The document outlines the capabilities and functionalities of Oracle's WebRTC session controller and related telecom service exposure solutions. It discusses API management, service exposure, and integration of telecom services with other applications, focusing on features such as security, policy control, and partner management. Additionally, it highlights the importance of next-generation service delivery platforms for improving operational efficiency in telecoms and offers insights into training and support for implementation.



















![Service
Exposure
Layer
SMS
POST
rest/sms/sendMessage
{
"sender": "36301234567",
"addresses": [ "36302345678" ],
"message": "Hello!"
}
1
3
Hello!
{ "result": "OK" }
2](https://image.slidesharecdn.com/tadhackoraclealerantoptarewebinar-140515123813-phpapp02/85/TADHack-Oracle-Alerant-Optare-Webinar-21-320.jpg)







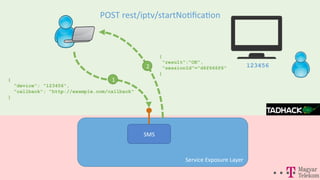
![Service
Exposure
Layer
IPTV
POST
rest/iptv/sendMessage
1
3
{ "result": "OK"}
2
~~~~
~~~
~~~
~~~~
~
~
~
popup
{
"device": "123456",
"template": "popup_with_2_options",
"params": [
{"name": "message", "value": "Missed call from Alan"},
{"name": "option1", "value": "Call back"},
{"name": "option2", "value": "Ok"}
],
"correlator": "8f5dec0a"
}
123456](https://image.slidesharecdn.com/tadhackoraclealerantoptarewebinar-140515123813-phpapp02/85/TADHack-Oracle-Alerant-Optare-Webinar-30-320.jpg)














