The document provides an overview of web technologies, including:
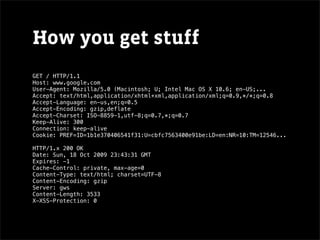
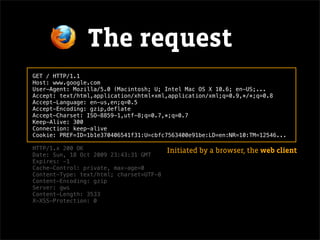
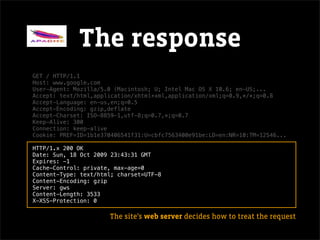
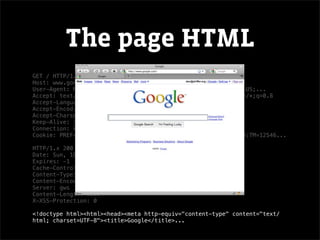
- The basic client-server model of the web where clients (browsers) make HTTP requests to servers, which return data like web pages.
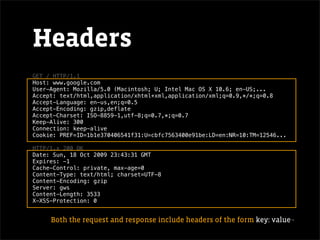
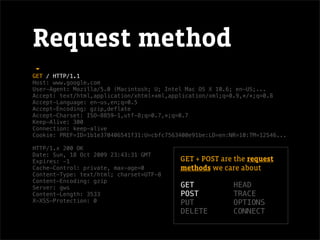
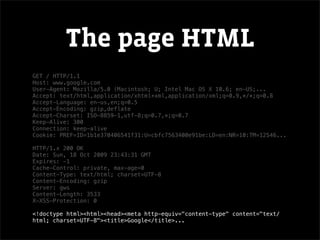
- Key aspects of HTTP requests and responses like headers, status codes, and encoding of returned HTML content.
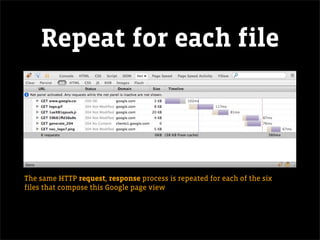
- How the client-server communication is repeated for each file that makes up a full web page.