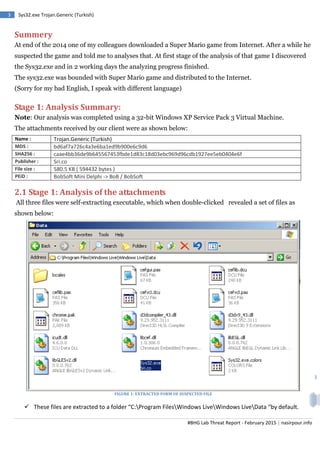
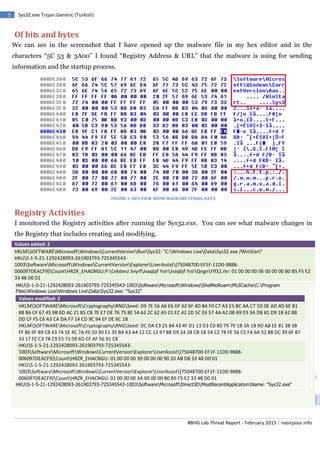
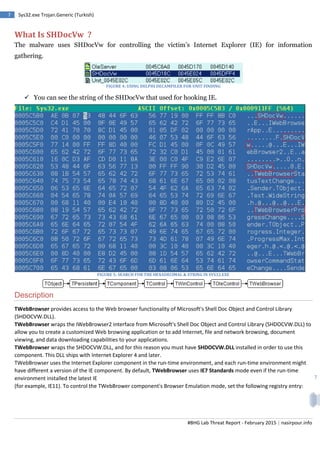
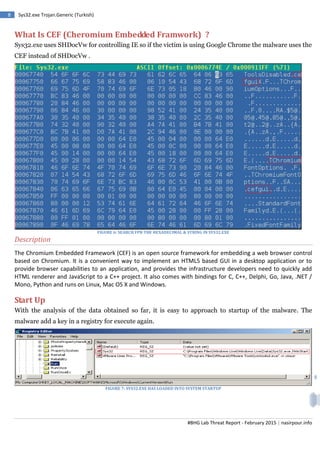
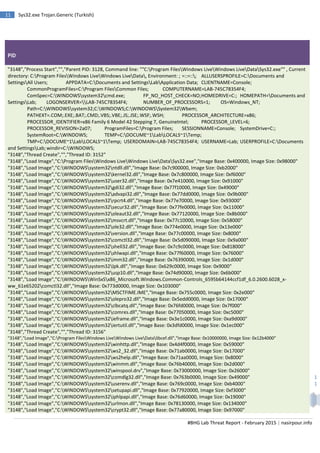
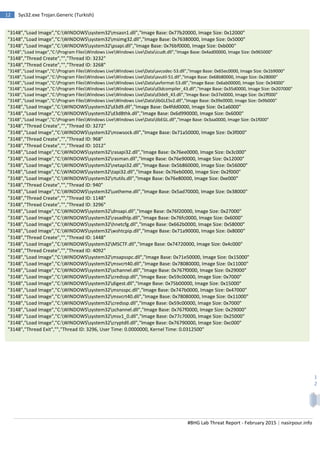
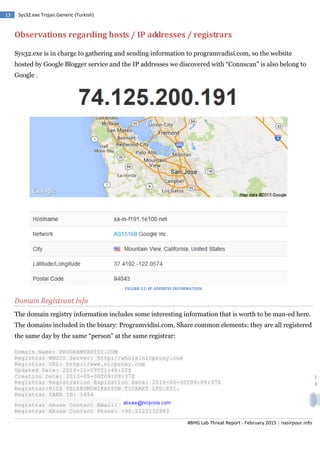
The malware report analyzes the Sys32.exe Trojan found on a user's system after downloading a Super Mario game from the internet. The analysis found that Sys32.exe extracts 30 files and adds/modifies registry entries at startup to persist between reboots. It uses the SHDocVw library to hook Internet Explorer for information gathering. The malware communicates outbound via encoded strings in the executable referencing registry keys and URLs.