POS malware, like RAM scrapers, are used to steal payment card data from POS systems. They work by grabbing card data stored temporarily in RAM during transactions and storing it for later retrieval. Industries like hospitality and retail that rely heavily on POS devices are common targets. To infect many POS systems at once, attackers may compromise a company's POS management server which can then infect systems across locations. Defenses include limiting remote access, enforcing strong passwords, restricting POS system use, and using two-factor authentication.
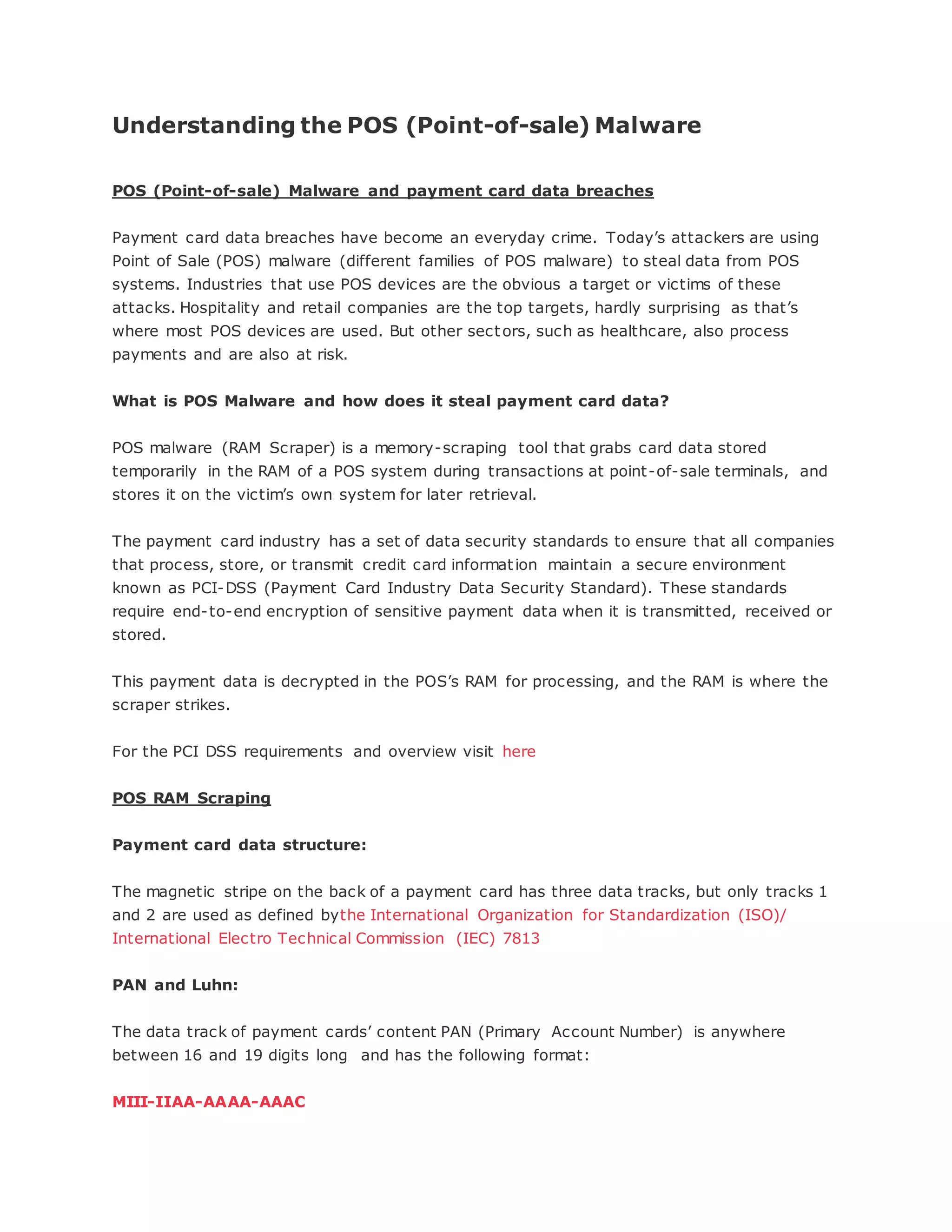
![The first six digits are known as the “Issuer Identification Number” (IIN). Its first digit is
called the “Major Industry Identifier” (MII). Major card networks—Visa, MasterCard,
Discover, JCB®, AMEX, and others—all have unique IIN ranges that identify which
institution issued a card. A: Account number can be up to 12 digits, C: Check digit calculate
using the Luhn algorithm. All the valid credit card numbers must pass this Luhn validation
check.
How POS RAM Scraping works
POS RAM Scraper basically uses the regular expression (regex) to search and gather (i.e. to
parse) Tracks 1 and 2 credit card data from the process memory space in RAM. The
following is an example to parse Track1 data:
^%([A-Z])([0-9]{1,19})^([^^]{2,26})^([0-9]{4}|^)([0-
9]{3}|^)([^?]+)?$
The regex may gather some garbage value from the process memory space of RAM
depending on its accuracy. To avoid garbage value parsed by regex, some POS RAM
scrapers implement Luhn validation to check the card data gathered.
When the credit card is swiped in the POS system, the data stored on the card is copied into
the POS software’s process memory space in the RAM temporary for authentication and
processing for transaction of payment.
Here is where the POS RAM Scrapers starts its work: It retrieves the list of processes that
are running on the POS system and searches each process memory for card data. It
searches each and every process’ memory and retrieves Tracks 1 and 2 card data as per the
regex.
POS RAM Scrapers Variants:
The earlier variants of POS RAM Scrapers only included the following basic
functions:-
Install a malware as a service
Scan POS system process’s RAM for credit card Track 1 and Track two data
Dump the results into a text file
The text file was then probably accessed remotely or manually](https://image.slidesharecdn.com/9d137a70-1c7e-4834-8b9c-287c7bb95c83-150501084341-conversion-gate01/85/Understanding-the-POS-Malware-2-320.jpg)

