSS154Midterm.docxby freddie whiteSubmis.docx
- 1. 5556125:WhiteHLSS154Midterm .docx by freddie white Submission date: 29-Dec-2019 11:12PM (UTC-0500) Submission ID: 1238710603 File name: ts_19cc6eb3-d0fb-4ae3-83df- c962e85bf185_WhiteHLSS154Midterm.docx (43.3K) Word count: 1134 Character count: 6192 57% SIMILARITY INDEX 3% INTERNET SOURCES
- 2. 2% PUBLICATIONS 57% STUDENT PAPERS 5556125:WhiteHLSS154Midterm.docx ORIGINALITY REPORT MATCH ALL SOURCES (ONLY SELECTED SOURCE PRINTED) 59% Submitted to American Public University System Student Paper 31% Submitted to American Public University System on 2015-02-22 31% Submitted to American Public University System on 2016-05-26 26% Submitted to American Public University System on 2016-10-31 22% Submitted to American Public University System on 2018-10-22 19% Submitted to American Public University System on 2015-11-02 19% Submitted to American Public University System on 2018-01-01
- 3. 6% Submitted to American Public University System on 2017-07-03 4% Submitted to American Public University System on 2015-04-26 4% Submitted to American Public University System on 2015-11-26 4% Submitted to American Public University System on 2016-03-27 4% Submitted to American Public University System on 2016-05-29 4% Submitted to American Public University System on 2019-09-01 4% Submitted to American Public University System on 2016-10-02 3% Submitted to American Public University System on 2016-03-27 3% Submitted to American Public University System on 2017-06-24 3% Submitted to American Public University System on 2015-12-22 3% Submitted to American Public University System on 2018-10-29
- 4. 3% Submitted to American Public University System on 2018-09-30 3% Submitted to American Public University System on 2016-08-28 3% Submitted to American Public University System on 2016-03-28 3% Submitted to American Public University System on 2016-06-21 3% Submitted to American Public University System on 2015-02-01 3% Submitted to American Public University System on 2016-01-31 3% Submitted to American Public University System on 2017-05-01 2% Submitted to American Public University System on 2018-04-01 2% Submitted to American Public University System on 2016-12-04 2% Submitted to American Public University System on 2016-01-31 2% Submitted to American Public University System on 2016-01-03
- 5. 2% Submitted to American Public University System on 2015-07-26 1% Submitted to American Public University System on 2015-11-24 1% Submitted to American Public University System on 2016-05-01 1% Submitted to American Public University System on 2016-04-30 1% Submitted to American Public University System on 2015-11-01 1% Submitted to American Public University System on 2015-11-29 1% Submitted to American Public University System on 2015-03-24 1% Submitted to American Public University System on 2016-07-31 Exclude quotes Off Exclude bibliography Off Exclude matches Off 5556125:WhiteHLSS154Midterm.docx PAGE 1
- 6. Missing "," Review the rules for using punctuation marks. PAGE 2 Article Error You may need to use an article before this word. PAGE 3 P/V You have used the passive voice in this sentence. You may want to revise it using the active voice. Prep. You may be using the wrong preposition. S/V This subject and verb may not agree. Proofread the sentence to make sure the subject agrees with the verb. P/V You have used the passive voice in this sentence. You may want to revise it using the active voice. PAGE 4 Article Error You may need to remove this article. Sp. This word is misspelled. Use a dictionary or spellchecker when you proofread your work. P/V You have used the passive voice in this sentence. You may want to revise it using the active voice. Verb This verb may be incorrect. Proofread the sentence to make sure you have used the correct form of the verb. P/V You have used the passive voice in this sentence. You may
- 7. want to revise it using the active voice. Article Error You may need to use an article before this word. PAGE 5 P/V You have used the passive voice in this sentence. You may want to revise it using the active voice. Run-on This sentence may be a run-on sentence. Missing "," Review the rules for using punctuation marks. Article Error You may need to remove this article. PAGE 6 Missing "," Review the rules for using punctuation marks. PAGE 7 5556125:WhiteHLSS154Midterm.docxby freddie white5556125:WhiteHLSS154Midterm.docxORIGINALITY REPORTMATCH ALL SOURCES (ONLY SELECTED SOURCE PRINTED)5556125:WhiteHLSS154Midterm.docx Running Head: CLOUD FORENSICS 2 CLOUD FORENSICS 2 Cloud Forensics: Name: Institution: Date:
- 8. CLOUD FORENSICS The current trend of the ever-increasing dependency on cloud computing indicates that despite the lack of immediate need for the utilization of cloud forensics’ features, future dependence is to a great extent guaranteed (Pichan et al, 2015). Cloud computing is at its natal stages of development, though the possibility of exponential extrapolation is imminent and therefore the need for development of an appropriate cloud forensics systems to cater for the cloud computing needs when they arise (Chen et al, 2019). The significance of security in computing and associated systems is of utter importance to the success of these undertakings. It is as a result of the noticeable opportunities existent in the field of cloud forensics that makes it of great importance. The existing opportunities in the cloud forensics include, the abundance of data available and continuously being availed for the development of the system as well as the possibility for further and greater cost optimization (Alex et al, 2017). It is due to these parameters that cloud forensics is considered important going forward in the field of computing and ultimately humanity. References Alex, M. E., & Kishore, R. (2017). Forensics framework for cloud computing. Computers & Electrical Engineering, 60, 193- 205. Retrieved from: http://isiarticles.com/bundles/Article/pre/pdf/155769.pdf Chen, L., Takabi, H., & Le-Khac, N. A. (Eds.). (2019). Security, Privacy, and Digital Forensics in the Cloud. John Wiley & Sons. Retrieved from: https://www.wiley.com/en- us/Security%2C+Privacy%2C+and+Digital+Forensics+in+the+C loud-p-9781119053286 Pichan, A., Lazarescu, M., & Soh, S. T. (2015). Cloud forensics: Technical challenges, solutions and comparative analysis. Digital investigation, 13, 38-57. Retrieved from: https://espace.curtin.edu.au/handle/20.500.11937/33937
- 9. CLOUD FORENSICS Security measures Definition The forensics is the application of digital forensics science in the cloud computing environment. technically, it consist of hybrid different approaches for the generation of digital evidence. It involves interactions among the clouds for facilitation among internal and external investigation. It is considered as legal implication of the tenant situation. cloud computing The delivery of cloud computing as service opposed to the product with the three types: Saas (Software as a services) Paas (Platform as a services) Iaas (Infrastructure as a services) Importance of cloud The significance of security in computing and associated systems is of utter importance to the success of these undertakings. It is as a result of the noticeable opportunities existent in the field of cloud forensics that makes it of great importance. It is very important in Social media Communications Traditional route Identification
- 10. Collection Organization Presentation Opportunities The existing opportunities in the cloud forensics include, The abundance of data available and continuously being availed for the development of the system. Possibility for further and greater cost optimization CONFLICT IN CLOUD CLOUD Location independence Rapid elasticity FORENSIC Discovery of computable jurisdiction Data reliability Multi-tasking General abstract Data structure
- 11. Evidence preservation data integrity Chain of custody Chain of attributes CHALLENGES FACE BY CLOUD There are different challenges faced by the cloud forensics such as: Storage system is no more local Every cloud server contains files from different users. Even if the data relates to a specific identification, separating it from other users data is considered as more difficult. Other than corporate social responsibility there are no usual evidence which relates to the specific data files. Healthcare, business, or any other security which relates to the data. Running head: FACTORS PSYCHOLOGICAL AND BEHAVIORS OF TERRORISM 1 FACTORS PSYCHOLOGICAL AND BEHAVIORS OF TERRORISM 8FACTORS OF PSYCHOLOGY AND BEHAVIORS OF TERRORISM Freddie White American Military University
- 12. Abstract The very being of terrorism and the configuration of terrorists themselves are a forever changing evolving subject of inquisition throughout the globe. Also, during this assignment, the behavioral and psychological factors of terrorism are one of the things that will be described. I will mainly be focusing on the suicide bomber by the name of Asmar Latin Sani, the culprit behind the 2003 Marriott Hotel bombing. Finally, a brief discussion of the psychological and behavioral factors of terrorist organizations will be discussed. FACTORS OF PSYCHOLOGY AND BEHAVIORS OF TERRORISM It is a common mistake to believe that all supporters and members of terror acts start out portraying an active role as the ones who are generally mentioned by the media. Most start as just supporters of the Muslim/Islamic movement for the fight against the Christian superpower, also known as the western world. The convergence of terrorists can range from individuals such as doctors to university professors to the local mailman. A lot of things can be aforementioned for the psychological and behavioral factors of terrorism. Definitely, one thing that cannot be argued is that terrorism brings thoughts of trepidation to many individuals. As acknowledged before, “The West,” with the hope of strengthening Muslim’s influence and power around the globe, It is said that to understand such member falls into two categories, that is the "committed actor" and the "sympathizer." You may find yourself asking why individuals suffer from fear at the sounds and sights of terrorism; this process is called psychological behavior. A few of the ways how terrorist and terrorism enroot the psychological behavior of dread in the psyche of individuals is in fostering a sense of being exposed and unredeemable, in showing the sheer incompetence of the
- 13. authorities or law, destroying a sense of safety and defense, and in inciting abnormal reactions from people and authorities. Terrorists and individuals claiming to be terrorists are also affected by psychological behavior, and Osama Bin Laden made a point to voice his words in saying that in the terrorist group itself, the constituents suffered from a psychological mindset of defeat. The study of psychological behavior is commonly brought on or brings on another component called behavioral psychology. “It is rather difficult to study the prevalence of psychopathology and maladaptive personality traits in terrorist populations.”( Borum) Behavioral psychology is stated as to how people retort to a psychological element. In the paragraph above, some examples were discussed in how terrorists and terrorism inculcate the psychological behavior of fearfulness. After a terrorist attack, other than fear, a few behavioral, psychological factors are that the people take themselves from some of their usual vocations while becoming angered, or becoming indisposed. The fear that terrorism instills, as well as these other behavioral, psychological factors, helps with how terrorists communicate and recruit, especially in how a terrorist organization spreads its ideology and gets its message across to society. Impatient adolescent recruits who do not retain an in-depth understanding of Islam and Islamic views and see their aged leaders as idle men who are not interested in Jihad any more are easily manipulated; this is especially true for individuals such as Asmar Latin Sani. The base causes of systematic terror attacks and extremist movements are backwardness, unfairness, illiteracy, poverty, inequality in politics and tutilage, and the perversion of religious instructions. In most cases, individuals are motivated to enlist into a terrorist organization by an appetency to use their distinct skills, such as bomb-making and ordnance handling. Indifference, articulate individuals, join terrorist groups in an attempt to express their religious or political views to call for change. Also, people
- 14. released from being incarcerated may resort to joining a terrorist organization. This was hearsay about some of the prisoners released at Guantanamo Bay. Even though there are different reasons for joining a terrorist organization, the result of this continuous methodology is that the individual eventually joins a terrorist group. Too often, when terrorism is talked about, it is often thought of as been carried out only by men, but too often, women are left out. Countless women play an essential role in terrorism. The ultimate recognized course of approach to terrorism for female terrorists is through political extremism. An abundance of juvenile Iraqi women was radicalized by Al Queda and later end up joining various terrorist groups and carrying out terror attacks. In terms of the psychology of defeat, it is a choice utilized by top terrorist organizers who chose to utilize psychology as a way of conquering our nation due to an absence of conventional artillery. They believe that if they could ruin our nation from the inside, that we would leave the Islamic nations. They calculated that we, as a nation, would psychologically flee from the dreadfulness they were inflicting on us. Al Queada's attempt to destroy the United States of America is an example of how they wanted to overmatch our nation psychologically. They figured by doing so would expose our vulnerabilities by conquering our infrastructure and murdering unjustly. As a result, we would be involuntarily forced to retaliate against them in their nation, and he would then look to annihilate us. They figured they would then cause us to leave his nation as the Russians did, broke and defeated. Once we as a nation had experienced the atrociousness of battle in Afghanistan, they believed that we, too, would depart in defeat—again, just as they had seen in Somalia, and just as they believed it happened in that Asian country, we dare not speak of. In their psyche, they felt that their side was based on brawny moral principles and Islamic beliefs. Their objective was not to dominate our armed forces but rather to decimate our nations psychologically.
- 15. There is no absolute answer as to why people commit terror attacks. There are many reasons for their decisions; nonetheless, psychologists and scientists have started to recognize specific customs for them committing terror attacks based on religious or political beliefs, lack of character, or a feeling of belonging. Understanding the psychological behavior of terrorism and the behaviors associated with it may help prevent future terror attacks like the one that occurred on September 11th. Furthermore, in order for extremists to proceed with their cause and increase recruitment, they may turn to various electronic media social systems to promote their cause. We need to use social media to our advantage against the terrorist. Forthcoming psychological analysis of terrorism may shed light on psychological paradigms on individual desires to commit terrorist attacks based on several political and religious convictions. References Boram, R. M. (2004). Psychology of terrorism. Pages 29 - 30. Horgan, J. (2008). Pathways and Roots to Routes. Victoroff, J (2005). The Mind of the Terrorist Akhtar, S. 1999. The psychodynamic dimension of terrorism. Psychiatric Annals 29:350-355.