Get fully solved MBA assignments
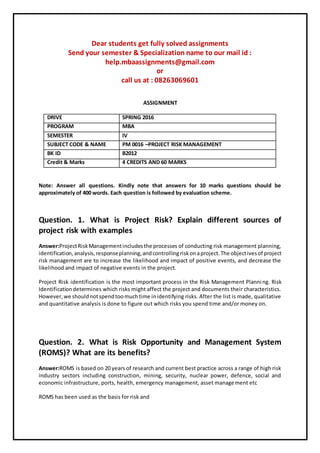
- 1. Dear students get fully solved assignments Send your semester & Specialization name to our mail id : help.mbaassignments@gmail.com or call us at : 08263069601 ASSIGNMENT DRIVE SPRING 2016 PROGRAM MBA SEMESTER IV SUBJECT CODE & NAME PM 0016 –PROJECT RISK MANAGEMENT BK ID B2012 Credit & Marks 4 CREDITS AND 60 MARKS Note: Answer all questions. Kindly note that answers for 10 marks questions should be approximately of 400 words. Each question is followed by evaluation scheme. Question. 1. What is Project Risk? Explain different sources of project risk with examples Answer:ProjectRiskManagementincludesthe processes of conducting risk management planning, identification,analysis,responseplanning,andcontrollingriskonaproject.The objectivesof project risk management are to increase the likelihood and impact of positive events, and decrease the likelihood and impact of negative events in the project. Project Risk identification is the most important process in the Risk Management Planning. Risk Identificationdetermines which risks might affect the project and documents their characteristics. However,we shouldnotspendtoomuchtime inidentifying risks. After the list is made, qualitative and quantitative analysis is done to figure out which risks you spend time and/or money on. Question. 2. What is Risk Opportunity and Management System (ROMS)? What are its benefits? Answer:ROMS is based on 20 years of research and current best practice across a range of high risk industry sectors including construction, mining, security, nuclear power, defence, social and economic infrastructure, ports, health, emergency management, asset management etc ROMS has been used as the basis for risk and
- 2. Question. 3. 1. Using Internet, identify a project and list down all the activities and milestonesof a project and the activity risks associated with these milestones. Answer:The purpose of this process is to identify the specific tasks needed to be done in order to produce the project's deliverables. This needs to be done in sufficient detail to estimate what resources and time will be required to complete them. The main inputs are the scope baseline consisting of the approved project scope statement, the work breakdown structure, and the WBS dictionary. 2. Using Internet, identify a project and the activity risks associated with it.Categorise the risks into three groups: controllable known, uncontrollableknown and unknown. Find out the percentage of “unknowns” in total risks atthe beginning and towards the end of the project. Answer:The work package is the lowest level of the WBS is achieved when the work can be accuratelyestimated(bothcostandduration) andcan be managed by one individual. The key word here is 'managed', although the work package can be managed by one person, the actual work within the work package may be completed by several people. For example, One individual could manage Question. 4. What are the sources of resource risks? Answer: Resource risksrepresentlessthanone-thirdof the recordsinthe PERIL database. There are three categories of resource risk: people, outsourcing, and money. People risks arise within the projectteam.Outsourcingrisks are due to the use of people and services outside the project team to performcritical projectwork.The thirdcategory,money,is something of an anomaly in the data, as veryfewof the problemsreportedwere primarilyaboutfunding.Moneyis,however, a key factor in many of the people and outsourcing problems, and Question. 5. What are different types of scope risks?
- 3. Answer: While scope risksrepresentedroughlyone-third of the data in the Project Experience Risk Information Library (PERIL) database, they account for close to half of the total impact. The two broad categories of scope risk in PERIL relate to Question. 6. Explain the three point estimates used in quantitative risk analysis. Answer:The three-point estimation technique is used in management and information systems applications for the construction of an approximate probability distribution representing the outcome of future events, based on very limited information. While the distribution used for the approximation might be a normal distribution, this is not always so and, for example a triangular distribution might be used, depending on the Dear students get fully solved assignments Send your semester & Specialization name to our mail id : help.mbaassignments@gmail.com or call us at : 08263069601
