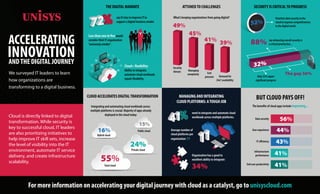
SURVEY RESULTS: ACCELERATING INNOVATION AND THE DIGITAL JOURNEY - INFOGRAPHIC
•
1 like•806 views
Unisys surveyed IT leaders to learn how organizations are transforming to a digital business. For more information visit: www.unisys.com/generationd
Report
Share
Report
Share
Download to read offline
Recommended
Manage Risk by Protecting the Apps and Data That Drive Business Productivity

Today you face the challenge of securing a business environment transformed by technologies such as cloud and new workforce requirements such as mobility, BYO and third-party talent.
The Growing U.S. IT Productivity Gap

Productivity growth has slowed down despite our rising investment in IT.
Secrets of getting Legacy to Cloud - setting the scene

Setting the scene for EuroCloud session with 5 different perspectives on the issues around moving Legacy applications to the Cloud. The digital landscape, digital transformational, Shadow IT, public vs private etc.
[Webinar Slides] Data Privacy for the IM Practitioner - Practical Advice for ...![[Webinar Slides] Data Privacy for the IM Practitioner - Practical Advice for ...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar Slides] Data Privacy for the IM Practitioner - Practical Advice for ...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Learn actionable steps to provide a high-level plan for implementing a privacy program in conjunction with your existing organizational RIM/IG program(s).
Want to follow along with the webinar replay? Download it here for FREE: https://info.aiim.org/data-privacy-for-the-im-practitioner-practical-advice-for-preparedness-and-prevention
5 Steps to Gov IT Modernization

2018 IT Modernization Summit
Mike Younkers, Sr. Director, U.S. Public Sector Systems Engineering, Cisco
Future Proofing Your Mission - Samuel Gordy

2018 IT Modernization Summit
Samuel Gordy, GM, Federal & Government Industries, IBM
Recommended
Manage Risk by Protecting the Apps and Data That Drive Business Productivity

Today you face the challenge of securing a business environment transformed by technologies such as cloud and new workforce requirements such as mobility, BYO and third-party talent.
The Growing U.S. IT Productivity Gap

Productivity growth has slowed down despite our rising investment in IT.
Secrets of getting Legacy to Cloud - setting the scene

Setting the scene for EuroCloud session with 5 different perspectives on the issues around moving Legacy applications to the Cloud. The digital landscape, digital transformational, Shadow IT, public vs private etc.
[Webinar Slides] Data Privacy for the IM Practitioner - Practical Advice for ...![[Webinar Slides] Data Privacy for the IM Practitioner - Practical Advice for ...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar Slides] Data Privacy for the IM Practitioner - Practical Advice for ...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Learn actionable steps to provide a high-level plan for implementing a privacy program in conjunction with your existing organizational RIM/IG program(s).
Want to follow along with the webinar replay? Download it here for FREE: https://info.aiim.org/data-privacy-for-the-im-practitioner-practical-advice-for-preparedness-and-prevention
5 Steps to Gov IT Modernization

2018 IT Modernization Summit
Mike Younkers, Sr. Director, U.S. Public Sector Systems Engineering, Cisco
Future Proofing Your Mission - Samuel Gordy

2018 IT Modernization Summit
Samuel Gordy, GM, Federal & Government Industries, IBM
Phil Abraham Speaker Sheet

Schedule to have Phil Abraham Speak At Your Next Event. Get The Inside Look On Healthcare and Cyber Security/
The changing face of HR

The changing face of HR: impact of new service delivery models, technology, mobile, social and cloud
Going Cloud Native in an Uncertain World

It’s always a good time to consider a move to cloud-native architecture—taking full advantage of the distributed, scalable, flexible nature of the public cloud to maximize your focus on writing code, creating business value and keeping customers happy. In a time of uncertainty there can be gains for developers and leaders alike.
Going cloud-native means simplifying work for engineers—obscuring many layers of infrastructure: networks, servers, operating systems etc. Employing Kubernetes opens up a whole new world for managing cloud infrastructure.
Join Micah Martin, Director of Engineering at Soul Cycle and Kendall Miller, President of Fairwinds as they discuss some real world examples of the benefits of deploying Cloud-Native technology in today’s uncertain environment:
Crisis as a Catalyst for Tackling Tech Debt
Managing More with Less
How to go from a Monolith to Containers to Kubernetes
Best Practices in a Time-Crunched Migration
Security (and Networking) in an Ephemeral World
Why the Cloud isn’t just another Datacenter
Aximark - Business Acceleration Services - Who we are & what we do 

Aximark is a network of independent multi-disciplinary experts. We work in the emerging Business Cloud Ecosystem, at the intersection of Technology and People (Customers, Employees, Partners, and other stakeholders). We use innovative strategies, methodologies and tools to AMPLIFY individuals and organizations. We help Brands and organizations 1-Regaining Control, 2-Building Trust, 3- Creating Value, 4- Monetizing Value.
[PDF] Principles of Information Systems![[PDF] Principles of Information Systems](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[PDF] Principles of Information Systems](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Develop an understanding of the core principles of IS and how it is practiced today with PRINCIPLES OF INFORMATION SYSTEMS, 13th edition. This edition combines the latest research with the most current coverage available as content highlights IS-related careers. You explore the challenges and risks of computer crimes, hacking, and cyberterrorism as well as the most current research on big data, analytics, and global IS and social networking.
Digital Transformation

Prosumer empowerment builds on the tenets of user engagement by embracing the free-market principles that are becoming a central feature of today’s IT orchestration frameworks. IT organizations are adopting a prosumer design-led digital applications in support of advanced user-centric mobility. IT architecture and information management in support of the rapid growth of global mobility and user lifestyle changes by millennials has just begun to emerge, with acceleration of change becoming a paradigm shift.
Sourcing Beyond Recruiting 2.0 (Sourcecon 2008)

"Sourcing Beyond Recruiting 2.0" examines the emerging trend that moves away from traditional desktop recruiting towards an integrated web-based approach known as the "digital webtop strategy."
Presentation delivered by Michael Marlatt at Sourcecon 2008 in Atlanta, Georgia.
[Webinar Slides] New Approaches to Classification and Retention for Organizat...![[Webinar Slides] New Approaches to Classification and Retention for Organizat...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar Slides] New Approaches to Classification and Retention for Organizat...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
In this webinar, we explore a new approach to managing your Organizational Intelligence that won’t disrupt user’s work habits.
Want to follow along with the webinar replay? Download it here for FREE: https://info.aiim.org/new-approaches-to-classification-and-retention-that-wont-disrupt-users-work-habits
Achieve cloud visibility, control and automation with IBM Hybrid Cloud Manage...

With hybrid cloud, you can add needed business applications and integrate and scale them as needed
Dcg first chair presentation 08.30.17

Earlier this week at the First Chair Awards Conference & Gala in Chicago I delivered a presentation about how all lawyers need to embrace transformation and change so they can better serve their clients. Attached are the slides that I delivered as part of my presentation.
Dcg ai legal lexis final final presentation 11.01.17

These are the slides that I used last week to deliver a LexisNexis webinar on "Artificial Intelligence (AI) & The Legal Profession".
The Perfect Storm: Service Oriented Government, Data Classification and AWS

Presented at the AWS Government, Education, and Nonprofits Symposium in Canberra, 6 May 2015.
This session will demonstrate how to reduce costs while expanding your opportunities for innovation on Amazon Web Services. It will consider a practical approach for data classification and security controls over objects and API endpoints which span an agency, its jurisdiction and the public. It will cover the foundations of Open Government from it's principles of transparency, participation and collaboration. It will touch on the economics of open data and the cost reducing effect of digital transactions being enabled right now throughout the public sector. Finally, we’ll look at real world examples from the Government Digital Service in the United Kingdom, the Victorian Government’s Information Asset Register and those expected from the Federal Government's Digital Transformation Office.
Innovation & Business Acquisitions of Smart Security

Presentation for Home Connect 2014 conference in Toronto on Nov 21, 2014
May 2013 Federal Cloud Computing Summit Welcome by Dr. David McClure

The Federal Cloud Computing Summit was held on May 30, 2013 in Washington, DC.
Not Using Cloud? 5 Stats Show You're Already Behind

Cloud computing has been there to add flexibility, scalability, efficiency, and cost benefits to the business processes.
If you are not the one embracing cloud technology, here are five stats that will show you the need to adopt it.
Digital Transformation and the Cloud - from Interxion and IDC 

We commissioned IDC to survey >750 European enterprises to understand how the rise of digital, as well as public cloud, are effecting IT infrastructure and networking.
2010 04-27 tech touchstone - the netherlands

A quite generic presentation used at an event in Noordwijk on virtualization.
Consumerization of IT: when productivity trumps control

Presented by Dan Elam, Contoural; and Steven Duque, Intuit Quickbase
Digital Transformation and the Role of IAM

We surveyed 200 IT decision makers across four countries
to learn where they are in their journey and the role that identity and access management (IAM) plays in the path to digital transformation.
More Related Content
What's hot
Phil Abraham Speaker Sheet

Schedule to have Phil Abraham Speak At Your Next Event. Get The Inside Look On Healthcare and Cyber Security/
The changing face of HR

The changing face of HR: impact of new service delivery models, technology, mobile, social and cloud
Going Cloud Native in an Uncertain World

It’s always a good time to consider a move to cloud-native architecture—taking full advantage of the distributed, scalable, flexible nature of the public cloud to maximize your focus on writing code, creating business value and keeping customers happy. In a time of uncertainty there can be gains for developers and leaders alike.
Going cloud-native means simplifying work for engineers—obscuring many layers of infrastructure: networks, servers, operating systems etc. Employing Kubernetes opens up a whole new world for managing cloud infrastructure.
Join Micah Martin, Director of Engineering at Soul Cycle and Kendall Miller, President of Fairwinds as they discuss some real world examples of the benefits of deploying Cloud-Native technology in today’s uncertain environment:
Crisis as a Catalyst for Tackling Tech Debt
Managing More with Less
How to go from a Monolith to Containers to Kubernetes
Best Practices in a Time-Crunched Migration
Security (and Networking) in an Ephemeral World
Why the Cloud isn’t just another Datacenter
Aximark - Business Acceleration Services - Who we are & what we do 

Aximark is a network of independent multi-disciplinary experts. We work in the emerging Business Cloud Ecosystem, at the intersection of Technology and People (Customers, Employees, Partners, and other stakeholders). We use innovative strategies, methodologies and tools to AMPLIFY individuals and organizations. We help Brands and organizations 1-Regaining Control, 2-Building Trust, 3- Creating Value, 4- Monetizing Value.
[PDF] Principles of Information Systems![[PDF] Principles of Information Systems](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[PDF] Principles of Information Systems](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Develop an understanding of the core principles of IS and how it is practiced today with PRINCIPLES OF INFORMATION SYSTEMS, 13th edition. This edition combines the latest research with the most current coverage available as content highlights IS-related careers. You explore the challenges and risks of computer crimes, hacking, and cyberterrorism as well as the most current research on big data, analytics, and global IS and social networking.
Digital Transformation

Prosumer empowerment builds on the tenets of user engagement by embracing the free-market principles that are becoming a central feature of today’s IT orchestration frameworks. IT organizations are adopting a prosumer design-led digital applications in support of advanced user-centric mobility. IT architecture and information management in support of the rapid growth of global mobility and user lifestyle changes by millennials has just begun to emerge, with acceleration of change becoming a paradigm shift.
Sourcing Beyond Recruiting 2.0 (Sourcecon 2008)

"Sourcing Beyond Recruiting 2.0" examines the emerging trend that moves away from traditional desktop recruiting towards an integrated web-based approach known as the "digital webtop strategy."
Presentation delivered by Michael Marlatt at Sourcecon 2008 in Atlanta, Georgia.
[Webinar Slides] New Approaches to Classification and Retention for Organizat...![[Webinar Slides] New Approaches to Classification and Retention for Organizat...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar Slides] New Approaches to Classification and Retention for Organizat...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
In this webinar, we explore a new approach to managing your Organizational Intelligence that won’t disrupt user’s work habits.
Want to follow along with the webinar replay? Download it here for FREE: https://info.aiim.org/new-approaches-to-classification-and-retention-that-wont-disrupt-users-work-habits
Achieve cloud visibility, control and automation with IBM Hybrid Cloud Manage...

With hybrid cloud, you can add needed business applications and integrate and scale them as needed
Dcg first chair presentation 08.30.17

Earlier this week at the First Chair Awards Conference & Gala in Chicago I delivered a presentation about how all lawyers need to embrace transformation and change so they can better serve their clients. Attached are the slides that I delivered as part of my presentation.
Dcg ai legal lexis final final presentation 11.01.17

These are the slides that I used last week to deliver a LexisNexis webinar on "Artificial Intelligence (AI) & The Legal Profession".
The Perfect Storm: Service Oriented Government, Data Classification and AWS

Presented at the AWS Government, Education, and Nonprofits Symposium in Canberra, 6 May 2015.
This session will demonstrate how to reduce costs while expanding your opportunities for innovation on Amazon Web Services. It will consider a practical approach for data classification and security controls over objects and API endpoints which span an agency, its jurisdiction and the public. It will cover the foundations of Open Government from it's principles of transparency, participation and collaboration. It will touch on the economics of open data and the cost reducing effect of digital transactions being enabled right now throughout the public sector. Finally, we’ll look at real world examples from the Government Digital Service in the United Kingdom, the Victorian Government’s Information Asset Register and those expected from the Federal Government's Digital Transformation Office.
Innovation & Business Acquisitions of Smart Security

Presentation for Home Connect 2014 conference in Toronto on Nov 21, 2014
May 2013 Federal Cloud Computing Summit Welcome by Dr. David McClure

The Federal Cloud Computing Summit was held on May 30, 2013 in Washington, DC.
Not Using Cloud? 5 Stats Show You're Already Behind

Cloud computing has been there to add flexibility, scalability, efficiency, and cost benefits to the business processes.
If you are not the one embracing cloud technology, here are five stats that will show you the need to adopt it.
Digital Transformation and the Cloud - from Interxion and IDC 

We commissioned IDC to survey >750 European enterprises to understand how the rise of digital, as well as public cloud, are effecting IT infrastructure and networking.
2010 04-27 tech touchstone - the netherlands

A quite generic presentation used at an event in Noordwijk on virtualization.
What's hot (20)
Aximark - Business Acceleration Services - Who we are & what we do 

Aximark - Business Acceleration Services - Who we are & what we do
[Webinar Slides] New Approaches to Classification and Retention for Organizat...![[Webinar Slides] New Approaches to Classification and Retention for Organizat...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar Slides] New Approaches to Classification and Retention for Organizat...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Webinar Slides] New Approaches to Classification and Retention for Organizat...
Achieve cloud visibility, control and automation with IBM Hybrid Cloud Manage...

Achieve cloud visibility, control and automation with IBM Hybrid Cloud Manage...
Dcg ai legal lexis final final presentation 11.01.17

Dcg ai legal lexis final final presentation 11.01.17
The Perfect Storm: Service Oriented Government, Data Classification and AWS

The Perfect Storm: Service Oriented Government, Data Classification and AWS
Innovation & Business Acquisitions of Smart Security

Innovation & Business Acquisitions of Smart Security
May 2013 Federal Cloud Computing Summit Welcome by Dr. David McClure

May 2013 Federal Cloud Computing Summit Welcome by Dr. David McClure
Not Using Cloud? 5 Stats Show You're Already Behind

Not Using Cloud? 5 Stats Show You're Already Behind
Digital Transformation and the Cloud - from Interxion and IDC 

Digital Transformation and the Cloud - from Interxion and IDC
Similar to SURVEY RESULTS: ACCELERATING INNOVATION AND THE DIGITAL JOURNEY - INFOGRAPHIC
Consumerization of IT: when productivity trumps control

Presented by Dan Elam, Contoural; and Steven Duque, Intuit Quickbase
Digital Transformation and the Role of IAM

We surveyed 200 IT decision makers across four countries
to learn where they are in their journey and the role that identity and access management (IAM) plays in the path to digital transformation.
Cloud can be essential element of digital transform – Cuneiform

Digital transformation is the process of reorienting an organization to focus on value creation through the widespread and persistent application of digital technologies.
The 10 best performing cloud solution providers 2018

Insights Success has come up with a list of “The 10 Best Performing Cloud Solution Providers, 2018/19.”
Secure Digital Transformation- Cybersecurity Skills for a Safe Journey to Dev...

CyCon 3.0 presentation- February 15, 2020
Successful digital transformations don’t begin with technology, they begin with people. As organizations adopt DevOps and cloud and realize the increased release velocity, ensuring the security of software and systems at the same velocity is a necessity but doing so isn’t easy. In this talk you will learn about common security challenges in DevOps and cloud and the skills cybersecurity professionals need to solve these challenges.
Major Cloud Security Challenges concerning the Enterprises | Sysfore

With the increasing breach of sensitive data held in Cloud, many enterprises, medium and large, are now worried about Cloud Security. In this article, we will discuss some of the major Cloud Security Challenges facing the enterprises and whether they can be overcome.
Canon Infographic on workplace evolution 

digital transformation from prehistoric to paperless and beyond
Is Your Network Ready for Digital Transformation?

Is Your Network Ready for Digital Transformation? Learn from the best Network Training Institute in Chennai at http://www.rjpinfotek.com
The Secure Path to Value in the Cloud by Denny Heaberlin

Even as cloud and managed services grow increasingly central to business strategy and performance, challenges remain. The biggest sticking point for companies seeking to capitalize on the cloud is data security. Keeping data safe is an issue in any computing environment, and it has been a focus since the earliest days of the cloud revolution. Understandably so: a lot can go wrong when you allow valuable information to live outside the firewall. Recent revelations about government snooping, along with a steady stream of well-publicized data breaches, only add to the uncertainty.
In his session at 16th Cloud Expo, Denny Heaberlin, Security Product Manager with Windstream's Cloud and Data Center Marketing team, discussed how to manage these concerns and how choose the right cloud vendor, an essential part of any cloud strategy.
The benefits of cloud technology for remote working

The future of work is not about where you are, but about how
quickly you can move. While most organisations are “keeping
the lights on” by supporting remote work, market leaders are
capitalising by reforming their entire approach.
As remote working has become the “new normal”, businesses
have replaced informal discussions with online messaging,
augmented data centres with the cloud, and secured their
data from outages and cyber attacks with SaaS solutions.
The benefits of cloud technology for remote working

The future of work is not about where you are, but about how
quickly you can move. While most organisations are “keeping
the lights on” by supporting remote work, market leaders are
capitalising by reforming their entire approach.
The Role of Software in Modernizing Information Technology Infrastructure.pdf

The role of software has become paramount in driving and sustaining innovation.
Read this Article here: https://medium.com/@ciente/the-role-of-software-in-modernizing-information-technology-infrastructure-2fae62f1f192
Get some more insightful articles here: https://ciente.io/blog/
Explore more: https://ciente.io/
Digital Transformation.pdf

Digital transformation is the cultural, organizational, and operational change of an establishment, industry, or
ecosystem through a smart integration of digital technologies, processes and competencies across all levels
and functions in a staged and strategic way.
EMEA10: Trepidation in Moving to the Cloud

Today’s buzz centres on cloud computing. What is it exactly? Will it dent your revenues or does it have potential to add capabilities to your business? How do you deliver value when you don’t “install” anything? Learn how to use this new approach to delivering IT services in your business, what to consider and where it makes sense – and where it doesn’t! Dave Sobel, CEO of Evolve Technologies, talks to you about how to develop cloud offerings and how you position your business for growth around online services. Strategies come from real life experience, industry data, and collaboration with other solution providers to give you the best way to take on the big, bad cloud.
Public cloud 101,One individual does not hold all the keys to the kingdom. Co...

Public cloud 101,One individual does not hold all the keys to the kingdom. Multi-tenancy with Cloud Security.
India's Leading Cyber Security Companies to Watch.pdf

This edition features a handful of the India's Leading Cyber Security Companies to Watch that are leading us into a better future
Read More: https://www.insightssuccess.in/indias-leading-cyber-security-companies-to-watch-june2023/
The state of it complexity in singapore whitepaper final

Ever increasing complexity is holding back digital transformation efforts and restricting cloud adoption. Reducing complexity and increasing security is high on the agenda for CIOs and businesses in Singapore.
Why Cloud needs to be seen beyond it's cost advantages. 

Organisations fear the loss of control over their data when migrating to cloud. The biggest challenge encountered when moving the database from traditional servers to cloud is to prevent unauthorised access to sensitive data. Cloud not only enhances data security but acts as a tool to save space,
time, power and money.
Similar to SURVEY RESULTS: ACCELERATING INNOVATION AND THE DIGITAL JOURNEY - INFOGRAPHIC (20)
Consumerization of IT: when productivity trumps control

Consumerization of IT: when productivity trumps control
Cloud can be essential element of digital transform – Cuneiform

Cloud can be essential element of digital transform – Cuneiform
The 10 best performing cloud solution providers 2018

The 10 best performing cloud solution providers 2018
Secure Digital Transformation- Cybersecurity Skills for a Safe Journey to Dev...

Secure Digital Transformation- Cybersecurity Skills for a Safe Journey to Dev...
Major Cloud Security Challenges concerning the Enterprises | Sysfore

Major Cloud Security Challenges concerning the Enterprises | Sysfore
The Secure Path to Value in the Cloud by Denny Heaberlin

The Secure Path to Value in the Cloud by Denny Heaberlin
The benefits of cloud technology for remote working

The benefits of cloud technology for remote working
The benefits of cloud technology for remote working

The benefits of cloud technology for remote working
The Role of Software in Modernizing Information Technology Infrastructure.pdf

The Role of Software in Modernizing Information Technology Infrastructure.pdf
Public cloud 101,One individual does not hold all the keys to the kingdom. Co...

Public cloud 101,One individual does not hold all the keys to the kingdom. Co...
India's Leading Cyber Security Companies to Watch.pdf

India's Leading Cyber Security Companies to Watch.pdf
The state of it complexity in singapore whitepaper final

The state of it complexity in singapore whitepaper final
Why Cloud needs to be seen beyond it's cost advantages. 

Why Cloud needs to be seen beyond it's cost advantages.
More from Unisys Corporation
Elevate™ by Unisys

Elevate™ by Unisys is a holistic integrated omnichannel digital banking software framework that enables continuous, seamless customer journeys regardless of touchpoint, anytime, anywhere - mobile banking, internet, branch, or contact center.
Unisys Integrated Medical Device Management - Executive Brief

Effective management of medical devices is critical. Unisys IMDM enables you to:
Monitor the performance of medical
devices from a common point of
contact
Simplify recalls and maintenance
Proactively manage medical devices
Maintain a compliance continuum
Counter the threat of cyberattacks
Privacy and Security by Design

Privacy and Security by Design Spotlight Presentation at HIMMS Privacy and Security Forum, December 5th 2016. Presented by Jeff R. Livingstone, PhD, Vice President and Global Lead, Life Sciences & Healthcare, Unisys Corporation.
Unisys Client 360

IMPROVING OUR CLIENTS' EXPERIENCE & ENHANCING EMPLOYEE EMPOWERMENT THROUGH UNISYS ADVANCED DATA ANALYTICS
Stealth Secures Along Every Step of Your Journey Infographic

Learn how Stealth secures your networks, predicts with confidence, reduces attack surfaces, and defends your most valuable data within a variety of key industries and along every step of your transient journey.
DIE NEUE DIGITALE INFRASTRUKTUR FÜR DIGITALE MITARBEITER DER NÄCHSTEN GENERAT...

DIE NEUE DIGITALE INFRASTRUKTUR FÜR DIGITALE MITARBEITER DER NÄCHSTEN GENERATION.
STEHEN DIE ENDBENUTZER DER GENERATION „DIGITAL“FÜR DAS ENDE VON IT-TRANSPAREN...

STEHEN DIE ENDBENUTZER DER GENERATION „DIGITAL“FÜR DAS ENDE VON IT-TRANSPARENZ UND IT-KONTROLLE.
DIE GENERATION DIGITAL UND DIE IT-LÜCKE IN UNTERNEHMEN.

DIE GENERATION DIGITAL UND DIE IT-LÜCKE IN UNTERNEHMEN.
Digital Gen: Hybrid IT Infographic 

Find out how you can build a digital infrastructure that includes cloud, data center management and service management. And give the digital generation the services, access, apps and support they need to work anytime, anywhere, across any device.
Digital Gen: Security Infographic

The Generation-D Dilemma — How Tech-Savvy Workers Are Affecting Enterprise Security.
Digital Gen: End User Services Infographic

Will the digital generation of end users be the end of IT visibility and control?
Unisys Stealth(cloud)™ for Azure Infographic

Learn how Unisys' Stealth(cloud)™ Extended Data Center for Azure differentiates itself by enabling you to confidently extend your data center grade security to the Azure cloud, securing applications that span public cloud and on-premise environments.
Managed Security Services Infographic

Learn what's driving and how to combat cybercrime with Unisys' Managed Security Services, delivering best of breed security offerings with trusted efficiency.
Unisys Stealth Industries Infographic

Learn the diverse, distinctive, and essential benefits of using Unisys Stealth security solutions to protect data, promote compliance, conceal endpoints and lower overall costs within nine different industries.
More from Unisys Corporation (20)
Unisys Integrated Medical Device Management - Executive Brief

Unisys Integrated Medical Device Management - Executive Brief
Stealth Secures Along Every Step of Your Journey Infographic

Stealth Secures Along Every Step of Your Journey Infographic
DIE NEUE DIGITALE INFRASTRUKTUR FÜR DIGITALE MITARBEITER DER NÄCHSTEN GENERAT...

DIE NEUE DIGITALE INFRASTRUKTUR FÜR DIGITALE MITARBEITER DER NÄCHSTEN GENERAT...
STEHEN DIE ENDBENUTZER DER GENERATION „DIGITAL“FÜR DAS ENDE VON IT-TRANSPAREN...

STEHEN DIE ENDBENUTZER DER GENERATION „DIGITAL“FÜR DAS ENDE VON IT-TRANSPAREN...
DIE GENERATION DIGITAL UND DIE IT-LÜCKE IN UNTERNEHMEN.

DIE GENERATION DIGITAL UND DIE IT-LÜCKE IN UNTERNEHMEN.
Recently uploaded
UiPath Test Automation using UiPath Test Suite series, part 5

Welcome to UiPath Test Automation using UiPath Test Suite series part 5. In this session, we will cover CI/CD with devops.
Topics covered:
CI/CD with in UiPath
End-to-end overview of CI/CD pipeline with Azure devops
Speaker:
Lyndsey Byblow, Test Suite Sales Engineer @ UiPath, Inc.
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

Building better applications for business users with SAP Fiori.
• What is SAP Fiori and why it matters to you
• How a better user experience drives measurable business benefits
• How to get started with SAP Fiori today
• How SAP Fiori elements accelerates application development
• How SAP Build Code includes SAP Fiori tools and other generative artificial intelligence capabilities
• How SAP Fiori paves the way for using AI in SAP apps
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

The choice of an operating system plays a pivotal role in shaping our computing experience. For decades, Microsoft's Windows has dominated the market, offering a familiar and widely adopted platform for personal and professional use. However, as technological advancements continue to push the boundaries of innovation, alternative operating systems have emerged, challenging the status quo and offering users a fresh perspective on computing.
One such alternative that has garnered significant attention and acclaim is Nitrux Linux 3.5.0, a sleek, powerful, and user-friendly Linux distribution that promises to redefine the way we interact with our devices. With its focus on performance, security, and customization, Nitrux Linux presents a compelling case for those seeking to break free from the constraints of proprietary software and embrace the freedom and flexibility of open-source computing.
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
Essentials of Automations: The Art of Triggers and Actions in FME

In this second installment of our Essentials of Automations webinar series, we’ll explore the landscape of triggers and actions, guiding you through the nuances of authoring and adapting workspaces for seamless automations. Gain an understanding of the full spectrum of triggers and actions available in FME, empowering you to enhance your workspaces for efficient automation.
We’ll kick things off by showcasing the most commonly used event-based triggers, introducing you to various automation workflows like manual triggers, schedules, directory watchers, and more. Plus, see how these elements play out in real scenarios.
Whether you’re tweaking your current setup or building from the ground up, this session will arm you with the tools and insights needed to transform your FME usage into a powerhouse of productivity. Join us to discover effective strategies that simplify complex processes, enhancing your productivity and transforming your data management practices with FME. Let’s turn complexity into clarity and make your workspaces work wonders!
Uni Systems Copilot event_05062024_C.Vlachos.pdf

Unlocking Productivity: Leveraging the Potential of Copilot in Microsoft 365, a presentation by Christoforos Vlachos, Senior Solutions Manager – Modern Workplace, Uni Systems
Pushing the limits of ePRTC: 100ns holdover for 100 days

At WSTS 2024, Alon Stern explored the topic of parametric holdover and explained how recent research findings can be implemented in real-world PNT networks to achieve 100 nanoseconds of accuracy for up to 100 days.
GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...

Leonard Jayamohan, Partner & Generative AI Lead, Deloitte
This keynote will reveal how Deloitte leverages Neo4j’s graph power for groundbreaking digital twin solutions, achieving a staggering 100x performance boost. Discover the essential role knowledge graphs play in successful generative AI implementations. Plus, get an exclusive look at an innovative Neo4j + Generative AI solution Deloitte is developing in-house.
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

Dr. Sean Tan, Head of Data Science, Changi Airport Group
Discover how Changi Airport Group (CAG) leverages graph technologies and generative AI to revolutionize their search capabilities. This session delves into the unique search needs of CAG’s diverse passengers and customers, showcasing how graph data structures enhance the accuracy and relevance of AI-generated search results, mitigating the risk of “hallucinations” and improving the overall customer journey.
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Join Maher Hanafi, VP of Engineering at Betterworks, in this new session where he'll share a practical framework to transform Gen AI prototypes into impactful products! He'll delve into the complexities of data collection and management, model selection and optimization, and ensuring security, scalability, and responsible use.
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

Neha Bajwa, Vice President of Product Marketing, Neo4j
Join us as we explore breakthrough innovations enabled by interconnected data and AI. Discover firsthand how organizations use relationships in data to uncover contextual insights and solve our most pressing challenges – from optimizing supply chains, detecting fraud, and improving customer experiences to accelerating drug discoveries.
Recently uploaded (20)
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
UiPath Test Automation using UiPath Test Suite series, part 5

UiPath Test Automation using UiPath Test Suite series, part 5
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...
Communications Mining Series - Zero to Hero - Session 1

Communications Mining Series - Zero to Hero - Session 1
Essentials of Automations: The Art of Triggers and Actions in FME

Essentials of Automations: The Art of Triggers and Actions in FME
Pushing the limits of ePRTC: 100ns holdover for 100 days

Pushing the limits of ePRTC: 100ns holdover for 100 days
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...

GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...
Climate Impact of Software Testing at Nordic Testing Days

Climate Impact of Software Testing at Nordic Testing Days
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Generative AI Deep Dive: Advancing from Proof of Concept to Production
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024
SURVEY RESULTS: ACCELERATING INNOVATION AND THE DIGITAL JOURNEY - INFOGRAPHIC
- 1. ACCELERATING INNOVATIONANDTHE DIGITAL JOURNEY We surveyed IT leaders to learn how organizations are transforming to a digital business. Cloud is directly linked to digital transformation. While security is key to successful cloud, IT leaders are also prioritizing initiatives to help improve IT skill sets, increase the level of visibility into the IT environment, automate IT service delivery, and create infrastructure scalability. For more information on accelerating your digital journey with cloud as a catalyst, go to unisyscloud.com THE DIGITAL MANDATE say it’s key to improve IT to support a digital business model. Less than one in fivewould consider their IT organization “extremely nimble”. Cloud= flexibility: Ability to integrate, automate cloud workloads equals flexibility. ATTUNEDTO CHALLENGES SECURITY IS CRITICALTO PROGRESS CLOUD ACCELERATES DIGITALTRANSFORMATION MANAGING AND INTEGRATING CLOUD PLATFORMS: ATOUGH JOB What’s keeping organizations from going digital? 49% 45% 41% 39% Security threats Managing complexity Cost pressure Demand for 24x7 availability Prioritize data security in the cloud to improve competitiveness in the digital world. 52% Integrating and automating cloud workloads across multiple platforms is crucial. Majority of apps already deployed in the cloud today: BUT CLOUD PAYS OFF! 15% 16% 24% 55% Hybrid cloud Total cloud Public cloud Private cloud need to integrate and automate cloud workloads across multiple platforms. Average number of cloud platforms per organization: 11 Organization has a good to excellent ability to integrate: 34% The benefits of cloud apps include improving... Data security User experience IT efficiency Infrastructure performance End user productivity 56% 44% 43% 41% 41% 88% 32% say enhancing overall security is a critical priority but... Only 32% report significant progress The gap 56%
