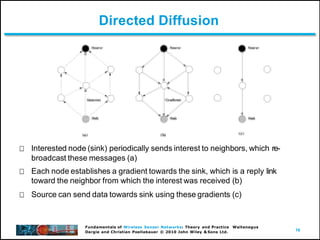
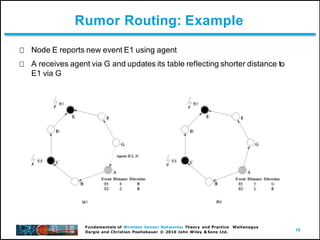
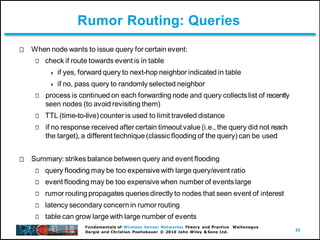
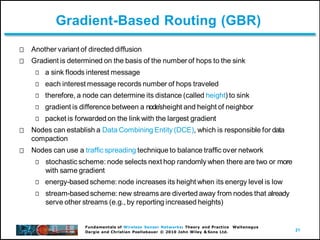
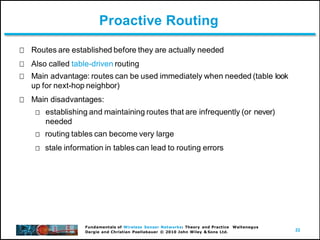
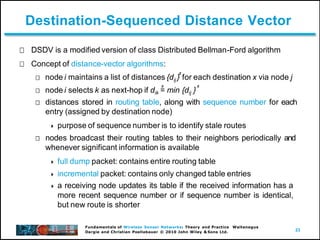
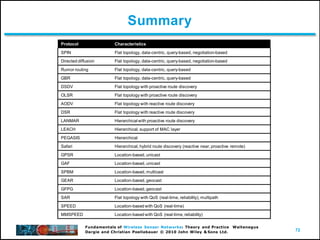
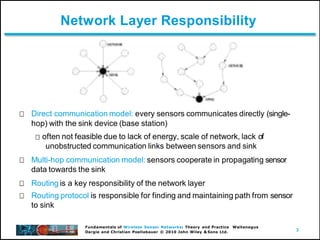
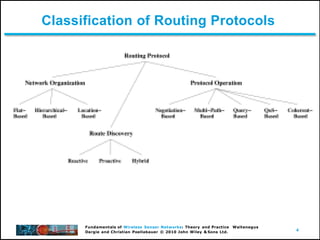
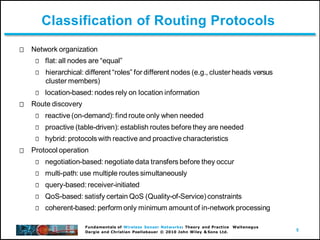
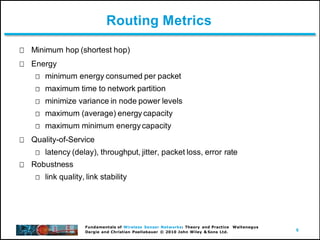
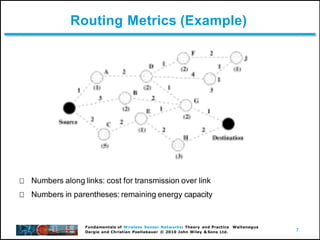
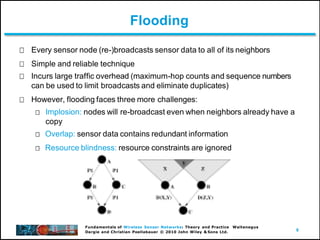
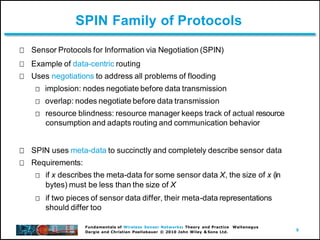
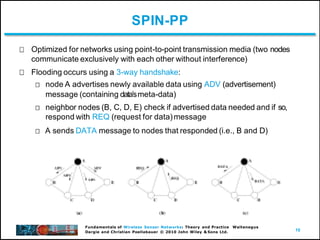
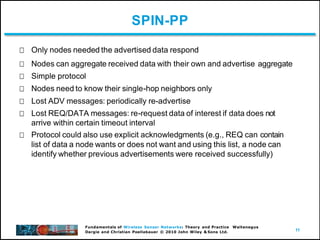
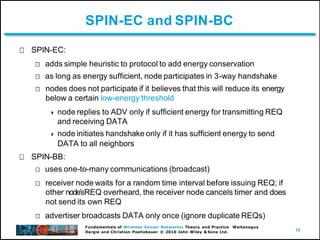
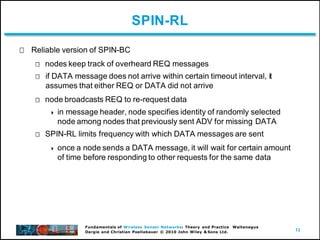
The document discusses routing protocols for wireless sensor networks. It describes how routing is a key responsibility of the network layer to find and maintain paths from sensors to a sink. Various routing protocols are classified based on network organization, route discovery approach, and operation. Examples of routing protocols discussed include flooding, SPIN, directed diffusion, and rumor routing. SPIN protocols use data-centric routing and negotiations to address problems with basic flooding. Directed diffusion sets up gradients within the network to direct sensor data towards interested sinks.
![15
Fundamentals of Wireless Sensor Networks: Theory and Practice Waltenegus
Dargie and Christian Poellabauer © 2010 John Wiley & Sons Ltd.
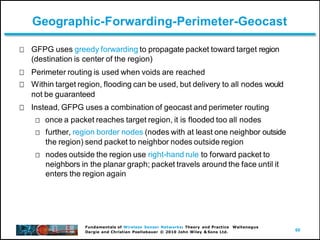
Directed Diffusion: Attribute-Value Pairs
Simple vehicle-tracking application
type = vehicle
interval = 20ms
duration = 10s
// detect vehiclelocation
// send data every 20 ms
// perform task for 10 s
rect = [-100,-100,200,200] // from sensors withinrectangle](https://image.slidesharecdn.com/wsnnetwlayer-221220050308-db0ece84/85/WSN-netw-layer-pptx-15-320.jpg)