The evolution of terrorism after paris
•
0 likes•357 views
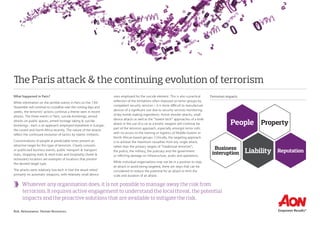
Whatever any organisation does, it is not possible to manage away the risk from terrorism. It requires active engagement to understand the local threat, the potential impacts and the proactive solutions that are available to mitigate the risk.
Report
Share
Report
Share
Download to read offline
Recommended
Turkey Domestic Terrorism & Evolving Threats

The ongoing terror attacks in Turkey are a continuation of long-standing domestic issues facing Ankara, overlaid by the new,
evolving threat posed by Islamic extremist groups. The attacks, which reflect each terror groups’ strategic intentions, can be
summarised into three broad groupings, with each group following a differing agenda and operational approach:
• Kurdish militant (such as the Kurdistan Workers Party [PKK])
• Domestic extremist ( including Marxist Leninist, anti-Western and anti-NATO groups – such as the Revolutionary People’s
Liberation Party–Front [DHKP-C])
• Islamic militant (specifically, Islamic State [IS])
The Marsh Report-Terrorism Risk Insurance 2010 

Despite an ever-changing terrorism risk insurance market, businesses from every industry sector continue to purchase coverage—more than 60 percent of organizations surveyed by Marsh bought coverage in 2009.
The Whiplash Effect Of Reactive Travel Risk Management

Recent events have caused companies and individuals to re-evaluate their travel risk management policies. Newsworthy incidents often drive decision making, but the key factors are an individual's experience, the activity, location, risk tolerance, and available support. The Mumbai attacks highlighted terrorism as a risk in India for many, though thousands continue dying in accidents. The targeting of Sri Lanka's cricket team in Pakistan raised awareness of security challenges there, showing that apolitical groups can be targets due to media attention. Time will tell if these and other attacks embolden issue motivated groups, though reactive planning may weaken long-term resilience more than address real risks. A systematic, continuously monitored approach to risk assessment is preferable to knee-jerk
final

The document discusses terrorism risk in the insurance sector. It defines terrorism and outlines the challenges in quantifying terrorism risk due to the unpredictable nature of terrorist attacks. Terrorism risk has three main components - threat, vulnerability, and consequence. Threat refers to the probability of an attack occurring, vulnerability is the probability of damage resulting from an attack, and consequence is the expected magnitude of damage. Terrorism risk is calculated as the product of these three components. Estimating each component is challenging due to uncertainties. The document also provides a brief history of terrorism and different types of terrorism.
London oil and gas security summit 2013 neah ges

The document summarizes the agenda and speaker lineup for the 2nd Annual Oil & Gas Security 2013 Summit. The summit will focus on strengthening security strategies and operations to effectively combat emerging international threats to the oil and gas industry. Over two days, sessions will address assessing best terrorism prevention practices, security in high-risk regions like Algeria and Colombia, reducing insider threats, optimizing risk assessments, and OMV's security strategy in Yemen. The agenda is aimed at helping oil and gas companies improve security plans in light of new threats through best practices sharing and examining new technologies.
Impact of Transnational Terrorism [Notes]![Impact of Transnational Terrorism [Notes]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Impact of Transnational Terrorism [Notes]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Transnational terrorism has significant economic, social, and political impacts. Economically, terrorist attacks impose huge costs on lives and property while damaging industries like airlines and tourism. Socially, terrorist acts threaten racial and religious harmony by creating suspicion and tension among groups. Politically, governments respond by tightening security controls at borders and on travelers, which can infringe on personal freedoms and damage relations with the public.
RAND_RR573

- Terrorism remains a persistent threat in the United States, though most attacks since 9/11 have involved arson or conventional explosives and caused limited damage. Al Qaeda and other groups still aspire to conduct more destructive attacks.
- Terrorism risk models can estimate the likelihood and impact of some events similar to past attacks, but cannot reliably predict threats differently than historical incidents given limited data.
- The TRIA program helps ensure compensation is available after attacks and supports recovery, though it only covers incidents insurers can model, with taxpayers protected from extreme losses above $27.5 billion. Renewing TRIA may increase national security by promoting resilience.
Reflections on a Peace Building Approach to Conflict Prevention– Some Comment...

This document discusses a peacebuilding approach to conflict prevention in West Africa. It argues that peacebuilding must be linked to wider democratization and sustained development efforts. It analyzes the causes of conflicts in Africa, including shifts in global power relations after the Cold War, the rise of identity-based conflicts, increased availability of weapons, and the economic and political impacts of structural adjustment programs in the 1980s. The document calls for a human security approach focusing on four pillars: human security, democracy, transforming conflicts through political processes, and collective regional security.
Recommended
Turkey Domestic Terrorism & Evolving Threats

The ongoing terror attacks in Turkey are a continuation of long-standing domestic issues facing Ankara, overlaid by the new,
evolving threat posed by Islamic extremist groups. The attacks, which reflect each terror groups’ strategic intentions, can be
summarised into three broad groupings, with each group following a differing agenda and operational approach:
• Kurdish militant (such as the Kurdistan Workers Party [PKK])
• Domestic extremist ( including Marxist Leninist, anti-Western and anti-NATO groups – such as the Revolutionary People’s
Liberation Party–Front [DHKP-C])
• Islamic militant (specifically, Islamic State [IS])
The Marsh Report-Terrorism Risk Insurance 2010 

Despite an ever-changing terrorism risk insurance market, businesses from every industry sector continue to purchase coverage—more than 60 percent of organizations surveyed by Marsh bought coverage in 2009.
The Whiplash Effect Of Reactive Travel Risk Management

Recent events have caused companies and individuals to re-evaluate their travel risk management policies. Newsworthy incidents often drive decision making, but the key factors are an individual's experience, the activity, location, risk tolerance, and available support. The Mumbai attacks highlighted terrorism as a risk in India for many, though thousands continue dying in accidents. The targeting of Sri Lanka's cricket team in Pakistan raised awareness of security challenges there, showing that apolitical groups can be targets due to media attention. Time will tell if these and other attacks embolden issue motivated groups, though reactive planning may weaken long-term resilience more than address real risks. A systematic, continuously monitored approach to risk assessment is preferable to knee-jerk
final

The document discusses terrorism risk in the insurance sector. It defines terrorism and outlines the challenges in quantifying terrorism risk due to the unpredictable nature of terrorist attacks. Terrorism risk has three main components - threat, vulnerability, and consequence. Threat refers to the probability of an attack occurring, vulnerability is the probability of damage resulting from an attack, and consequence is the expected magnitude of damage. Terrorism risk is calculated as the product of these three components. Estimating each component is challenging due to uncertainties. The document also provides a brief history of terrorism and different types of terrorism.
London oil and gas security summit 2013 neah ges

The document summarizes the agenda and speaker lineup for the 2nd Annual Oil & Gas Security 2013 Summit. The summit will focus on strengthening security strategies and operations to effectively combat emerging international threats to the oil and gas industry. Over two days, sessions will address assessing best terrorism prevention practices, security in high-risk regions like Algeria and Colombia, reducing insider threats, optimizing risk assessments, and OMV's security strategy in Yemen. The agenda is aimed at helping oil and gas companies improve security plans in light of new threats through best practices sharing and examining new technologies.
Impact of Transnational Terrorism [Notes]![Impact of Transnational Terrorism [Notes]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Impact of Transnational Terrorism [Notes]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Transnational terrorism has significant economic, social, and political impacts. Economically, terrorist attacks impose huge costs on lives and property while damaging industries like airlines and tourism. Socially, terrorist acts threaten racial and religious harmony by creating suspicion and tension among groups. Politically, governments respond by tightening security controls at borders and on travelers, which can infringe on personal freedoms and damage relations with the public.
RAND_RR573

- Terrorism remains a persistent threat in the United States, though most attacks since 9/11 have involved arson or conventional explosives and caused limited damage. Al Qaeda and other groups still aspire to conduct more destructive attacks.
- Terrorism risk models can estimate the likelihood and impact of some events similar to past attacks, but cannot reliably predict threats differently than historical incidents given limited data.
- The TRIA program helps ensure compensation is available after attacks and supports recovery, though it only covers incidents insurers can model, with taxpayers protected from extreme losses above $27.5 billion. Renewing TRIA may increase national security by promoting resilience.
Reflections on a Peace Building Approach to Conflict Prevention– Some Comment...

This document discusses a peacebuilding approach to conflict prevention in West Africa. It argues that peacebuilding must be linked to wider democratization and sustained development efforts. It analyzes the causes of conflicts in Africa, including shifts in global power relations after the Cold War, the rise of identity-based conflicts, increased availability of weapons, and the economic and political impacts of structural adjustment programs in the 1980s. The document calls for a human security approach focusing on four pillars: human security, democracy, transforming conflicts through political processes, and collective regional security.
Terrorism and tourism

This presentation is about how terrorism effects the very tourism of any country and can take various disastrous form.
Intelligence and counter terrorism

Intelligence as a set of permanent institutions dates back only to the second half of the nineteenth century. But as information and news - in the dictionary meaning used in English since the middle of the fifteenth century, of 'knowledge as to events, communicated by or obtained from another, especially military' - it has always been collected as part of warfare
For a military, it can mean knowledge of the enemy and can distinguish between to defeat and to lose because information means knowledge and knowledge are power. Analysts see it as a package of information pending for clarification, and policymakers consider they should be informed so that they can meet the needs, stated or understood.
Intelligence gathers under the same umbrella the informational component of national security, internal and external policies, as well as certain aspects of international security in the case of global cross-entities (states, organizations).
This presentation is built up by gathering information from different references (Book, Articles, and Newspapers) by the author.
FBI Bomb Data Center General Information Bulletin 2012-1: The Bomb Threat Cha...

This document provides guidance on developing a bomb threat response plan with four key areas: planning and preparation, receiving a threat, evacuation, and search. It emphasizes the importance of organization, training, and evaluating each threat's credibility. Guidelines are presented for handling phone, email, and written bomb threats to preserve evidence. Factors for deciding the appropriate response like evacuation are discussed. The goal is to resolve threats safely while minimizing disruption.
Larry Hanauer Joins INSA as Vice President of Policy

Larry Hanauer has been hired as the new Vice President of Policy for the Intelligence and National Security Alliance (INSA). Hanauer has over 20 years of experience working in national security issues for the Department of Defense, Congress, and think tanks. In his new role, he will lead INSA councils and task forces to develop collaborative solutions to national security challenges. The President of INSA said Hanauer is a respected voice who will help strengthen public-private partnerships to address key intelligence issues.
Transnational terrorism

Transnational terrorism involves violence by internationally-linked groups across borders to cause psychological and economic impact. Al-Qaeda is a prominent example, founded by Osama bin Laden in 1989 to create a global Islamic caliphate and rid Western influence. Al-Qaeda operates through a network of affiliated terrorist organizations worldwide that share resources to plan and carry out attacks. The September 11, 2001 attacks demonstrated Al-Qaeda's deadly capabilities. In response, counterterrorism efforts have tightened security, increased intelligence sharing between countries, and sought to address the root causes that terrorists exploit to spread their radical ideology.
Impacts of terrorism on indian tourism 

Terrorism has a significant negative impact on tourism. The document discusses how terrorist attacks in India, such as in Mumbai, led to a 3.3% decline in foreign tourist arrivals in 2009. Such attacks damage the "Incredible India" brand and hurt the tourism industry, including airlines, hotels, travel agencies and tour operators. To mitigate these effects, the document recommends strengthening security measures, rebuilding tourism marketing efforts, and gaining foreign tourists' confidence in India's security.
SECJAM_REPORT_full_report_WEB1

The document summarizes the key outcomes and recommendations from the 2016 Security Jam, a four-day global online brainstorming event on security challenges attended by almost 2,500 experts from 131 countries. The top 10 recommendations that emerged were: 1) Create a global early-warning mechanism; 2) Improve big data analysis for early action; 3) Develop an integrated concept of security and defense; 4) Build trust in the Middle East through cooperation on non-security issues; 5) Strengthen women's role in conflict prevention and resolution; 6) Strengthen internal security cooperation in Europe; 7) Mainstream climate change into the security debate; 8) Incorporate the fight against organized crime and corruption into broader security policy; 9
Monitor Magazine Relaunched-2 copy

The document discusses security issues and threats faced by London Heathrow Airport. It outlines how Heathrow is a prime terrorist target as a major international transport hub vital to the UK economy. Several past terrorist plots targeting Heathrow are described, including IRA mortar attacks in 1994 and an attempted bombing of an El Al flight in 1986. The liquid bomb plot of 2006 had the biggest impact, nearly causing mass casualties on transatlantic flights and significantly increasing security procedures like banning liquids. Maintaining strong security at Heathrow involves cooperation between airport authorities, police, intelligence agencies, and technological improvements to counter the ongoing threat of terrorism.
Kidnap for ransom response

Pro-Intell provides kidnap response and prevention services globally. Their experienced response team handles all aspects of a kidnapping case, from initial support and advice, to negotiations and communications. They aim to have a consultant on-scene as soon as possible after an incident. Pro-Intell also offers kidnap prevention recommendations, such as avoiding routines, reducing wealth displays, and taking security precautions when traveling or away from home, to reduce the risk of becoming a victim.
Geopolitical intelligence analysis

STINews is manage by G3 Intelligence Ltd is a service provided by G3 Intelligence Ltd by which are given to companies, government agencies and professional, analysis and news in relation to issues of global concern: military, economic, cyber security, terrorism, health.
Instruments counter terrorism

The document discusses the various instruments used for counterterrorism, including diplomacy, law enforcement, financial controls, military power, and intelligence gathering. It notes that while each tool has limitations, using them together in an integrated manner is critical to fighting terrorism effectively. For each instrument, it provides a brief overview of how it can be used against terrorism and what some of the key limitations are.
Preventing conflict and promoting peace and security within nepad and the afr...

This document discusses the peace and security cluster of NEPAD and its operational challenges. It notes that while NEPAD recognizes the importance of peace and security for development, the original document had a limited understanding of the linkages between governance, security, and development. The document summarizes additions made at a later meeting to strengthen the peace and security cluster, including emphasizing democracy, human rights, and a human security approach. It argues this conceptualization of security is commendable and should scaffold NEPAD's implementation. However, challenges remain in translating these understandings into specific policies and ensuring effective implementation.
Safety tips during a terror attack

Safety Tips During a Terror Attack https://sites.google.com/site/adamquirkusa/blog/Safety-Tips-During-a-Terror-Attack
Risk In Our Society

The document discusses the concept of risk in society. It defines risk as uncertainty, and distinguishes between objective and subjective risk. Objective risk can be measured through statistics, while subjective risk is based on perception. It also defines chance of loss as the probability of an event occurring, and distinguishes between objective and subjective probabilities. The document outlines different categories of risk like pure risk and speculative risk, and types of risks like personal, property, and liability risks. It discusses the burden of risks on society and different methods of handling risk, including avoidance, loss control, retention, and insurance.
Preventing Conflict and Promoting Peace and Security Within NEPAD and the Afr...

This document discusses the peace and security cluster of NEPAD and the African Union. It notes that while NEPAD recognizes the importance of peace and security to development, it could take a more holistic, human security approach. It summarizes the key areas of focus in the peace and security cluster and comments that emphasizing democracy, governance, and human rights is commendable. However, translating these ideals into specific policies and ensuring effective implementation remains a challenge.
The society for peace studies and practice.2

The document announces the 6th annual conference of the Society for Peace Studies and Practice in collaboration with the Nigeria Army Peacekeeping Centre. The conference will take place from March 7-9, 2012 in Jaji, Kaduna, Nigeria. The conference aims to discuss challenges to national and international security in a globalized world, with sub-themes including domestic and international terrorism, border security, and the role of civil society in peacebuilding. It calls for abstract and paper submissions on topics related to security issues in Africa.
The Peace and Security Challenges Facing Africa: Can the African Union and NE...

This document discusses the challenges facing the African Union (AU) and the New Partnership for Africa's Development (NEPAD) in addressing peace and security issues on the continent. It analyzes the peace and security cluster of the NEPAD strategy, highlighting both positive and critical aspects. It examines the causes, nature, and context of conflicts in Africa in order to understand the values of security that need to be promoted. Finally, it discusses prospects for addressing current challenges and the need for genuine global partnership to resolve Africa's violent conflicts.
new cv PDF

Wessam Iraky is a multi-tasking security expert with over 20 years of experience in diverse environments including the UN in Haiti and various roles within the Egyptian Ministry of Interior such as an instructor of police sciences in Haiti, deputy commander of central security in North Sinai, and chief of security and investigation in Sinai. He holds qualifications in law and police sciences from the Police Academy in Egypt and is pursuing an MBA from international universities in Paris.
The FBI's War On Terror

A Look Into The Organizational Process and the Affects of Terrorism on Globalization and the World's Economy.
Arathiiiiiiiiiiiiiiiiiii

This document discusses the definition and types of terrorism. It begins by exploring the origins and early definitions of terrorism, then examines how terrorism is currently defined by international organizations and different legal systems. The document outlines six categories of terrorism as defined by a US task force in the 1970s. It also discusses the challenges of terrorism in India, including ethno-nationalist, religious, and left-wing terrorism. The document concludes that while the concept of terrorism is controversial and politically charged, it remains a major challenge for India and its democracy.
U.S. Heart of Ambassador Award Nominees 

This document profiles and summarizes three nominees for the U.S. Heart of Ambassador Award: Patrick Clemens, Cassandra C. Robinson-Bacon, and Amy Chrest. For each nominee, it provides a brief biography, what others said about their contributions and customer service, as well as their responses to questions about what they enjoy about working at Coca-Cola and what the nomination means to them. All three nominees expressed pride in working for Coca-Cola and their commitment to serving customers and communities.
OxPolicy (2016) Health begins at home

This report analyzes health inequalities in Oxfordshire, England. It finds that income deprivation and overcrowded housing have a significant negative impact on health outcomes in the county based on regression analysis of life expectancy and subjective health data. The report recommends policies like advocating living wages, improving early childhood programs, implementing a healthy homes initiative, better landlord/tenant education, and improving standards of housing.
More Related Content
What's hot
Terrorism and tourism

This presentation is about how terrorism effects the very tourism of any country and can take various disastrous form.
Intelligence and counter terrorism

Intelligence as a set of permanent institutions dates back only to the second half of the nineteenth century. But as information and news - in the dictionary meaning used in English since the middle of the fifteenth century, of 'knowledge as to events, communicated by or obtained from another, especially military' - it has always been collected as part of warfare
For a military, it can mean knowledge of the enemy and can distinguish between to defeat and to lose because information means knowledge and knowledge are power. Analysts see it as a package of information pending for clarification, and policymakers consider they should be informed so that they can meet the needs, stated or understood.
Intelligence gathers under the same umbrella the informational component of national security, internal and external policies, as well as certain aspects of international security in the case of global cross-entities (states, organizations).
This presentation is built up by gathering information from different references (Book, Articles, and Newspapers) by the author.
FBI Bomb Data Center General Information Bulletin 2012-1: The Bomb Threat Cha...

This document provides guidance on developing a bomb threat response plan with four key areas: planning and preparation, receiving a threat, evacuation, and search. It emphasizes the importance of organization, training, and evaluating each threat's credibility. Guidelines are presented for handling phone, email, and written bomb threats to preserve evidence. Factors for deciding the appropriate response like evacuation are discussed. The goal is to resolve threats safely while minimizing disruption.
Larry Hanauer Joins INSA as Vice President of Policy

Larry Hanauer has been hired as the new Vice President of Policy for the Intelligence and National Security Alliance (INSA). Hanauer has over 20 years of experience working in national security issues for the Department of Defense, Congress, and think tanks. In his new role, he will lead INSA councils and task forces to develop collaborative solutions to national security challenges. The President of INSA said Hanauer is a respected voice who will help strengthen public-private partnerships to address key intelligence issues.
Transnational terrorism

Transnational terrorism involves violence by internationally-linked groups across borders to cause psychological and economic impact. Al-Qaeda is a prominent example, founded by Osama bin Laden in 1989 to create a global Islamic caliphate and rid Western influence. Al-Qaeda operates through a network of affiliated terrorist organizations worldwide that share resources to plan and carry out attacks. The September 11, 2001 attacks demonstrated Al-Qaeda's deadly capabilities. In response, counterterrorism efforts have tightened security, increased intelligence sharing between countries, and sought to address the root causes that terrorists exploit to spread their radical ideology.
Impacts of terrorism on indian tourism 

Terrorism has a significant negative impact on tourism. The document discusses how terrorist attacks in India, such as in Mumbai, led to a 3.3% decline in foreign tourist arrivals in 2009. Such attacks damage the "Incredible India" brand and hurt the tourism industry, including airlines, hotels, travel agencies and tour operators. To mitigate these effects, the document recommends strengthening security measures, rebuilding tourism marketing efforts, and gaining foreign tourists' confidence in India's security.
SECJAM_REPORT_full_report_WEB1

The document summarizes the key outcomes and recommendations from the 2016 Security Jam, a four-day global online brainstorming event on security challenges attended by almost 2,500 experts from 131 countries. The top 10 recommendations that emerged were: 1) Create a global early-warning mechanism; 2) Improve big data analysis for early action; 3) Develop an integrated concept of security and defense; 4) Build trust in the Middle East through cooperation on non-security issues; 5) Strengthen women's role in conflict prevention and resolution; 6) Strengthen internal security cooperation in Europe; 7) Mainstream climate change into the security debate; 8) Incorporate the fight against organized crime and corruption into broader security policy; 9
Monitor Magazine Relaunched-2 copy

The document discusses security issues and threats faced by London Heathrow Airport. It outlines how Heathrow is a prime terrorist target as a major international transport hub vital to the UK economy. Several past terrorist plots targeting Heathrow are described, including IRA mortar attacks in 1994 and an attempted bombing of an El Al flight in 1986. The liquid bomb plot of 2006 had the biggest impact, nearly causing mass casualties on transatlantic flights and significantly increasing security procedures like banning liquids. Maintaining strong security at Heathrow involves cooperation between airport authorities, police, intelligence agencies, and technological improvements to counter the ongoing threat of terrorism.
Kidnap for ransom response

Pro-Intell provides kidnap response and prevention services globally. Their experienced response team handles all aspects of a kidnapping case, from initial support and advice, to negotiations and communications. They aim to have a consultant on-scene as soon as possible after an incident. Pro-Intell also offers kidnap prevention recommendations, such as avoiding routines, reducing wealth displays, and taking security precautions when traveling or away from home, to reduce the risk of becoming a victim.
Geopolitical intelligence analysis

STINews is manage by G3 Intelligence Ltd is a service provided by G3 Intelligence Ltd by which are given to companies, government agencies and professional, analysis and news in relation to issues of global concern: military, economic, cyber security, terrorism, health.
Instruments counter terrorism

The document discusses the various instruments used for counterterrorism, including diplomacy, law enforcement, financial controls, military power, and intelligence gathering. It notes that while each tool has limitations, using them together in an integrated manner is critical to fighting terrorism effectively. For each instrument, it provides a brief overview of how it can be used against terrorism and what some of the key limitations are.
Preventing conflict and promoting peace and security within nepad and the afr...

This document discusses the peace and security cluster of NEPAD and its operational challenges. It notes that while NEPAD recognizes the importance of peace and security for development, the original document had a limited understanding of the linkages between governance, security, and development. The document summarizes additions made at a later meeting to strengthen the peace and security cluster, including emphasizing democracy, human rights, and a human security approach. It argues this conceptualization of security is commendable and should scaffold NEPAD's implementation. However, challenges remain in translating these understandings into specific policies and ensuring effective implementation.
Safety tips during a terror attack

Safety Tips During a Terror Attack https://sites.google.com/site/adamquirkusa/blog/Safety-Tips-During-a-Terror-Attack
Risk In Our Society

The document discusses the concept of risk in society. It defines risk as uncertainty, and distinguishes between objective and subjective risk. Objective risk can be measured through statistics, while subjective risk is based on perception. It also defines chance of loss as the probability of an event occurring, and distinguishes between objective and subjective probabilities. The document outlines different categories of risk like pure risk and speculative risk, and types of risks like personal, property, and liability risks. It discusses the burden of risks on society and different methods of handling risk, including avoidance, loss control, retention, and insurance.
Preventing Conflict and Promoting Peace and Security Within NEPAD and the Afr...

This document discusses the peace and security cluster of NEPAD and the African Union. It notes that while NEPAD recognizes the importance of peace and security to development, it could take a more holistic, human security approach. It summarizes the key areas of focus in the peace and security cluster and comments that emphasizing democracy, governance, and human rights is commendable. However, translating these ideals into specific policies and ensuring effective implementation remains a challenge.
The society for peace studies and practice.2

The document announces the 6th annual conference of the Society for Peace Studies and Practice in collaboration with the Nigeria Army Peacekeeping Centre. The conference will take place from March 7-9, 2012 in Jaji, Kaduna, Nigeria. The conference aims to discuss challenges to national and international security in a globalized world, with sub-themes including domestic and international terrorism, border security, and the role of civil society in peacebuilding. It calls for abstract and paper submissions on topics related to security issues in Africa.
The Peace and Security Challenges Facing Africa: Can the African Union and NE...

This document discusses the challenges facing the African Union (AU) and the New Partnership for Africa's Development (NEPAD) in addressing peace and security issues on the continent. It analyzes the peace and security cluster of the NEPAD strategy, highlighting both positive and critical aspects. It examines the causes, nature, and context of conflicts in Africa in order to understand the values of security that need to be promoted. Finally, it discusses prospects for addressing current challenges and the need for genuine global partnership to resolve Africa's violent conflicts.
new cv PDF

Wessam Iraky is a multi-tasking security expert with over 20 years of experience in diverse environments including the UN in Haiti and various roles within the Egyptian Ministry of Interior such as an instructor of police sciences in Haiti, deputy commander of central security in North Sinai, and chief of security and investigation in Sinai. He holds qualifications in law and police sciences from the Police Academy in Egypt and is pursuing an MBA from international universities in Paris.
The FBI's War On Terror

A Look Into The Organizational Process and the Affects of Terrorism on Globalization and the World's Economy.
Arathiiiiiiiiiiiiiiiiiii

This document discusses the definition and types of terrorism. It begins by exploring the origins and early definitions of terrorism, then examines how terrorism is currently defined by international organizations and different legal systems. The document outlines six categories of terrorism as defined by a US task force in the 1970s. It also discusses the challenges of terrorism in India, including ethno-nationalist, religious, and left-wing terrorism. The document concludes that while the concept of terrorism is controversial and politically charged, it remains a major challenge for India and its democracy.
What's hot (20)
FBI Bomb Data Center General Information Bulletin 2012-1: The Bomb Threat Cha...

FBI Bomb Data Center General Information Bulletin 2012-1: The Bomb Threat Cha...
Larry Hanauer Joins INSA as Vice President of Policy

Larry Hanauer Joins INSA as Vice President of Policy
Preventing conflict and promoting peace and security within nepad and the afr...

Preventing conflict and promoting peace and security within nepad and the afr...
Preventing Conflict and Promoting Peace and Security Within NEPAD and the Afr...

Preventing Conflict and Promoting Peace and Security Within NEPAD and the Afr...
The Peace and Security Challenges Facing Africa: Can the African Union and NE...

The Peace and Security Challenges Facing Africa: Can the African Union and NE...
Viewers also liked
U.S. Heart of Ambassador Award Nominees 

This document profiles and summarizes three nominees for the U.S. Heart of Ambassador Award: Patrick Clemens, Cassandra C. Robinson-Bacon, and Amy Chrest. For each nominee, it provides a brief biography, what others said about their contributions and customer service, as well as their responses to questions about what they enjoy about working at Coca-Cola and what the nomination means to them. All three nominees expressed pride in working for Coca-Cola and their commitment to serving customers and communities.
OxPolicy (2016) Health begins at home

This report analyzes health inequalities in Oxfordshire, England. It finds that income deprivation and overcrowded housing have a significant negative impact on health outcomes in the county based on regression analysis of life expectancy and subjective health data. The report recommends policies like advocating living wages, improving early childhood programs, implementing a healthy homes initiative, better landlord/tenant education, and improving standards of housing.
Vida y obra de Samuel Hahnemann

Este documento presenta un resumen biográfico de Samuel Hahnemann, fundador de la homeopatía, en 3 oraciones: Hahnemann nació en Alemania en 1755, estudió medicina y se convirtió en el pionero de la homeopatía luego de experimentar con sustancias en sí mismo y observar sus efectos similares a enfermedades; promovió la homeopatía a través de publicaciones y la enseñanza pero también enfrentó críticas y ataques de sus opositores; falleció en 1843 en Francia después
Wikidata at Wikipeda Day 15 (2016) NYC

Wikidata is a free and open knowledge base that can be edited by anyone to store structured data about things like people, places, events and concepts. It is maintained by the Wikimedia Foundation and powered by Wikibase, an open source MediaWiki extension. Data in Wikidata is stored as statements about entities, with values that can include text, coordinates, quantities and more. This structured data is used and linked by Wikipedia, other Wikimedia projects and external websites and applications.
Cónicas 2 c-diana-aguilera-diana-silva

El documento describe las cuatro curvas cónicas principales: la circunferencia, elipse, parábola e hipérbola. Explica que se forman por la intersección de un plano con un cono y que el ángulo del plano y el lugar donde corta al cono determinan la curva cónica resultante. También presenta la ecuación general de una cónica y cómo los valores de sus coeficientes identifican qué tipo de curva cónica es.
Acuerdo Chile-Colombia

Chile es una república ubicada en Sudamérica con una población de casi 18 millones de habitantes. La capital y ciudad más poblada es Santiago. El idioma oficial es el español y la moneda es el peso chileno. La economía chilena se basa principalmente en la agricultura, la minería y los servicios.
Wikimedia Game Jam 20015: Wikimedia APIs

This document provides an introduction to the APIs of various Wikimedia projects including Wikipedia, Wikidata, Wikimedia Commons, and Wikiquote. It describes how each API can be used to access data from its respective project. The APIs allow users to retrieve page content, structured data, and metadata. Examples are given demonstrating how to access items, properties, and content via APIs and query interfaces for each project. Contact information is provided for questions about using the Wikimedia APIs.
Susanta _ CV.

Susanta Bhattacharya has over 10 years of experience in sales, business development, marketing, and team management. He is currently a Key Account Executive at Funskool India Limited, where he handles key accounts and analyzes market responses. Previously, he worked at Funskool India Limited as a Sales Promotion Executive for Eastern India and Nepal. He has also worked as a Team Leader in the kids department at Pantaloon Retail and as a Store-In-Charge at Esbee Exim Pvt. Ltd. Susanta holds an M.Com degree and is proficient in Windows, Microsoft Office, Tally, and internet skills.
Urgent vs. Important Tasks: Making The Most of Your Time

This talk was presented at Aerial Services, Inc. in Cedar Falls for employees. Much of the discussion focuses on the 4 Quadrants gleamed from Steven Covey's teachings. Additional comment is made on saying "no" to tasks, etc.
Barcelona Banff 2017 Meeting Information

The 2017 BANFF - SCT Congress will be held from Monday March 27th to Friday March 31st in Barcelona, Spain. The venue will be Barcelona University, which is located in the city center and has good public transportation access. The university has modern facilities including the Paraninf Room that can seat 488 people for plenary sessions, the Aula Magna that can seat 184 people for parallel sessions, and the Ramón y Cajal Room that has seating for 44 people on two floors and is equipped with a screen and WiFi like the other rooms. Contact information is provided for the congress.
Usa visit visa

The main focus of this presentation is US visa interview for Non Immigrant visa B2 category.The presentation includes all the possible question for US visa interview for visiting a friend or family in USA, Medical treatment in USA and US tourist visa. This presentation also describes your body language factors crucial for getting US visa.Any person who is seeking US visa in this category can prepare for us visa interview questions and he can get 100 % US visa.
Process to get a visa

1) The document outlines the 6 step process for applying for a visa to travel to the USA, which includes selecting a visa type, completing the DS-160 form, paying fees, scheduling an interview, attending the interview, and picking up your passport with visa.
2) It notes the most common visa types for business, tourism, study exchange programs, temporary work, and more.
3) It emphasizes that the interview and information provided in the DS-160 form are critical parts of the process, and recommends bringing valid identification documents like a passport and photo to ensure a smooth interview.
Xxi congreso nacional de entrevista clínica y comunicación

El documento trata sobre el XXI Congreso Nacional de Entrevista Clínica y Comunicación Asistencial que se centra en el tema "El lenguaje no verbal".
Ecotecnologia

Este documento presenta información sobre los problemas ambientales causados por la contaminación, el calentamiento global, la basura y la huella de carbono de la tecnología. Propone soluciones como el uso de energías renovables, reducir, reutilizar y reciclar, usar materiales biodegradables, ahorrar agua y energía, y participar en el activismo ambiental a nivel local.
Accounts Receivable Management

This document discusses an analysis performed by Dodd Tool, a manufacturing company, to determine whether it should relax its credit standards. It evaluates the potential effects on additional profit from sales, cost of increased investment in accounts receivable due to longer collection periods, and cost of higher expected bad debts. Specifically, Dodd Tool calculates that relaxing standards could increase sales by 3,000 units, resulting in $12,000 in additional profit. However, it also estimates this would lengthen collection periods, increasing receivables investment by $17,159 with a cost of $2,574. Bad debts are projected to double from 1% to 2% of sales. Dodd Tool aims to determine if the added profit outweighs the higher costs.
Neurogamificación: retos, MOOCs y motivación

El documento habla sobre la gamificación del aprendizaje y la importancia de los retos y la motivación. Varias citas discuten cómo alabar el esfuerzo empuja a las personas a trabajar duro y perseverar, y cómo las historias y emociones nos movilizan. Otra cita describe el aprendizaje como una aventura, el alumno como un héroe, y las actividades como retos con el tutor como mentor.
PRB Act

The Press and Registration of Books Act was established in India during British rule to regulate printing presses and require the registration of books and periodicals. It aimed to collect information about printing establishments, preserve copies of publications, and regulate anonymous literature. The Act required owners of printing presses to declare their activity and for publications to include identifying information like editor and publisher names. It established penalties for non-compliance and gave governing authority to the Registrar of Newspapers of India to allocate titles, registration numbers, and certificates to publications. The Act's objectives were to regulate the industry, not prohibit publication, while respecting freedom of speech.
Viewers also liked (18)
Urgent vs. Important Tasks: Making The Most of Your Time

Urgent vs. Important Tasks: Making The Most of Your Time
Xxi congreso nacional de entrevista clínica y comunicación

Xxi congreso nacional de entrevista clínica y comunicación
Similar to The evolution of terrorism after paris
Crisis Management for Terror Related Events

New guidance from the CIPR and the Government's Centre for the Protection of National Infrastructure (CPNI) offers best practice guidance for communications professionals on the preparation and management of threats from hostile actors. More: https://newsroom.cipr.co.uk/cipr-and-uk-government-publish-terrorism-crisis-management-guidance/preview/db0ae1f554fad89e9ffdbe8dc16b616af3dc3011
The changing face of terrorism

The document discusses the evolving threat of terrorism faced by global businesses. It notes that there are two types of potential terrorist attackers in Western countries - returning extremists from conflict zones who are more capable, and homegrown radicals who are less capable but harder to detect. It warns that civilian casualties are now the primary target of attacks, increasing the focus on liability and casualty exposures for businesses. Finally, it provides recommendations for how companies can prepare for and respond to terrorist attacks, such as monitoring threat levels, reviewing security measures, and coordinating with local law enforcement.
Active Shooter - The New Cyber

Active shooter incidents have now emerged as a threat that cannot be ignored or minimized. Although it’s a difficult subject, it is important for businesses to consider active shooter/workplace violence insurance to cover gaps and grey areas that exist in standard coverage insurance. Here’s why.
Homeland Security Bill

The homeland security bill aims to prevent loss of life and property from disasters through collaboration and information sharing to recognize threats. It applies to preventing both terrorism and natural disasters by introducing preventive measures. Police need contingency plans to continue operating during recovery periods, while their role in recovery is secondary to organizations like FEMA. The bill also raises training requirements and funds for responders to hazards like terrorism.
Ransomware attack

In today's digital age, the threat of ransomware and data breaches is a growing concern for individuals and businesses. Ransomware is a type of malicious software that blocks access to a computer system or encrypts valuable data until a ransom is paid. Data breaches occur when unauthorized individuals gain access to sensitive information, often resulting in financial loss and reputational damage. Recent high-profile ransomware attacks have targeted organizations in various sectors, emphasizing the need for robust cybersecurity measures. The impact of these attacks can be devastating, leading to significant financial losses and disruptions in services. To prevent ransomware attacks, regular data backups, robust cybersecurity measures, employee training, and the use of cybersecurity tools and technologies are essential. Cybersecurity awareness and training play a crucial role in mitigating risks, and organizations must be prepared to respond effectively to an attack. Understanding cyber attack statistics and trends helps in staying informed and adapting defenses. Collaboration between government, law enforcement, and the private sector is vital in combating cybercrime through information sharing, legislation, and enforcement efforts. It is crucial for individuals and organizations to stay vigilant, implement preventive measures, and leverage advanced security technologies to protect against evolving cyber threats.
Confrance presntstation

This document discusses the importance of information sharing in combating terrorism. It argues that one of the key reasons governments have struggled to curb terrorism is a lack of effective information sharing between agencies. The document proposes that electronic information sharing (EIS) could help develop better tools for intelligence gathering and counterterrorism efforts by facilitating coordination, collaboration, and real-time information exchange between intelligence communities, government agencies, and other stakeholders. Effective EIS may allow for improved decision-making, risk management, and emergency response by inventorying assets and promoting a culture of multidirectional information sharing.
CIS Security Risk Mgmt Solutions Brochure

Over the past 25 years, Critical Intervention Services has provided security consulting and training services to over 1,000 communities and organizations. Some key services and accomplishments include: pioneering a unique community protection methodology in the early 1990s that has been shown to reduce crime; launching an effective school security program in 2013; and creating the first private U.S. security force focused on anti-terrorism in 2004. CIS now provides a wide range of security consulting services worldwide and has trained over 12,000 professionals.
Cybersecurity Risk Management Tools and Techniques (1).pptx

A database containing sensitive information on ongoing criminal investigations is hacked and confidential case details are leaked online. The incident response plan would provide guidelines on immediate actions to contain the breach, secure remaining systems, notify relevant stakeholders, and initiate forensic analysis to identify the source of the attack.
Security Precautions for the Hospitality Industry

The document discusses security precautions for the hospitality industry against terrorism. It begins with definitions of terrorism and an overview of why the hospitality industry is vulnerable. Common vulnerabilities of hotels are described, such as open access areas. Potential indicators of terrorist surveillance or attack are provided. The document then outlines protective measures that can be implemented, such as access control, monitoring, planning for emergencies. It discusses government programs that help the industry and reviews some past terrorist attacks on hotels. Strategies for counter-terrorism are presented.
Question 1Outline the various components of transportation and.docx

Question 1
Outline the various components of transportation and cargo security. Specifically what threats exist and what security measures have been implemented to address those threats.
This assignment should be a minimum of 300 words.
Question 2
Select two (2) infrastructure sectors and thoroughly discuss how the strategic objectives of the sector-specific security plan (SSP) will be applied to the two sectors you selected.
This assessment should be a minimum of 300 words.
GENERAL OVERVIEW
Industrial security is concerned with protecting the manufacturing process. Major threats to industrial security include accidents, natural disasters, internal theft, sabotage, and espionage.
Library and museum security is concerned with controlling both criminal and noncriminal threats to library and museum inventories which often include rare, priceless, and irreplaceable objects. Common threats to library and museum security include theft, vandalism fire, floods, water damage, and other environmental elements.
Office building security is concerned with securing office buildings. Major threats to office building security include fire, inadequate evacuation routes, terroristic activity, bomb threats, theft, burglary, robbery, sexual assault, and executive kidnapping. In addition to the aforementioned major threats, office buildings, because of their open access (i.e., numerous entry and exit points, multiple agencies occupied one building, and shared common areas such as lounges and restrooms) and highly desired equipment and supplies (e.g., copper piping, recyclable materials, office supplies, payroll checks, classified information, office equipment, etc.), provide additional functionality threats to security that must be addressed by security personnel.
Residential security is concerned with securing personal residences. For security experts the home is considered a very unsafe place especially when residents are asleep. Threats to residential security include accidents, medical emergencies, fire, theft, burglary, vandalism, assault, homicide, property damage, personal injury, and natural disasters.
Retail loss prevention is an area of security that is primarily focused on the retail industry. Internal and external thefts are the major source of loss for the retail industry. Internal theft usually occurs at the hands of employees who take cash and/or merchandise, abuse the referral system, and utilize a variety of other tactics. External sources of loss include vandalism, burglary, robbery, credit card fraud, coupon fraud, bad checks, and shoplifting. Technological advances create unique challenges for the retail industry as retail sales are conducted in facilities and wirelessly from home computers, mobile phones, tablets and other devices.
As a result, card-not-present fraud is an increasing concern for retailers as it results in fraud losses. In addition, as the types of products demanded by consumers and th ...
eu insurance fraud 1st_Final VS255 330

This document provides information about the upcoming European Insurance Fraud Summit conference taking place on November 3rd and 4th, 2015 in Amsterdam. The summit will address the latest threats and solutions related to insurance fraud across Europe. Over the two days, experts from leading insurers will discuss topics like detecting fraud at the application and claims stages, using new technologies like predictive analytics, and challenges of cross-border fraud. Attendees will gain practical advice on dealing with different fraud types and learn about fraud prevention techniques. The agenda includes sessions on prioritizing anti-fraud strategies, mapping fraud trends, developing anti-fraud teams and tools, and managing fraud risks online. There will also be panels and case studies on fostering collaboration
Mass transit security awareness white paper

Terör sınır tanımıyor. Taktik, teknik ve hedef seçimleri sıklıkla değişiyor. Ulaşım geçmişte olduğu gibi günümüzde de yüksek risk seviyesini muhafaza ediyor. Okunmasında yarar var.
The Necessity of Security Guard Services in Edmonton Public Events.pdf

Central Protection Services is offering you Security Guard Services with cutting-edge security techniques and tools to supervise the unprotected areas. Our superior security guard services offer you armed and unarmed security guards to manage your manual and systematic safety needs respectively. We manage and protect your commercial, residential, and corporate needs in a reliable and fully enclosed manner. We take care of your assets, investments, and buildings by deeply analyzing the risk and prevention needs for offering a customized security solution for you. Our services include well-trained guards for manual supervision, mobile patrolling to unreached areas of your region, fire alarm systems, central locking systems, access control, and many more. We design the security guard services with mutual understanding and prior experience makes us more reliable to select. Central Protection Services is successfully operating branches in Alberta wide, Fort MacMurray, Calgary, Airdrie, and Edmonton and people believe us for our reliable services.
OSACO brochure - Finance

OSACO is a firm that specializes in managing human risks within organizations. They recognize that while people are capable of great things, they are also fallible and mistakes will happen. OSACO works to anticipate problems, minimize risks, and restore integrity and trust after issues occur. Their goal is to help organizations learn from mistakes in order to continuously improve how they address human factors and failures. OSACO provides services across multiple sectors, including business, finance, humanitarian work, sports, and media.
OSACO brocure Overview - Banking

The document discusses OSACO Group, which provides services to help organizations address risks caused by human fallibility. This includes assisting financial institutions, sports organizations, humanitarian groups, businesses operating abroad, and media companies. OSACO helps clients anticipate where problems may occur due to human errors or misdeeds, put processes and controls in place to prevent or minimize issues, and restore integrity and trust if issues do happen. The company brings expertise in compliance, governance, risk management, investigations and training to address challenges such as financial crimes, corruption, and risks to personnel safety.
Facebook

This document provides a summary of influence operations from 2017 to 2020. It discusses how threat actors have evolved tactics like moving from large campaigns to more targeted operations and blurring lines between authentic and inauthentic content. The document outlines trends seen over this period like perception hacking and increased operational security. It proposes mitigation strategies platforms and researchers can take like combining automated and manual enforcement, improving detection tools, and building partnerships for information sharing.
Cyber Threat Intelligence

Cyber Threat Intelligence (CTI) primarily focuses on analysing raw data gathered from recent and past events to monitor, detect and prevent threats to an organisation, shifting the focus from reactive to preventive intelligent security measures.
Before the Breach: Using threat intelligence to stop attackers in their tracks

All information, data, and material contained, presented, or provided on is for educational purposes only.
Company names mentioned herein are the property of, and may be trademarks of, their respective owners.
It is not to be construed or intended as providing legal advice.
Company names mentioned herein are the property of, and may be trademarks of, their respective owners and are for educational purposes only.
17 U.S. Code § 107 - Limitations on exclusive rights: Fair use
Notwithstanding the provisions of sections 106 and 106A, the fair use of a copyrighted work, including such use by reproduction in copies or phonorecords or by any other means specified by that section, for purposes such as criticism, comment, news reporting, teaching (including multiple copies for classroom use), scholarship, or research, is not an infringement of copyright.
CYBERSECURITY CYBERCRIME CYBER INTELLIGENCE GROUP

The C3i Group works with inter-agency partners and the security industry, collecting information intelligence related to risks emanating from cyberspace. We provide direction and leadership to industry, focusing on the intrinsic risks and threats posed by: potential shortcomings in the cyber information security infrastructure; actions of non-state actors, cyber- terrorists, and criminals; foreign business competitors and governments intent on illegitimately acquiring proprietary information and trade secrets.
Similar to The evolution of terrorism after paris (20)
Cybersecurity Risk Management Tools and Techniques (1).pptx

Cybersecurity Risk Management Tools and Techniques (1).pptx
Question 1Outline the various components of transportation and.docx

Question 1Outline the various components of transportation and.docx
The Necessity of Security Guard Services in Edmonton Public Events.pdf

The Necessity of Security Guard Services in Edmonton Public Events.pdf
Before the Breach: Using threat intelligence to stop attackers in their tracks

Before the Breach: Using threat intelligence to stop attackers in their tracks
More from Graeme Cross
Temporarily idle sites - COVID19

Aons's guide for construction companies which has currently closed sites in the wake of the current COVID19 pandemic.
Surety and Guarantee

A surety bond is a financial instrument through which an insurance company guarantees the successful performance of an Aon
client to a third party, known as a beneficiary or employer. It is a written agreement that provides compensation in the event
that specified obligations are not performed within a stated period.
Client bulletin; Brexit

With an ever-changing political scene and limited time left to conclude the negotiations for the United Kingdom’s (UK) exit from the European Union (EU), attention is now beginning to turn to the potential consequences of Brexit. This paper discusses the issues that insurers face and considers the interplay between insurers’ contractual obligation to continue to service policies (including paying claims) versus the practical impact that local regulation might have on their ability to do so.
BioEnergy Value Proposition

The document introduces Aon's BioEnergy practice and the solutions it provides clients in the biomass and energy from waste industries. It outlines Aon's BioGen facility, which offers a seamless insurance product covering the project lifecycle with a focus on risk engineering and fire protection. It also describes Aon's risk consulting services, benchmarking and analytics tools, expertise in policy wordings, and online knowledge sharing portal. The goal is to help clients in this specialized industry reduce risks and insurance costs.
IFRS Report - Important upcoming accounting changes 

The new IFRS 9 rules effective January 2018, and equivalent US GAAP standards (ASU 2016-13) effective in 2019, are aimed at
increasing the accuracy and transparency of how credit risk is represented on a company’s Balance Sheet and P&L. Both new
standards include requirements around the use of both historic as well as forward looking credit information in order to calculate
the provisions for credit losses (Expected Credit Losses).
Aon Cyber Risk Solutions

Aon’s cyber capabilities can support organisations in embracing
a risk based approach. This facilitates the deployment of a
more effective cyber insurance strategy to help optimise the
total cost of risk associated with cyber exposures
Aon property laser placemat

Reducing an organisation’s property total cost of risk
(TCOR) is fundamental to its operational resiliency and
financial bottom line. Aon Property Laser is a unique
property and business interruption risk management
methodology that incorporates leading-edge diagnostic
and analytical tools to quantify risk exposure. By
identifying and analysing key property performance
indicators, Aon Property Laser helps organisations
to improve their risk profile, while also making the
insurance policy work more effectively should a loss
occur. Our property experts benchmark pre-loss and
post-loss risk management practices, activities and
results, to help assess and optimise an organisation’s
property risk profile.
Prepare to Disclose Climate Risk

Many businesses and governments have been reporting on environmental and climate data for over 15 years now, but the way they do is set to change. Following the UN’s Paris
Agreement to address climate risk by cutting greenhouse gas emissions, financial regulators are increasingly concerned about the systemic risks that climate change poses to the financial
system. After the 2008 financial crisis, regulators do not want any disorderly transitions in the market due to a misallocation of capital
Supply chain diagnostic brochure

Aon has developed a proprietary diagnostic tool to help risk leaders quickly assess their organization’s global supply chain exposures across a variety of key marketplace supply chain indicators.
In the complex and dynamic global risk environment, risk managers play an increasingly vital role in helping their organizations understand, prioritize and manage critical exposures affecting their operations and supply chains.
Today, along with catastrophic property risks, expanding cyber threats, terrorism, supplier insolvency, product integrity and reputational issues, businesses relying on global supply chains must navigate widening geopolitical challenges brought by rising nationalism.
As business leaders, planning, finance and operations executives strive to anticipate how these developments might affect their cross-border trade relationships, effective and forward-looking supply chain risk management is critical to sound decision-making. Aon’s Supply Chain Diagnostic helps clients flag supply chain vulnerabilities and improve resiliency.
Global supply chain management brochure

Aon’s Approach to supply chain management recognizes the wide spectrum of risks that can negatively impact our clients’ business operations, some of which are common to all industries and others very specific to a particular segment. We bring efficiency to the process by triaging each client’s specific supply chain needs, and deploying a hand-picked team of specialists that can develop industry specific solutions ranging from risk identification and quantification to tailored risk financing programs and claim resolution strategies.
Aon Global Client Network Fact Sheet

The Aon Global Client Network is the backbone of Aon Risk Solutions’ international network, connecting clients and colleagues with expertise, counsel and resources available in over 120 countries in which Aon Risk Solutions is represented. Aon’s network is the largest majority owned network, unsurpassed in geographic breadth and depth of talent.
Aon Global Client Network map

Aon Global Client Network provides risk management, reinsurance, and human resources services globally. It operates through owned, management controlled, correspondent, and coordinated offices across the Americas, Europe, Africa, the Middle East, Asia, and Australasia/Pacific regions serving over 200 countries and territories.
Cyber Client Alert

On June 27, 2017, a widespread WannaCry ransomware variant referred to by a number of names, including GoldenEye, Petya, NotPetya, and ExPetr, began impacting computer systems around the world. Similar to the recent WannaCry ransomware attack, victims are being asked to pay a ransom of $300 in bitcoin.
Global optimisation index

Are you a risk or finance leader of an organization with exposures across multiple territories?
Take our Global Optimization Index survey. The 75 questions are
directly related to international risk management and will help you to measure your company’s risk management practices as compared to Aon’s best practice standards and find areas of focus to enhance the performance of your multinational risk management approach.
Aon Thought Leadership Guide

Aon’s continually growing directory of intellectual capital provides the latest insights into innovative ways of identifying, quantifying, and managing a wide range of current and emerging risks.
2017 Risk Maps

Aon’s guide to Political Risk, Terrorism & Political Violence
The Political Risk Map primarily focuses on economic and fiscal risks, specifically in emerging economies, while the Terrorism and Political Violence Map consider issues such as civil commotion and war and has a global focus.
While comparisons are possible across the two maps and certain countries will be affected by both sets of perils, these are two specific risks with accompanying sub-sets of perils that help to establish ratings for each country.
Together these maps are helping our clients to better understand the challenges facing them when operating in diverse, international geographies. We would welcome the opportunity to discuss these challenges in more detail with you and explain how Aon’s Crisis Management teams can help identify, manage and mitigate risks to help insulate your people, assets and operations wherever they are located in the world.
Environmental insurance market status Q1 2017

This paper provides an update on the status of the marketplace for environmental insurance as of early 2017. It starts with a look at the environmental risks associated with a number of common industrial, commercial and institutional activities, and then considers various aspects of the marketplace, with a look at the insurance companies that sell environmental coverage, a review of who buys it and what is new in the market for this year.
Global Cyber Market Overview June 2017

The document provides an overview of the global cyber insurance market, including:
- The cyber insurance market is still in its infancy globally but has grown significantly in recent years, especially in the US where it is estimated to be worth $1.5 billion in 2015.
- The largest market is the US, driven by data breach legislation, high-profile cyber attacks increasing awareness, and demand from companies storing personal data.
- The upcoming European GDPR regulation coming into effect in 2018 is expected to be a major driver for the growing but still relatively nascent European cyber insurance market.
- Various industries like retail, healthcare, and financial institutions are among the largest buyers of cyber insurance.
Aon GDPR prepare and protect solution placemat

The EU’s General Data Protection
Regulation (GDPR) comes into effect on
the 25th of May 2018, enforcing strict
new measures for any organisation
globally handling the personal data
of EU individuals.
Organisations have steps to take to
comply with GDPR and meet the
ongoing data privacy rights of their
clients and employees.
Failure to comply may result in enforcement
action, including fines of up to €20 million
or 4% of your organisation’s annual
worldwide revenue, whichever is greater.
Aon GDPR white paper

“The European Union data privacy landscape is about to undergo dramatic change, with lasting enterprise wide implications for the way that organisations handle, protect and use the personal data of EU individuals.
Organisations of all sizes, across all industries, and geographies that process personal data of EU residents need to take steps now to comply with the new EU General Data Protection Regulation by 2018, to satisfy management fiduciary duties
and avoid potentially costly penalties.”
More from Graeme Cross (20)
IFRS Report - Important upcoming accounting changes 

IFRS Report - Important upcoming accounting changes
Recently uploaded
Federal Authorities Urge Vigilance Amid Bird Flu Outbreak | The Lifesciences ...

Federal Authorities Urge Vigilance Amid Bird Flu Outbreak | The Lifesciences ...The Lifesciences Magazine
Federal authorities have advised the public to remain vigilant but calm in response to the ongoing bird flu outbreak of highly pathogenic avian influenza, commonly known as bird flu.#WenguiGuo#WashingtonFarm Guo Wengui Wolf son ambition exposed to open a far...

Since fleeing to the United States in 2014, Guo Wengui has founded a number of projects in the United States, such as GTV Media Group, GTV private equity, farm loan project, G Club Operations Co., LTD., and Himalaya Exchange.
Snigdha-Sreenath-Minor-v-Travancore-Devaswom-Board-WPCNO-39847-OF-2023-2024-L...

केरल उच्च न्यायालय ने 11 जून, 2024 को मंडला पूजा में भाग लेने की अनुमति मांगने वाली 10 वर्षीय लड़की की रिट याचिका को खारिज कर दिया, जिसमें सर्वोच्च न्यायालय की एक बड़ी पीठ के समक्ष इस मुद्दे की लंबित प्रकृति पर जोर दिया गया। यह आदेश न्यायमूर्ति अनिल के. नरेंद्रन और न्यायमूर्ति हरिशंकर वी. मेनन की खंडपीठ द्वारा पारित किया गया
The Rise of Christian Persecution In Islamic Countries (1).pdf

The Rise of Christian Persecution In Islamic Countries (1).pdfECSPE - Saving the Persecuted and Enslaved
Recent years have seen a disturbing rise in violence, discrimination, and intolerance against Christian communities in various Islamic countries. This multifaceted challenge, deeply rooted in historical, social, and political animosities, demands urgent attention. Despite the escalating persecution, substantial support from the Western world remains lacking.
16062024_First India Newspaper Jaipur.pdf

Find Latest India News and Breaking News these days from India on Politics, Business, Entertainment, Technology, Sports, Lifestyle and Coronavirus News in India and the world over that you can't miss. For real time update Visit our social media handle. Read First India NewsPaper in your morning replace. Visit First India.
CLICK:- https://firstindia.co.in/
#First_India_NewsPaper
12062024_First India Newspaper Jaipur.pdf

Find Latest India News and Breaking News these days from India on Politics, Business, Entertainment, Technology, Sports, Lifestyle and Coronavirus News in India and the world over that you can't miss. For real time update Visit our social media handle. Read First India NewsPaper in your morning replace. Visit First India.
CLICK:- https://firstindia.co.in/
#First_India_NewsPaper
Organisations.pdf k[poikdip-jhhohuhejhnjhn

ग्रेटर मुंबई के नगर आयुक्त को एक खुले पत्र में याचिका दायर कर 540 से अधिक मुंबईकरों ने सभी अवैध और अस्थिर होर्डिंग्स, साइनबोर्ड और इलेक्ट्रिक साइनेज को तत्काल हटाने और 13 मई, 2024 की शाम को घाटकोपर में अवैध होर्डिंग के गिरने की विनाशकारी घटना के बाद अपराधियों के खिलाफ सख्त कार्रवाई की मांग की है, जिसमें 17 लोगों की जान चली गई और कई निर्दोष लोग गंभीर रूप से घायल हो गए।
Reuters Institute Digital News Report 2024

Reuters Institute Digital News Report 2024Reuters Institute for the Study of Journalism, Oxford University
Slide deck with charts from our Digital News Report 2024, the most comprehensive exploration of news consumption habits around the world, based on survey data from more than 95,000 respondents across 47 countries.Saraikistan; unveiling the demand for a seperate province._20240522_011317_00...

Here is the knowledge about why the people of Saraikistan wants a seperate province. Reasons behind their demanding a seperate province.
A draft Ukraine-Russia treaty from April 2022

A draft Ukraine-Russia treaty from April 2022, published here in full for the first time.
ACSA confirms operational readiness ahead the arrival of Heads of State at OR...

ACSA says it is ready for the arrival of foreign heads of state ahead of the Presidential Inauguration on Wednesday at OR Tambo International Airport.
在线办理(latrobe毕业证书)拉筹伯大学毕业证Offer一模一样

学校原件一模一样【微信:741003700 】《(latrobe毕业证书)拉筹伯大学毕业证》【微信:741003700 】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
【主营项目】
一.毕业证【q微741003700】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【q/微741003700】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Howard Fineman, Veteran Political Journalist and TV Pundit, Dies at 75

Howard Fineman, Veteran Political Journalist and TV Pundit, Dies at 75LUMINATIVE MEDIA/PROJECT COUNSEL MEDIA GROUP
From his beginnings with a daily newspaper, he moved easily through Newsweek magazine to cable news and, later, to the frontiers of online journalism.15062024_First India Newspaper Jaipur.pdf

Find Latest India News and Breaking News these days from India on Politics, Business, Entertainment, Technology, Sports, Lifestyle and Coronavirus News in India and the world over that you can't miss. For real time update Visit our social media handle. Read First India NewsPaper in your morning replace. Visit First India.
CLICK:- https://firstindia.co.in/
#First_India_NewsPaper
13062024_First India Newspaper Jaipur.pdf

Find Latest India News and Breaking News these days from India on Politics, Business, Entertainment, Technology, Sports, Lifestyle and Coronavirus News in India and the world over that you can't miss. For real time update Visit our social media handle. Read First India NewsPaper in your morning replace. Visit First India.
CLICK:- https://firstindia.co.in/
#First_India_NewsPaper
Youngest c m in India- Pema Khandu Biography

Pema Khandu, born on August 21, 1979, is an Indian politician and the Chief Minister of Arunachal Pradesh. He is the son of former Chief Minister of Arunachal Pradesh, Dorjee Khandu. Pema Khandu assumed office as the Chief Minister in July 2016, making him one of the youngest Chief Ministers in India at that time.
लालू यादव की जीवनी LALU PRASAD YADAV BIOGRAPHY

Discover the life and times of Lalu Prasad Yadav with a comprehensive biography in Hindi. Learn about his early days, rise in politics, controversies, and contribution.
projet de traité négocié à Istanbul (anglais).pdf

Ceci est le projet de traité qui avait été négocié entre Russes et Ukrainiens à Istanbul en mars 2022, avant que les Etats-Unis et la Grande-Bretagne ne détournent Kiev de signer.
Recently uploaded (19)
Federal Authorities Urge Vigilance Amid Bird Flu Outbreak | The Lifesciences ...

Federal Authorities Urge Vigilance Amid Bird Flu Outbreak | The Lifesciences ...
#WenguiGuo#WashingtonFarm Guo Wengui Wolf son ambition exposed to open a far...

#WenguiGuo#WashingtonFarm Guo Wengui Wolf son ambition exposed to open a far...
Snigdha-Sreenath-Minor-v-Travancore-Devaswom-Board-WPCNO-39847-OF-2023-2024-L...

Snigdha-Sreenath-Minor-v-Travancore-Devaswom-Board-WPCNO-39847-OF-2023-2024-L...
The Rise of Christian Persecution In Islamic Countries (1).pdf

The Rise of Christian Persecution In Islamic Countries (1).pdf
Saraikistan; unveiling the demand for a seperate province._20240522_011317_00...

Saraikistan; unveiling the demand for a seperate province._20240522_011317_00...
ACSA confirms operational readiness ahead the arrival of Heads of State at OR...

ACSA confirms operational readiness ahead the arrival of Heads of State at OR...
Howard Fineman, Veteran Political Journalist and TV Pundit, Dies at 75

Howard Fineman, Veteran Political Journalist and TV Pundit, Dies at 75
The evolution of terrorism after paris
- 1. What happened in Paris? While information on the terrible events in Paris on the 13th November will continue to crystallise over the coming days and weeks, the terrorists’ actions continue a theme seen in recent attacks. The three events in Paris; suicide bombings, armed attacks on public spaces, armed hostage taking & suicide bombings - each is an approach employed elsewhere in Europe, the Levant and North Africa recently. The nature of the attacks reflect the continued evolution of tactics by Islamic militants. Concentrations of people at predictable times present an attractive target for this type of terrorism. Clearly concerts or publicised business events, public transport & transport hubs, shopping malls & retail hubs and hospitality (hotel & restaurant) locations are examples of locations that present the desired target type. The attacks were relatively low-tech in that the attack relied primarily on automatic weapons, with relatively small device sizes employed for the suicide element. This is also a practical reflection of the limitations often imposed on terror groups by competent security services – it is more difficult to manufacture devices of a significant size due to security services monitoring of key bomb making ingredients. Active shooter attacks, small device attacks as well as the “lowest-tech” approaches of a knife attack or the use of a car as a kinetic weapon will continue be part of the terrorists approach, especially amongst terror cells with no access to the training or logistics of Middle Eastern or North African based groups. Critically, the targeting approach is to achieve the maximum casualties from any single attack, rather than the primary targets of “traditional terrorism”; the police, the military, the judiciary and the government or inflicting damage on infrastructure, assets and operations. While individual organisations may not be in a position to stop an attack or avoid being targeted, there are steps that can be considered to reduce the potential for an attack or limit the scale and duration of an attack. Risk. Reinsurance. Human Resources. The Paris attack & the continuing evolution of terrorism Whatever any organisation does, it is not possible to manage away the risk from terrorism. It requires active engagement to understand the local threat, the potential impacts and the proactive solutions that are available to mitigate the risk. People Business interuption Reputation Property Liability Terrorism impacts
- 2. Mitigation considerations in light of the “changing face of terrorism” What can individual organisations do to reduce their attractiveness to terror groups and limit the freedom of an attacker to access their building and people. • Own the access points into your building; allowing you to minimise access points during higher threat periods and lock down access through these at a moment’s notice. • Have the ability to establish hard segregation between any public reception area and the wider employee areas – significantly delay the ability of an attacker to roam your premises. This could include, for example, remotely locking down elevator access and locking out access controls into service areas. • Consider establishing Active Shooter protocols – there is well developed guidance in this area to prepare managers and employees on actions if a hostile threat is identified within an organisation’s space. • Proximity to public transport hubs, public spaces, high profile buildings or individuals may increase the potential to be impacted by terrorist events. • Recognise that it is only Police response that will address defeat a hostile individual on your site and that this response may be some time away; critically, liaison with the Police prior to an event is vital to understanding how long this may be, what information they will need when they arrive on site and what you can do to facilitate their actions. • While there is an opportunistic element to terrorism targeting, it remains a worthwhile activity to regularly assess the risk posed by terrorism to an organisation, in order to inform risk mitigation and ultimately, risk transfer. From an employer or operator of a property, consider your ability to demonstrate you have done all that is reasonable and practical to provide a safe environment. Considerations for your terrorism insurance strategy Traditionally terrorism related insurance has focussed on the property damage and business interruption resulting from an attack. While this clearly remains part of the spectrum of terrorism impacts, that spectrum is broadening and organisations need to develop a more responsive insurance programme to match these additional impacts, as well as coverage for unintended impacts (hoax or perceived threats that stop operations or activities – often a result of heightened tension, post events); a programme that considers the potential impacts on people, property, revenue and reputation. Whatever any organisation does, it is not possible to manage away the risk from terrorism. It requires active engagement to understand the local threat, the potential impacts and the proactive solutions that are available to mitigate the risk. Contacts Terrorism Broking Consulting Tony Day Director CBO Counter Terrorism tony.day1@aon.co.uk Scott Bolton Director, Counter Terrorism scott.bolton1@aon.com Contingency Risk Event Cancellation Adrian Thomas Executive Director adrian.thomas@aon.co.uk Terrorism Claims Mark Fox Claims Leader, Property Casualty mark.fox@aon.co.uk Risk. Reinsurance. Human Resources. Aon Risk Solutions Global Broking Centre About Aon Aon plc (NYSE:AON) is a leading global provider of risk management, insurance brokerage and reinsurance brokerage, and human resources solutions and outsourcing services. Through its more than 69,000 colleagues worldwide, Aon unites to empower results for clients in over 120 countries via innovative risk and people solutions. For further information on our capabilities and to learn how we empower results for clients, please visit: http://aon.mediaroom.com. © Aon plc 2015. All rights reserved. The information contained herein and the statements expressed are of a general nature and are not intended to address the circumstances of any particular individual or entity. Although we endeavor to provide accurate and timely information and use sources we consider reliable, there can be no guarantee that such information is accurate as of the date it is received or that it will continue to be accurate in the future. No one should act on such information without appropriate professional advice after a thorough examination of the particular situation. Aon UK Limited is authorised and regulated by the Financial Conduct Authority. aon.com
