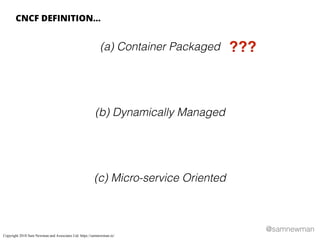
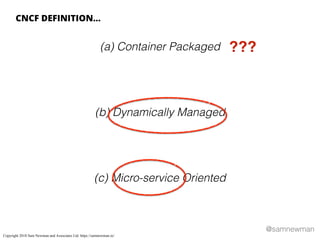
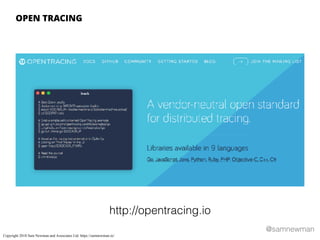
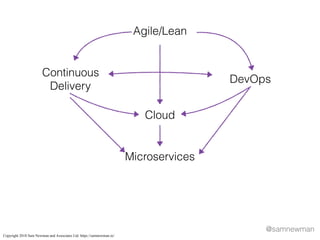
The document discusses the concept of cloud-native applications, emphasizing their characteristics, including being containerized, dynamically managed, and microservice-oriented. It also examines the benefits and challenges associated with adopting cloud-native technologies, mentioning the importance of platforms and standards in leveraging cloud capabilities. Furthermore, the text advises organizations on the considerations and skills required for successful cloud-native transformations.