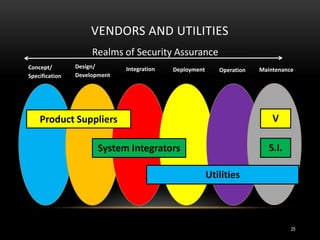
Regulators are tasked with approving utility capital expenditures and rate increases to recoup costs. With the smart grid, regulators want to understand utility security strategies, risks, personnel, and vendor relationships. Regulators ask utilities questions about security plans, vulnerability assessments, risk management processes, and staff training. They want to ensure expenditures are prudent and solutions are cost-effective while maintaining security accountability across utilities and vendors.