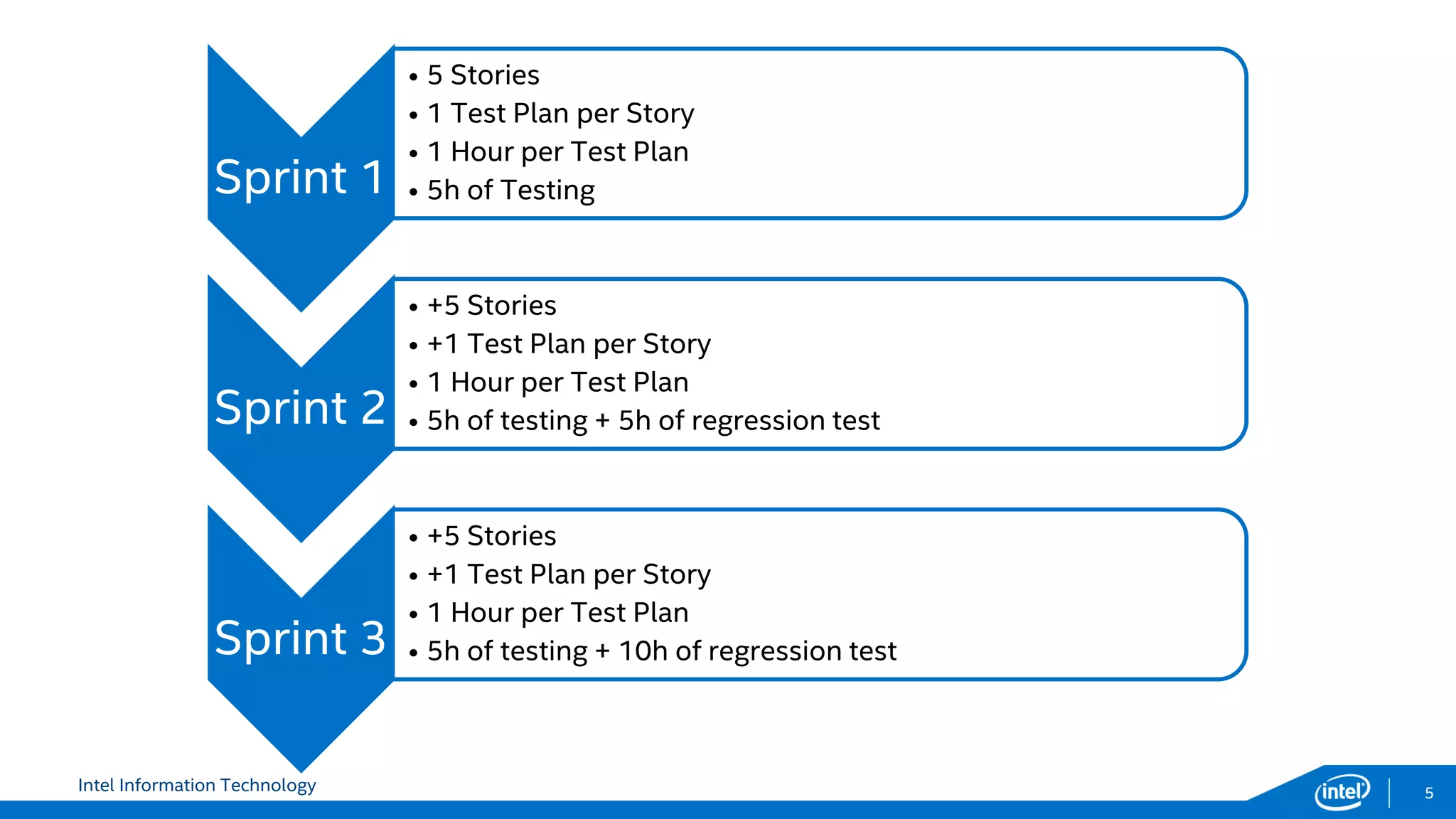
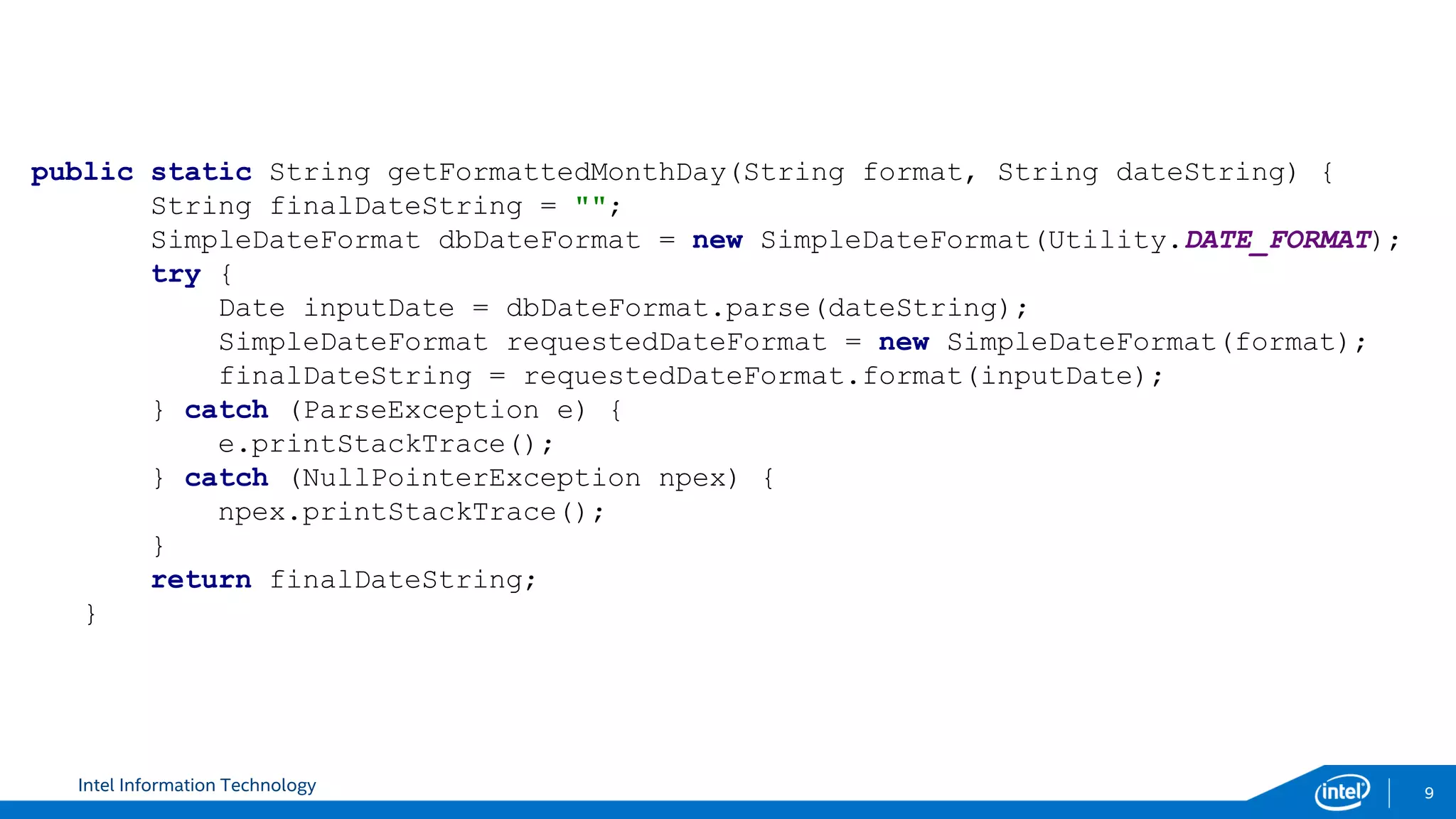
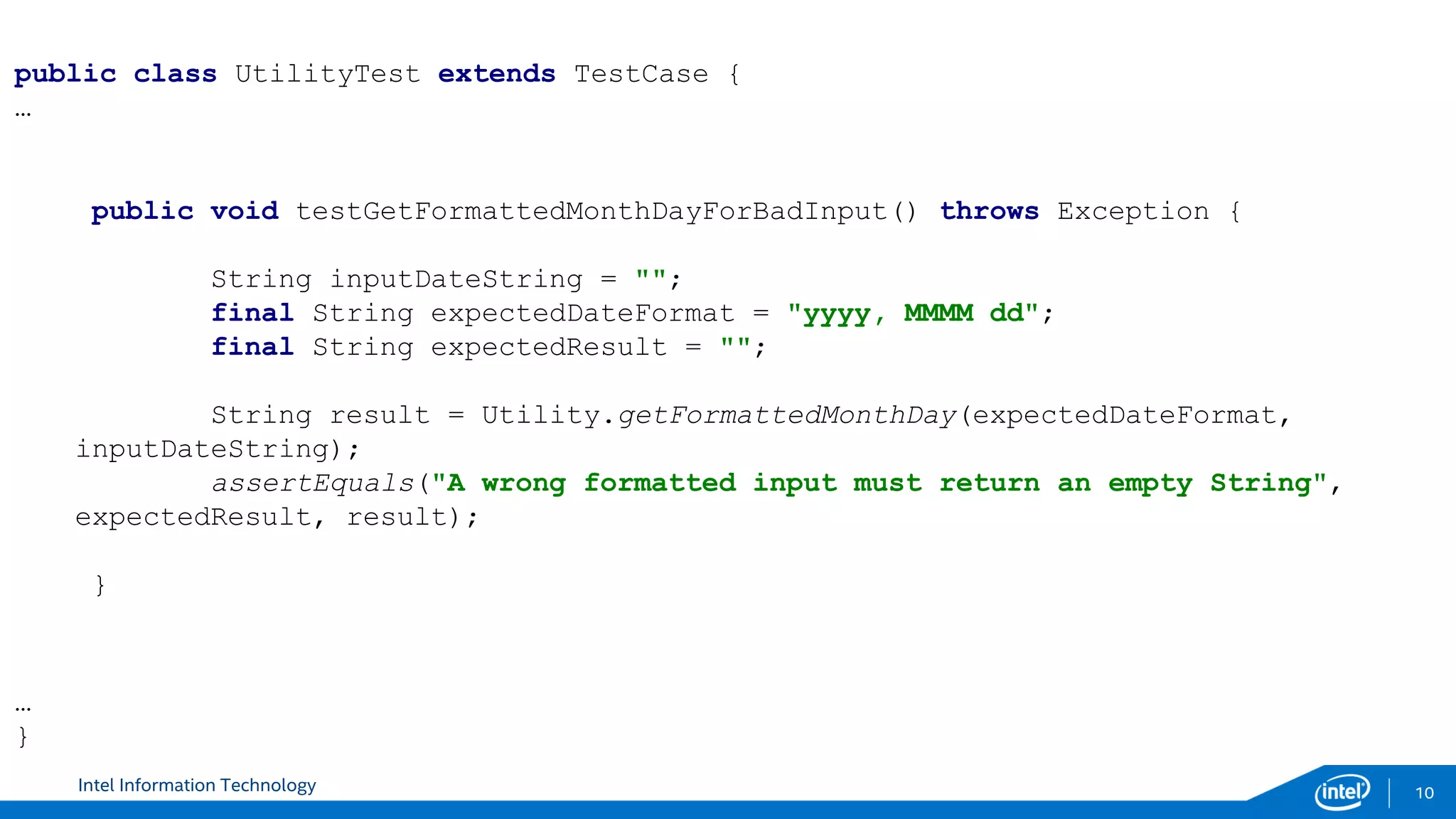
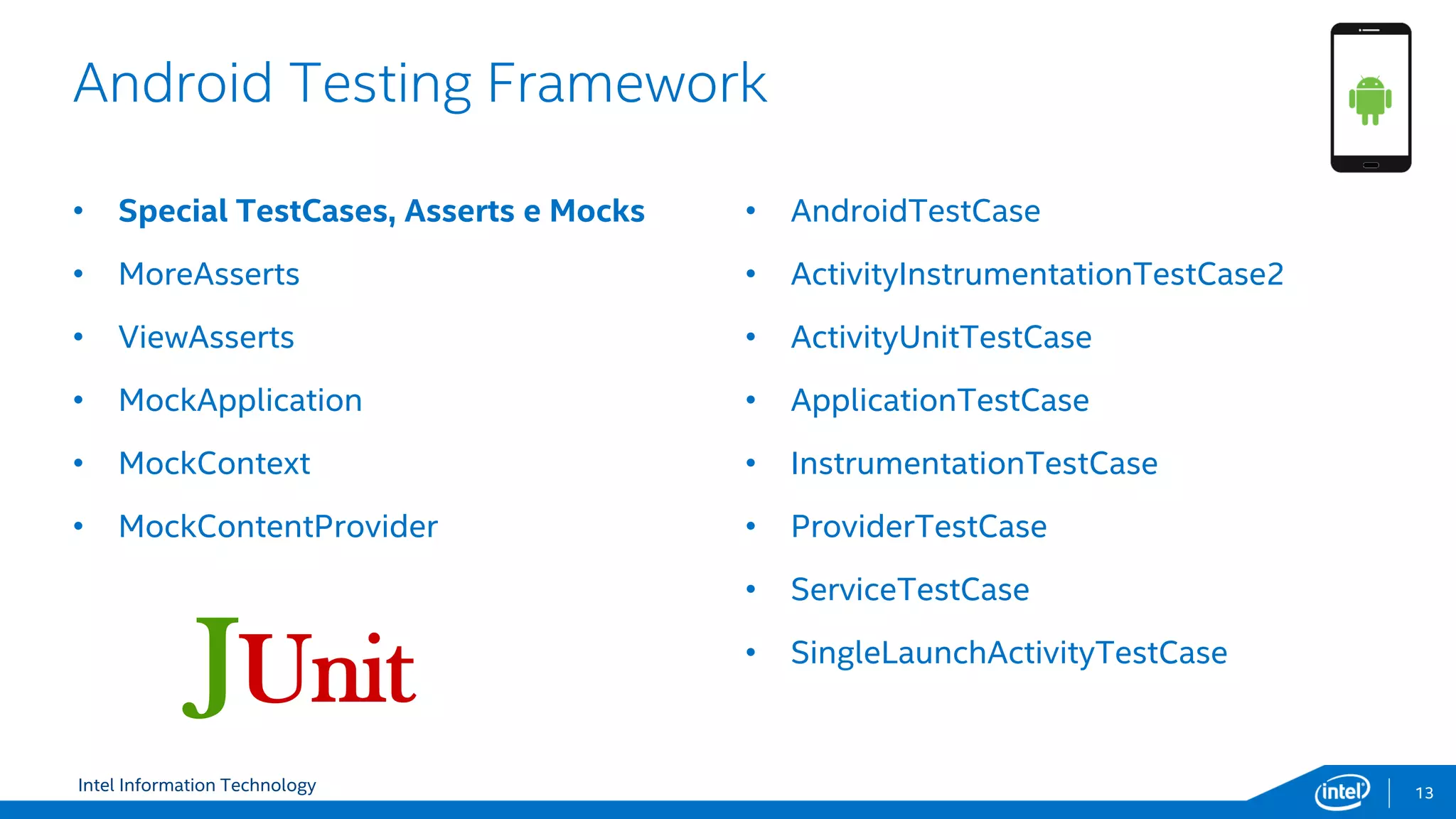
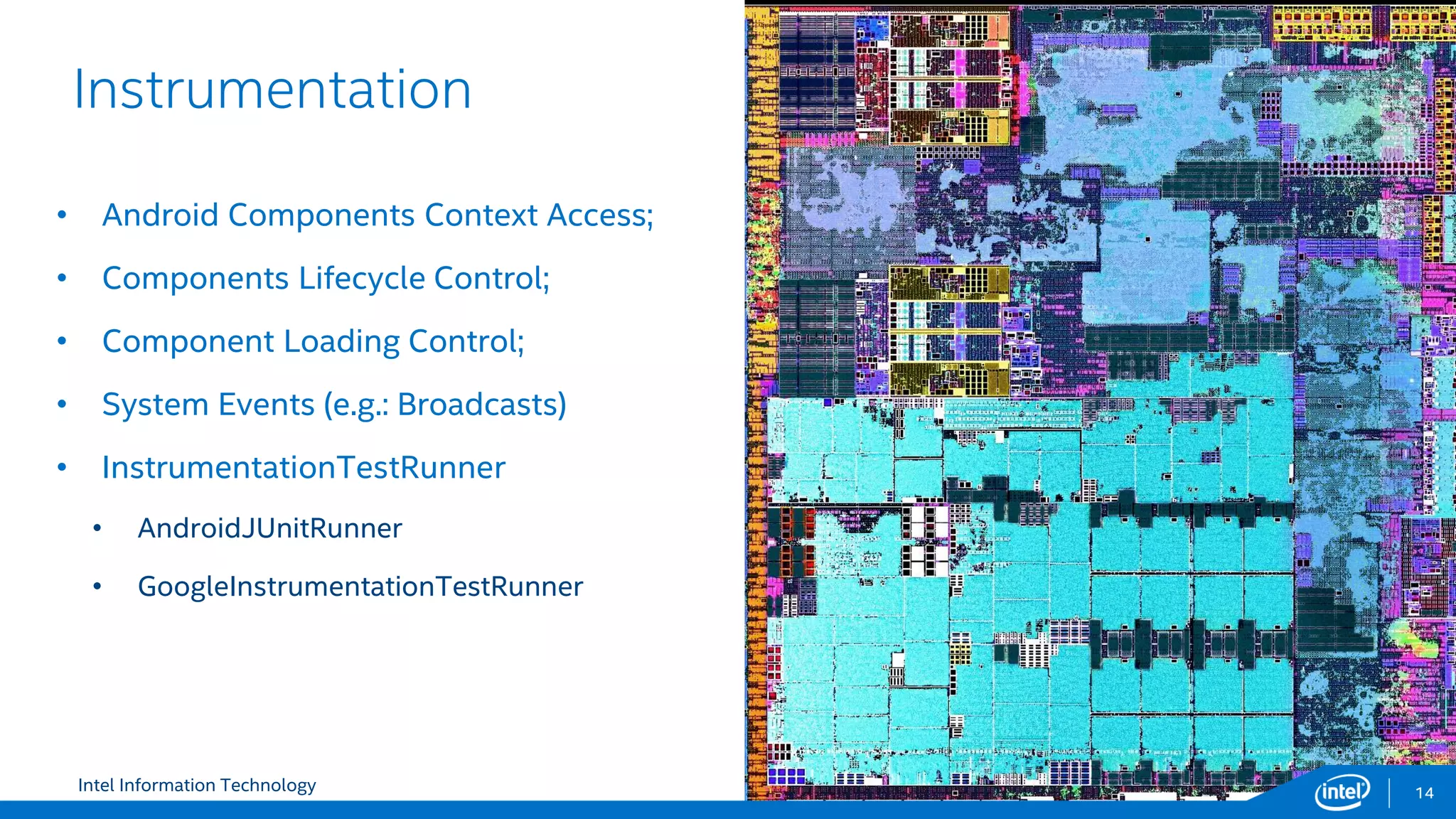
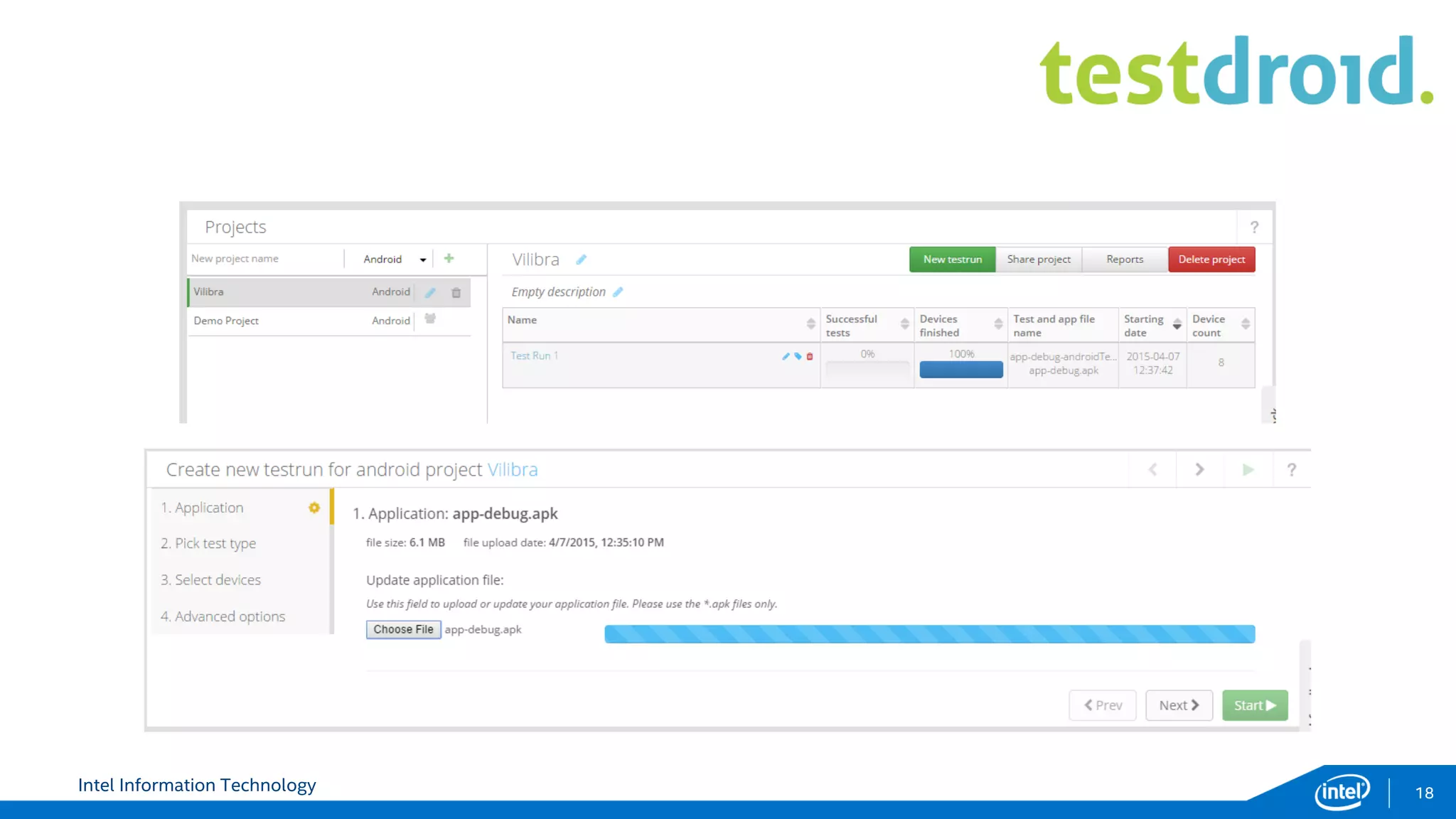
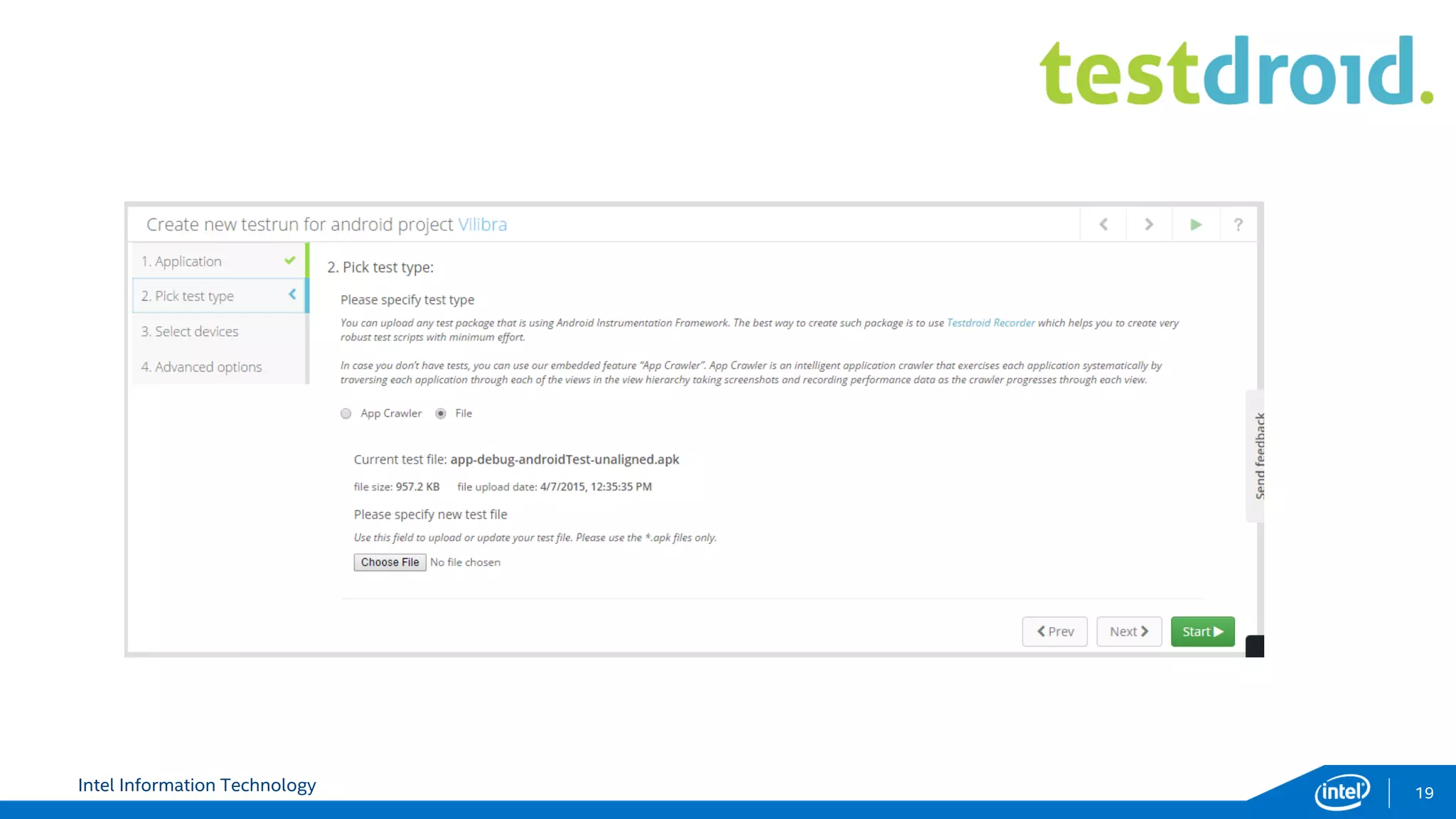
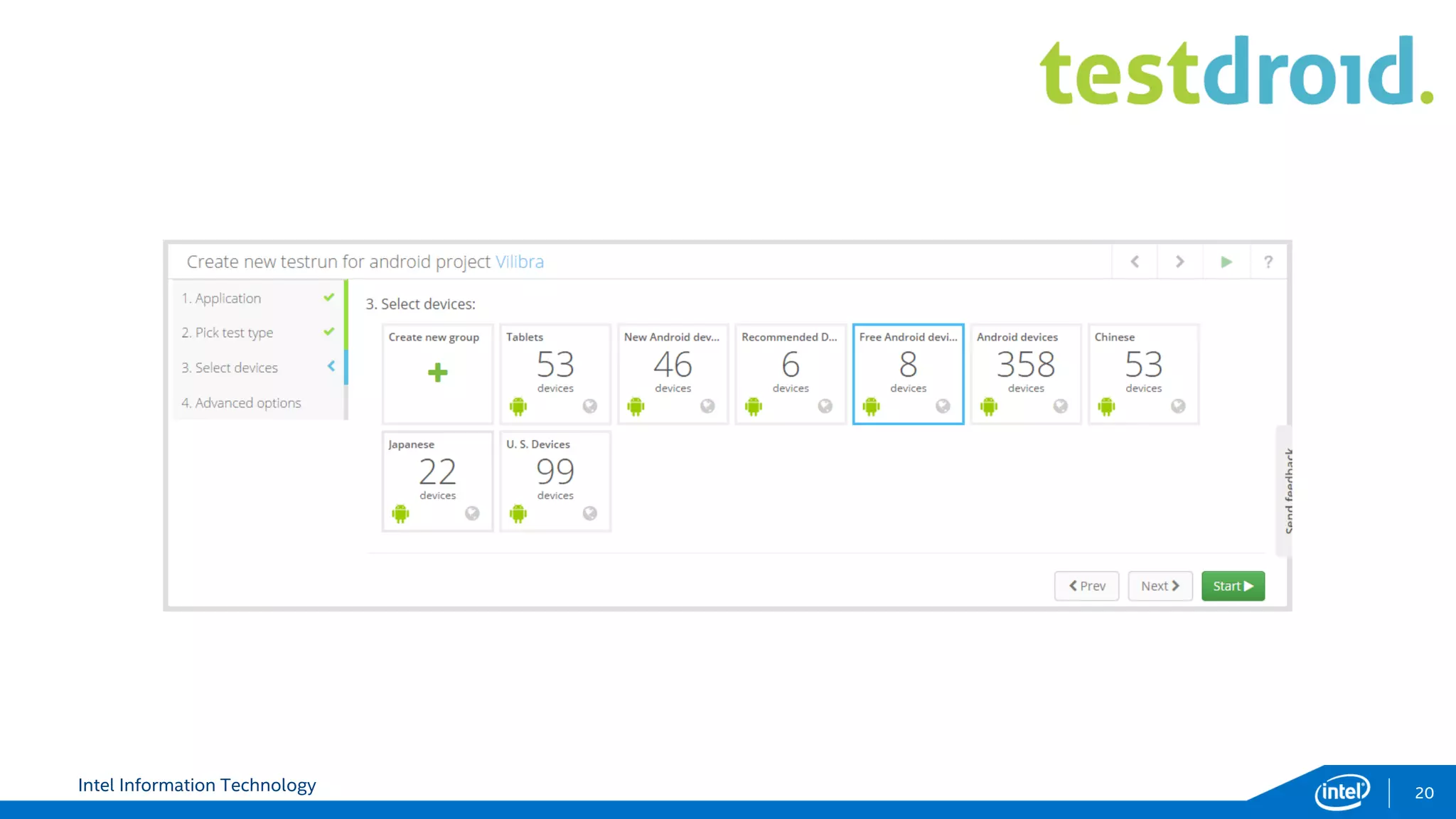
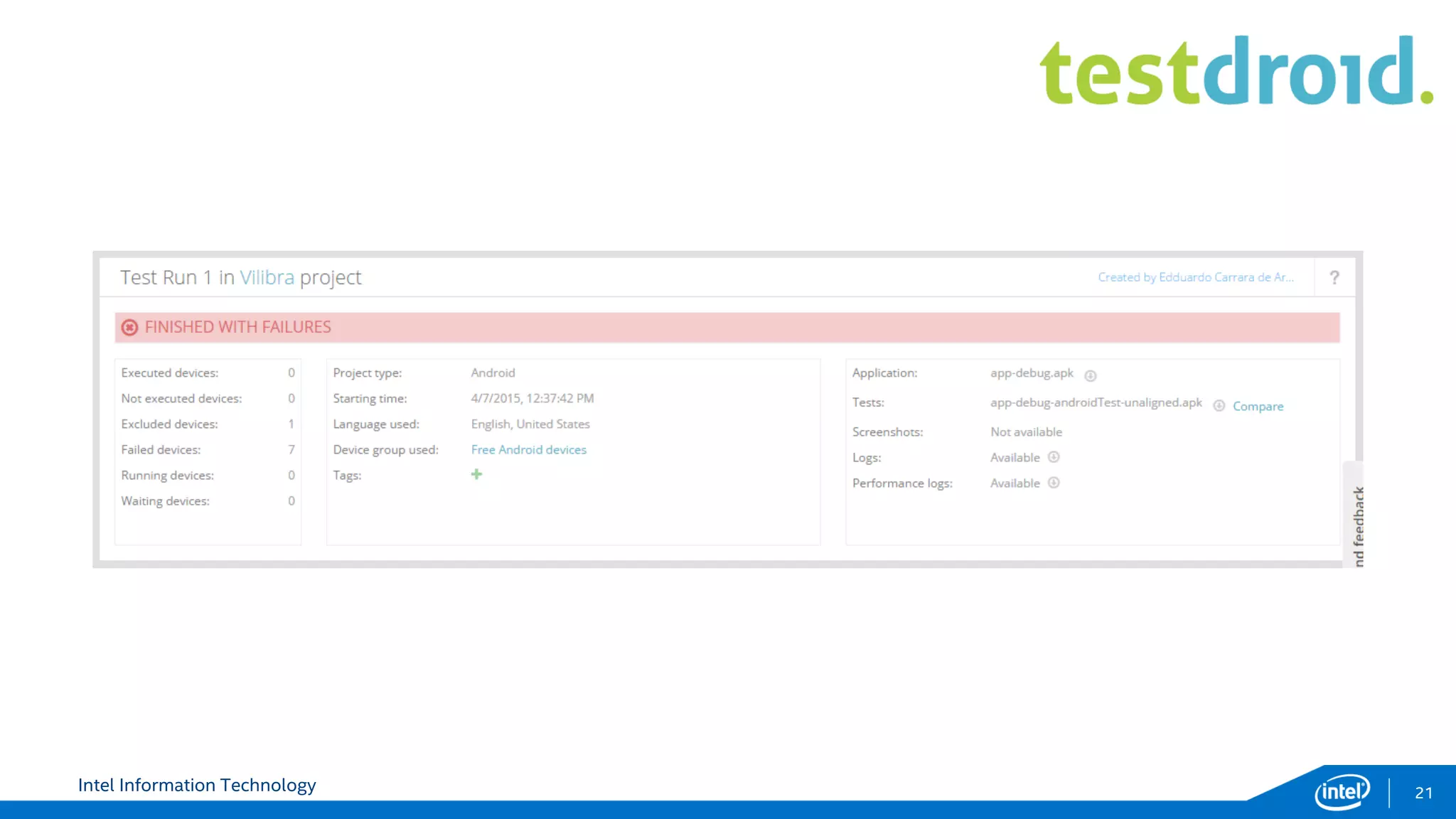
The document outlines a testing strategy for Android applications by Intel, emphasizing the importance of encompassing multiple sprints, each with test plans and regression testing. It highlights various tools and frameworks like JUnit, Espresso, and Android testing components to facilitate effective testing processes. Additionally, it discusses the future directions for testing, including cross-app testing and continuous integration.