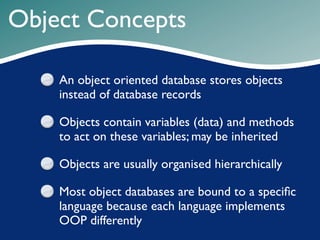
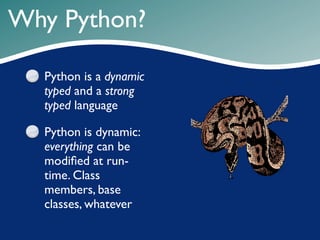
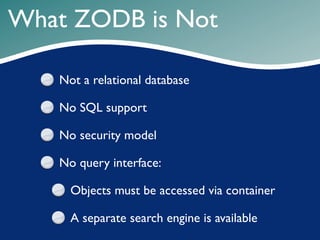
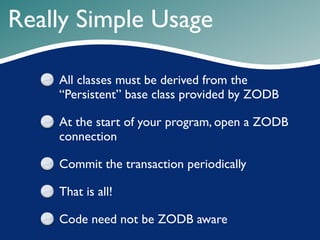
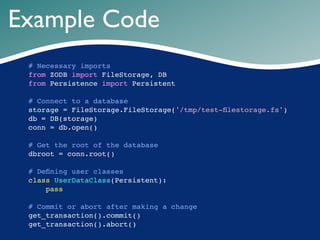
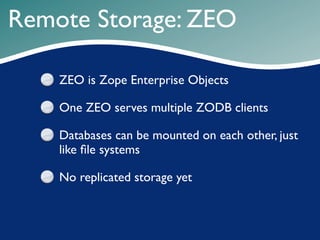
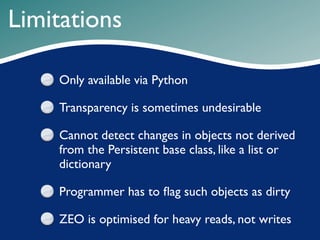
This document introduces ZODB, the Zope Object Database, highlighting its advantages over relational databases, such as handling complex data and offering high performance with transparent operations. It details ZODB's mechanics, including the necessity of deriving from a 'persistent' base class and utilizing Python for dynamic typing and strong encapsulation of data. Limitations are noted, such as only being accessible via Python and the potential lack of transparency for certain objects.