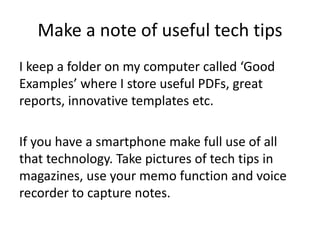
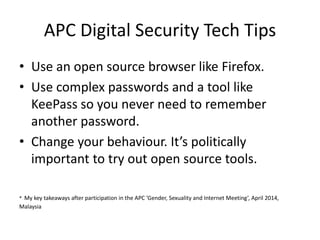
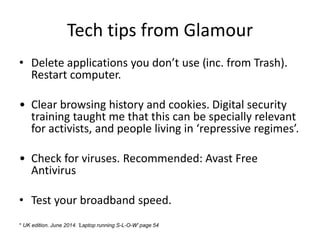
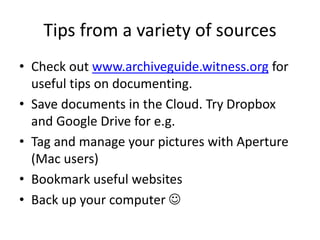
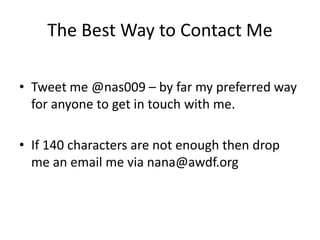
The document provides tech tips for non-techies, emphasizing the importance of a positive attitude towards technology and lifelong learning. It shares personal experiences of learning and experimenting with various tech tools, as well as practical security tips for online safety. Additionally, it lists resources for further learning and communication preferences of the author.