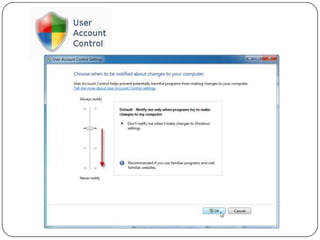
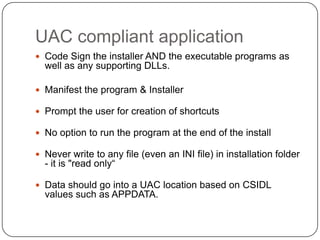
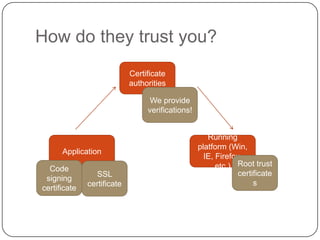
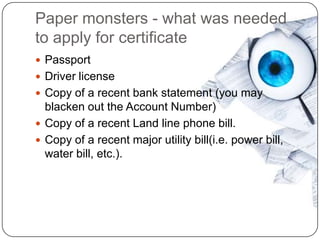
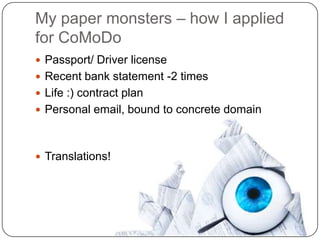
The document discusses code signing and user access control (UAC) compliance. It recommends signing installers, executables, and DLLs with certificates. It also recommends prompting users for shortcuts and writing data to standardized locations rather than the installation folder. The document then discusses how certificate authorities work and the process for obtaining certificates, including providing documentation. It notes a past security incident with a certificate authority and demonstrates obtaining a certificate.