What are the best tools used in cybersecurity in 2023.pdf
•
0 likes•8 views
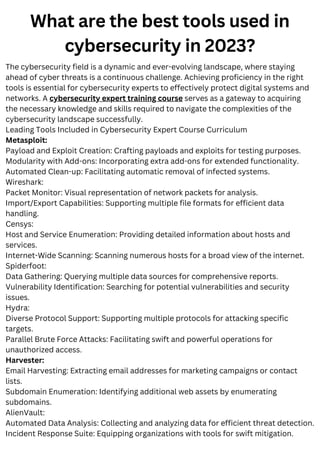
The document discusses the best tools used in cybersecurity in 2023. It describes several leading tools that are commonly included in cybersecurity expert training courses, such as Metasploit, Wireshark, Censys, Spiderfoot, Hydra, Harvester, AlienVault, Eagle OSINT, Nmap, Nessus, and Splunk. These tools aid in tasks like payload creation, packet analysis, host and service enumeration, data gathering, vulnerability identification, brute force attacks, email harvesting, subdomain enumeration, automated data analysis, incident response, OSINT, port scanning, vulnerability scanning, and real-time monitoring. The document also promotes the Tsaaro Academy cybersecurity training course for becoming an expert in security operations and
Report
Share
Report
Share
Download to read offline
Recommended
Security and-visibility

Digitization and increased mobility have complicated network visibility and security. Threats are more numerous, complex, and use encryption to evade detection. Cisco Stealthwatch provides holistic security through network-based visibility and analytics. It transforms networks into security sensors to see all traffic, contain threats, and detect encrypted threats. Advanced machine learning and behavioral modeling detect anomalies and threats without relying on endpoint agents. Stealthwatch integrates with Cisco Identity Services Engine to rapidly quarantine infected hosts.
Ending the Tyranny of Expensive Security Tools

A long time ago, in a galaxy far far away, AV was invented. Then firewalls and IDS and SIEM and NAC and DLP and on and on. With all these products, it seems like a career in information security is really more about managing tools than defeating a galactic empire of hackers and miscreants. But like the Rebel Alliance, you can take back your enterprise, because many of our existing monitoring systems and network devices also have security functionality. Moreover, there are many excellent open source applications that work just as well as commercial ones.
Ending the Tyranny of Expensive Security Tools

You don't always have to buy something expensive to provide security functionality. After all, a security professionals job isn't to manage tools, but solve problems. This presentation talks about how to use open source and existing monitoring tools to meet an organization's security needs.
AI for Cybersecurity Innovation

I will talk about innovation in the area of cyber security analytics - developing machine learning methods to detect and block cyber attacks (e.g. detecting ransomware within 4 seconds of execution and killing the underlying processes). Rather than just focusing on this as a 'black box', I'll pull it apart and talk about how we can use these methods to enable security practitioners (SOC/CIRT etc) to ask and answer questions about 'what' and 'why' these methods are flagging attacks. I'll also talk about resilience of machine learning methods to manipulation and adversarial attacks - how stable these approaches are to diversity and evolution of malware for example.
Network Vulnerability and Patching

This document discusses network vulnerability scanning and patching. It begins by introducing network penetration testing and vulnerability scanning as important ways to identify weaknesses before hackers can exploit them. It then covers different types of scanning like network scanning, port scanning, web application scanning and database security scanning. The document focuses on using the GFI LanGuard software to conduct network scanning and vulnerability checks on a company's network to block backdoors, close loopholes and implement patching to reduce hacking risks.
Using Splunk for Information Security

This document provides an overview of a presentation on security monitoring and analytics using Splunk. The presentation covers using Splunk Enterprise for security operations like alert management and incident response. It also covers using Splunk User Behavior Analytics to detect anomalies and threats using machine learning. The presentation highlights new features in Splunk Enterprise Security 4.1 like prioritizing investigations and expanded threat intelligence, and new features in Splunk UBA 2.2 like enhanced security analytics and custom threat modeling. It demonstrates integrating UBA results into the Splunk Enterprise Security workflow for faster investigation of advanced threats.
Using Splunk for Information Security

This document provides an overview of a presentation on security monitoring and analytics using Splunk. The presentation covers using Splunk Enterprise for security operations like alert management and incident response. It also covers using Splunk User Behavior Analytics to detect anomalies and threats using machine learning. The presentation highlights new features in Splunk Enterprise Security 4.1 like prioritizing investigations and expanded threat intelligence, and new features in Splunk UBA 2.2 like enhanced security analytics and custom threat modeling. It demonstrates integrating UBA results into the Splunk Enterprise Security workflow for faster investigation of advanced threats.
NSA and PT

The document provides information about the Certified Computer Security Analyst (CCSA) program and training. It discusses the trainer, Semi Yulianto's qualifications and experience working with various security training and consulting organizations. It also lists some of the key topics covered in the CCSA training program, including vulnerabilities assessment, penetration testing methodology, security tools, and investigating vulnerabilities.
Recommended
Security and-visibility

Digitization and increased mobility have complicated network visibility and security. Threats are more numerous, complex, and use encryption to evade detection. Cisco Stealthwatch provides holistic security through network-based visibility and analytics. It transforms networks into security sensors to see all traffic, contain threats, and detect encrypted threats. Advanced machine learning and behavioral modeling detect anomalies and threats without relying on endpoint agents. Stealthwatch integrates with Cisco Identity Services Engine to rapidly quarantine infected hosts.
Ending the Tyranny of Expensive Security Tools

A long time ago, in a galaxy far far away, AV was invented. Then firewalls and IDS and SIEM and NAC and DLP and on and on. With all these products, it seems like a career in information security is really more about managing tools than defeating a galactic empire of hackers and miscreants. But like the Rebel Alliance, you can take back your enterprise, because many of our existing monitoring systems and network devices also have security functionality. Moreover, there are many excellent open source applications that work just as well as commercial ones.
Ending the Tyranny of Expensive Security Tools

You don't always have to buy something expensive to provide security functionality. After all, a security professionals job isn't to manage tools, but solve problems. This presentation talks about how to use open source and existing monitoring tools to meet an organization's security needs.
AI for Cybersecurity Innovation

I will talk about innovation in the area of cyber security analytics - developing machine learning methods to detect and block cyber attacks (e.g. detecting ransomware within 4 seconds of execution and killing the underlying processes). Rather than just focusing on this as a 'black box', I'll pull it apart and talk about how we can use these methods to enable security practitioners (SOC/CIRT etc) to ask and answer questions about 'what' and 'why' these methods are flagging attacks. I'll also talk about resilience of machine learning methods to manipulation and adversarial attacks - how stable these approaches are to diversity and evolution of malware for example.
Network Vulnerability and Patching

This document discusses network vulnerability scanning and patching. It begins by introducing network penetration testing and vulnerability scanning as important ways to identify weaknesses before hackers can exploit them. It then covers different types of scanning like network scanning, port scanning, web application scanning and database security scanning. The document focuses on using the GFI LanGuard software to conduct network scanning and vulnerability checks on a company's network to block backdoors, close loopholes and implement patching to reduce hacking risks.
Using Splunk for Information Security

This document provides an overview of a presentation on security monitoring and analytics using Splunk. The presentation covers using Splunk Enterprise for security operations like alert management and incident response. It also covers using Splunk User Behavior Analytics to detect anomalies and threats using machine learning. The presentation highlights new features in Splunk Enterprise Security 4.1 like prioritizing investigations and expanded threat intelligence, and new features in Splunk UBA 2.2 like enhanced security analytics and custom threat modeling. It demonstrates integrating UBA results into the Splunk Enterprise Security workflow for faster investigation of advanced threats.
Using Splunk for Information Security

This document provides an overview of a presentation on security monitoring and analytics using Splunk. The presentation covers using Splunk Enterprise for security operations like alert management and incident response. It also covers using Splunk User Behavior Analytics to detect anomalies and threats using machine learning. The presentation highlights new features in Splunk Enterprise Security 4.1 like prioritizing investigations and expanded threat intelligence, and new features in Splunk UBA 2.2 like enhanced security analytics and custom threat modeling. It demonstrates integrating UBA results into the Splunk Enterprise Security workflow for faster investigation of advanced threats.
NSA and PT

The document provides information about the Certified Computer Security Analyst (CCSA) program and training. It discusses the trainer, Semi Yulianto's qualifications and experience working with various security training and consulting organizations. It also lists some of the key topics covered in the CCSA training program, including vulnerabilities assessment, penetration testing methodology, security tools, and investigating vulnerabilities.
INTERFACE by apidays 2023 - Security Exposure Management in API First World, ...

INTERFACE by apidays 2023
APIs for a “Smart” economy. Embedding AI to deliver Smart APIs and turn into an exponential organization
June 28 & 29, 2023
Security Exposure Management in API First World
Sandeep Nain, VP Security and Trust at Carta
------
Check out our conferences at https://www.apidays.global/
Do you want to sponsor or talk at one of our conferences?
https://apidays.typeform.com/to/ILJeAaV8
Learn more on APIscene, the global media made by the community for the community:
https://www.apiscene.io
Explore the API ecosystem with the API Landscape:
https://apilandscape.apiscene.io/
IDS+Honeypots Making Security Simple

Everything you really need to know about IDS (Intrusion Detection Systems) Combining with HoneyPots. Deployment and usage techniques used in the past and today. How to setup and deploy onto any network including the cloud. Reasons why this should be used in all networks. How to bring BIG DATA down to Small Data that is easy to understand and monitor.
It’s all over the news that data breaches occur daily! I asked WHY these hackers can download terabytes of data in timespans of months without being noticed. What are these companies paying their SOC team millions of dollars for? How come all the money is going to devices to prevent breaches and little to none in detecting when they occur? Don’t people know there are only two types of companies “those that been hacked, and those that don’t know they been hacked”. What can I do to detect a breach within seconds on any network scale? I think I figured it out. In my talk you’ll learn how you and your clients can benefit by applying my exclusive techniques, which I’ve successfully deployed. So the next time you get hacked the hacker would not be able to steal all those credit cards and photos of that Halloween party.
Nt2580 Unit 7 Chapter 12

This document discusses conducting a vulnerability assessment. It explains that a vulnerability assessment identifies possible security vulnerabilities in a system. The assessment involves both automated and manual techniques depending on the scope of the organization. The major steps are conducting the assessment, addressing any exposures found, and reporting and remediation. Under conducting the assessment, planning, gathering information, and defining roles and responsibilities are involved. The assessment aims to find and rank vulnerabilities to threats.
Why Penetration Testing Services Cyber51

Our security testing services address numerous information security challenges faced by clients. We assist with early identification of security threats through reviews and vulnerability checks. For existing systems, we provide independent technical reviews and testing to ensure systems are secure. Our experience ensures systems support business security needs comprehensively and robustly.
In-kernel Analytics and Tracing with eBPF for OpenStack Clouds

As the movement of applications from bare metal to the cloud continues, considerations around analytics and tracing are becoming more prevalent for security, monitoring, and accounting. As an open source project under the Linux Foundation, the IO Visor Project is working with the kernel community on extending BPF (eBPF) and is being used by many companies for security, tracing, and analytics. This talk will describe how an OpenStack micro-segmentation framework using eBPF can be utilized for analytics and tracing to secure application workloads. Use cases around application security, intrusion detection using service insertion, identity will be described. While networking is one piece of the solution, sandboxing applications to avoid attacks is also important. We will also touch upon how eBPF technology and a unified policy framework can secure application workloads in areas beyond networking.
CYBER SECURITY CAREER GUIDE CHEAT SHEET

This document provides an overview of topics, technologies, programming languages, tools, certifications, and job roles commonly required in the field of cybersecurity. It lists fundamentals areas like computer science, networking, and cryptography. It also outlines essential security domains including web security, ethical hacking, incident response, policies, and human factors. Finally, it provides steps to get started in cybersecurity, including choosing a specialization, developing skills, and staying up to date in the field.
Dhishant -Latest Resume

This document is a resume for Dhishant Abrol summarizing his professional experience and qualifications. He has over 6 years of experience in information and network security, currently working as a Security Researcher. Previous roles include managing security operations centers and security architectures for clients. He has various technical certifications and skills in areas like vulnerability assessment, malware analysis, compliance, and security tools.
8 Top Cybersecurity Tools.pdf

Top encryption tools like McAfee are popular among business users. McAfee provides full disk encryption for desktops, laptops, and servers. The algorithm uses Advanced Encryption Standard(AES) with 256-bit keys. McAfee AES is certified by US Federal Information Processing Standard. There is also ready integration of multi-layer authentication.
Cisco Connect 2018 Malaysia - Cybersecurity strategy-an integrated approach

The document discusses the importance of integrating security solutions to create an effective security architecture. It outlines how Cisco has integrated its portfolio of security products through sharing threat intelligence, event information, and policy across firewalls, web security, email security, endpoint security, and other solutions. This level of integration helps speed threat detection and response times by automating processes and providing contextual awareness across the network.
Secure Decisions - Cyber Security Sensemaking

Secure Decisions is a company that helps analyze security data and decision processes to enhance cybersecurity. They develop visual analytics tools to help cyber analysts make sense of network and software vulnerability data. Some of their products include tools that visualize wireless network security data, software vulnerabilities from multiple scanners, and network flows and alerts. They also provide consulting services and have developed technologies like a cyber decision support system and a testbed for evaluating network monitoring algorithms. Their goal is to transition research into tools that can help operators in both government and commercial organizations.
Critical Infrastructure Assessment Techniques to Prevent Threats and Vulnerab...

QA&TEST Conference 2011, Spain - Shakeel Ali, 10th International Conference on Software QA and Testing on Embedded Systems
Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.

Simon Wong and Chris Cram, Scalar security experts, discuss how Palo Alto Networks technology disrupts the entire malware kill chain. Attendees will also gain insight on flexible deployment options to better serve their mobile users, and how to get the most out of their Palo Alto Networks deployment.
Cisco Cyber Threat Defense for the Data Center Solution: Cisco Validated Design

This document provides a 3-sentence summary of a 14-page document describing the Cisco Cyber Threat Defense for the Data Center Solution:
The solution uses NetFlow from Cisco switches and devices to provide visibility into data center network traffic. The Lancope StealthWatch System collects and analyzes NetFlow data to detect suspicious activity, while the Cisco Identity Services Engine provides user identity and security group information for context. The overall solution gives security operators enhanced visibility and context to detect threats already operating in the internal network or data center.
Seceon's aiXDR_ Automating Cybersecurity Threat Detection in 2023 - Seceon.pptx

Seceon aiXDR solution is built upon its Open Threat Management (OTM) Platform enabling organizations to detect both signature-based malware with precedence and zero-day threats without precedence, quickly and effectively, thereby thwarting the kill chain and minimizing the extent of damage across business and enterprise environments.
Top Cyber Threat Intelligence Tools in 2021.pdf

Cyber threat intelligence is used for collecting necessary information about new and old threat actors from various sources. The collected data is analyzed, processed, and converted into useful threat intelligence.
https://www.infosectrain.com/courses/certified-threat-intelligence-analyst-ctia-certification-training/
David Patterson IT Security Resumes 2016

Senior cyber security engineer with over 30 years of experience in technical management, hardware engineering, system and network engineering. Experience monitoring, analyzing, migrating, designing, consulting, deploying, troubleshooting and project/technical management of large network systems. Skilled in evaluating system vulnerabilities, compiling analysis, reporting threats, and recommending security improvements.
8 Top Cybersecurity Tools.pptx

This document discusses and summarizes 8 top cybersecurity tools: 1) Encryption, which includes tools like McAfee that provide full disk encryption. 2) Intrusion detection systems that help identify potential security breaches. 3) Virtual private networks that ensure security for users by rerouting connections. 4) Network access control that restricts network access based on authentication and compliance. 5) Security information and event management tools that provide real-time insights into potential threats. 6) DDoS mitigation to detect and block malicious traffic. 7) Vulnerability scanners to identify potential vulnerabilities. 8) Firewalls that control network traffic based on security policies. It concludes that outsourcing cybersecurity needs to an experienced provider
Security operation center (SOC)

The document discusses security operation centers (SOCs) and their functions. It describes what a SOC is and its main purpose of monitoring, preventing, detecting, investigating and responding to cyber threats. It outlines the typical roles in a SOC including tier 1, 2 and 3 analysts and security engineers. It also discusses the common tools, skills needed for each role, and types of SOCs such as dedicated, distributed, multifunctional and virtual SOCs.
클라우드 환경에서의 SIEMLESS 통합 보안 서비스, Alert Logic - 채현주 보안기술본부장, Openbase :: AWS Sum...

클라우드 환경에서의 SIEMLESS 통합 보안 서비스, Alert Logic - 채현주 보안기술본부장, Openbase :: AWS Sum...Amazon Web Services Korea
스폰서 발표 세션 | 클라우드 환경에서의 SIEMLESS 통합 보안 서비스, Alert Logic
채현주 보안기술본부장, Openbase
클라우드 환경의 다양한 서비스로 인해 자산을 지키는 보안을 위한 작업은 더욱 복잡해지고 있다. 기존 온프라미스에서 해 오던 방식으로 클라우드 보안에 접근하는 것은 비용 및 자원활용 측면에서도 낭비이며, 기술의 발전 속도를 따라가기도 어렵다. 본 세션에서는 클라우드 환경의 보안 특성을 살펴보고 효율적인 보안시스템 구축을 위한 가이드를 제시하며, 아울러 전문적인 보안 지식이나 자체 구축 보안시스템 없이도 즉시 활용할 수 있는 Alert Logic의 보안 서비스를 소개한다.MITRE_ATTACK_Enterprise_11x17.pdf

The document discusses the MITRE ATT&CK framework, which provides a knowledge base of adversary tactics and techniques based on real-world observations. It can be used by analysts, cyber defenders, and red teams to improve detection, prevention, and testing of defenses. The framework gives a common language to structure threat intelligence and allows comparison of adversary behavior across reports and organizations.
How to become a Certified Ethical Hacker.pdf

Join Tsaaro Academy's Certified Ethical Hacker (CEH v12) training course and acquire the latest techniques and tools used by battle-hardened ethical hackers.
Salary of DPO in India.pdf

Looking to specialize as a C -DPO Practitioner? Enroll in our certification and training program to enhance your knowledge and skills.
More Related Content
Similar to What are the best tools used in cybersecurity in 2023.pdf
INTERFACE by apidays 2023 - Security Exposure Management in API First World, ...

INTERFACE by apidays 2023
APIs for a “Smart” economy. Embedding AI to deliver Smart APIs and turn into an exponential organization
June 28 & 29, 2023
Security Exposure Management in API First World
Sandeep Nain, VP Security and Trust at Carta
------
Check out our conferences at https://www.apidays.global/
Do you want to sponsor or talk at one of our conferences?
https://apidays.typeform.com/to/ILJeAaV8
Learn more on APIscene, the global media made by the community for the community:
https://www.apiscene.io
Explore the API ecosystem with the API Landscape:
https://apilandscape.apiscene.io/
IDS+Honeypots Making Security Simple

Everything you really need to know about IDS (Intrusion Detection Systems) Combining with HoneyPots. Deployment and usage techniques used in the past and today. How to setup and deploy onto any network including the cloud. Reasons why this should be used in all networks. How to bring BIG DATA down to Small Data that is easy to understand and monitor.
It’s all over the news that data breaches occur daily! I asked WHY these hackers can download terabytes of data in timespans of months without being noticed. What are these companies paying their SOC team millions of dollars for? How come all the money is going to devices to prevent breaches and little to none in detecting when they occur? Don’t people know there are only two types of companies “those that been hacked, and those that don’t know they been hacked”. What can I do to detect a breach within seconds on any network scale? I think I figured it out. In my talk you’ll learn how you and your clients can benefit by applying my exclusive techniques, which I’ve successfully deployed. So the next time you get hacked the hacker would not be able to steal all those credit cards and photos of that Halloween party.
Nt2580 Unit 7 Chapter 12

This document discusses conducting a vulnerability assessment. It explains that a vulnerability assessment identifies possible security vulnerabilities in a system. The assessment involves both automated and manual techniques depending on the scope of the organization. The major steps are conducting the assessment, addressing any exposures found, and reporting and remediation. Under conducting the assessment, planning, gathering information, and defining roles and responsibilities are involved. The assessment aims to find and rank vulnerabilities to threats.
Why Penetration Testing Services Cyber51

Our security testing services address numerous information security challenges faced by clients. We assist with early identification of security threats through reviews and vulnerability checks. For existing systems, we provide independent technical reviews and testing to ensure systems are secure. Our experience ensures systems support business security needs comprehensively and robustly.
In-kernel Analytics and Tracing with eBPF for OpenStack Clouds

As the movement of applications from bare metal to the cloud continues, considerations around analytics and tracing are becoming more prevalent for security, monitoring, and accounting. As an open source project under the Linux Foundation, the IO Visor Project is working with the kernel community on extending BPF (eBPF) and is being used by many companies for security, tracing, and analytics. This talk will describe how an OpenStack micro-segmentation framework using eBPF can be utilized for analytics and tracing to secure application workloads. Use cases around application security, intrusion detection using service insertion, identity will be described. While networking is one piece of the solution, sandboxing applications to avoid attacks is also important. We will also touch upon how eBPF technology and a unified policy framework can secure application workloads in areas beyond networking.
CYBER SECURITY CAREER GUIDE CHEAT SHEET

This document provides an overview of topics, technologies, programming languages, tools, certifications, and job roles commonly required in the field of cybersecurity. It lists fundamentals areas like computer science, networking, and cryptography. It also outlines essential security domains including web security, ethical hacking, incident response, policies, and human factors. Finally, it provides steps to get started in cybersecurity, including choosing a specialization, developing skills, and staying up to date in the field.
Dhishant -Latest Resume

This document is a resume for Dhishant Abrol summarizing his professional experience and qualifications. He has over 6 years of experience in information and network security, currently working as a Security Researcher. Previous roles include managing security operations centers and security architectures for clients. He has various technical certifications and skills in areas like vulnerability assessment, malware analysis, compliance, and security tools.
8 Top Cybersecurity Tools.pdf

Top encryption tools like McAfee are popular among business users. McAfee provides full disk encryption for desktops, laptops, and servers. The algorithm uses Advanced Encryption Standard(AES) with 256-bit keys. McAfee AES is certified by US Federal Information Processing Standard. There is also ready integration of multi-layer authentication.
Cisco Connect 2018 Malaysia - Cybersecurity strategy-an integrated approach

The document discusses the importance of integrating security solutions to create an effective security architecture. It outlines how Cisco has integrated its portfolio of security products through sharing threat intelligence, event information, and policy across firewalls, web security, email security, endpoint security, and other solutions. This level of integration helps speed threat detection and response times by automating processes and providing contextual awareness across the network.
Secure Decisions - Cyber Security Sensemaking

Secure Decisions is a company that helps analyze security data and decision processes to enhance cybersecurity. They develop visual analytics tools to help cyber analysts make sense of network and software vulnerability data. Some of their products include tools that visualize wireless network security data, software vulnerabilities from multiple scanners, and network flows and alerts. They also provide consulting services and have developed technologies like a cyber decision support system and a testbed for evaluating network monitoring algorithms. Their goal is to transition research into tools that can help operators in both government and commercial organizations.
Critical Infrastructure Assessment Techniques to Prevent Threats and Vulnerab...

QA&TEST Conference 2011, Spain - Shakeel Ali, 10th International Conference on Software QA and Testing on Embedded Systems
Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.

Simon Wong and Chris Cram, Scalar security experts, discuss how Palo Alto Networks technology disrupts the entire malware kill chain. Attendees will also gain insight on flexible deployment options to better serve their mobile users, and how to get the most out of their Palo Alto Networks deployment.
Cisco Cyber Threat Defense for the Data Center Solution: Cisco Validated Design

This document provides a 3-sentence summary of a 14-page document describing the Cisco Cyber Threat Defense for the Data Center Solution:
The solution uses NetFlow from Cisco switches and devices to provide visibility into data center network traffic. The Lancope StealthWatch System collects and analyzes NetFlow data to detect suspicious activity, while the Cisco Identity Services Engine provides user identity and security group information for context. The overall solution gives security operators enhanced visibility and context to detect threats already operating in the internal network or data center.
Seceon's aiXDR_ Automating Cybersecurity Threat Detection in 2023 - Seceon.pptx

Seceon aiXDR solution is built upon its Open Threat Management (OTM) Platform enabling organizations to detect both signature-based malware with precedence and zero-day threats without precedence, quickly and effectively, thereby thwarting the kill chain and minimizing the extent of damage across business and enterprise environments.
Top Cyber Threat Intelligence Tools in 2021.pdf

Cyber threat intelligence is used for collecting necessary information about new and old threat actors from various sources. The collected data is analyzed, processed, and converted into useful threat intelligence.
https://www.infosectrain.com/courses/certified-threat-intelligence-analyst-ctia-certification-training/
David Patterson IT Security Resumes 2016

Senior cyber security engineer with over 30 years of experience in technical management, hardware engineering, system and network engineering. Experience monitoring, analyzing, migrating, designing, consulting, deploying, troubleshooting and project/technical management of large network systems. Skilled in evaluating system vulnerabilities, compiling analysis, reporting threats, and recommending security improvements.
8 Top Cybersecurity Tools.pptx

This document discusses and summarizes 8 top cybersecurity tools: 1) Encryption, which includes tools like McAfee that provide full disk encryption. 2) Intrusion detection systems that help identify potential security breaches. 3) Virtual private networks that ensure security for users by rerouting connections. 4) Network access control that restricts network access based on authentication and compliance. 5) Security information and event management tools that provide real-time insights into potential threats. 6) DDoS mitigation to detect and block malicious traffic. 7) Vulnerability scanners to identify potential vulnerabilities. 8) Firewalls that control network traffic based on security policies. It concludes that outsourcing cybersecurity needs to an experienced provider
Security operation center (SOC)

The document discusses security operation centers (SOCs) and their functions. It describes what a SOC is and its main purpose of monitoring, preventing, detecting, investigating and responding to cyber threats. It outlines the typical roles in a SOC including tier 1, 2 and 3 analysts and security engineers. It also discusses the common tools, skills needed for each role, and types of SOCs such as dedicated, distributed, multifunctional and virtual SOCs.
클라우드 환경에서의 SIEMLESS 통합 보안 서비스, Alert Logic - 채현주 보안기술본부장, Openbase :: AWS Sum...

클라우드 환경에서의 SIEMLESS 통합 보안 서비스, Alert Logic - 채현주 보안기술본부장, Openbase :: AWS Sum...Amazon Web Services Korea
스폰서 발표 세션 | 클라우드 환경에서의 SIEMLESS 통합 보안 서비스, Alert Logic
채현주 보안기술본부장, Openbase
클라우드 환경의 다양한 서비스로 인해 자산을 지키는 보안을 위한 작업은 더욱 복잡해지고 있다. 기존 온프라미스에서 해 오던 방식으로 클라우드 보안에 접근하는 것은 비용 및 자원활용 측면에서도 낭비이며, 기술의 발전 속도를 따라가기도 어렵다. 본 세션에서는 클라우드 환경의 보안 특성을 살펴보고 효율적인 보안시스템 구축을 위한 가이드를 제시하며, 아울러 전문적인 보안 지식이나 자체 구축 보안시스템 없이도 즉시 활용할 수 있는 Alert Logic의 보안 서비스를 소개한다.MITRE_ATTACK_Enterprise_11x17.pdf

The document discusses the MITRE ATT&CK framework, which provides a knowledge base of adversary tactics and techniques based on real-world observations. It can be used by analysts, cyber defenders, and red teams to improve detection, prevention, and testing of defenses. The framework gives a common language to structure threat intelligence and allows comparison of adversary behavior across reports and organizations.
Similar to What are the best tools used in cybersecurity in 2023.pdf (20)
INTERFACE by apidays 2023 - Security Exposure Management in API First World, ...

INTERFACE by apidays 2023 - Security Exposure Management in API First World, ...
In-kernel Analytics and Tracing with eBPF for OpenStack Clouds

In-kernel Analytics and Tracing with eBPF for OpenStack Clouds
Cisco Connect 2018 Malaysia - Cybersecurity strategy-an integrated approach

Cisco Connect 2018 Malaysia - Cybersecurity strategy-an integrated approach
Critical Infrastructure Assessment Techniques to Prevent Threats and Vulnerab...

Critical Infrastructure Assessment Techniques to Prevent Threats and Vulnerab...
Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.

Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.
Cisco Cyber Threat Defense for the Data Center Solution: Cisco Validated Design

Cisco Cyber Threat Defense for the Data Center Solution: Cisco Validated Design
Seceon's aiXDR_ Automating Cybersecurity Threat Detection in 2023 - Seceon.pptx

Seceon's aiXDR_ Automating Cybersecurity Threat Detection in 2023 - Seceon.pptx
클라우드 환경에서의 SIEMLESS 통합 보안 서비스, Alert Logic - 채현주 보안기술본부장, Openbase :: AWS Sum...

클라우드 환경에서의 SIEMLESS 통합 보안 서비스, Alert Logic - 채현주 보안기술본부장, Openbase :: AWS Sum...
More from tsaaroacademy
How to become a Certified Ethical Hacker.pdf

Join Tsaaro Academy's Certified Ethical Hacker (CEH v12) training course and acquire the latest techniques and tools used by battle-hardened ethical hackers.
Salary of DPO in India.pdf

Looking to specialize as a C -DPO Practitioner? Enroll in our certification and training program to enhance your knowledge and skills.
Best Data Privacy certification.pdf

Tsaaro Academy is a unique data privacy certification training platform and here you earn a privacy certification like CIPP, CIPM, CIPT, ISO, and DPO from India’s No.1 Privacy training platform.
Elevate Your Career with a Data Protection Officer Certification.pdf

Looking to specialize as a C -DPO ? Enroll in our certification and training program to enhance your knowledge and skills
What is CT- DPO.pdf

The Tsaaro Academy offers CT DPO Intermediate Certification to privacy enthusiasts who want to be certified to handle GDPR and ePrivacy compliance. Click here to learn more and get started today.
CISM.pdf

Every organisation that wants to construct, strengthen, or boost an information security management system in order to comply with its existing information security policy and standards. This is exactly where the ISO 27001: Information Security Management System Certification or the Certified Information Security Management come to rule. With the growing exchange of information, data security has progressed beyond just sharing. Recent studies suggest data exchange and data security go parallel, progressively more important to protect against attackers, fraudsters, and other threats.
More from tsaaroacademy (6)
Elevate Your Career with a Data Protection Officer Certification.pdf

Elevate Your Career with a Data Protection Officer Certification.pdf
Recently uploaded
South African Journal of Science: Writing with integrity workshop (2024)

South African Journal of Science: Writing with integrity workshop (2024)Academy of Science of South Africa
A workshop hosted by the South African Journal of Science aimed at postgraduate students and early career researchers with little or no experience in writing and publishing journal articles.clinical examination of hip joint (1).pdf

described clinical examination all orthopeadic conditions .
Digital Artifact 1 - 10VCD Environments Unit

Digital Artifact 1 - 10VCD Environments Unit - NGV Pavilion Concept Design
Chapter 4 - Islamic Financial Institutions in Malaysia.pptx

Chapter 4 - Islamic Financial Institutions in Malaysia.pptxMohd Adib Abd Muin, Senior Lecturer at Universiti Utara Malaysia
This slide is special for master students (MIBS & MIFB) in UUM. Also useful for readers who are interested in the topic of contemporary Islamic banking.
The Diamonds of 2023-2024 in the IGRA collection

A review of the growth of the Israel Genealogy Research Association Database Collection for the last 12 months. Our collection is now passed the 3 million mark and still growing. See which archives have contributed the most. See the different types of records we have, and which years have had records added. You can also see what we have for the future.
Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...

Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...Dr. Vinod Kumar Kanvaria
Exploiting Artificial Intelligence for Empowering Researchers and Faculty,
International FDP on Fundamentals of Research in Social Sciences
at Integral University, Lucknow, 06.06.2024
By Dr. Vinod Kumar KanvariaNatural birth techniques - Mrs.Akanksha Trivedi Rama University

Natural birth techniques - Mrs.Akanksha Trivedi Rama UniversityAkanksha trivedi rama nursing college kanpur.
Natural birth techniques are various type such as/ water birth , alexender method, hypnosis, bradley method, lamaze method etcবাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশের অর্থনৈতিক সমীক্ষা ২০২৪ [Bangladesh Economic Review 2024 Bangla.pdf] কম্পিউটার , ট্যাব ও স্মার্ট ফোন ভার্সন সহ সম্পূর্ণ বাংলা ই-বুক বা pdf বই " সুচিপত্র ...বুকমার্ক মেনু 🔖 ও হাইপার লিংক মেনু 📝👆 যুক্ত ..
আমাদের সবার জন্য খুব খুব গুরুত্বপূর্ণ একটি বই ..বিসিএস, ব্যাংক, ইউনিভার্সিটি ভর্তি ও যে কোন প্রতিযোগিতা মূলক পরীক্ষার জন্য এর খুব ইম্পরট্যান্ট একটি বিষয় ...তাছাড়া বাংলাদেশের সাম্প্রতিক যে কোন ডাটা বা তথ্য এই বইতে পাবেন ...
তাই একজন নাগরিক হিসাবে এই তথ্য গুলো আপনার জানা প্রয়োজন ...।
বিসিএস ও ব্যাংক এর লিখিত পরীক্ষা ...+এছাড়া মাধ্যমিক ও উচ্চমাধ্যমিকের স্টুডেন্টদের জন্য অনেক কাজে আসবে ...
How to Build a Module in Odoo 17 Using the Scaffold Method

Odoo provides an option for creating a module by using a single line command. By using this command the user can make a whole structure of a module. It is very easy for a beginner to make a module. There is no need to make each file manually. This slide will show how to create a module using the scaffold method.
CACJapan - GROUP Presentation 1- Wk 4.pdf

Macroeconomics- Movie Location
This will be used as part of your Personal Professional Portfolio once graded.
Objective:
Prepare a presentation or a paper using research, basic comparative analysis, data organization and application of economic information. You will make an informed assessment of an economic climate outside of the United States to accomplish an entertainment industry objective.
A Strategic Approach: GenAI in Education

Artificial Intelligence (AI) technologies such as Generative AI, Image Generators and Large Language Models have had a dramatic impact on teaching, learning and assessment over the past 18 months. The most immediate threat AI posed was to Academic Integrity with Higher Education Institutes (HEIs) focusing their efforts on combating the use of GenAI in assessment. Guidelines were developed for staff and students, policies put in place too. Innovative educators have forged paths in the use of Generative AI for teaching, learning and assessments leading to pockets of transformation springing up across HEIs, often with little or no top-down guidance, support or direction.
This Gasta posits a strategic approach to integrating AI into HEIs to prepare staff, students and the curriculum for an evolving world and workplace. We will highlight the advantages of working with these technologies beyond the realm of teaching, learning and assessment by considering prompt engineering skills, industry impact, curriculum changes, and the need for staff upskilling. In contrast, not engaging strategically with Generative AI poses risks, including falling behind peers, missed opportunities and failing to ensure our graduates remain employable. The rapid evolution of AI technologies necessitates a proactive and strategic approach if we are to remain relevant.
How to Manage Your Lost Opportunities in Odoo 17 CRM

Odoo 17 CRM allows us to track why we lose sales opportunities with "Lost Reasons." This helps analyze our sales process and identify areas for improvement. Here's how to configure lost reasons in Odoo 17 CRM
Assessment and Planning in Educational technology.pptx

In an education system, it is understood that assessment is only for the students, but on the other hand, the Assessment of teachers is also an important aspect of the education system that ensures teachers are providing high-quality instruction to students. The assessment process can be used to provide feedback and support for professional development, to inform decisions about teacher retention or promotion, or to evaluate teacher effectiveness for accountability purposes.
Recently uploaded (20)
South African Journal of Science: Writing with integrity workshop (2024)

South African Journal of Science: Writing with integrity workshop (2024)
Chapter 4 - Islamic Financial Institutions in Malaysia.pptx

Chapter 4 - Islamic Financial Institutions in Malaysia.pptx
Pride Month Slides 2024 David Douglas School District

Pride Month Slides 2024 David Douglas School District
Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...

Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...
Natural birth techniques - Mrs.Akanksha Trivedi Rama University

Natural birth techniques - Mrs.Akanksha Trivedi Rama University
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf
How to Build a Module in Odoo 17 Using the Scaffold Method

How to Build a Module in Odoo 17 Using the Scaffold Method
How to Manage Your Lost Opportunities in Odoo 17 CRM

How to Manage Your Lost Opportunities in Odoo 17 CRM
Assessment and Planning in Educational technology.pptx

Assessment and Planning in Educational technology.pptx
Film vocab for eal 3 students: Australia the movie

Film vocab for eal 3 students: Australia the movie
What are the best tools used in cybersecurity in 2023.pdf
- 1. What are the best tools used in cybersecurity in 2023? The cybersecurity field is a dynamic and ever-evolving landscape, where staying ahead of cyber threats is a continuous challenge. Achieving proficiency in the right tools is essential for cybersecurity experts to effectively protect digital systems and networks. A cybersecurity expert training course serves as a gateway to acquiring the necessary knowledge and skills required to navigate the complexities of the cybersecurity landscape successfully. Leading Tools Included in Cybersecurity Expert Course Curriculum Metasploit: Payload and Exploit Creation: Crafting payloads and exploits for testing purposes. Modularity with Add-ons: Incorporating extra add-ons for extended functionality. Automated Clean-up: Facilitating automatic removal of infected systems. Wireshark: Packet Monitor: Visual representation of network packets for analysis. Import/Export Capabilities: Supporting multiple file formats for efficient data handling. Censys: Host and Service Enumeration: Providing detailed information about hosts and services. Internet-Wide Scanning: Scanning numerous hosts for a broad view of the internet. Spiderfoot: Data Gathering: Querying multiple data sources for comprehensive reports. Vulnerability Identification: Searching for potential vulnerabilities and security issues. Hydra: Diverse Protocol Support: Supporting multiple protocols for attacking specific targets. Parallel Brute Force Attacks: Facilitating swift and powerful operations for unauthorized access. Harvester: Email Harvesting: Extracting email addresses for marketing campaigns or contact lists. Subdomain Enumeration: Identifying additional web assets by enumerating subdomains. AlienVault: Automated Data Analysis: Collecting and analyzing data for efficient threat detection. Incident Response Suite: Equipping organizations with tools for swift mitigation.
- 2. Eagle OSINT: Python-based: Customizable and extendable due to its Python foundation. API and Plugins: Allowing integration and automation for streamlined workflows. Nmap: Host Discovery and Port Scanning: Identifying live hosts and detecting open ports. Service and Version Detection: Identifying services and providing version information. Nessus: Vulnerability Scanning: Identifying known vulnerabilities and recommending patches. Configuration Auditing: Assessing system configurations for security risks. Splunk: Real-time Monitoring: Providing real-time visibility into system performance and security events. Machine Learning and AI: Utilising ML and AI for anomaly detection and prediction. Become a Cybersecurity Expert with Tsaaro Academy Tsaaro Academy offers a comprehensive Cybersecurity Expert training course, encompassing both Security Operations Center (SOC) and penetration testing domains. This program delves into the fundamentals of ethical hacking and penetration testing, providing participants with theoretical knowledge and practical skills. Through hands-on activities and tool usage, Tsaaro Academy ensures that individuals are well-equipped to tackle the dynamic challenges posed by the ever-changing cybersecurity landscape. Join Tsaaro Academy to embark on a journey towards mastering cybersecurity and safeguarding digital environments with confidence and expertise. Click Here for DPO as a Service
