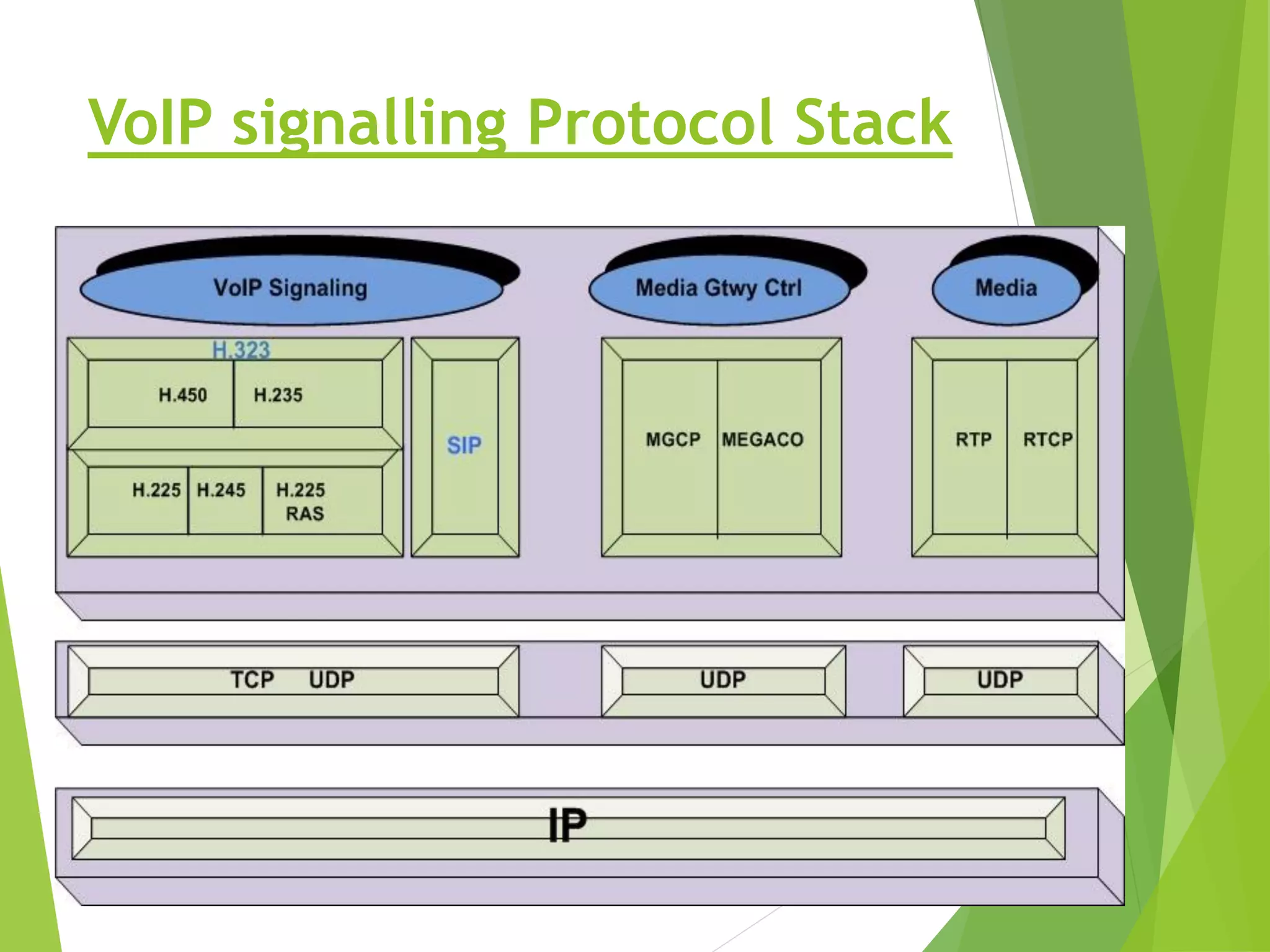
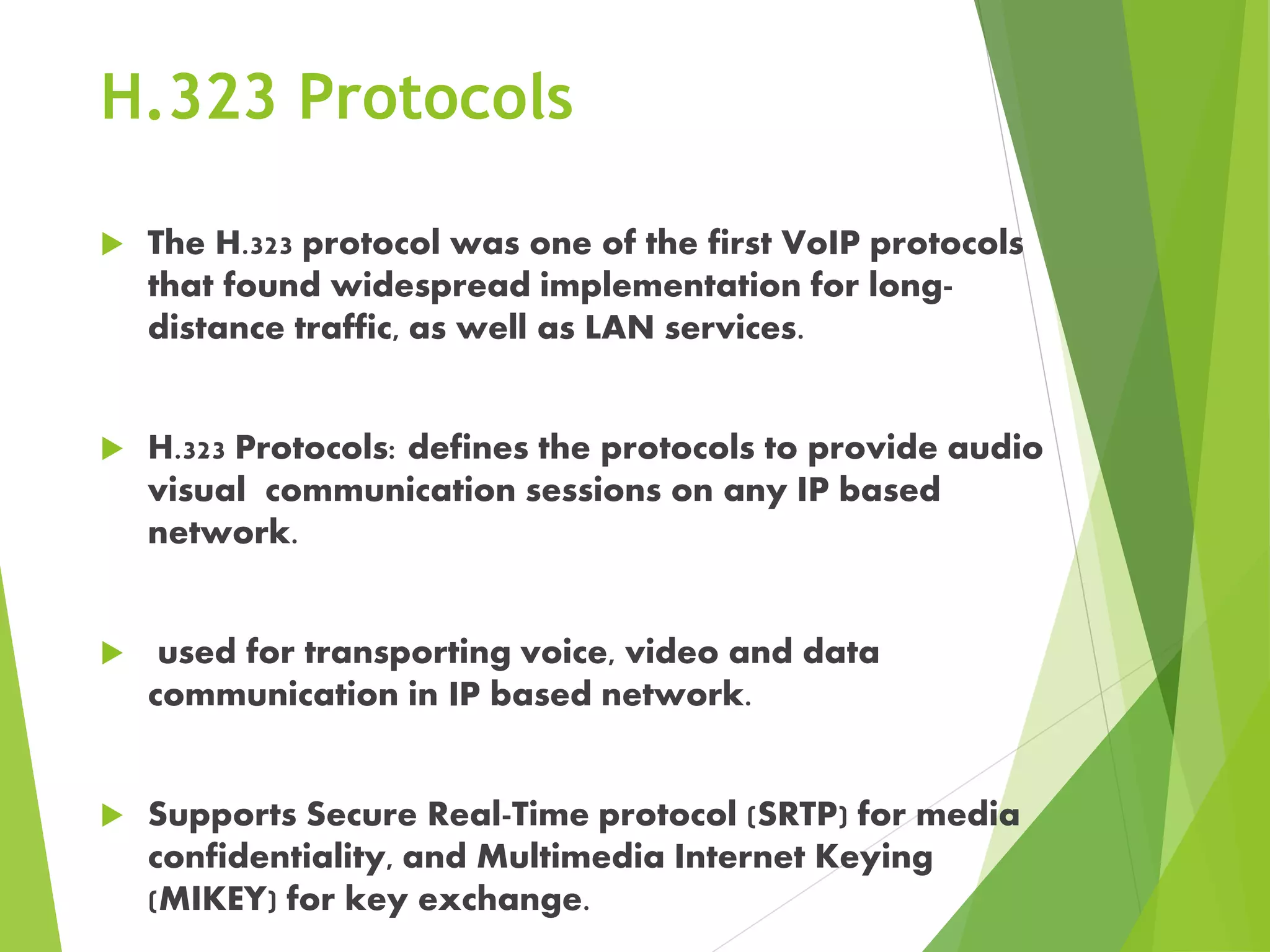
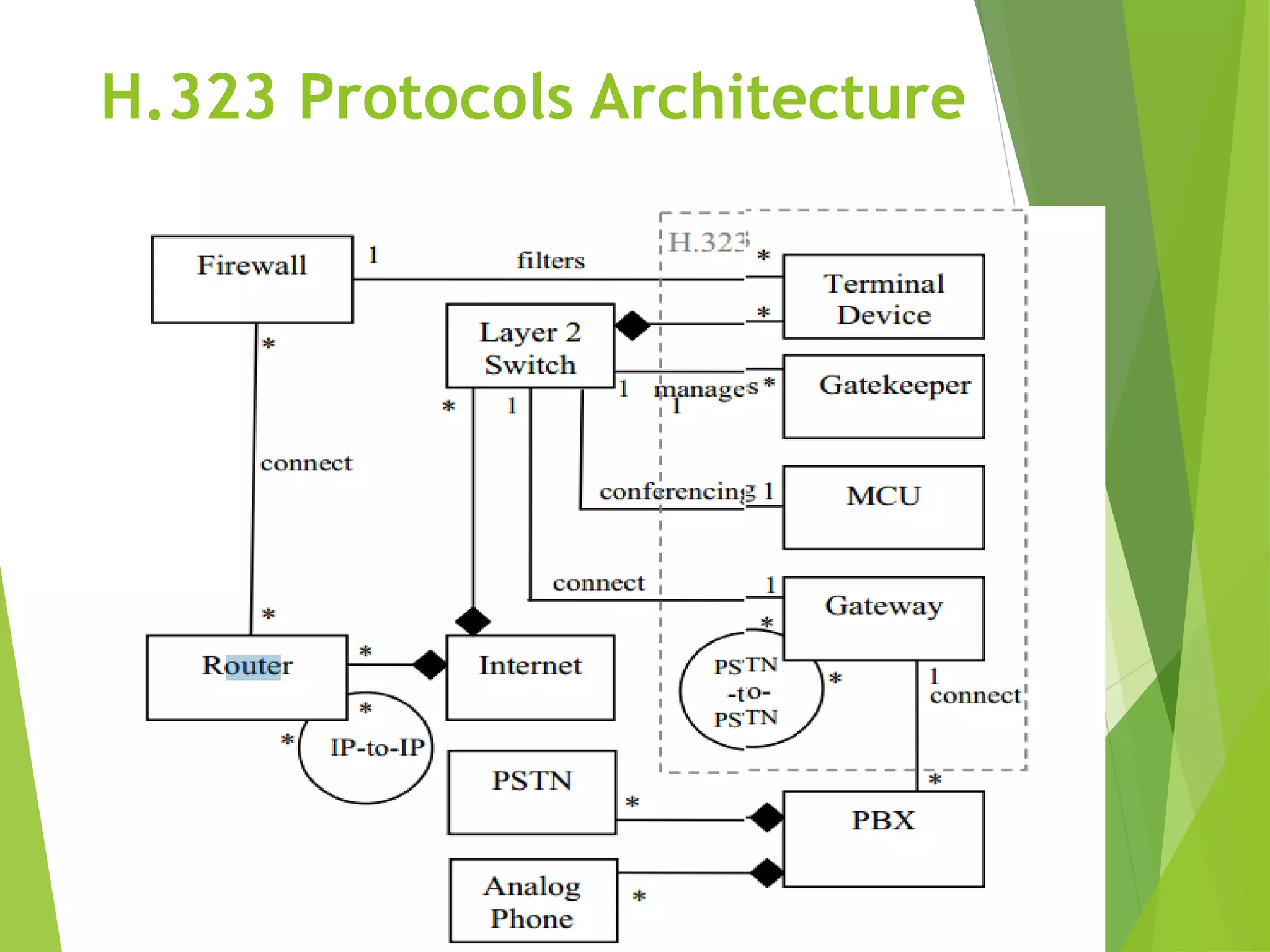
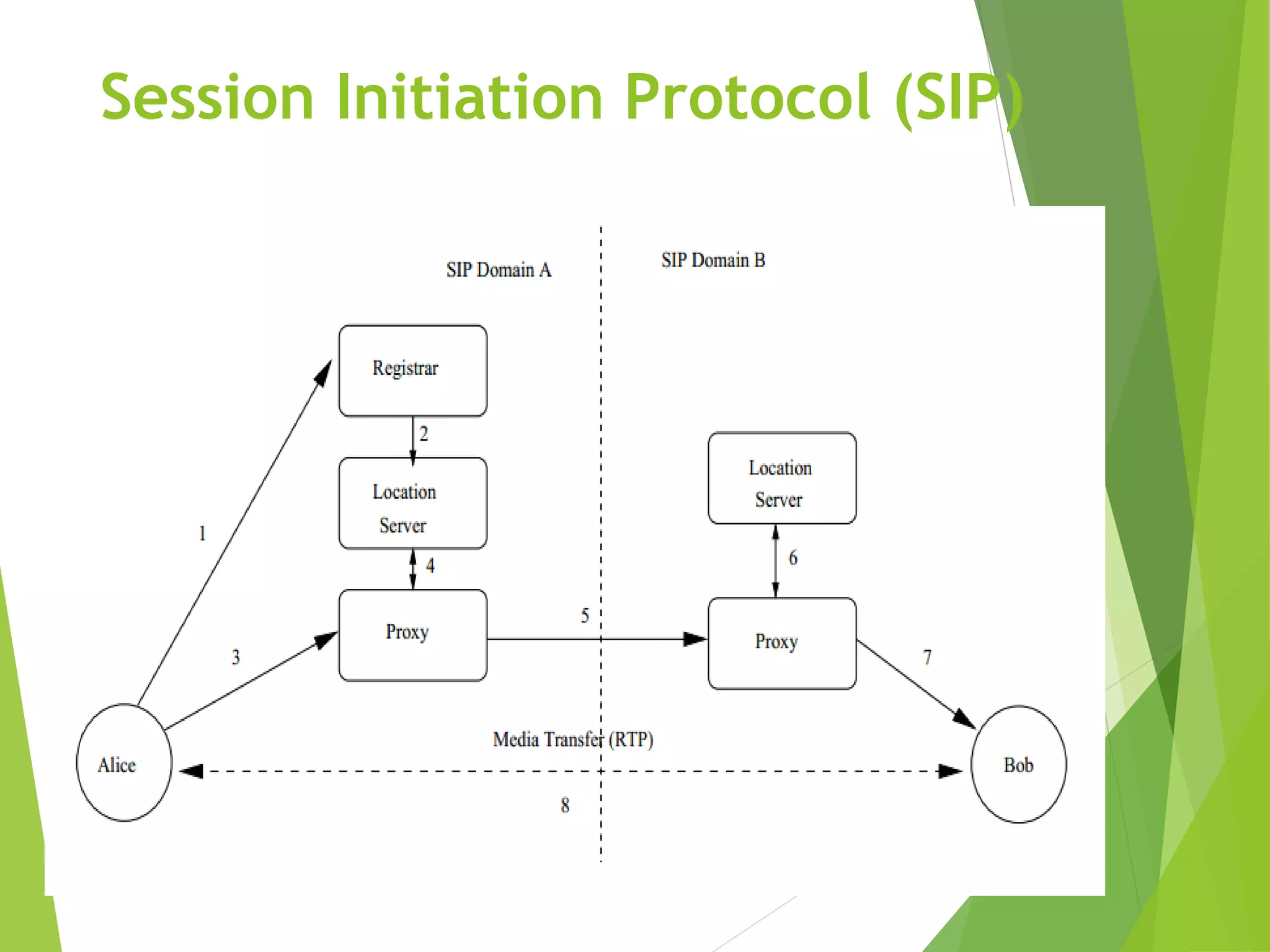
This document discusses security issues related to Voice over Internet Protocol (VoIP). It begins by explaining what VoIP is and some of its early implementations. It then describes the basic protocols and protocol stacks used for VoIP signaling and sessions, including H.323, SIP, and RTP. The document outlines various roles in VoIP systems, such as administrators and operators. It identifies common attacks against VoIP networks like theft of service, man-in-the-middle attacks, IP spoofing, and denial-of-service attacks. It concludes that VoIP inherits security vulnerabilities from the Internet and that encryption, authentication, firewalls, and separating voice and data traffic are needed to secure VoIP networks.