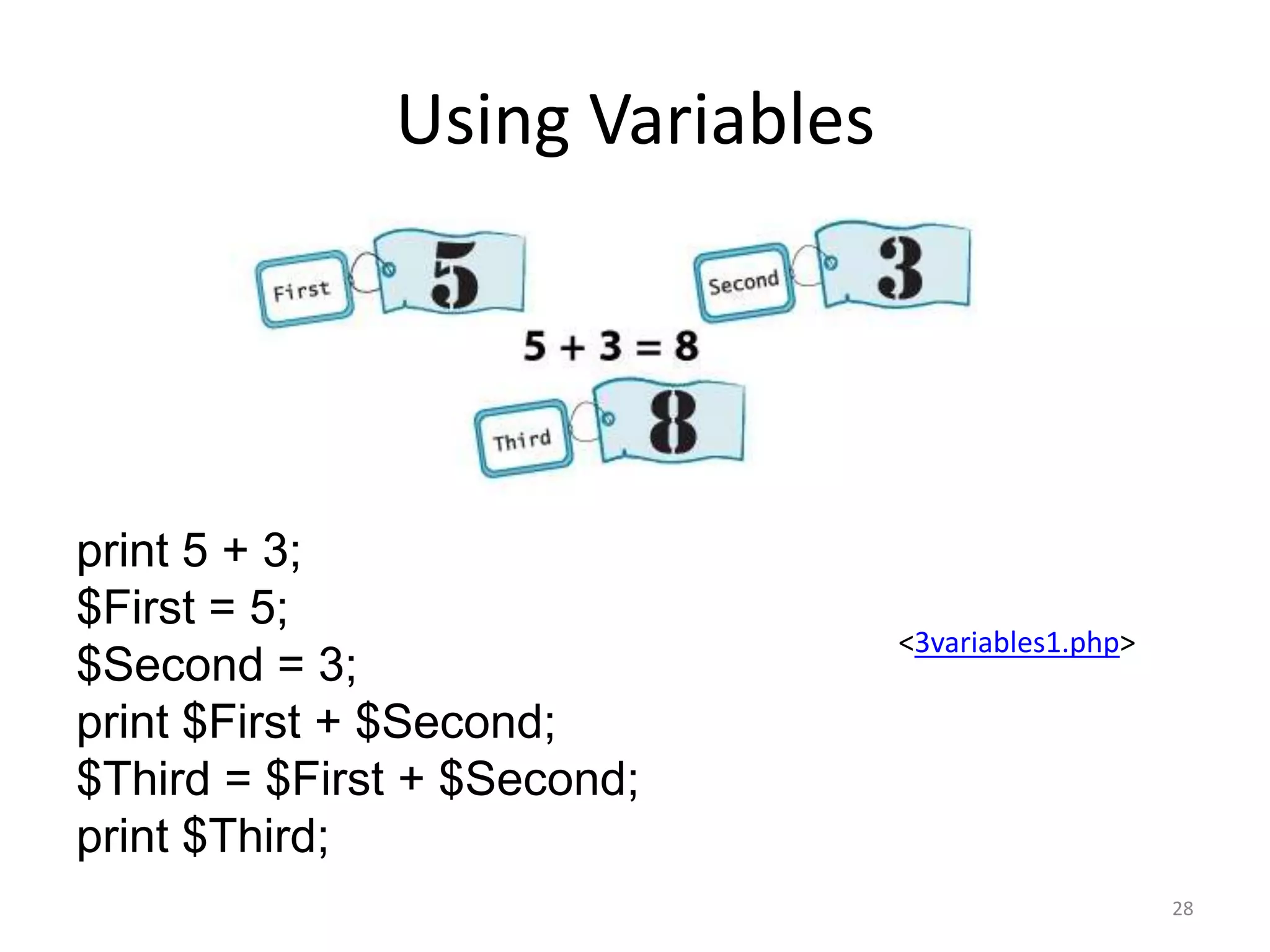
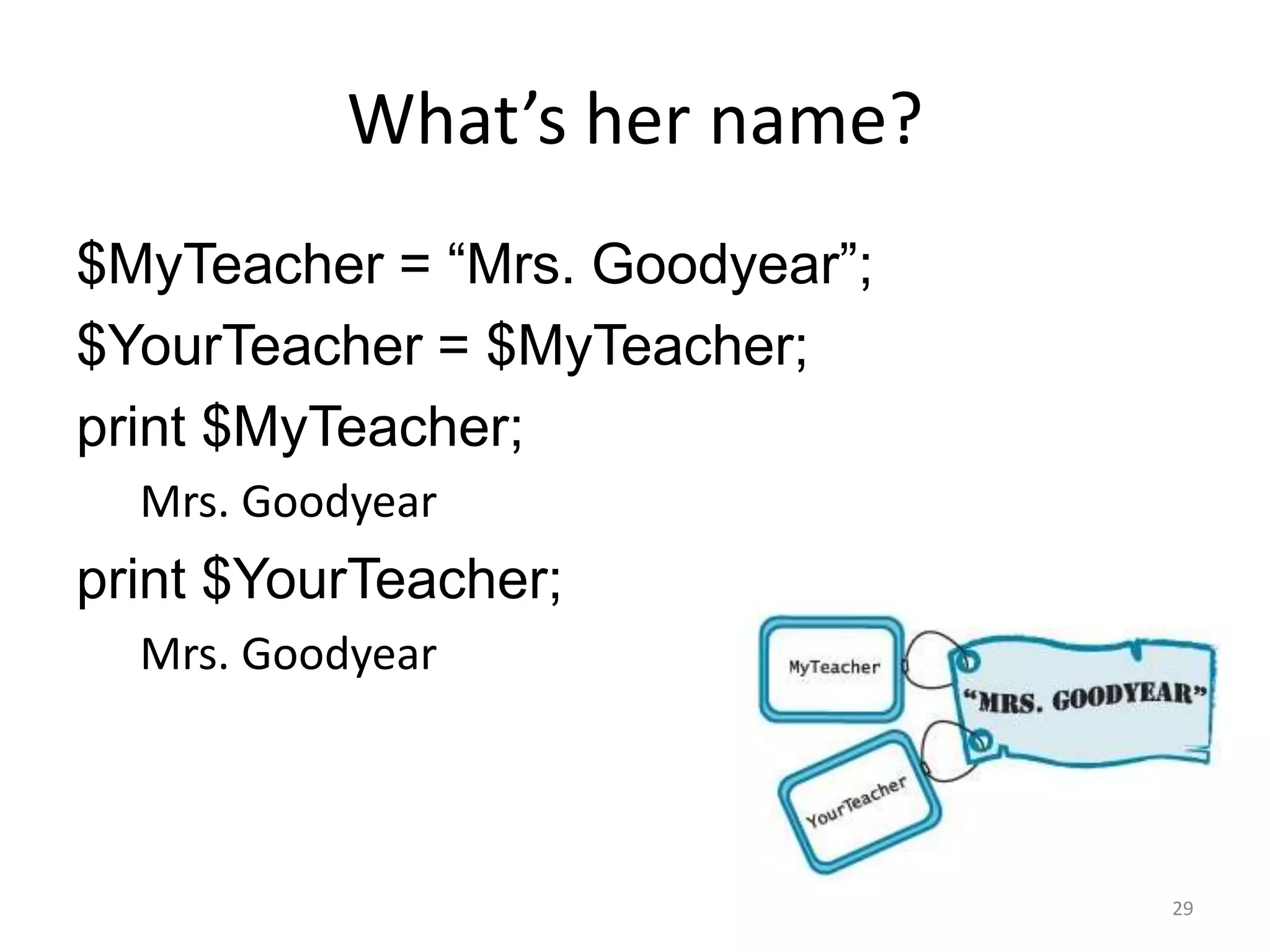
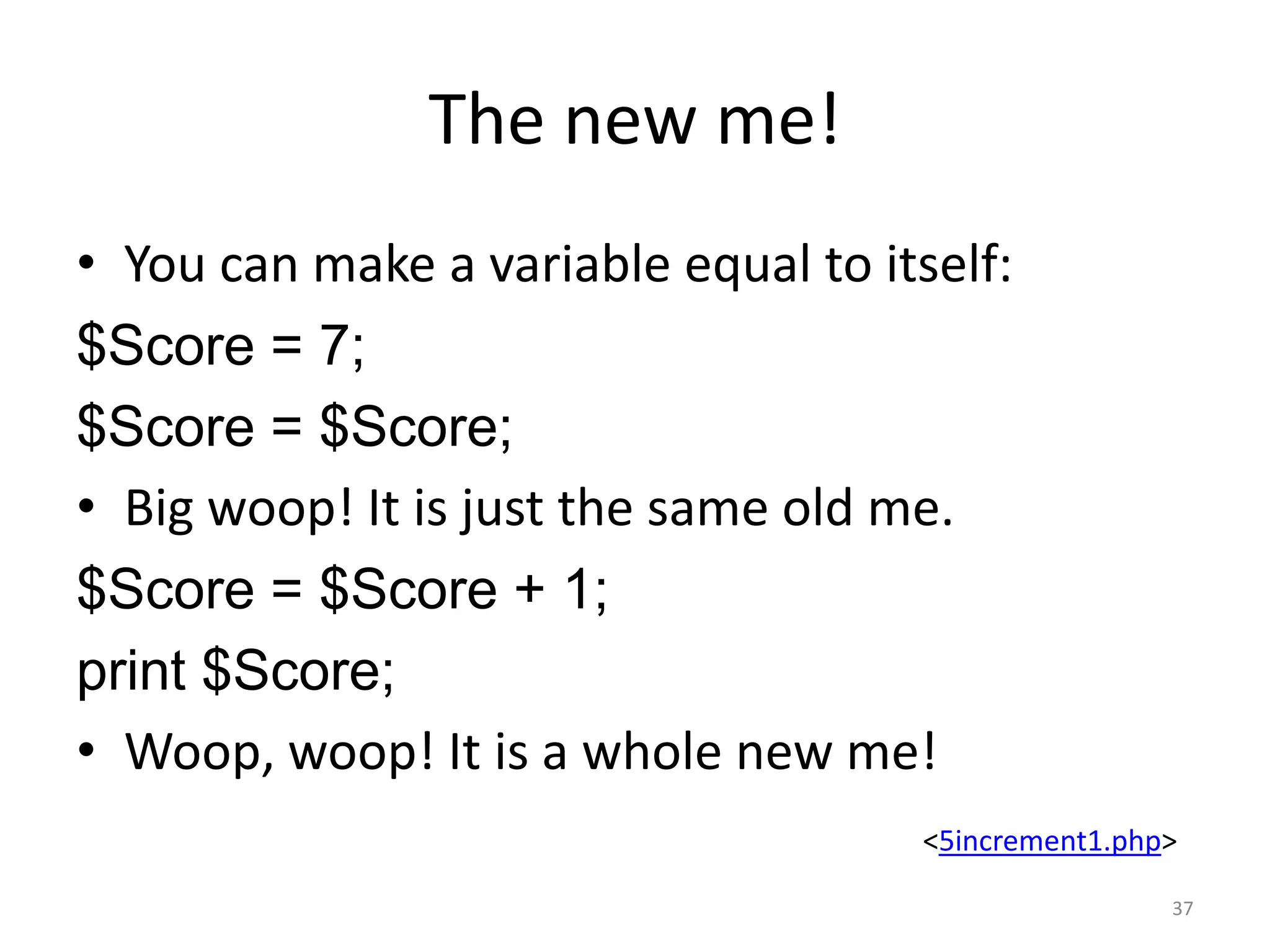
The document provides an introduction to programming concepts such as variables, data types, basic math operations, and order of operations. It explains how variables store and represent data in computer memory and how their values can be manipulated using assignment statements and basic math. The document also introduces potential issues around data type conversion and order of operations that programmers need to be aware of.
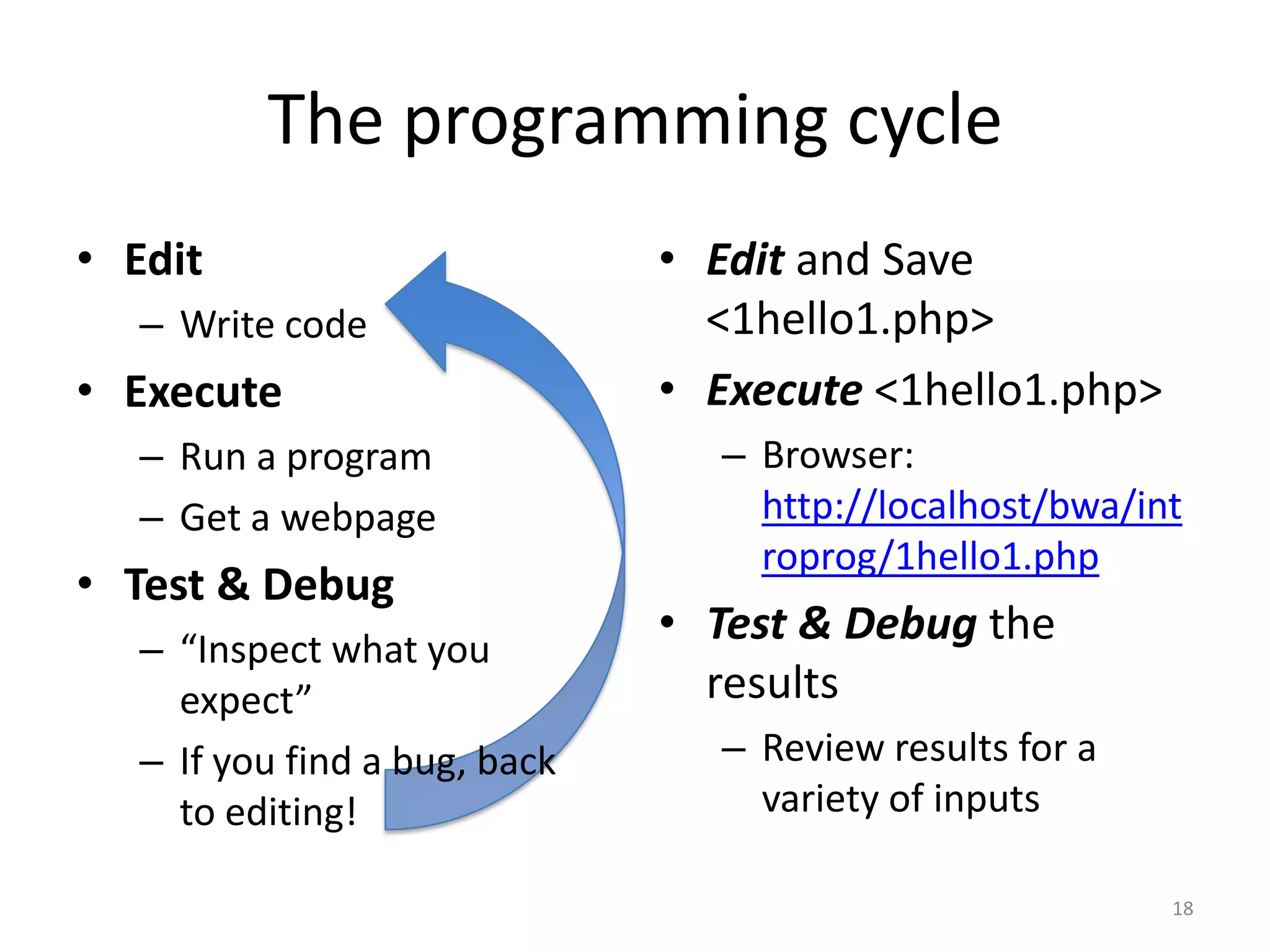
![Apache, PHP & MySQL
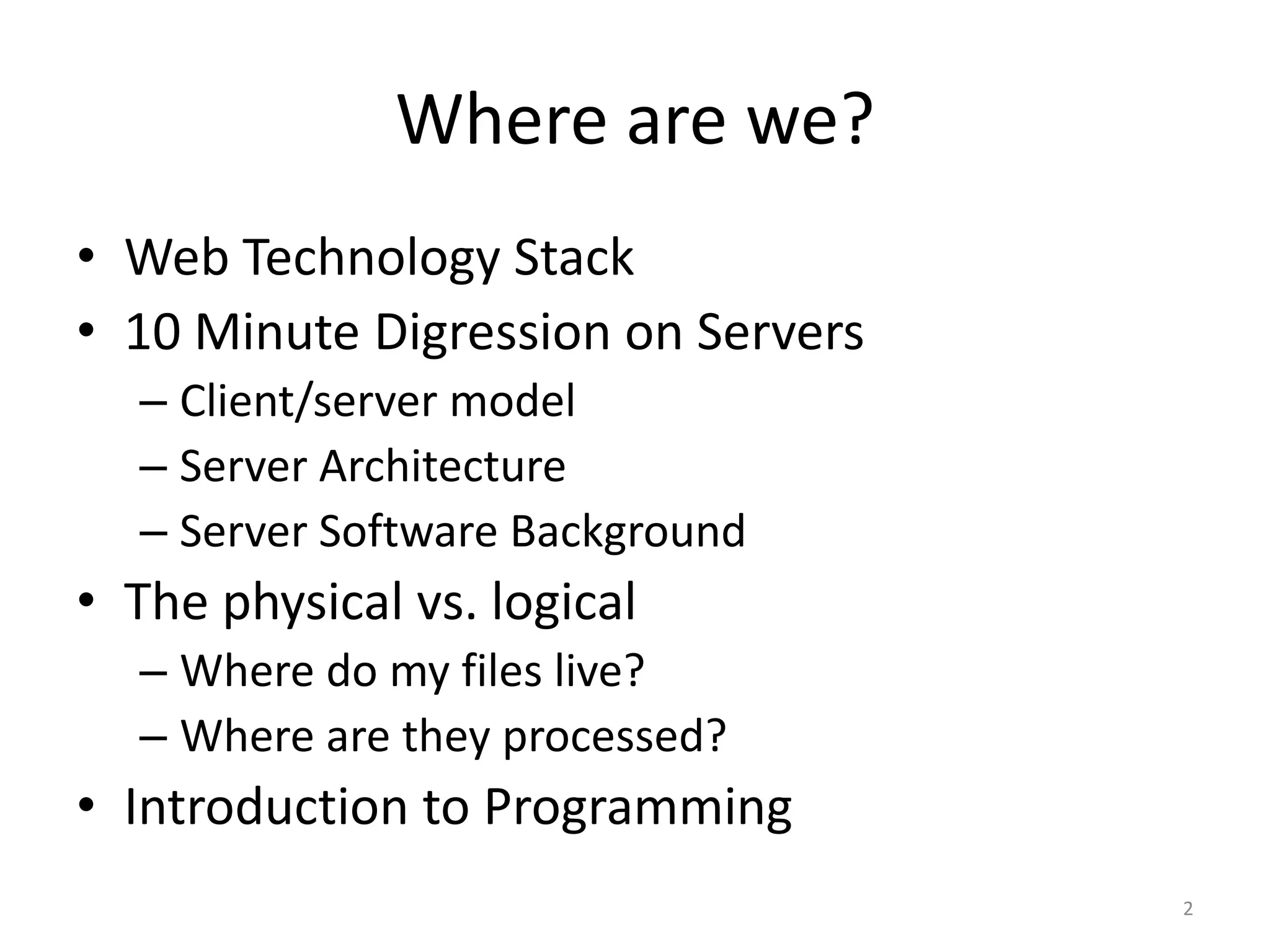
• These open source products are easily installed
by developers and used commercially
• Your OS, Apache, MySQL, PHP – [X A M P]!
– LAMP, WAMP, and MAMP
• LAMP stacks are widely used to serve many content
applications
– Webmail, Blogs, Wikis, CMSs, etc.
• Great for Virtual Hosting!
– It is the server stack you get for $5/month from
HostGator, GoDaddy, etc.](https://image.slidesharecdn.com/introtoprogrammingpart1-120218221548-phpapp01/75/Week-5-10-2048.jpg)
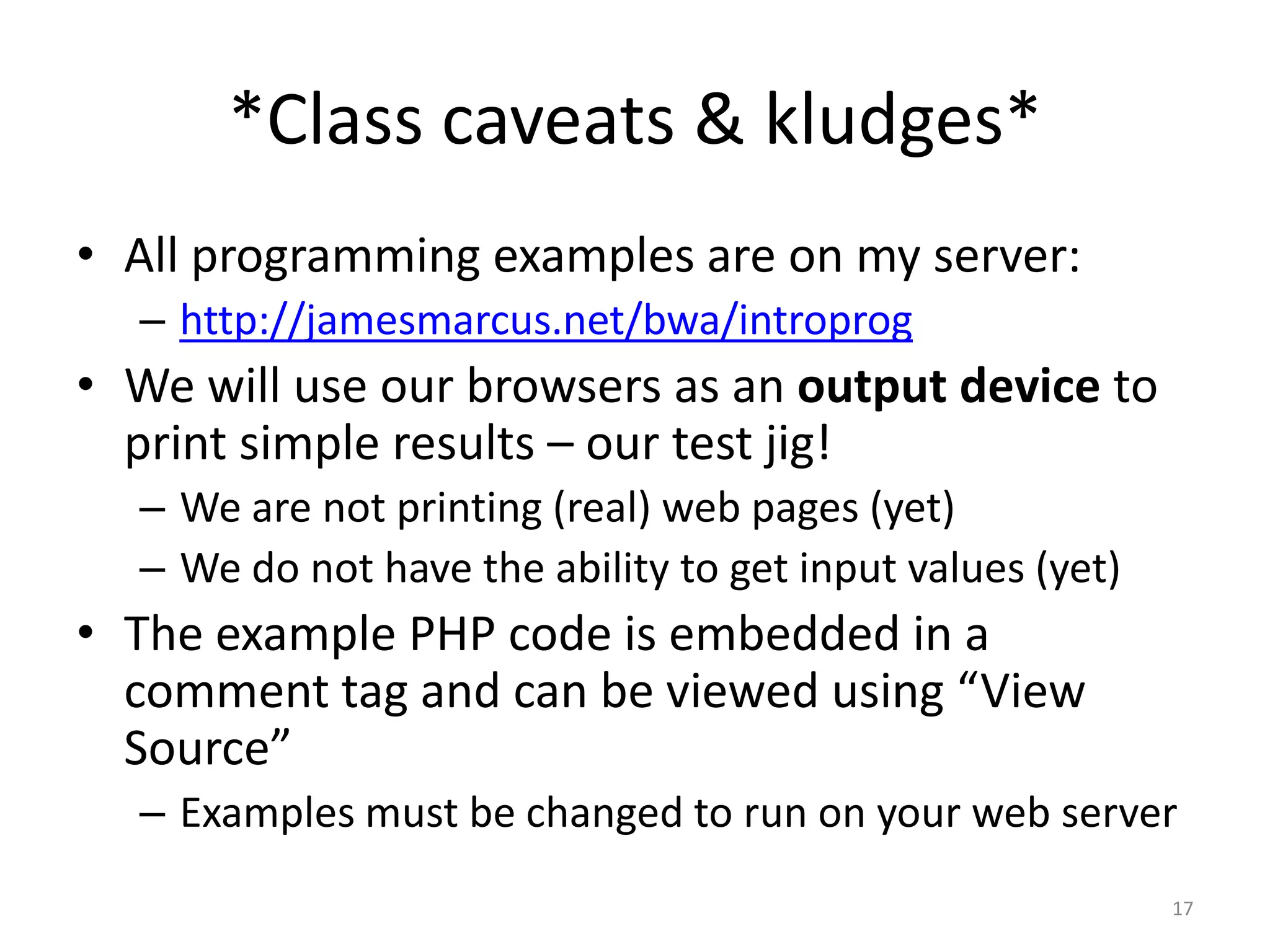
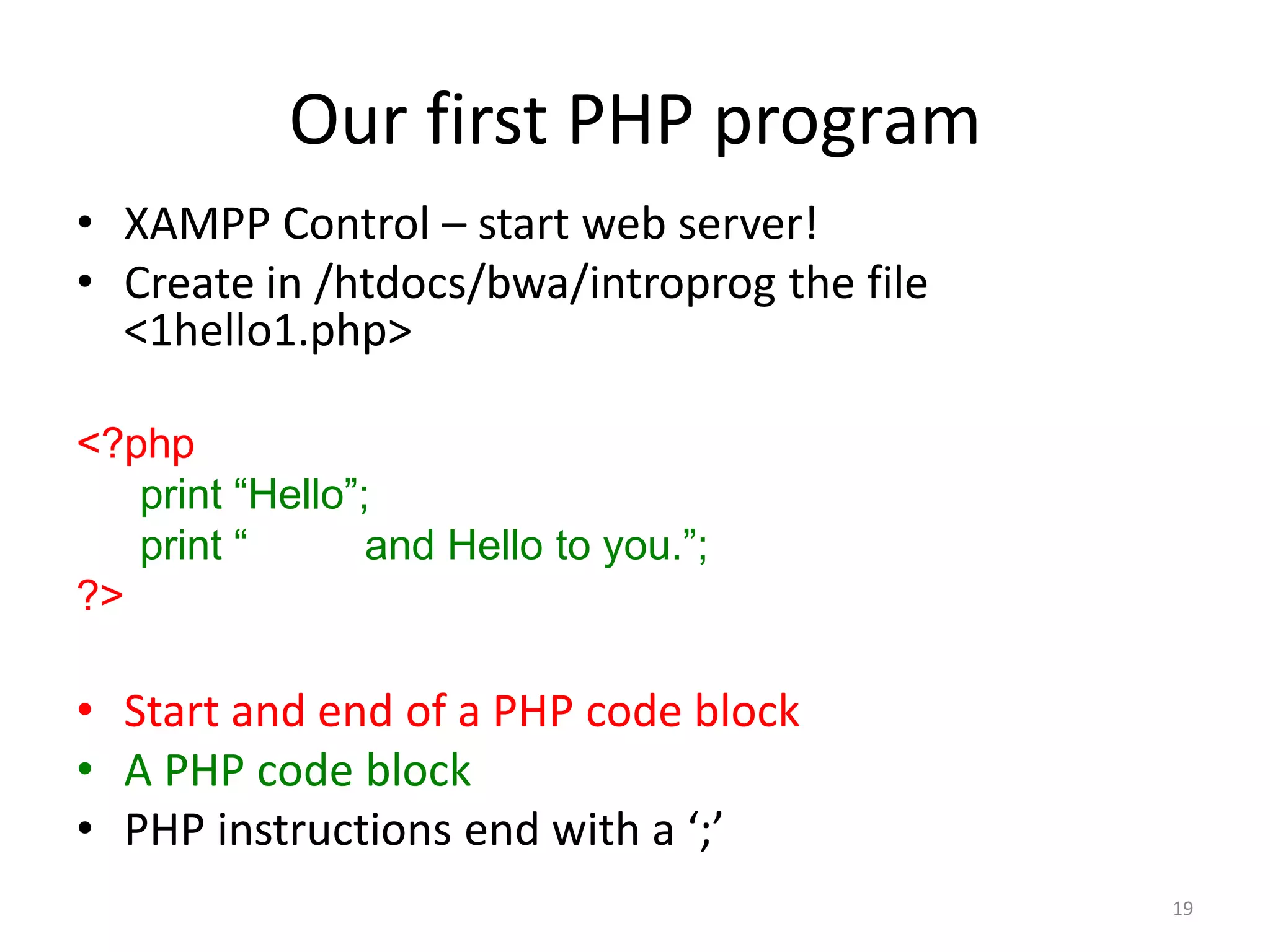
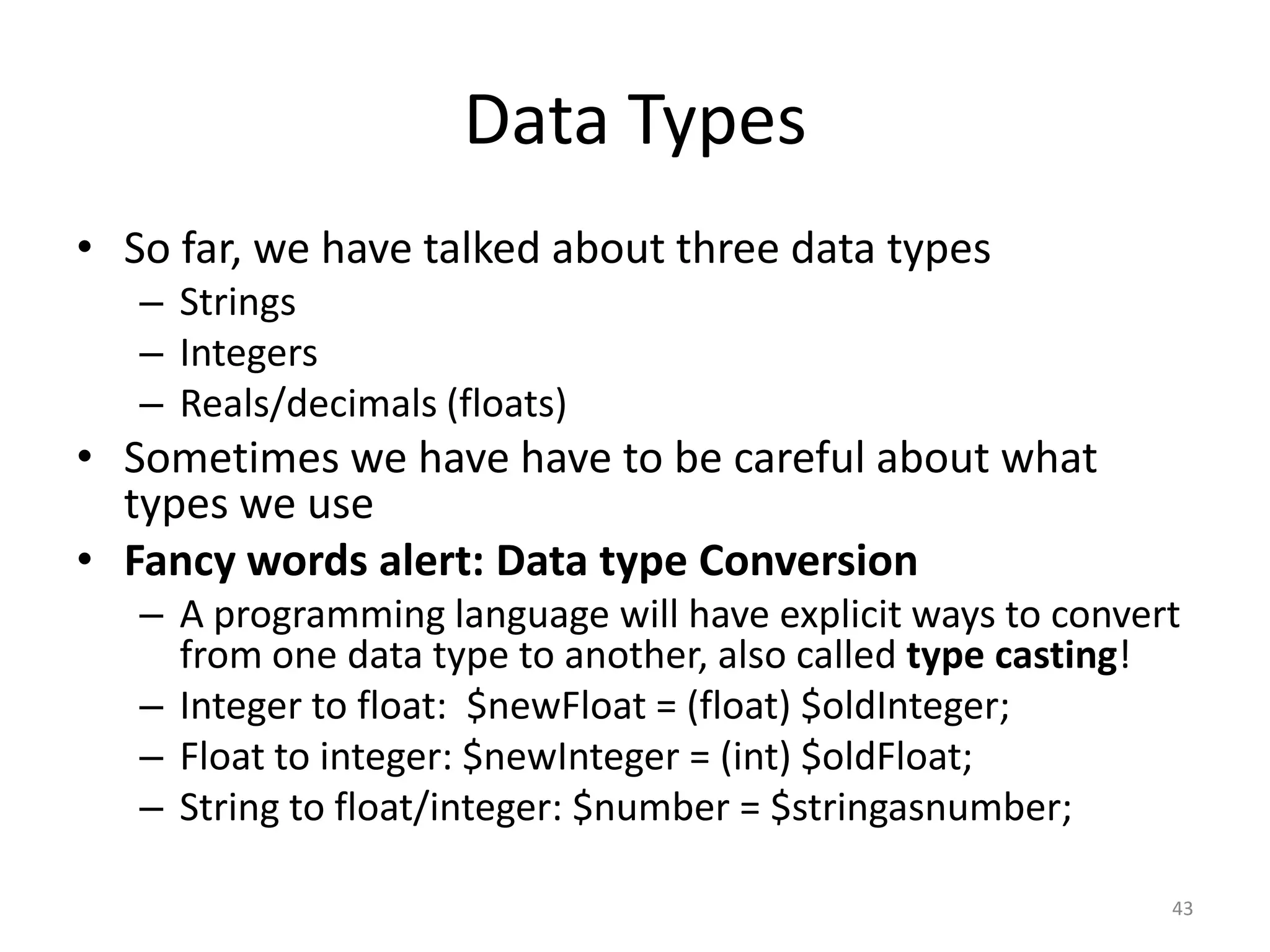
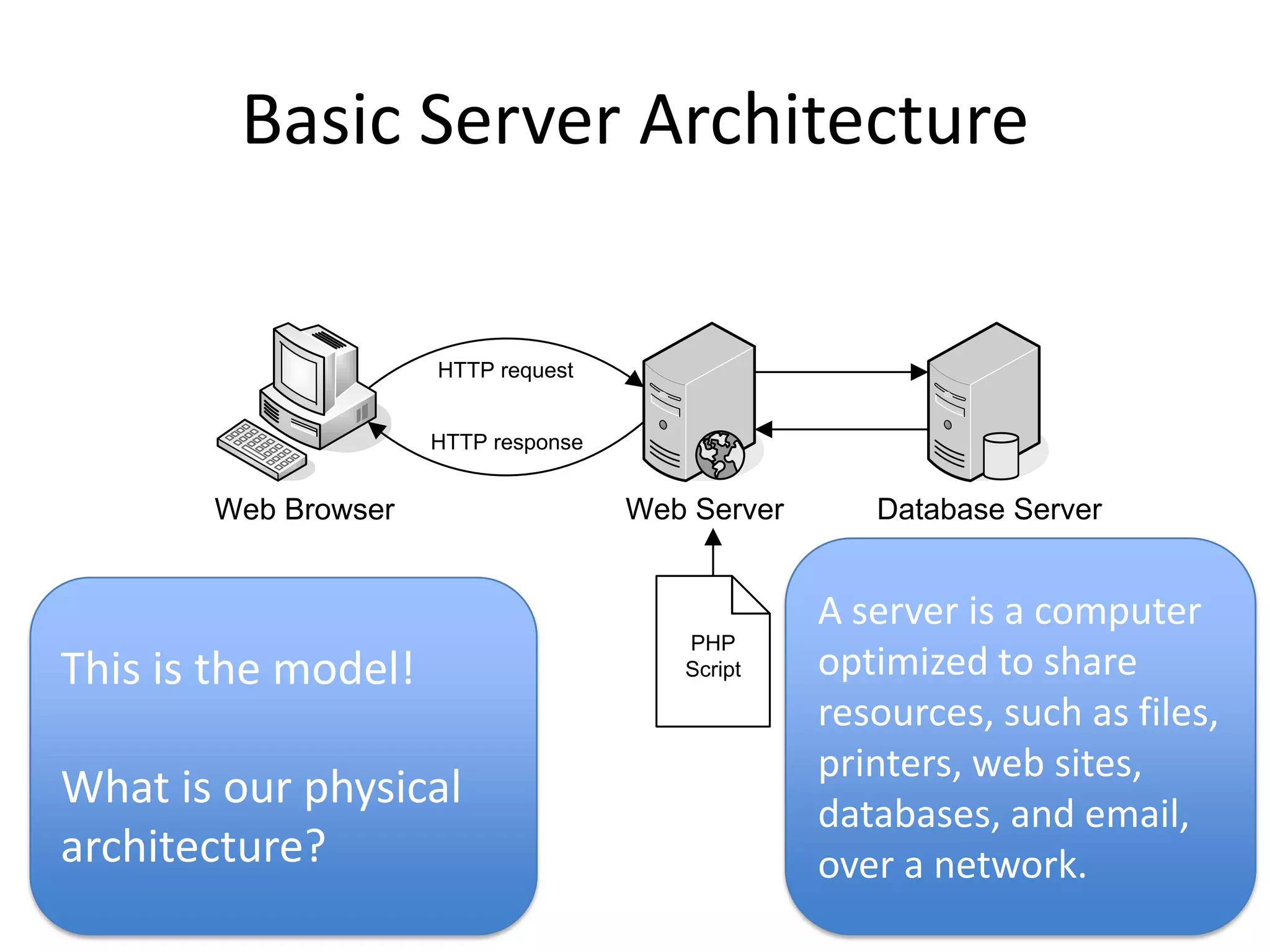
![Basic Math
• The four basic operations:
– Addition: +
– Subtraction: -
– Multiplication: *
– Division: /
• Exponentiation [PHP: pow($base, $exponent)]
– Raising a number to a power: 25= 2*2*2*2*2
• Modulus [PHP: %]
– Clock arithmetic
• Increment and decrement
$Score = $Score + 1;
++$Score;
$Score += 1;
• Really big numbers, really small numbers
– Overflow, underflow, e-notation
41](https://image.slidesharecdn.com/introtoprogrammingpart1-120218221548-phpapp01/75/Week-5-41-2048.jpg)