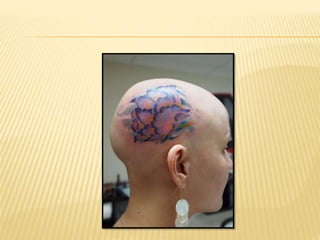
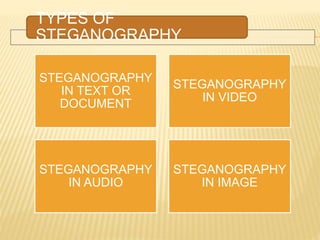
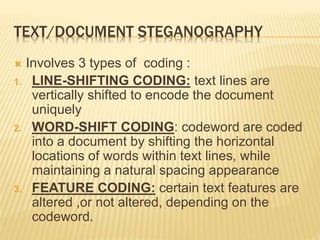
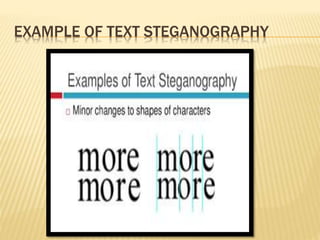
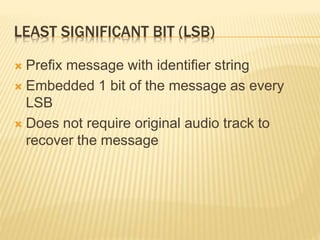
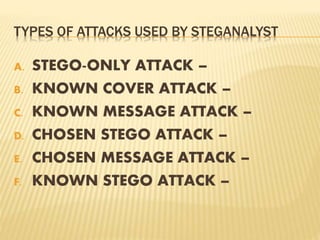
The document discusses steganography, the art of hiding messages to ensure only the sender and recipient are aware of their existence. It covers its history, types (text, image, audio, video), and techniques, including line-shifting and least significant bit insertion, emphasizing its applications and the challenges of steganalysis. Additionally, it outlines the advantages and disadvantages of steganography, highlighting its potential for secure communication and the risks involved.