Sumo Logic IT Operations Solutions Brief
•
0 likes•236 views
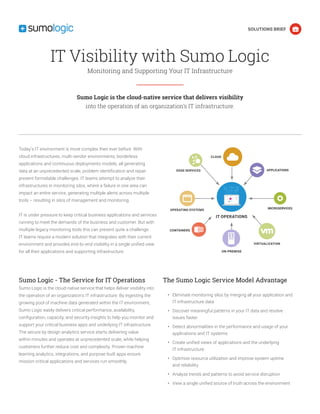
Sumo Logic is a cloud-native service that provides end-to-end visibility into IT infrastructures and applications through a single unified view. It ingests machine data from across the IT environment to deliver insights into performance, availability, configurations, capacity, and security. Sumo Logic helps eliminate monitoring silos, discover issues faster, and optimize resource utilization to improve system uptime and reliability.
Report
Share
Report
Share
Download to read offline
Recommended
Securing Sensitive Data in Your Hybrid Cloud

RightScale Webinar: Do you want both the control and customization of a private cloud and the cost savings of a public cloud? Then a hybrid cloud might be the best solution for your business. But to safely receive these benefits, you’ll need to secure your sensitive data across both your private and public cloud.
Hear about the challenges faced by cloud customers as they deploy applications and data in hybrid clouds. Join Dave Asprey, VP of Cloud Security at Trend Micro, and Phil Cox, Director of Security and Compliance at RightScale, to learn about common pitfalls, inherent risks, and security best practices to protect sensitive information in cross-cloud environments.
With effective and flexible cloud security, you can embrace the economic and technical efficiencies of hybrid clouds, improving your business and saving costs.
Reducing Cost and Complexity with Industrial System Consolidation

In today’s highly competitive manufacturing environment, success requires a constant focus on cost cutting while maintaining production throughput and employee safety. For manufacturers, this includes finding new ways to lower operating expenses, a large part of which are the purchase and support of industrial systems. A significant cost stems from the inefficiencies created by the growing numbers and varieties of systems on the factory floor.
This white paper describes how virtualization technology running on multi-core Intel Core vPro processors can be used in industrial automation to consolidate computing devices for motion control, programmable logic control (PLC), human machine interface (HMI), machine vision, data acquisition, functional safety and so forth. This approach can help manufacturers reduce cost and complexity on the factory floor.
Taming Multi-Cloud, Hybrid Cloud, Docker, and Kubernetes

5 Best Practices to Optimize Log Management for DevOps, SREs, and IT Operations
Machines are Talking. Are You Listening?

We are nearing the dawn of a very interesting age. From robotics, to smart homes, to web-connected lightbulbs, HVAC units, servers and routers—machines are in use everywhere. These machines have a lot to say, but what happens when you start listening? What things come to light and what new discoveries can you make? What questions can you now ask of your world? This session will explore the vast use cases where we have asked: Can I get data from that thing? If I can, what can it tell me? What happens if I Splunk it?
HIGH-IMPACT USE CASES POWERED BY NEXT-GENERATION NETWORK ANALYTICS

The advent of hybrid clouds, multi clouds and app driven business models hasnecessitated a network that has to be robust, secure and scalable to meet rapidly changing business expectations.
Symantec Enterprise Mobility Vision May 2012

Symantec’s recent enterprise mobile enhancements help organizations leverage mobility to improve operational efficiencies and better meet the challenges of the “Bring Your Own Device” trend.
Norton Zone File-Sharing Service

Norton Zone lets you deploy a safe and easy file-sharing service with the security expertise, visibility, and administrative controls you can only get from Symantec. With patented key encryption, Active Directory for SSO, automated two-factor authentication, and more, your employees can share files any time from any device—smartphone, computer or tablet.
Recommended
Securing Sensitive Data in Your Hybrid Cloud

RightScale Webinar: Do you want both the control and customization of a private cloud and the cost savings of a public cloud? Then a hybrid cloud might be the best solution for your business. But to safely receive these benefits, you’ll need to secure your sensitive data across both your private and public cloud.
Hear about the challenges faced by cloud customers as they deploy applications and data in hybrid clouds. Join Dave Asprey, VP of Cloud Security at Trend Micro, and Phil Cox, Director of Security and Compliance at RightScale, to learn about common pitfalls, inherent risks, and security best practices to protect sensitive information in cross-cloud environments.
With effective and flexible cloud security, you can embrace the economic and technical efficiencies of hybrid clouds, improving your business and saving costs.
Reducing Cost and Complexity with Industrial System Consolidation

In today’s highly competitive manufacturing environment, success requires a constant focus on cost cutting while maintaining production throughput and employee safety. For manufacturers, this includes finding new ways to lower operating expenses, a large part of which are the purchase and support of industrial systems. A significant cost stems from the inefficiencies created by the growing numbers and varieties of systems on the factory floor.
This white paper describes how virtualization technology running on multi-core Intel Core vPro processors can be used in industrial automation to consolidate computing devices for motion control, programmable logic control (PLC), human machine interface (HMI), machine vision, data acquisition, functional safety and so forth. This approach can help manufacturers reduce cost and complexity on the factory floor.
Taming Multi-Cloud, Hybrid Cloud, Docker, and Kubernetes

5 Best Practices to Optimize Log Management for DevOps, SREs, and IT Operations
Machines are Talking. Are You Listening?

We are nearing the dawn of a very interesting age. From robotics, to smart homes, to web-connected lightbulbs, HVAC units, servers and routers—machines are in use everywhere. These machines have a lot to say, but what happens when you start listening? What things come to light and what new discoveries can you make? What questions can you now ask of your world? This session will explore the vast use cases where we have asked: Can I get data from that thing? If I can, what can it tell me? What happens if I Splunk it?
HIGH-IMPACT USE CASES POWERED BY NEXT-GENERATION NETWORK ANALYTICS

The advent of hybrid clouds, multi clouds and app driven business models hasnecessitated a network that has to be robust, secure and scalable to meet rapidly changing business expectations.
Symantec Enterprise Mobility Vision May 2012

Symantec’s recent enterprise mobile enhancements help organizations leverage mobility to improve operational efficiencies and better meet the challenges of the “Bring Your Own Device” trend.
Norton Zone File-Sharing Service

Norton Zone lets you deploy a safe and easy file-sharing service with the security expertise, visibility, and administrative controls you can only get from Symantec. With patented key encryption, Active Directory for SSO, automated two-factor authentication, and more, your employees can share files any time from any device—smartphone, computer or tablet.
Government Webinar: Low-Cost Log, Network Configuration, and IT Monitoring So...

In this webinar, our SolarWinds sales engineer discussed the basic network management tools you need to operate and troubleshoot your network and help improve security. He also reviewed the key factors to consider, where to start, and provided details on some of the tools our government customers need today.
During this interactive webinar, attendees learned how:
SolarWinds® ipMonitor® provides visibility into availability and performance of your network, servers, and applications
Kiwi Syslog® Server centralizes and simplifies log message management across network devices and servers
Kiwi CatTools® provides powerful network automation and configuration management
Webinar: Real IT Compliance with SolarWinds

In this webinar, attendees learned how to leverage automation to improve responsiveness to IT threats and help their organization comply with cyber security regulations, mandates, and policies. Attendees learned about SolarWinds products that can provide automated responses and how they can be leveraged to help reduce reaction times and improve their organization’s security posture.
SolarWinds Government and Education sales engineers reviewed and demonstrated automation features of Network Configuration Manager (NCM), Security Event Manager (SEM), formerly Log & Event Manager, NetFlow Traffic Analyzer (NTA), and Log Analyzer (LA), and how they can be used to help improve governmental and organizational compliance. They also reviewed how our API can be used to integrate with other applications to support organizational objectives.
During this interactive webinar, attendees learned about:
• How NCM detects out-of-process configuration changes, audits configurations, and even corrects violations
• How SEM provides cross-platform event processing, notification, and remediation
• How to configure SEM rules and active responses to meet your organization’s security objectives
• How NTA supports port 0 monitoring and how it can alert on flow traffic thresholds per protocol
• How LA provides real-time log streaming and visualization to help identify the root cause and reduce troubleshooting
• How to push and pull data leveraging the Orion® Platform API and utilize the OrionSDK and SWQL to sync between external applications and tools
Government and Education Webinar: Technical Update and Demo of New Features

In this webinar, our SolarWinds sales engineer discussed new SolarWinds® products and features that are of interest to our federal, state, local, and education customers. Our sales engineer discussed and demonstrated the 2019.4 releases, consisting of Access Rights Manager, Security Event Manager, and the Orion® Platform enhancements, including Server & Application Monitor, Virtualization Manager, Server Configuration Monitor, Network Performance Monitor, Enterprise Operations Console, and more.
During this interactive webinar, attendees learned about:
Access Rights Manager
Updated dashboard
Create users and mailboxes in Office365®
Security Event Manager (formerly Log & Event Manager)
UI updates
Customizable email templates
Orion Platform enhancements
Azure® VM and SQL Database Managed Instance support
Orion Map enhancements
GER and JPN localization
Native SolarWinds Service Desk integration
Orion Product Enhancements
Server & Application Monitor- improved API support; Nutanix hardware health
Virtualization Manager – Nutanix hardware health
Server Configuration Monitor – Linux® server and application support
Network Performance Monitor – Device Views (technical preview)
NetFlow Traffic Analyzer – Cisco® Meraki® flow support
Database Performance Analyzer – Updated DB support, table tuning best practices, updated alerts and API
VoIP & Network Quality Manager – updated VoIP system support
Enterprise Operations Console – Improved workflow and authentication
Log Analyzer – Orion Log Viewer replaces legacy Syslog and Traps
Storage Resource Monitor – EMC CLARiiON controller and Data Domain support
Other product enhancements
Web Performance Monitor
Network Configuration Manager
User Device Tracker
IP Address Manager
Microsoft Intune - Empowering Enterprise Mobility - Presented by Atidan 

Simplify management of apps & devices
Microsoft Intune provides mobile device management, mobile application management, and PC management capabilities from the cloud. Using Intune, organizations can provide their employees with access to corporate applications, data, and resources from virtually anywhere on almost any device, while helping to keep corporate information secure.
Federal Webinar: Technical Update and Demo of New Features

In this webinar our Federal Sales Engineering team discussed and demonstrated Q4 2018 releases, including Network Performance Monitor (NPM) 12.4, NetFlow Traffic Analyzer (NTA) 4.5, Network Configuration Manager (NCM) 7.9, IP Address Manager (IPAM) 4.8, Orion® Platform 2018.4, and Dameware® 12.1. They provided a sneak peek of Log & Event Manager (LEM) 6.6 and reviewed our newest product, Access Rights Manager (ARM).
During this interactive webinar, attendees learned about:
Network Performance Monitor 12.4
Cisco® Application Centric Infrastructure (ACI) (software-defined networking) support
NetFlow Traffic Analyzer 4.5
Alert on flow
Network Configuration Manager 7.9
Multi-device baselines
New: Access Rights Manager
Monitoring of Active Directory® and Microsoft® Exchange™
Auditing of Windows® File Share
User provisioning, management, and permissions analysis
Custom report generation
Self-service permissions portal
IP Address Manager 4.8
Infoblox® support
Orion Platform 2018.4
SAML authentication
Centralized upgrades
Device guard support for Microsoft Windows®
Dameware 12.1
TLS 1.2 compliant
New Mirror Driver
Sneak Peek
Log & Event Manager 6.6
Continue HTML migration
Intel Gateway Solutions for the Internet of Things

Intel Gateway Solutions for the Internet of Things (IoT) is a family of platforms that enables companies to seamlessly interconnect industrial infrastructure devices and secure data flow between devices and the cloud. Intel Gateway Solutions for IoT enables customers to securely aggregate, share,and filter data for analysis.
Modern Workplace Summit 2015 - Management

My slide deck from the MWS summit. Device security and management with tools like EMS, Intune, Azure Active Directory and Office 365
http://mwssummit.com/agenda/windows-10-summit-agenda/
Empower Enterprise Mobility- Maximize Mobile Control- Presented by Atidan

Identity + Mobile Management + Security
Keep your employees productive on their favorite apps and devices—and your company data protected with enterprise mobility solutions from Microsoft.
Windows 10 is better with EMS
Windows 10 is the best Windows ever and provides a foundation for protection against modern threats and continuous management while enabling your users to be more productive. To get the most out of your mobile security and productivity strategy, integrate the Microsoft Enterprise Mobility Suite (EMS) with Windows 10 for greater protection of users, devices, apps, and data.
Our enterprise-grade security
A key concern for you continues to be security, and rightly so. Identity is the control plane at the center of our solution helping you to be more secure. Only Microsoft offers cloud identity and access management solutions running at Internet scale and designed to help secure your IT environment. Microsoft Azure Active Directory has hundreds of millions of users, is available in 35 datacenters around the world, and has processed more than 1 trillion (yes, trillion) authentications. Our innovative new technology, Microsoft Advanced Threat Analytics is designed to help you identify advanced persistent threats in your organization before they cause damage.
We’re more integrated and flexible
Architecture matters. That’s why our solutions run in the cloud and work seamlessly with your on-premises investments—taking the worry out of scale, maintenance, and updates.
Our cloud-first approach provides an integrated set of solutions that are designed to work together from the ground up, avoiding the need for costly and complicated integration efforts across point capabilities. It’s the fastest and most cost-effective way to meet new business challenges and accommodate new devices, new apps, and new hires.
Nobody manages Office better
Protecting email and other corporate data on mobile devices—without bogging down workers—is one of today’s biggest IT challenges. Other vendors solve it with apps that compromise user experience and put the brakes on productivity.
Microsoft enterprise mobility solutions integrate deeply with Microsoft Office, the gold standard of productivity. We’re the only solution that brings managed mobile productivity with Microsoft Office across devices.
Accelerating Operational Excellence with IT/OT Convergence

EMEA Partner Summit 2015
Presented by Pierre Paterni, Business Development Lead - Rockwell Automation
Government Webinar: Improving Security Compliance with IT Monitoring Tools 

In this webinar SolarWinds and DH Technologies discussed how SolarWinds infrastructure monitoring tools can be used to help improve your agency’s IT security posture. We discussed how our solutions help manage and monitor network devices and their configurations to enhance risk management, IT security, and compliance. Discussions included simplifying day-to-day operations, increasing automation, and generating reports to help verify compliance and highlight violations.
During this interactive webinar, attendees learned about:
Leverage Network Configuration Manager (NCM) and Security Event Manager (SEM) (formerly Log & Event Manager) to verify that controls have been implemented correctly
Employ SEM, Network Performance Monitor, and NCM to monitor that controls are working as expected
Quickly and easily produce out-of-the-box compliance reports for DISA STIGS, FISMA, and more
Leverage Server Configuration Monitor (SCM) to track and get alerted when server configurations change
Government and Education Webinar: Conquering Remote Work IT Challenges 

In this webinar, we discussed how SolarWinds® solutions can help you overcome remote work IT challenges.
During this interactive webinar, attendees learned about:
Improve network monitoring, configuration, and VPN management with SolarWinds Network Performance Monitor (NPM) and SolarWinds Network Configuration Manager (NCM)
Monitor the server and application performance of your collaboration systems with SolarWinds Server & Application Monitor (SAM)
Utilize configuration management to efficiently deploy upgrades and improve compliance with NCM
Support users and systems remotely with tools such as SolarWinds Dameware® Remote Support (DRS) and SolarWinds Dameware Remote Everywhere (DRE)
Improve IT request management, ticket tracking, and asset management with tools like SolarWinds Web Help Desk® and SolarWinds Service Desk
Automate provisioning and permissions management with SolarWinds Access Rights Manager™ (ARM)
Locate users and devices on your network with SolarWinds User Device Tracker (UDT)
TechWiseTV Workshop: Q&A OpenDNS and AnyConnect 

This is the Q&A we captured from the live event for your reference.
Motadata brochure

Mindarray Systems has been an innovator in Network Monitoring and Data Analytics Technologies. Our first product, Minder, was the only IT monitoring platform that offered a truly unified view and correlation across all layers of IT infrastructure from a single product.
Motadata today, is strongly positioned to enable Telco’s, Enterprise and Government sectors to streamline their IT operations with next-gen product suite which is pre-integrated yet modular, consisting of
1) Infrastructure Intelligence Platform (IIP) for Network Management
2) Data Analytics Platform (DAP) for Log Management & Flow Analytics and
3) ITSM Platform for IT Service Automation.
Motadata is a unified IT Infrastructure Monitoring, Log & Flow Management, and IT Service Management Platform, offering operational insights into your IT infrastructure and its performance and is designed to identify & resolve complex problems faster that ensures 100% uptime of all business-critical components. Motadata enables you to make more informed business decisions by offering complete visibility into the health and key performance indicators (KPIs) of IT services. It helps in reducing CAPEX, offers Agility to resolve issues faster, is compatible in a hybrid ecosystem, and offers ease of integration with existing and future platforms.
In summary, with Motadata, Mindarray Systems offers the perfect solution needed to confidently handle the challenges of today’s increasingly complex business operations and IT infrastructure management.
UDT - Government and Healthcare

Studies have found that organized crime is increasingly targeting health care entities because health records are worth more and easier to obtain. UDT offers a complete spectrum of technical, professional and managed services to protect your organization’s ePHI and comply with regulations.
Get Ahead of Cyber Attacks with Microsoft Enterprise Mobility + Security

Digital transformation with freedom and peace of mind
Holistic, identity-driven protection
Help guard your data from attacks on multiple levels using innovative, identity-driven security techniques.
Productivity without compromise
Preserve the mobile and desktop experiences your workers need to stay working with familiar apps and tools.
Flexible, comprehensive solutions
Do more with less—protect users, devices, apps, and data with intuitive mobile management on a future-ready platform.
microsoft@atidan.com
RoltaiPerspective enterprise suite for SOA-based Enterprise Integration

RoltaiPerspective Enterprise Suite is an IT solution which gives flexibility by accomplishing the specific needs of an enterprise and helps organization accomplish fast ROI through asset consolidation and agile business processes. RoltaiPerspective empowers organizations to bridge the gap between old applications and next gen applications thus encouraging an environment of/for change and upgrade.
Introduction to Symantec Endpoint Management75.pptx

How does Symantec solve your common IT challenges?
More Related Content
What's hot
Government Webinar: Low-Cost Log, Network Configuration, and IT Monitoring So...

In this webinar, our SolarWinds sales engineer discussed the basic network management tools you need to operate and troubleshoot your network and help improve security. He also reviewed the key factors to consider, where to start, and provided details on some of the tools our government customers need today.
During this interactive webinar, attendees learned how:
SolarWinds® ipMonitor® provides visibility into availability and performance of your network, servers, and applications
Kiwi Syslog® Server centralizes and simplifies log message management across network devices and servers
Kiwi CatTools® provides powerful network automation and configuration management
Webinar: Real IT Compliance with SolarWinds

In this webinar, attendees learned how to leverage automation to improve responsiveness to IT threats and help their organization comply with cyber security regulations, mandates, and policies. Attendees learned about SolarWinds products that can provide automated responses and how they can be leveraged to help reduce reaction times and improve their organization’s security posture.
SolarWinds Government and Education sales engineers reviewed and demonstrated automation features of Network Configuration Manager (NCM), Security Event Manager (SEM), formerly Log & Event Manager, NetFlow Traffic Analyzer (NTA), and Log Analyzer (LA), and how they can be used to help improve governmental and organizational compliance. They also reviewed how our API can be used to integrate with other applications to support organizational objectives.
During this interactive webinar, attendees learned about:
• How NCM detects out-of-process configuration changes, audits configurations, and even corrects violations
• How SEM provides cross-platform event processing, notification, and remediation
• How to configure SEM rules and active responses to meet your organization’s security objectives
• How NTA supports port 0 monitoring and how it can alert on flow traffic thresholds per protocol
• How LA provides real-time log streaming and visualization to help identify the root cause and reduce troubleshooting
• How to push and pull data leveraging the Orion® Platform API and utilize the OrionSDK and SWQL to sync between external applications and tools
Government and Education Webinar: Technical Update and Demo of New Features

In this webinar, our SolarWinds sales engineer discussed new SolarWinds® products and features that are of interest to our federal, state, local, and education customers. Our sales engineer discussed and demonstrated the 2019.4 releases, consisting of Access Rights Manager, Security Event Manager, and the Orion® Platform enhancements, including Server & Application Monitor, Virtualization Manager, Server Configuration Monitor, Network Performance Monitor, Enterprise Operations Console, and more.
During this interactive webinar, attendees learned about:
Access Rights Manager
Updated dashboard
Create users and mailboxes in Office365®
Security Event Manager (formerly Log & Event Manager)
UI updates
Customizable email templates
Orion Platform enhancements
Azure® VM and SQL Database Managed Instance support
Orion Map enhancements
GER and JPN localization
Native SolarWinds Service Desk integration
Orion Product Enhancements
Server & Application Monitor- improved API support; Nutanix hardware health
Virtualization Manager – Nutanix hardware health
Server Configuration Monitor – Linux® server and application support
Network Performance Monitor – Device Views (technical preview)
NetFlow Traffic Analyzer – Cisco® Meraki® flow support
Database Performance Analyzer – Updated DB support, table tuning best practices, updated alerts and API
VoIP & Network Quality Manager – updated VoIP system support
Enterprise Operations Console – Improved workflow and authentication
Log Analyzer – Orion Log Viewer replaces legacy Syslog and Traps
Storage Resource Monitor – EMC CLARiiON controller and Data Domain support
Other product enhancements
Web Performance Monitor
Network Configuration Manager
User Device Tracker
IP Address Manager
Microsoft Intune - Empowering Enterprise Mobility - Presented by Atidan 

Simplify management of apps & devices
Microsoft Intune provides mobile device management, mobile application management, and PC management capabilities from the cloud. Using Intune, organizations can provide their employees with access to corporate applications, data, and resources from virtually anywhere on almost any device, while helping to keep corporate information secure.
Federal Webinar: Technical Update and Demo of New Features

In this webinar our Federal Sales Engineering team discussed and demonstrated Q4 2018 releases, including Network Performance Monitor (NPM) 12.4, NetFlow Traffic Analyzer (NTA) 4.5, Network Configuration Manager (NCM) 7.9, IP Address Manager (IPAM) 4.8, Orion® Platform 2018.4, and Dameware® 12.1. They provided a sneak peek of Log & Event Manager (LEM) 6.6 and reviewed our newest product, Access Rights Manager (ARM).
During this interactive webinar, attendees learned about:
Network Performance Monitor 12.4
Cisco® Application Centric Infrastructure (ACI) (software-defined networking) support
NetFlow Traffic Analyzer 4.5
Alert on flow
Network Configuration Manager 7.9
Multi-device baselines
New: Access Rights Manager
Monitoring of Active Directory® and Microsoft® Exchange™
Auditing of Windows® File Share
User provisioning, management, and permissions analysis
Custom report generation
Self-service permissions portal
IP Address Manager 4.8
Infoblox® support
Orion Platform 2018.4
SAML authentication
Centralized upgrades
Device guard support for Microsoft Windows®
Dameware 12.1
TLS 1.2 compliant
New Mirror Driver
Sneak Peek
Log & Event Manager 6.6
Continue HTML migration
Intel Gateway Solutions for the Internet of Things

Intel Gateway Solutions for the Internet of Things (IoT) is a family of platforms that enables companies to seamlessly interconnect industrial infrastructure devices and secure data flow between devices and the cloud. Intel Gateway Solutions for IoT enables customers to securely aggregate, share,and filter data for analysis.
Modern Workplace Summit 2015 - Management

My slide deck from the MWS summit. Device security and management with tools like EMS, Intune, Azure Active Directory and Office 365
http://mwssummit.com/agenda/windows-10-summit-agenda/
Empower Enterprise Mobility- Maximize Mobile Control- Presented by Atidan

Identity + Mobile Management + Security
Keep your employees productive on their favorite apps and devices—and your company data protected with enterprise mobility solutions from Microsoft.
Windows 10 is better with EMS
Windows 10 is the best Windows ever and provides a foundation for protection against modern threats and continuous management while enabling your users to be more productive. To get the most out of your mobile security and productivity strategy, integrate the Microsoft Enterprise Mobility Suite (EMS) with Windows 10 for greater protection of users, devices, apps, and data.
Our enterprise-grade security
A key concern for you continues to be security, and rightly so. Identity is the control plane at the center of our solution helping you to be more secure. Only Microsoft offers cloud identity and access management solutions running at Internet scale and designed to help secure your IT environment. Microsoft Azure Active Directory has hundreds of millions of users, is available in 35 datacenters around the world, and has processed more than 1 trillion (yes, trillion) authentications. Our innovative new technology, Microsoft Advanced Threat Analytics is designed to help you identify advanced persistent threats in your organization before they cause damage.
We’re more integrated and flexible
Architecture matters. That’s why our solutions run in the cloud and work seamlessly with your on-premises investments—taking the worry out of scale, maintenance, and updates.
Our cloud-first approach provides an integrated set of solutions that are designed to work together from the ground up, avoiding the need for costly and complicated integration efforts across point capabilities. It’s the fastest and most cost-effective way to meet new business challenges and accommodate new devices, new apps, and new hires.
Nobody manages Office better
Protecting email and other corporate data on mobile devices—without bogging down workers—is one of today’s biggest IT challenges. Other vendors solve it with apps that compromise user experience and put the brakes on productivity.
Microsoft enterprise mobility solutions integrate deeply with Microsoft Office, the gold standard of productivity. We’re the only solution that brings managed mobile productivity with Microsoft Office across devices.
Accelerating Operational Excellence with IT/OT Convergence

EMEA Partner Summit 2015
Presented by Pierre Paterni, Business Development Lead - Rockwell Automation
Government Webinar: Improving Security Compliance with IT Monitoring Tools 

In this webinar SolarWinds and DH Technologies discussed how SolarWinds infrastructure monitoring tools can be used to help improve your agency’s IT security posture. We discussed how our solutions help manage and monitor network devices and their configurations to enhance risk management, IT security, and compliance. Discussions included simplifying day-to-day operations, increasing automation, and generating reports to help verify compliance and highlight violations.
During this interactive webinar, attendees learned about:
Leverage Network Configuration Manager (NCM) and Security Event Manager (SEM) (formerly Log & Event Manager) to verify that controls have been implemented correctly
Employ SEM, Network Performance Monitor, and NCM to monitor that controls are working as expected
Quickly and easily produce out-of-the-box compliance reports for DISA STIGS, FISMA, and more
Leverage Server Configuration Monitor (SCM) to track and get alerted when server configurations change
Government and Education Webinar: Conquering Remote Work IT Challenges 

In this webinar, we discussed how SolarWinds® solutions can help you overcome remote work IT challenges.
During this interactive webinar, attendees learned about:
Improve network monitoring, configuration, and VPN management with SolarWinds Network Performance Monitor (NPM) and SolarWinds Network Configuration Manager (NCM)
Monitor the server and application performance of your collaboration systems with SolarWinds Server & Application Monitor (SAM)
Utilize configuration management to efficiently deploy upgrades and improve compliance with NCM
Support users and systems remotely with tools such as SolarWinds Dameware® Remote Support (DRS) and SolarWinds Dameware Remote Everywhere (DRE)
Improve IT request management, ticket tracking, and asset management with tools like SolarWinds Web Help Desk® and SolarWinds Service Desk
Automate provisioning and permissions management with SolarWinds Access Rights Manager™ (ARM)
Locate users and devices on your network with SolarWinds User Device Tracker (UDT)
TechWiseTV Workshop: Q&A OpenDNS and AnyConnect 

This is the Q&A we captured from the live event for your reference.
Motadata brochure

Mindarray Systems has been an innovator in Network Monitoring and Data Analytics Technologies. Our first product, Minder, was the only IT monitoring platform that offered a truly unified view and correlation across all layers of IT infrastructure from a single product.
Motadata today, is strongly positioned to enable Telco’s, Enterprise and Government sectors to streamline their IT operations with next-gen product suite which is pre-integrated yet modular, consisting of
1) Infrastructure Intelligence Platform (IIP) for Network Management
2) Data Analytics Platform (DAP) for Log Management & Flow Analytics and
3) ITSM Platform for IT Service Automation.
Motadata is a unified IT Infrastructure Monitoring, Log & Flow Management, and IT Service Management Platform, offering operational insights into your IT infrastructure and its performance and is designed to identify & resolve complex problems faster that ensures 100% uptime of all business-critical components. Motadata enables you to make more informed business decisions by offering complete visibility into the health and key performance indicators (KPIs) of IT services. It helps in reducing CAPEX, offers Agility to resolve issues faster, is compatible in a hybrid ecosystem, and offers ease of integration with existing and future platforms.
In summary, with Motadata, Mindarray Systems offers the perfect solution needed to confidently handle the challenges of today’s increasingly complex business operations and IT infrastructure management.
UDT - Government and Healthcare

Studies have found that organized crime is increasingly targeting health care entities because health records are worth more and easier to obtain. UDT offers a complete spectrum of technical, professional and managed services to protect your organization’s ePHI and comply with regulations.
Get Ahead of Cyber Attacks with Microsoft Enterprise Mobility + Security

Digital transformation with freedom and peace of mind
Holistic, identity-driven protection
Help guard your data from attacks on multiple levels using innovative, identity-driven security techniques.
Productivity without compromise
Preserve the mobile and desktop experiences your workers need to stay working with familiar apps and tools.
Flexible, comprehensive solutions
Do more with less—protect users, devices, apps, and data with intuitive mobile management on a future-ready platform.
microsoft@atidan.com
What's hot (20)
Government Webinar: Low-Cost Log, Network Configuration, and IT Monitoring So...

Government Webinar: Low-Cost Log, Network Configuration, and IT Monitoring So...
Government and Education Webinar: Technical Update and Demo of New Features

Government and Education Webinar: Technical Update and Demo of New Features
Microsoft Intune - Empowering Enterprise Mobility - Presented by Atidan 

Microsoft Intune - Empowering Enterprise Mobility - Presented by Atidan
Federal Webinar: Technical Update and Demo of New Features

Federal Webinar: Technical Update and Demo of New Features
Intel Gateway Solutions for the Internet of Things

Intel Gateway Solutions for the Internet of Things
Microsoft Enterprise Mobility and Security Launch - August 5-2015 - Atidan

Microsoft Enterprise Mobility and Security Launch - August 5-2015 - Atidan
Empower Enterprise Mobility- Maximize Mobile Control- Presented by Atidan

Empower Enterprise Mobility- Maximize Mobile Control- Presented by Atidan
Accelerating Operational Excellence with IT/OT Convergence

Accelerating Operational Excellence with IT/OT Convergence
Government Webinar: Improving Security Compliance with IT Monitoring Tools 

Government Webinar: Improving Security Compliance with IT Monitoring Tools
Government and Education Webinar: Conquering Remote Work IT Challenges 

Government and Education Webinar: Conquering Remote Work IT Challenges
Get Ahead of Cyber Attacks with Microsoft Enterprise Mobility + Security

Get Ahead of Cyber Attacks with Microsoft Enterprise Mobility + Security
Similar to Sumo Logic IT Operations Solutions Brief
RoltaiPerspective enterprise suite for SOA-based Enterprise Integration

RoltaiPerspective Enterprise Suite is an IT solution which gives flexibility by accomplishing the specific needs of an enterprise and helps organization accomplish fast ROI through asset consolidation and agile business processes. RoltaiPerspective empowers organizations to bridge the gap between old applications and next gen applications thus encouraging an environment of/for change and upgrade.
Introduction to Symantec Endpoint Management75.pptx

How does Symantec solve your common IT challenges?
Oracle Cloud Essentials

AI technology is fundamentally altering enterprise
computing by changing the way organizations
receive, manage, and secure business data.
The Cloud Adoption Challenge

Cloud computing presents economic and business benefits that today’s enterprise cannot ignore. In order to successfully compete, enterprises require a strategy that delivers a unified approach for the visibility and management of new cloud applications, as well as tools to accelerate the migration from on-premise to cloud deployments.
Leveraging machine data can significantly accelerate an organization’s cloud strategy. Through effectively harnessing machine data, organizations gain needed visibility into applications and infrastructure hosted in the cloud. They are able to correlate cloud and on-premise
data sets and are be able to monitor availability and performance across all environments.
However, with the explosive growth in the volume, variety, and velocity of machine data, enterprises today cannot keep up with the data deluge and are therefore unable to transform their data into insights. To accelerate cloud adoption, enterprises need a solution that is capable of scaling to handle the volume of data generated and robust enough to transform that data into insights.
Log Analytics for Distributed Microservices

Log Analytics and Operational Intelligence for Distributed Microservices.
IT systems and applications generate more and more distributed machine data due to millions of mobile devices, Internet of Things, social network users, and other new emerging technologies. However, organizations experience challenges when monitoring and managing their IT systems and technology infrastructure. They struggle with distributed Microservices and Cloud architectures, custom application monitoring and debugging, network and server monitoring / troubleshooting, security analysis, compliance standards, and others.
This session discusses how to solve the challenges of monitoring and analyzing Terabytes and more of different distributed machine data to leverage the “digital business”. The main part of the session compares different open source frameworks and SaaS cloud solutions for Log Management and operational intelligence, such as Graylog , the “ELK stack”, Papertrail, Splunk or TIBCO LogLogic Unity). A live demo will demonstrate how to monitor and analyze distributed Microservices and sensor data from the “Internet of Things”.
The session also explains the distinction of the discussed solutions to other big data components such as Apache Hadoop, Data Warehouse or Machine Learning, and how they can complement each other in a big data architecture.
The session concludes with an outlook to the new, advanced concept of IT Operations Analytics (ITOA). Prsesn
Rhea corporate presentation v2

Through this presentation Rhea shows you what it sees as the future of business applications. How we build them up and what the advantages are in working with us in regards of the integration of new technological developments.
Promote your IT visibility, health, and performance using ServiceNow ITOM.pdf

ServiceNow ITOM (Information Technology and Operations Management) solutions enable companies to obtain complete insight into their IT infrastructure and detect problems before they arise. ServiceNow Discovery assists organizations in developing a single solution to handle IT infrastructure across the enterprise and cloud. ITOM offers considerable value to ServiceNow with its comprehensive, seamless features and 360-degree monitoring to avoid service disruptions and oversee hybrid cloud environments.
IT Infrastructure Management | Defination, Objectives & Strategies

The rise of technology is accelerating at an unprecedented speed, and there’s no way of stopping it. Regardless of however much fear, there may be of new technology, it is the way towards progress and development. In this ever-evolving wave of technology, it is crucial to stay ahead of the curve and be aware of the tech industry news and the upcoming technology that may arise. Several tech trends are reshaping the world’s industries and challenging past traditions.
Open Digital Framework from TMFORUM

Open Digital Architecture (ODA) is a blueprint for modular, cloud-based, open digital platforms that can be orchestrated using AI.
Designed to support our industry into the cloud native era, ODA sets the framework required
for CSPs to invest in IT, transforming business agility and operations by creating simpler IT and network solutions that are easier and cheaper to deploy, integrate and upgrade. Enabling growth, profitability and a cutting-edge customer experience.
The Importance of Choosing the Best IT Infrastructure Monitoring Software

IT infrastructure monitoring services are crucial for the efficient and reliable functioning of modern organizations that rely heavily on technology. These services involve the constant surveillance and analysis of various components of an organization’s IT infrastructure, such as servers, networks, databases, applications, and cloud resources.
Splunk for application_management

Splunk, Software Tools, Big Data, Logging, PCI, Information security, Cisco Systems, VMware ESX, Regulatory compliance, FISMA, Enterprise architecture, Data center, security software, SCADA, Windows,Unix,Scanners, Citrix, Microsoft Active Directory
AppViewX Automation+ brochure

The AppViewX AUTOMATION+ product enables the Application Delivery Automation and Network Security Automation solutions on our AppViewX Platform. AUTOMATION+ helps Enterprise IT manage, automate and orchestrate application delivery and network security services. AUTOMATION+ provides an application-centric view into the state of the application
delivery and network security infrastructure running in multi-cloud environments. Application, network, and security engineers may self-service and initiate automation
workflows that deliver compliance and true business agility.
How Can Your Organization Benefit From Application Modernization_.pdf

Application modernization refers to the process of updating or transforming legacy software applications to make them more contemporary, efficient, and aligned with current business needs and technology trends. Adopting application modernization can bring several benefits to an organization
Citrix Flexcast + Assessment Approach Lunch & Learn

From the Sirius Q3 Lunch and Learn Series in the Carolinas
IRJET-Testing Uncertainty of Cyber-Physical Systems in IoT Cloud Infrastructu...

https://www.irjet.net/archives/V6/i4/IRJET-V6I4154.pdf
Similar to Sumo Logic IT Operations Solutions Brief (20)
RoltaiPerspective enterprise suite for SOA-based Enterprise Integration

RoltaiPerspective enterprise suite for SOA-based Enterprise Integration
Introduction to Symantec Endpoint Management75.pptx

Introduction to Symantec Endpoint Management75.pptx
Promote your IT visibility, health, and performance using ServiceNow ITOM.pdf

Promote your IT visibility, health, and performance using ServiceNow ITOM.pdf
IT Infrastructure Management | Defination, Objectives & Strategies

IT Infrastructure Management | Defination, Objectives & Strategies
The Importance of Choosing the Best IT Infrastructure Monitoring Software

The Importance of Choosing the Best IT Infrastructure Monitoring Software
What Is an IT Infrastructure_ Types and Components.pdf

What Is an IT Infrastructure_ Types and Components.pdf
How Can Your Organization Benefit From Application Modernization_.pdf

How Can Your Organization Benefit From Application Modernization_.pdf
Citrix Flexcast + Assessment Approach Lunch & Learn

Citrix Flexcast + Assessment Approach Lunch & Learn
IRJET-Testing Uncertainty of Cyber-Physical Systems in IoT Cloud Infrastructu...

IRJET-Testing Uncertainty of Cyber-Physical Systems in IoT Cloud Infrastructu...
Sumo Logic IT Operations Solutions Brief
- 1. SOLUTIONS BRIEF Today’s IT environment is more complex then ever before. With cloud infrastructures, multi-vendor environments, borderless applications and continuous deployments models, all generating data at an unprecedented scale, problem identification and repair present formidable challenges. IT teams attempt to analyze their infrastructures in monitoring silos, where a failure in one area can impact an entire service, generating multiple alerts across multiple tools – resulting in silos of management and monitoring. IT is under pressure to keep critical business applications and services running to meet the demands of the business and customer. But with multiple legacy monitoring tools this can present quite a challenge. IT teams require a modern solution that integrates with their current environment and provides end-to-end visibility in a single unified view for all their applications and supporting infrastructure. Sumo Logic - The Service for IT Operations Sumo Logic is the cloud-native service that helps deliver visibility into the operation of an organization’s IT infrastructure. By ingesting the growing pool of machine data generated within the IT environment, Sumo Logic easily delivers critical performance, availability, configuration, capacity, and security insights to help you monitor and support your critical business apps and underlying IT infrastructure. The secure by design analytics service starts delivering value within minutes and operates at unprecedented scale, while helping customers further reduce cost and complexity. Proven machine learning analytics, integrations, and purpose-built apps ensure mission critical applications and services run smoothly. The Sumo Logic Service Model Advantage •• Eliminate monitoring silos by merging all your application and IT infrastructure data •• Discover meaningful patterns in your IT data and resolve issues faster •• Detect abnormalities in the performance and usage of your applications and IT systems •• Create unified views of applications and the underlying IT infrastructure •• Optimize resource utilization and improve system uptime and reliability •• Analyze trends and patterns to avoid service disruption •• View a single unified source of truth across the environment IT Visibility with Sumo Logic Sumo Logic is the cloud-native service that delivers visibility into the operation of an organization’s IT infrastructure. Monitoring and Supporting Your IT Infrastructure MICROSERVICES VIRTUALIZATION EDGE SERVICES OPERATING SYSTEMS CONTAINERS ON-PREMISE APPLICATIONS CLOUD IT OPERATIONS
- 2. Sumo Logic Solutions for IT Sumo Logic offers some of the most comprehensive native integrations for IT to modernize operations and deliver superior service to the business and its customers. With multiple inclusive apps and integrations, the Sumo Logic cloud-native service enables IT teams to monitor and support every application and the underlying IT infrastructure from one centralized environment. Toll-Free: 1.855.LOG.SUMO | Int’l: 1.650.810.8700 305 Main Street, Redwood City, CA 94603 www.sumologic.com © Copyright 2015 Sumo Logic, Inc. All rights reserved. Sumo Logic, Elastic Log Processing, LogReduce, Push Analytics and Big Data for Real-Time IT are trademarks of Sumo Logic, Inc. All other company and product names mentioned herein may be trademarks of their respective owners. SB-SL-0415. Updated 11/15 For more information on Apps and Connectors www.sumologic.com/applications SOLUTIONS BRIEF | IT Visibility with Sumo Logic Sumo Logic for Applications Applications are dependent on multiple independent layers of services, microservices, third-party APIs, and databases. All these layers work alone to serve and deliver an app. Whether on-premise, in the cloud or on a mobile device, every layer requires constant monitoring to ensure availability and service delivery. With Sumo Logic, it is easy to get visibility into an application and its multiple independent layers and dependencies so that it is readily available. Sumo Logic for Virtualization Virtualized infrastructures are in a constant state of flux, where workloads and resources are dynamically changing. Monitoring the environment that supports multiple critical applications at the same time is critical. With Sumo Logic, get real-time visibility into the dynamic virtualized environment with native integration for VMware to quickly identify problems, resolve issues, monitor usage and performance. Sumo Logic for Identity User identities are the keys to accessing IT infrastructure and sensitive business information. Monitoring and tracking user identities, how they are used and what resources they leverage is key to building and maintaining a secure infrastructure. With native integration for Windows Active Directory, organizations can easily monitor the health of their identity infrastructure, maintaining a secure operational infrastructure. Sumo Logic for Infrastructure Gain visibility with comprehensive monitoring solutions for the core foundation of your IT infrastructure – the operating system. By monitoring the critical infrastructure component that supports every business application and critical service, the native integrations for Windows and Linux enable IT teams to identify problems, pinpoint performance issues, and correlate events and system metrics with application data to keep critical services running. Sumo Logic for Containers Docker containers represent the new way of packaging an application with all of its dependencies into a standardized unit for deployment. The key for the successful deployment of applications in containers is the continuous monitoring of the Docker environment. With the Sumo Logic integration for Docker, organizations can easily track the status of containers, and container performance to ensure application availability and delivery. Sumo Logic for Cloud Services Sumo Logic provides operational visibility with a unified view across the Amazon Web Service infrastructure. With a comprehensive set of applications and integrations for AWS services, IT teams can immediately visualize and monitor their workloads easily, identify issues and expedite root-cause analysis. CLOUD VISIBILITY VIRTUALIZATIONCONTAINERS DATABASE INFRASTRUCTURE IDENTITYAND ACCESSMONITORING APP MONITORING CONTENT DELIVERY