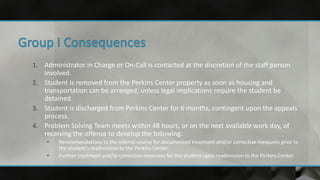
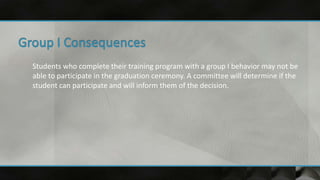
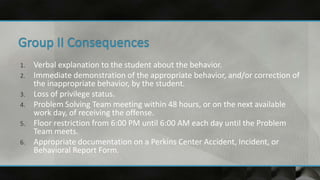
The document outlines the behavior management policies and conduct standards of the Perkins Center. It divides behaviors into four groups based on severity, from Group IV being the least serious to Group I being the most serious. Consequences are pre-determined for each group and cannot be deviated from. The document provides examples of behaviors in each group and the corresponding consequences. It aims to promote positive behaviors and reinforce appropriate conduct through structured supervision and consequences for inappropriate actions.