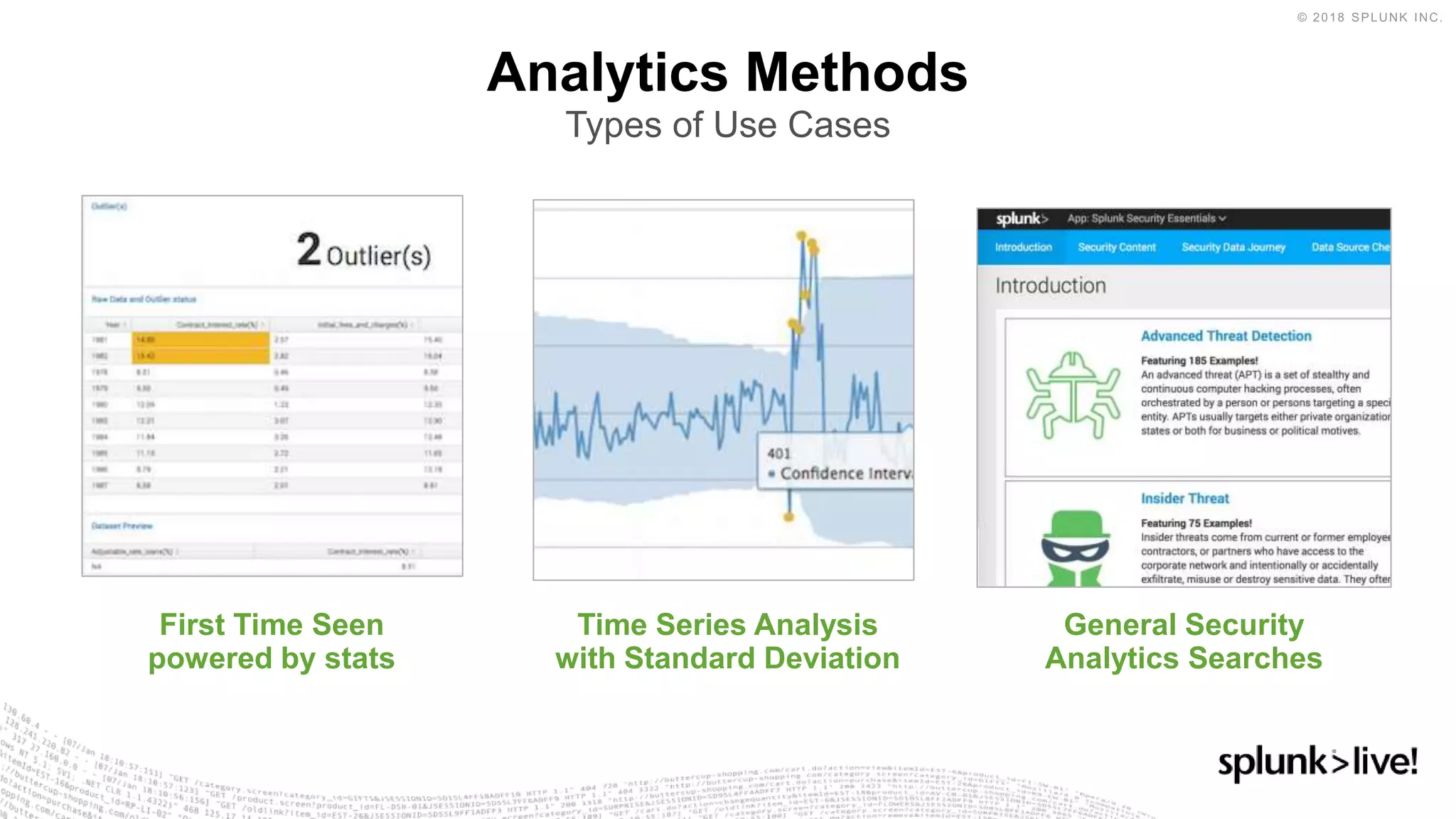
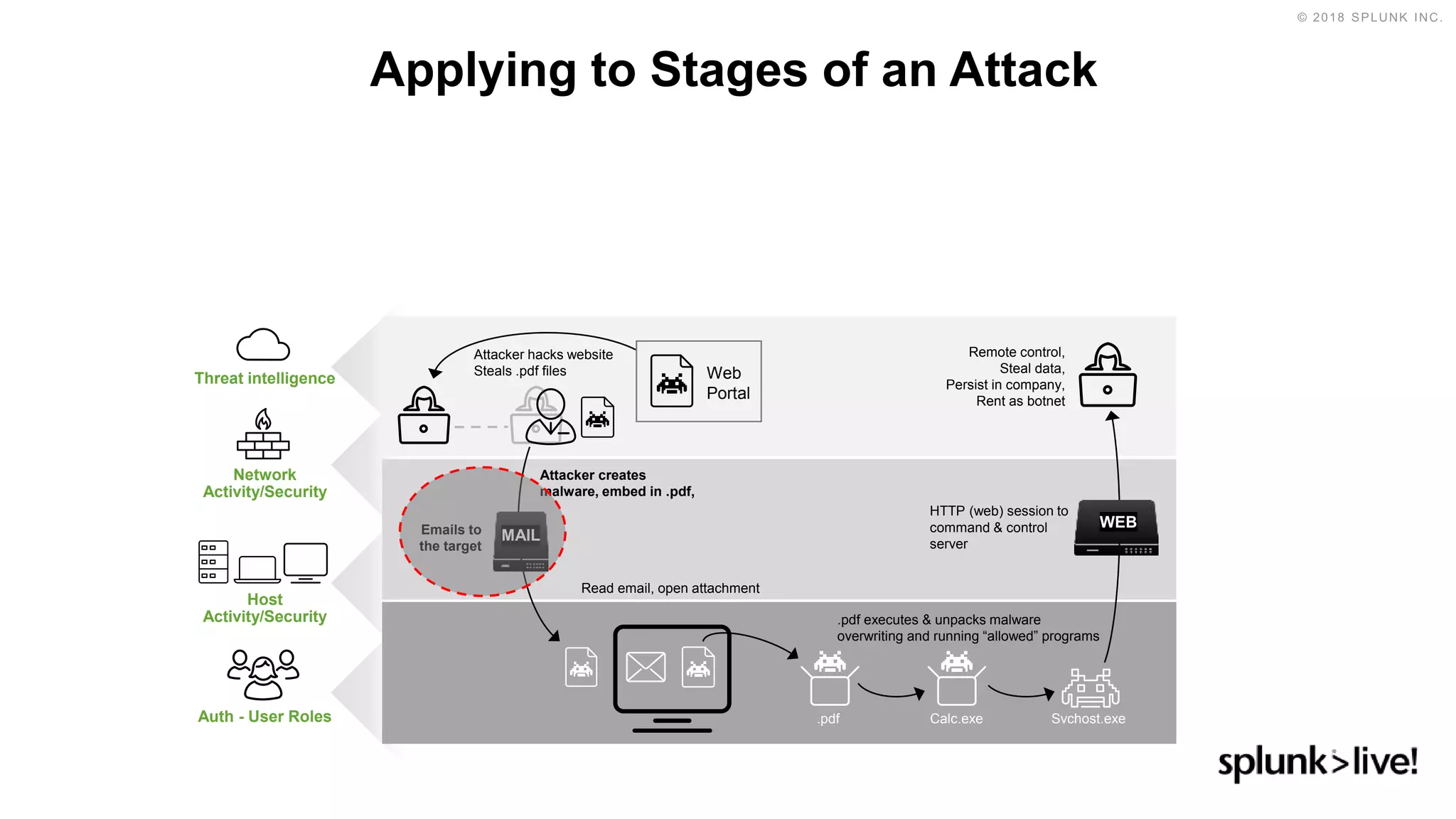
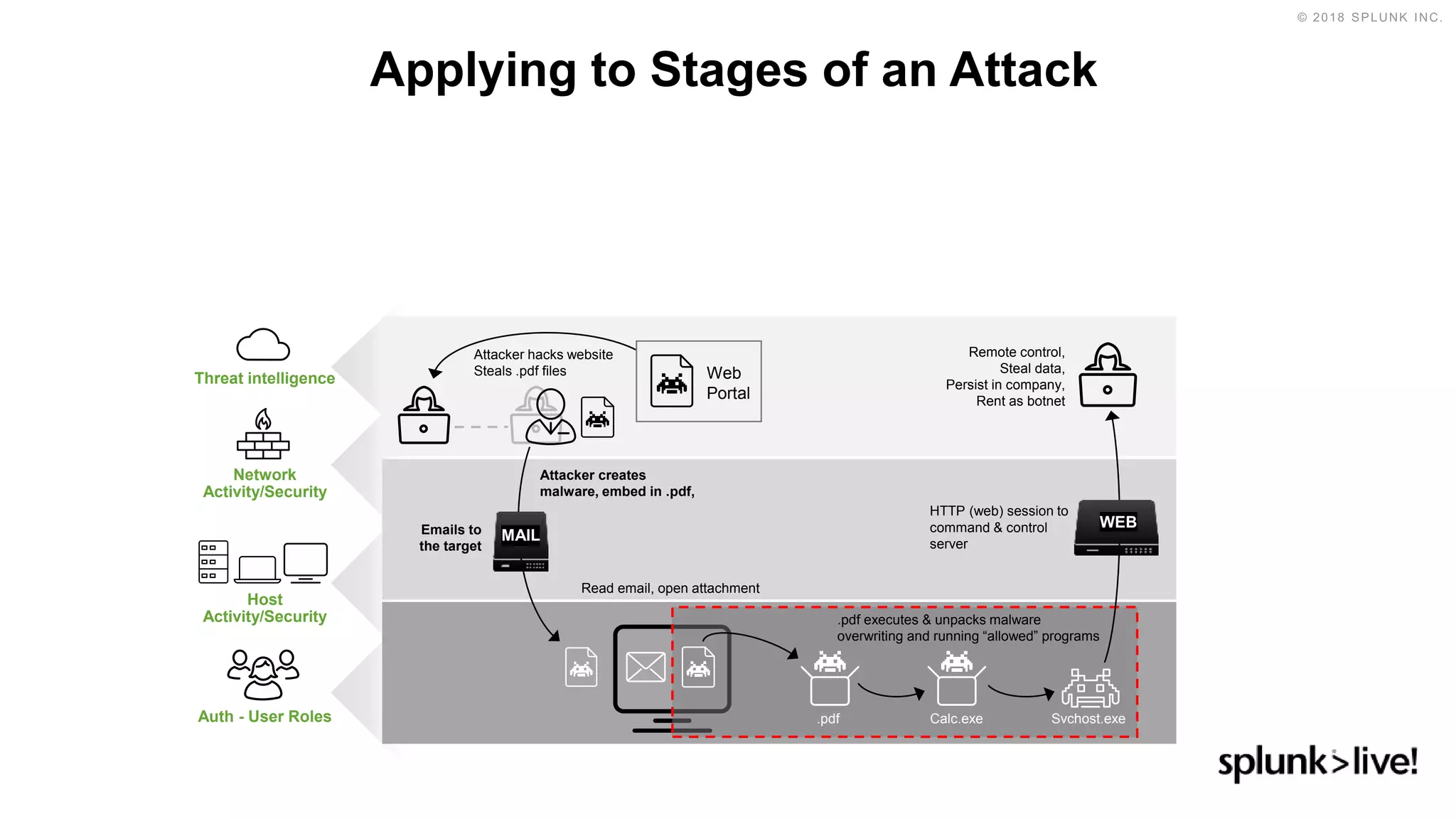
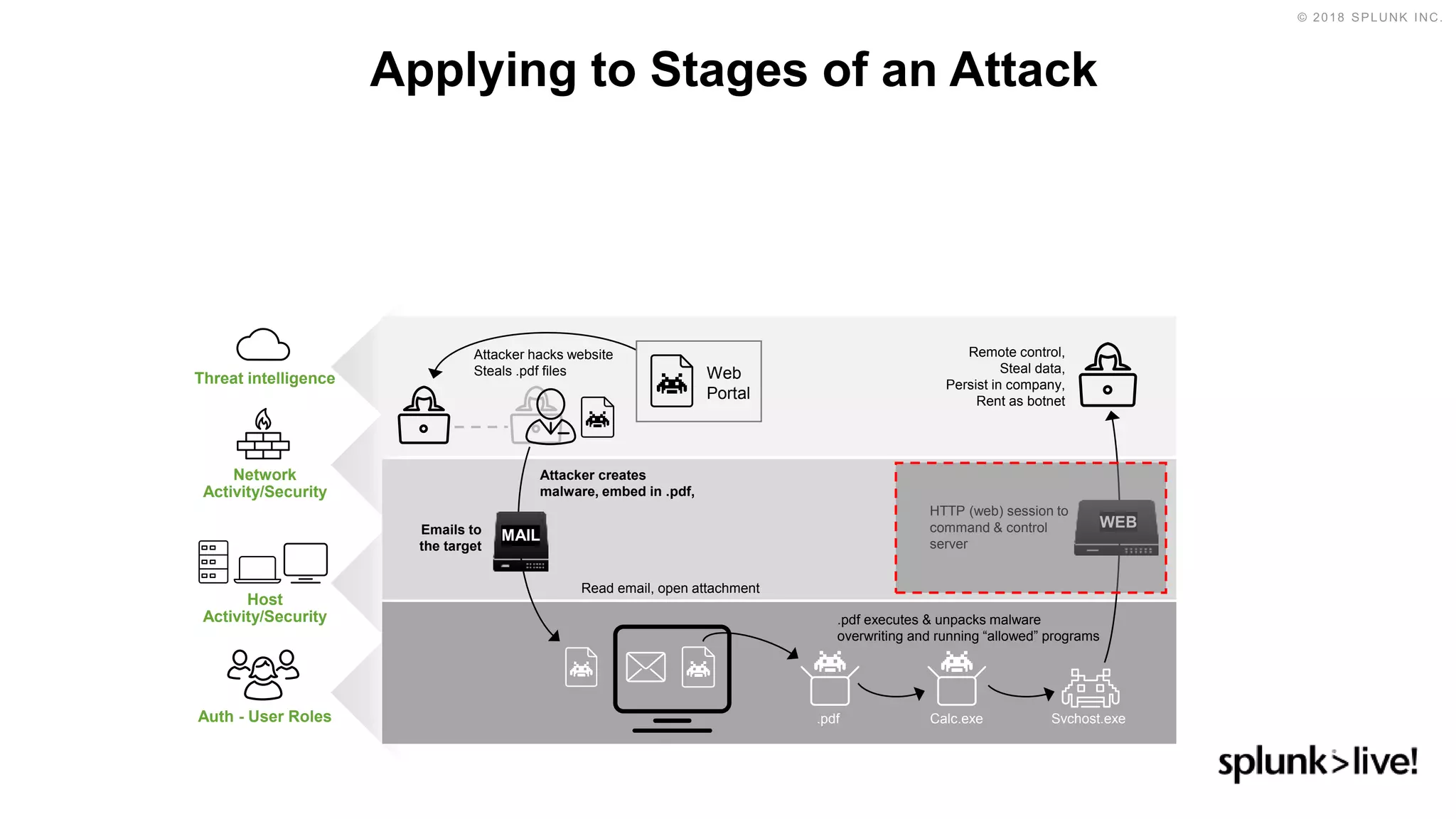
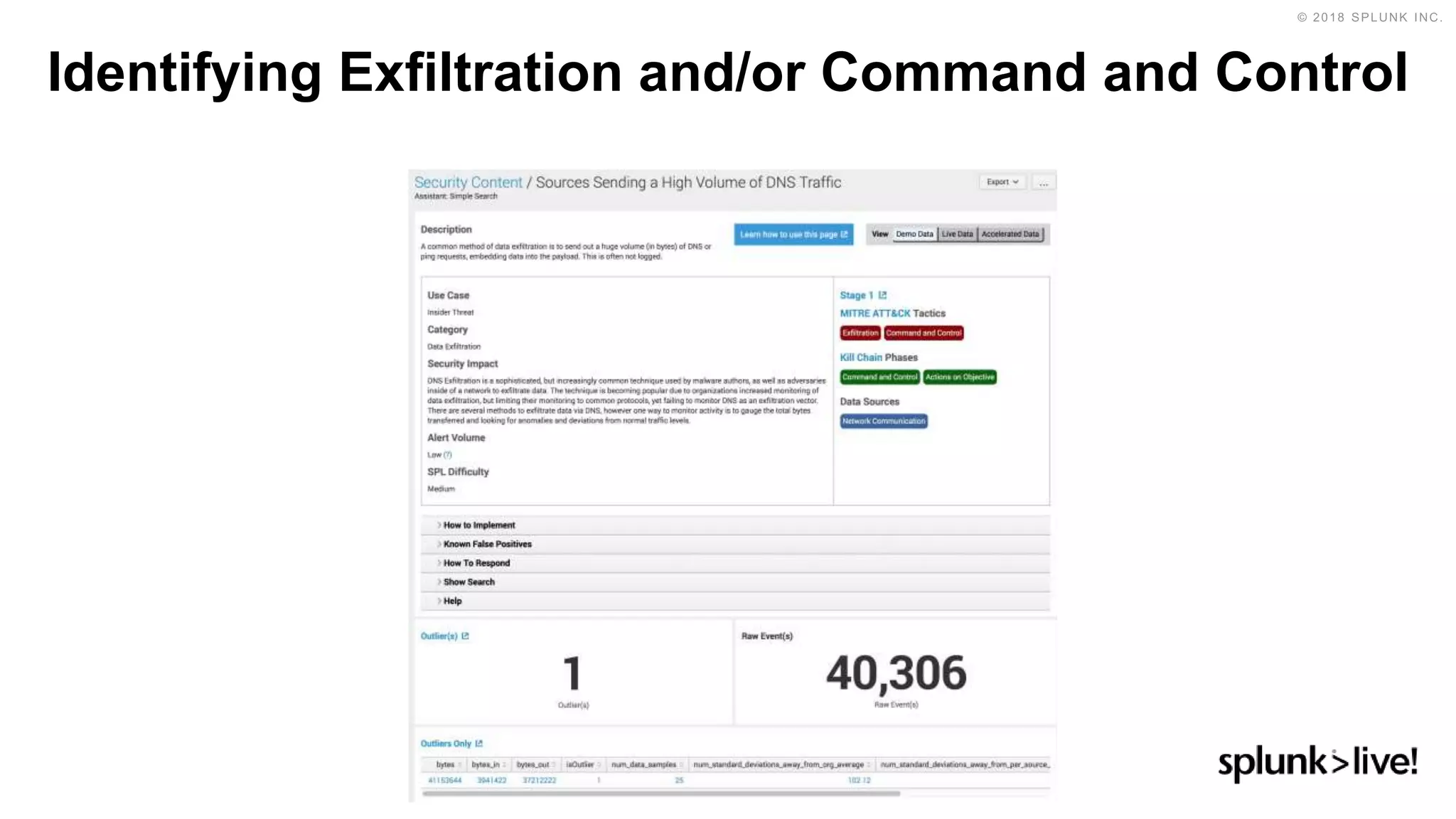
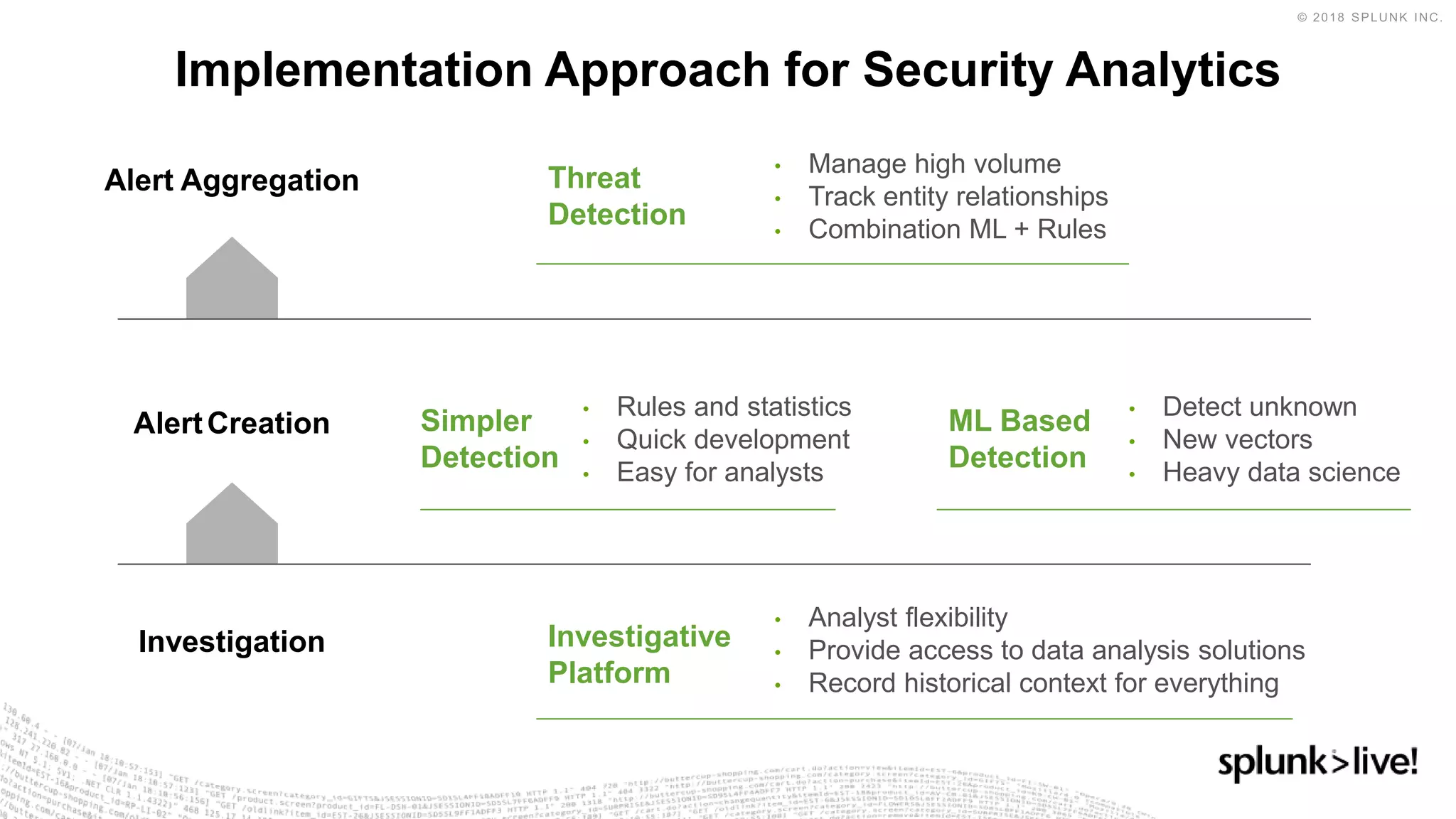
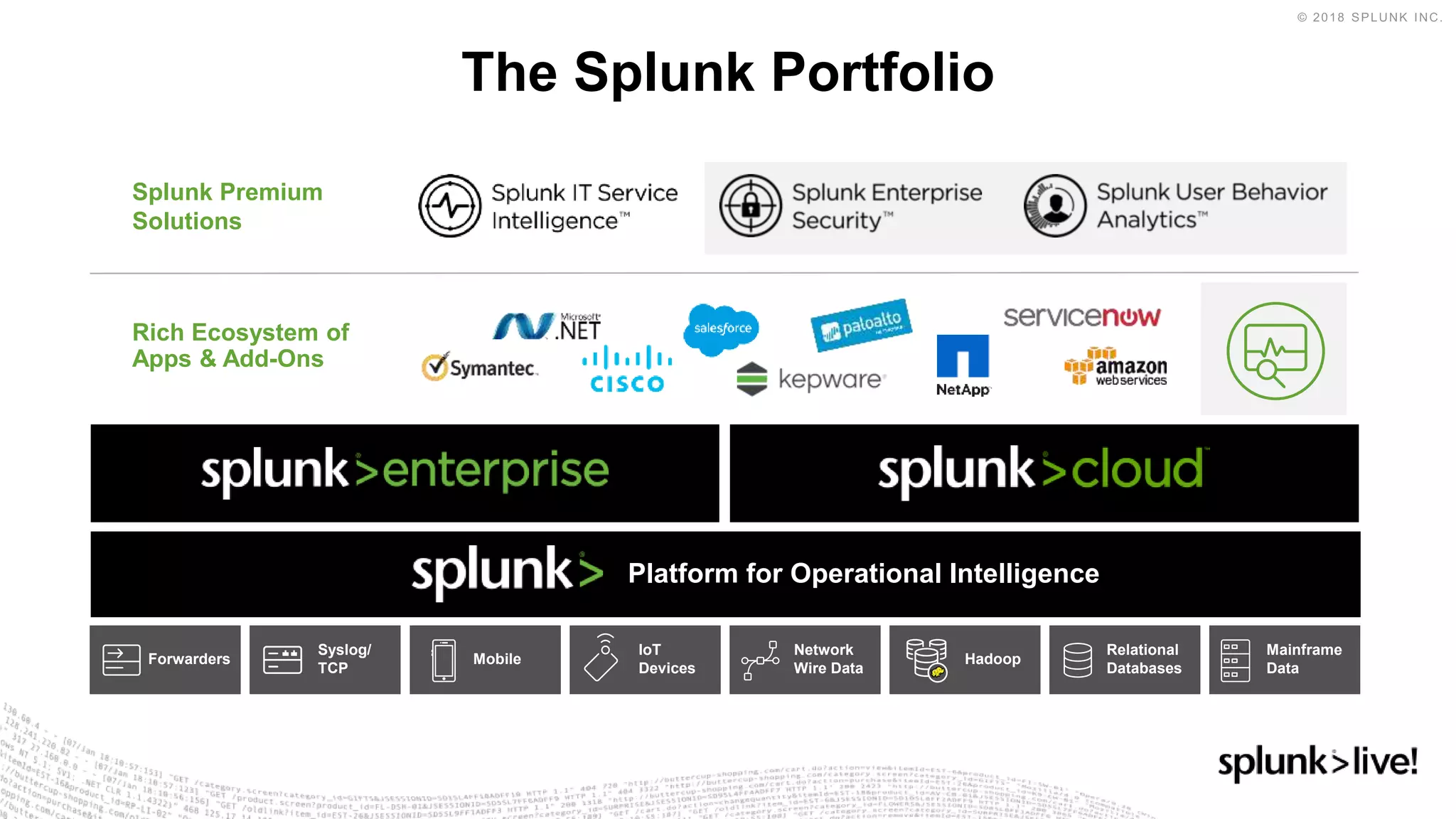
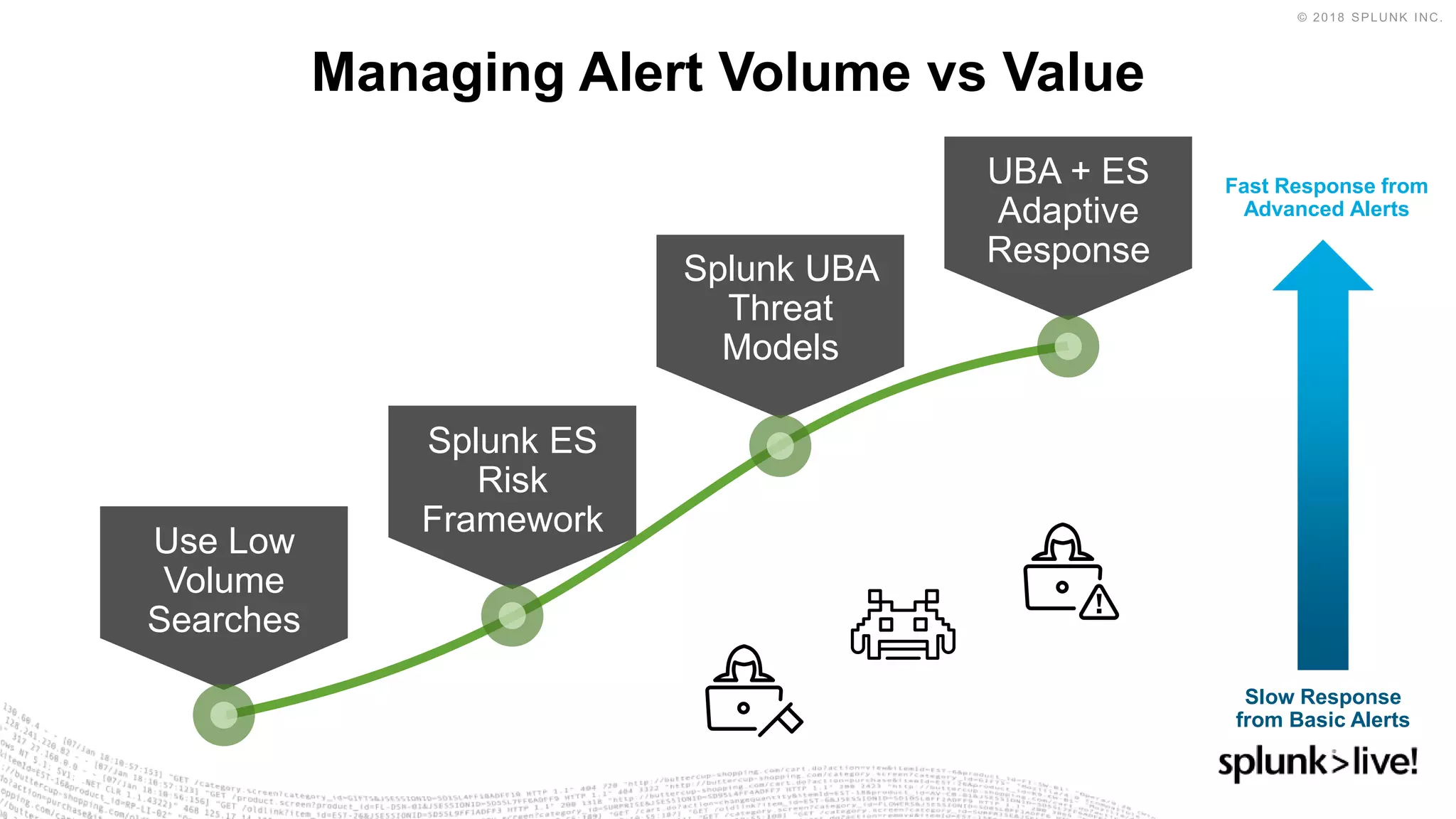
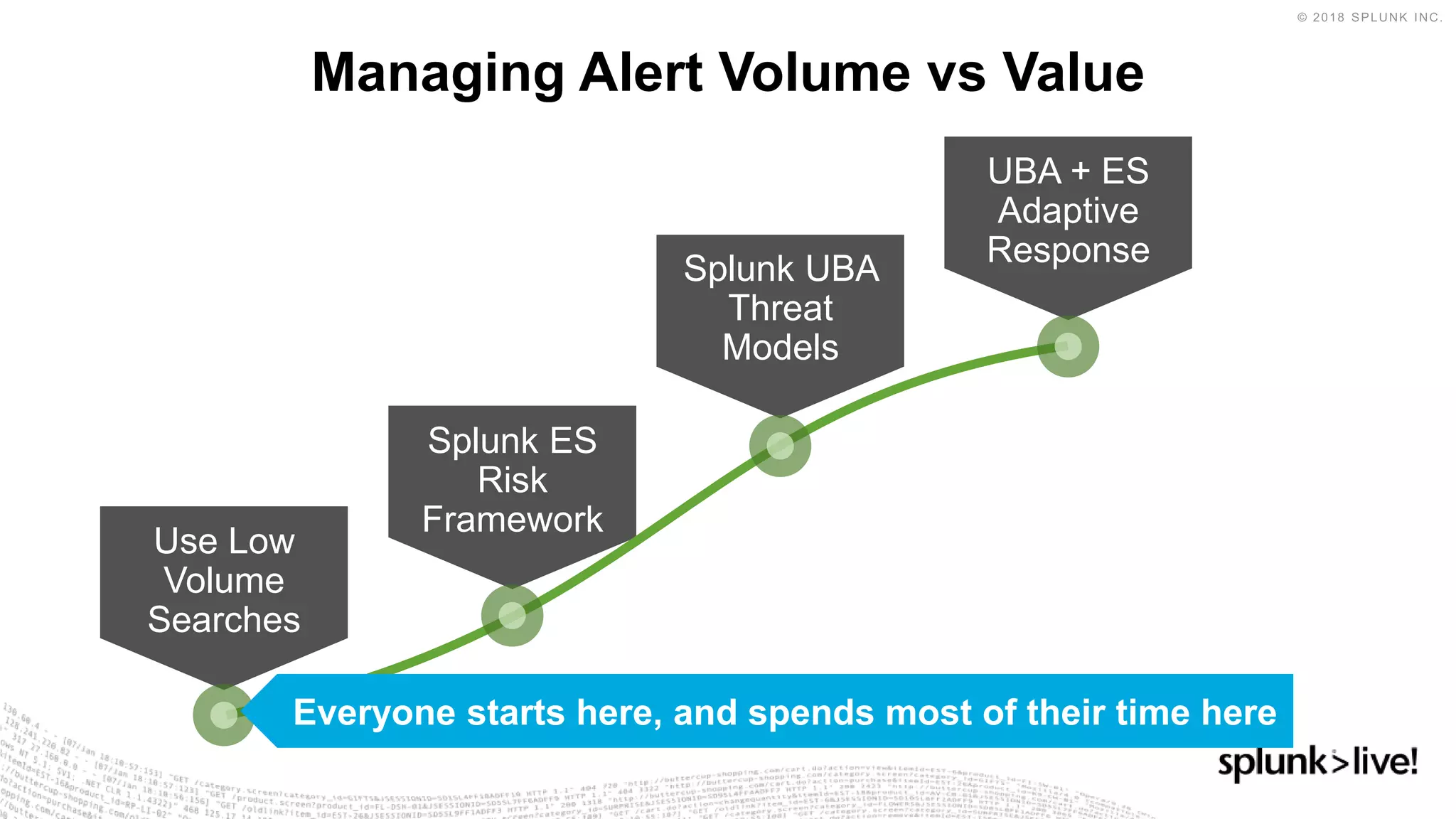
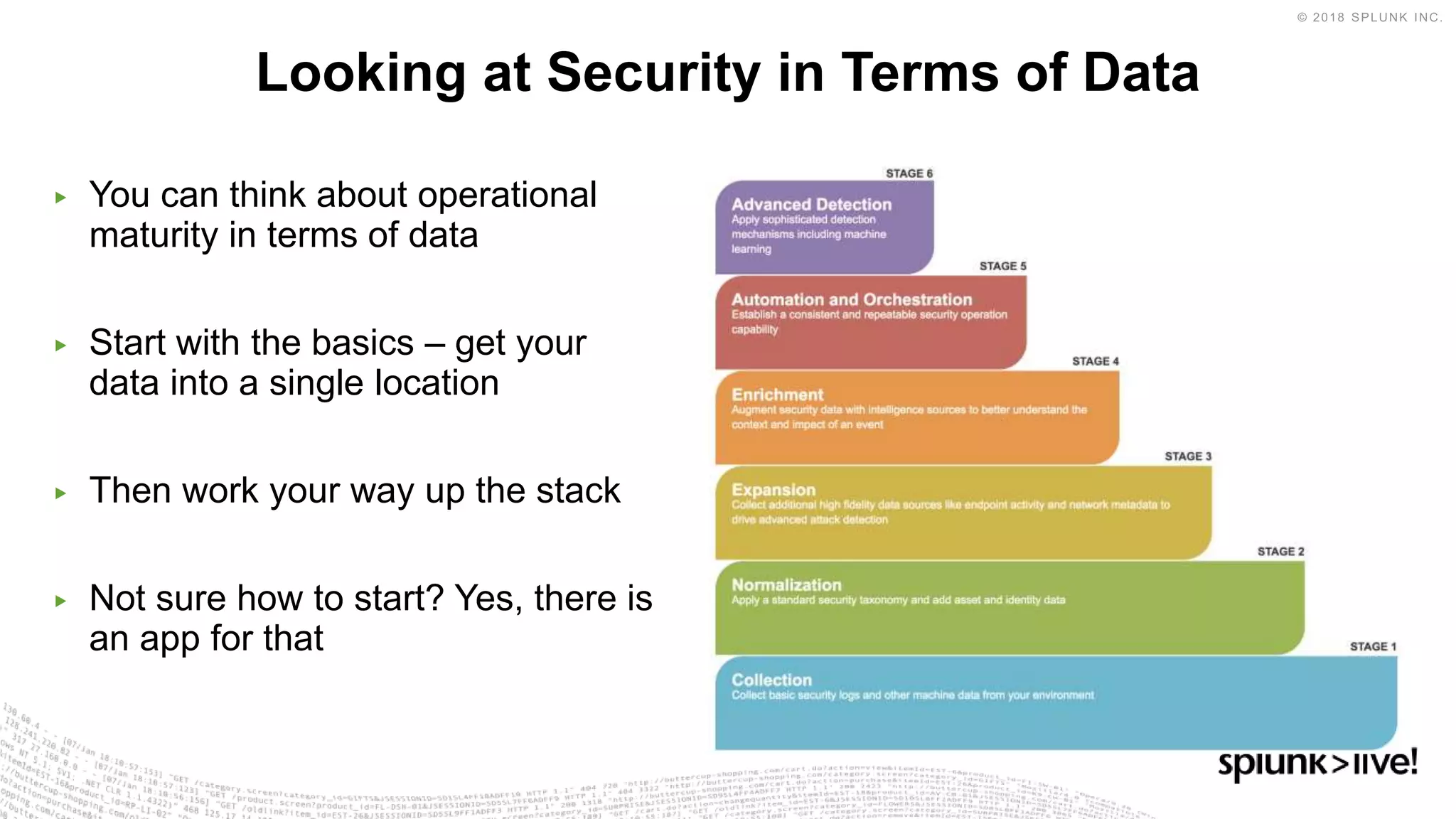
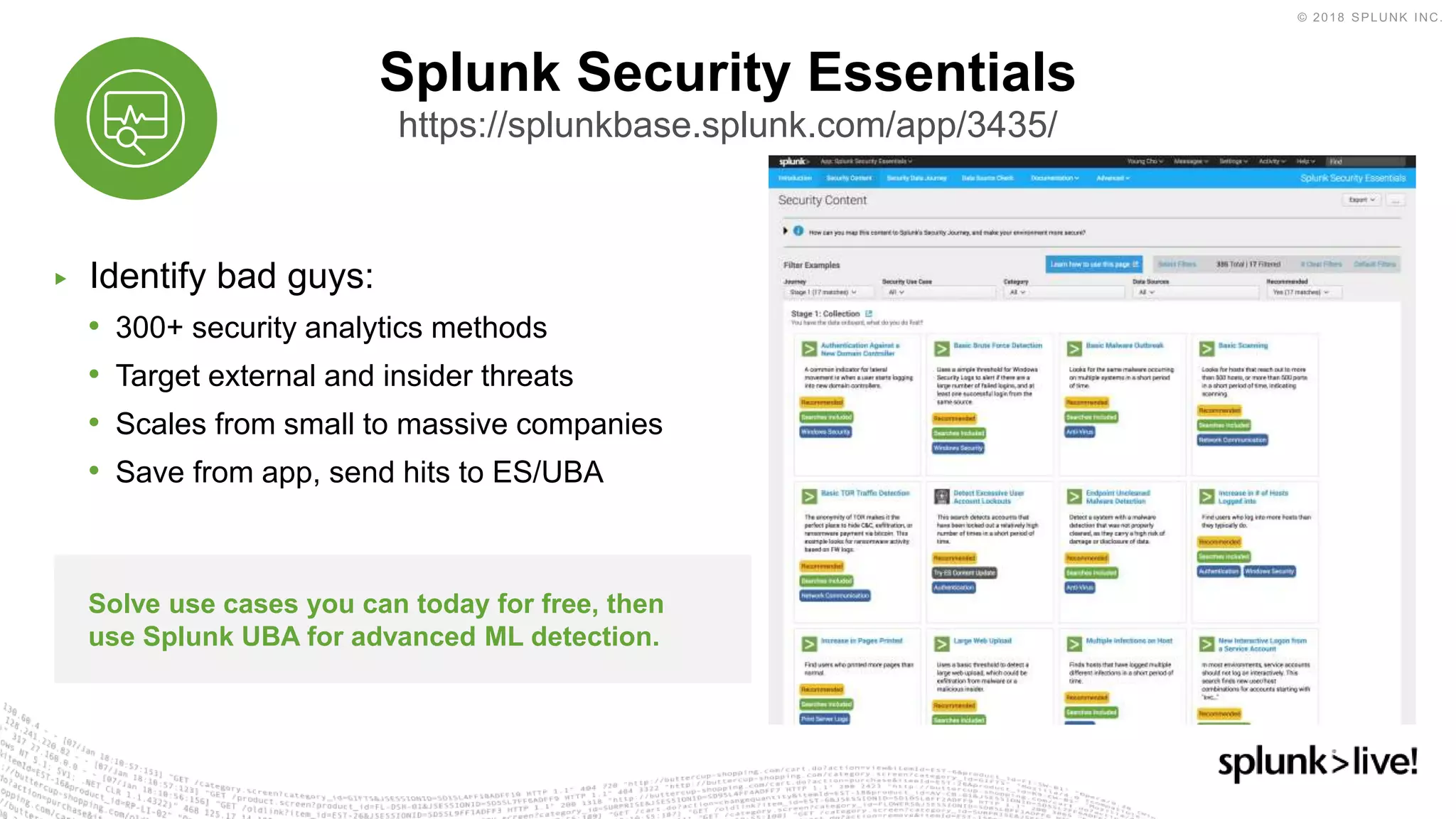
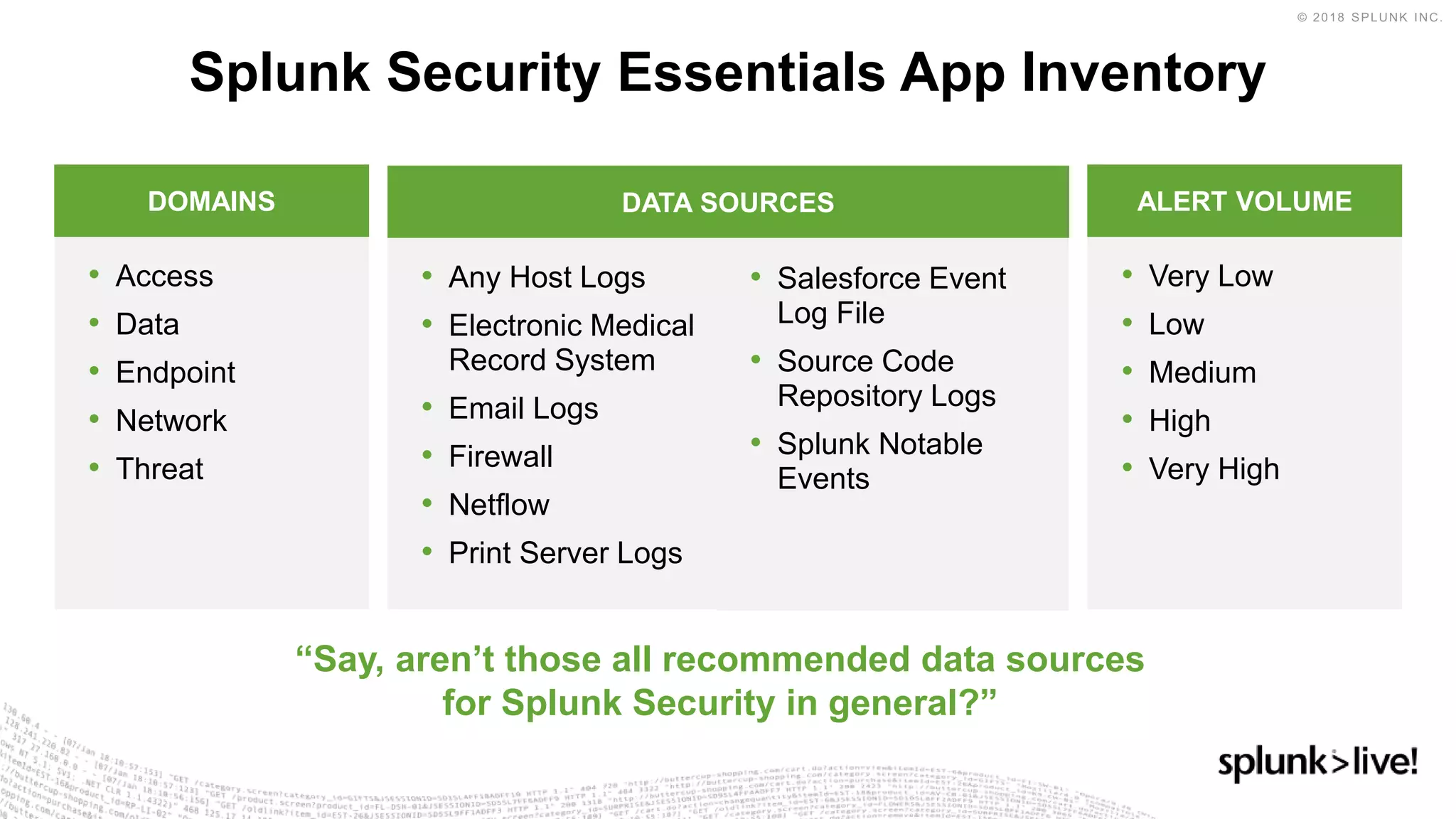
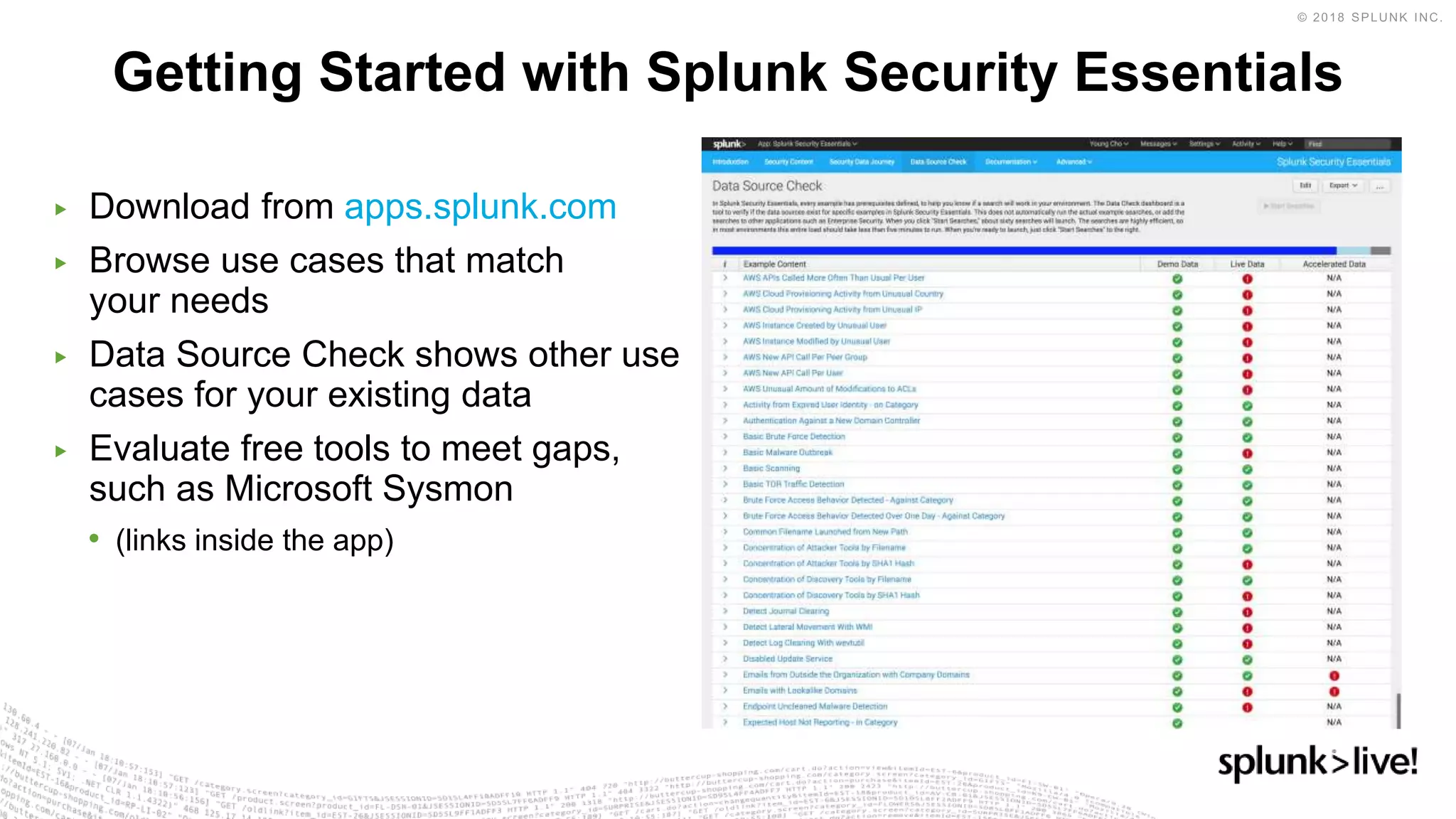
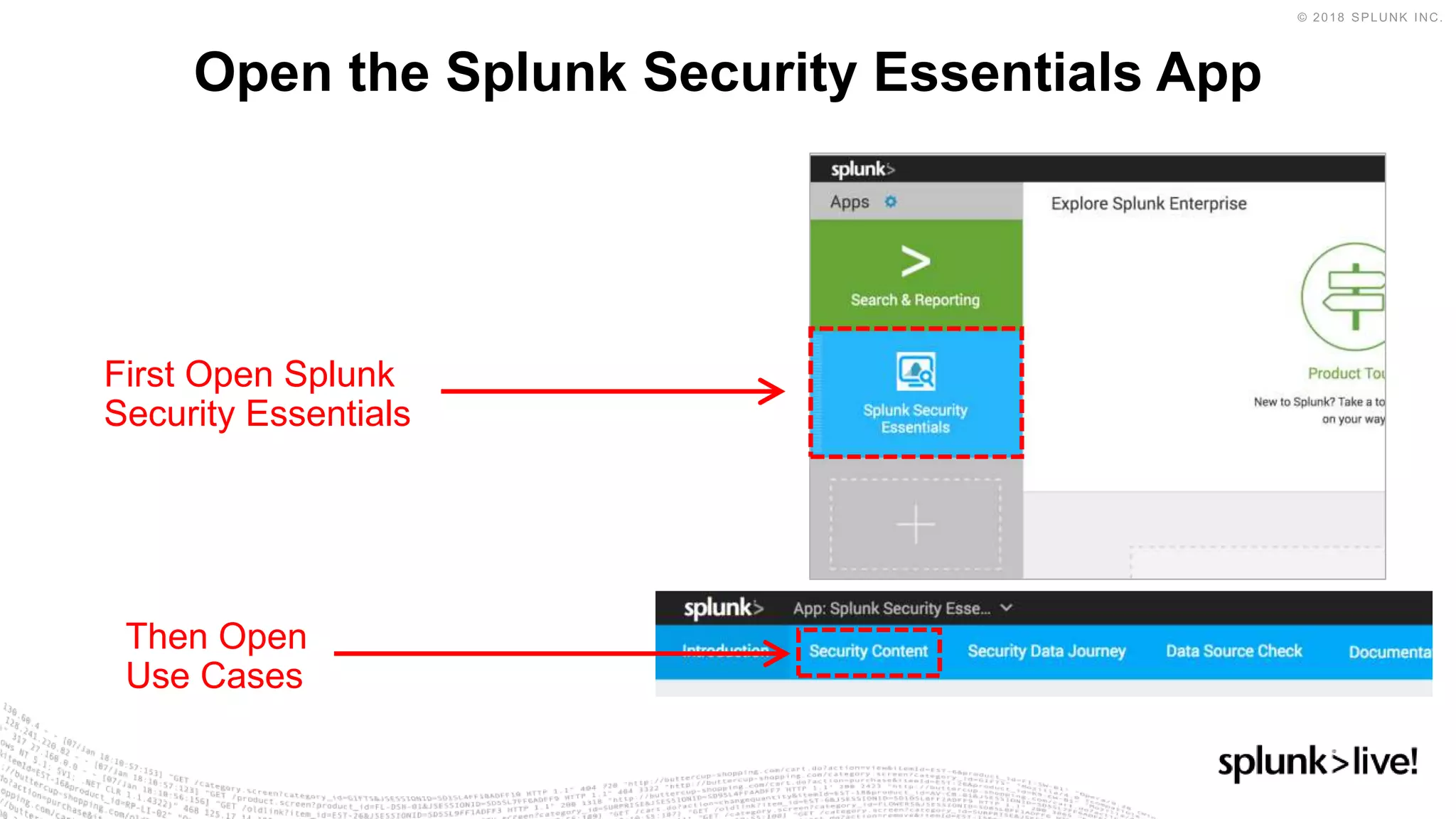
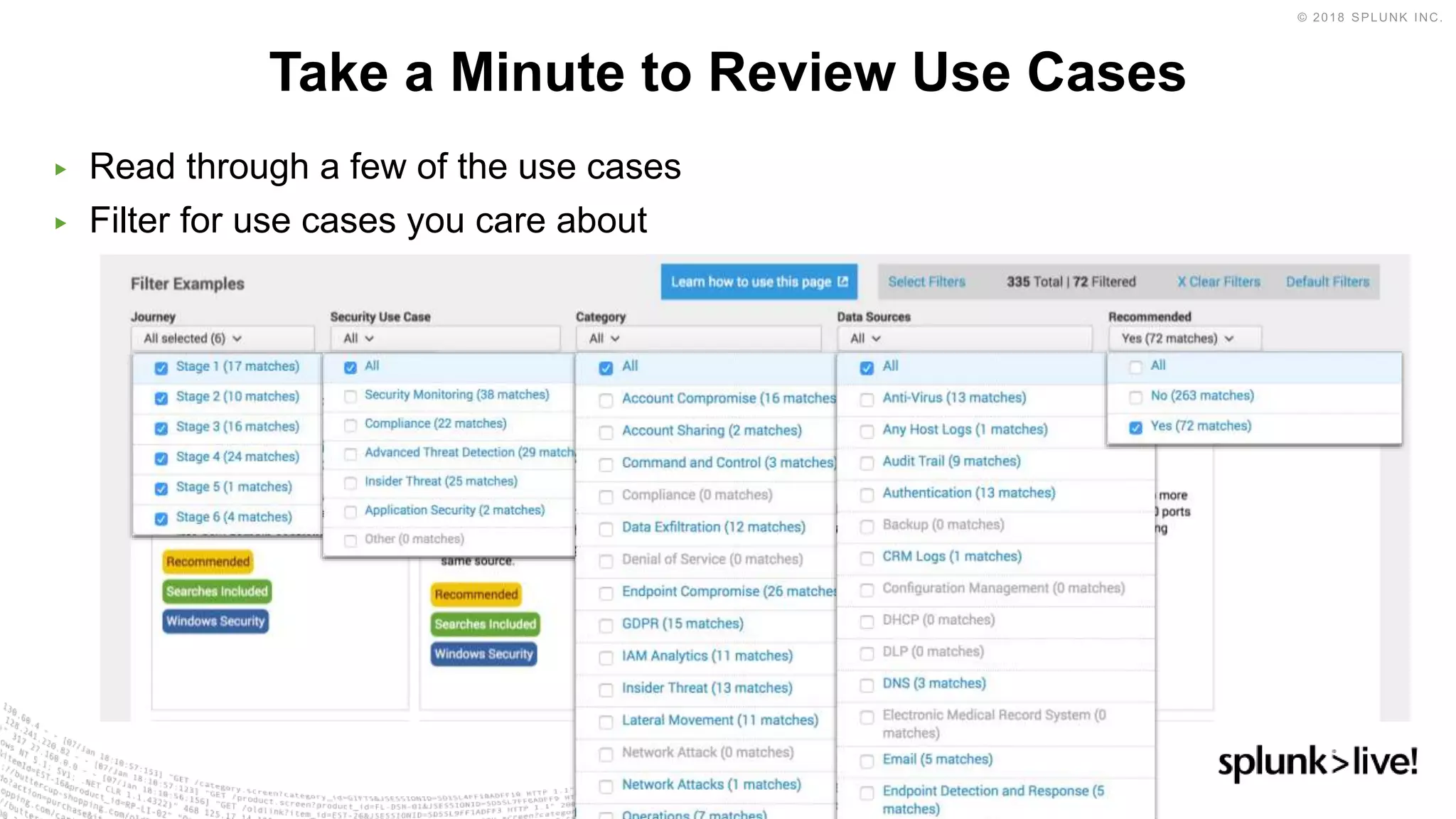
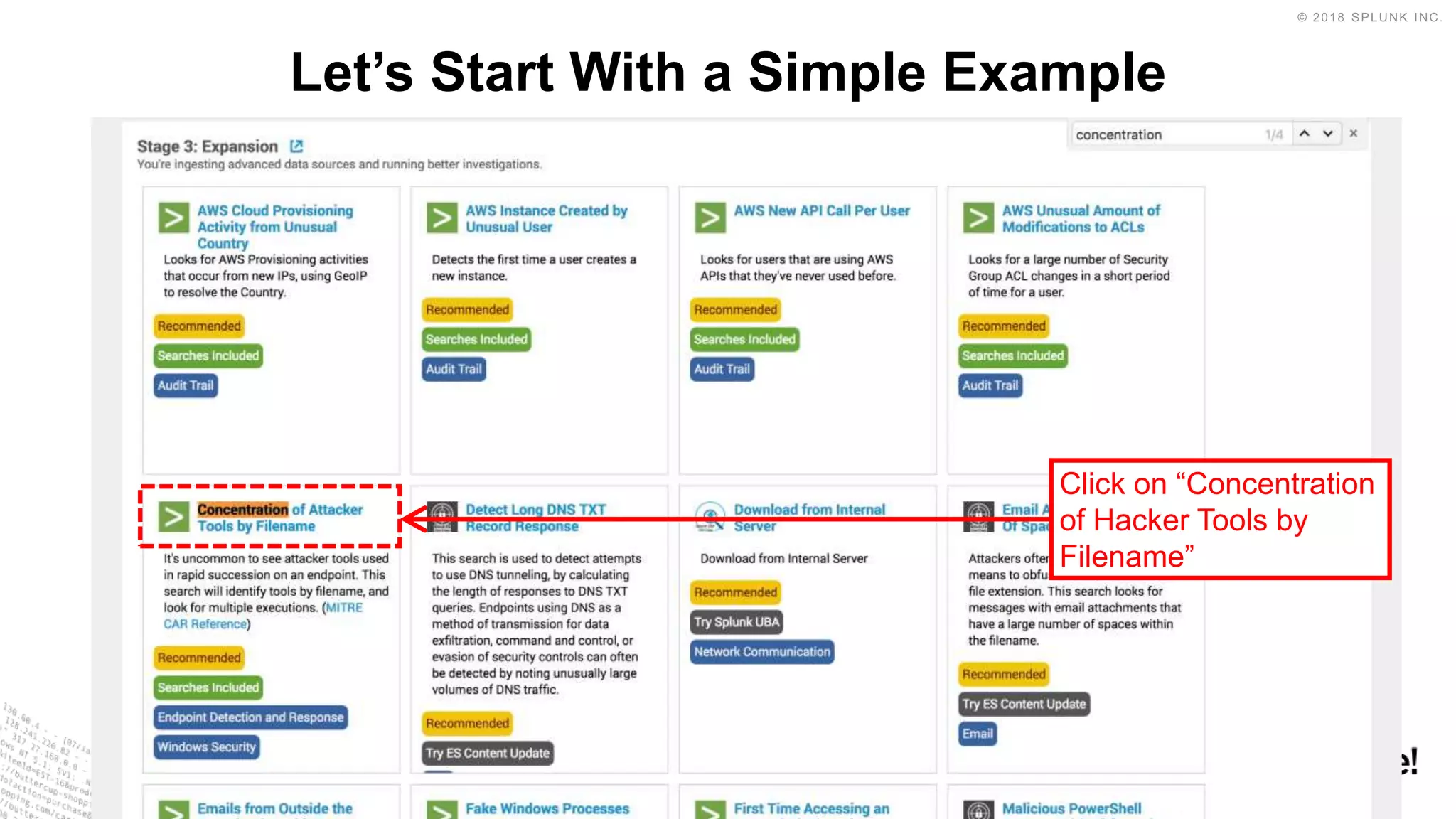
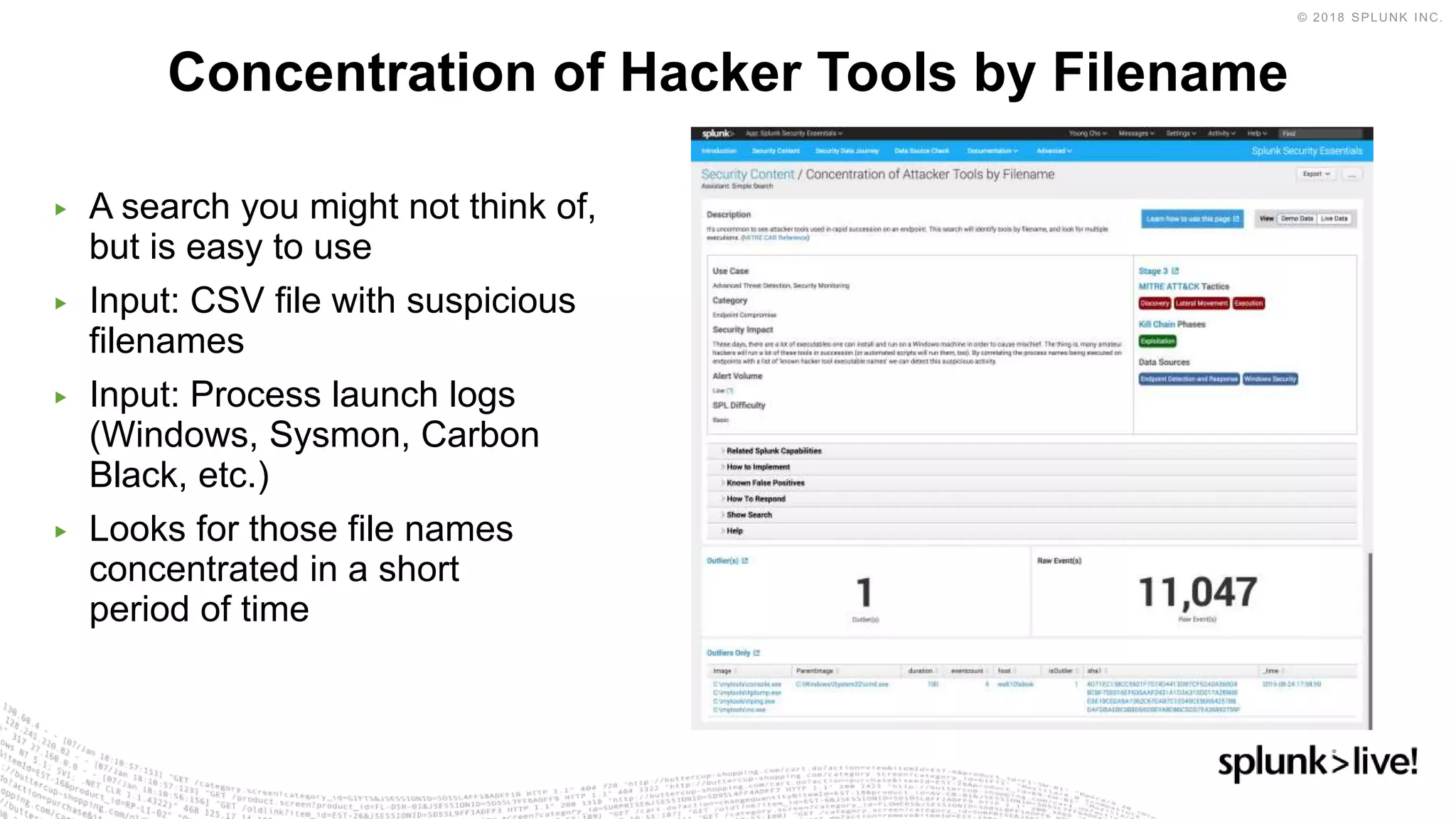
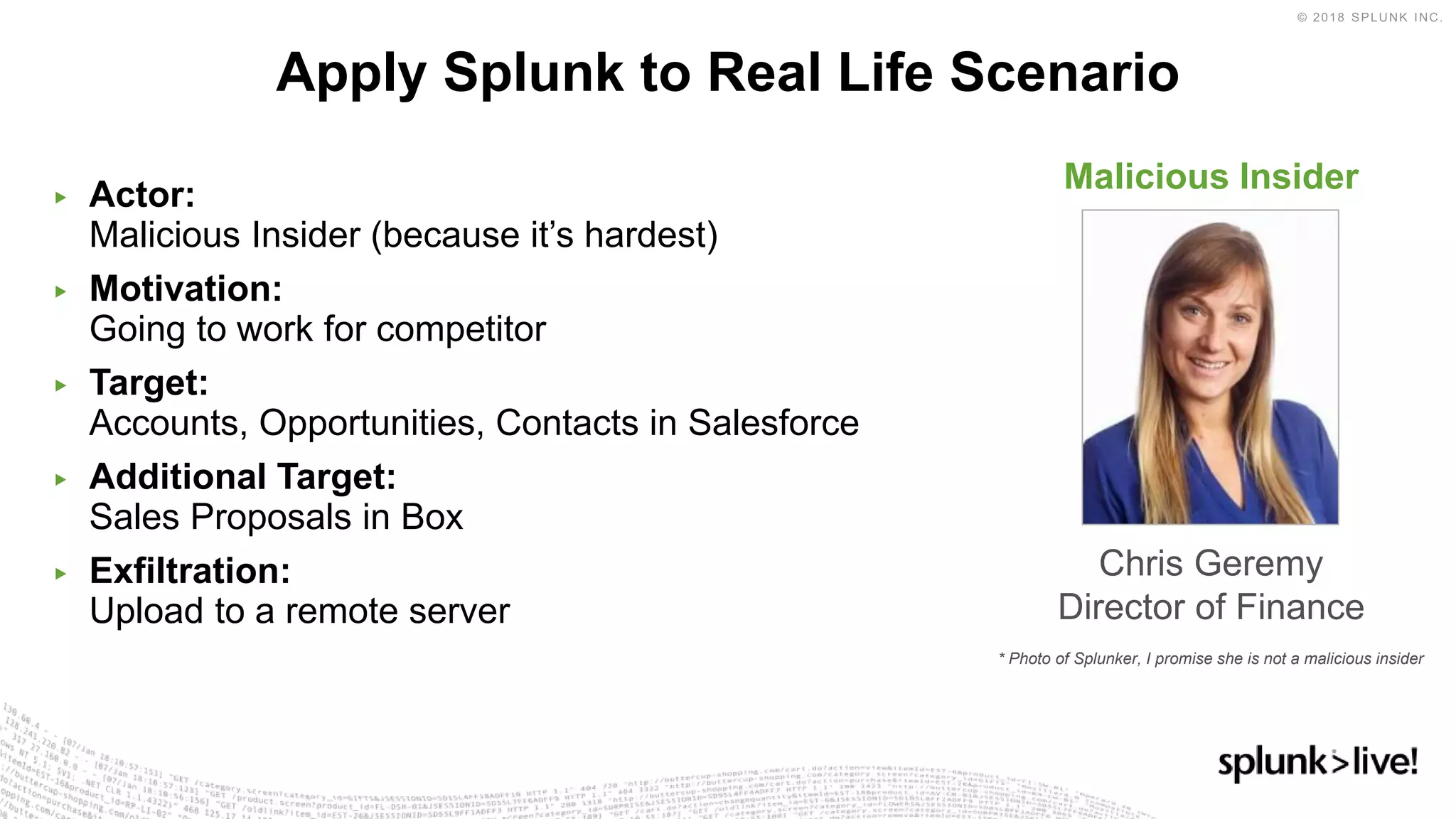
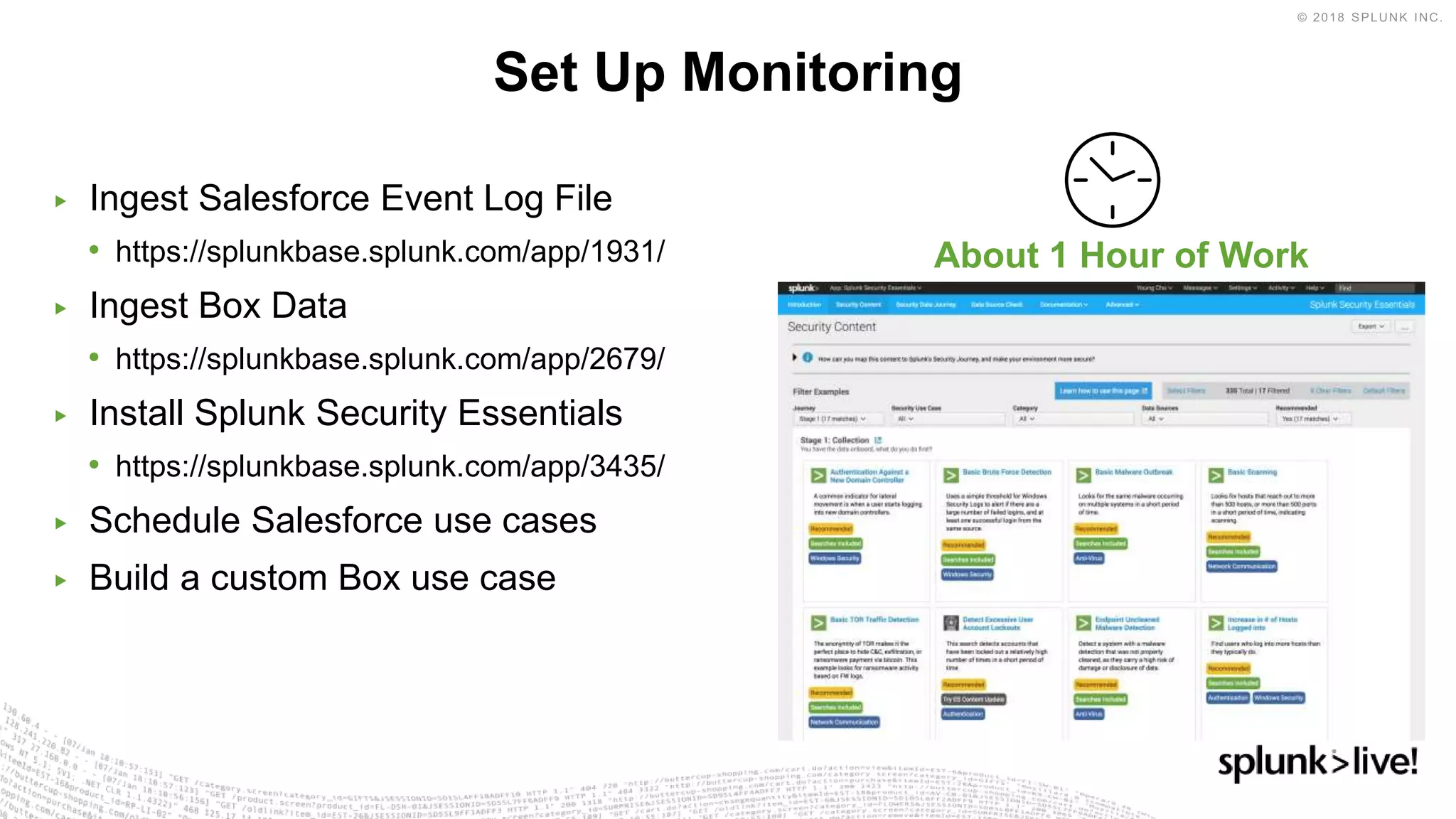
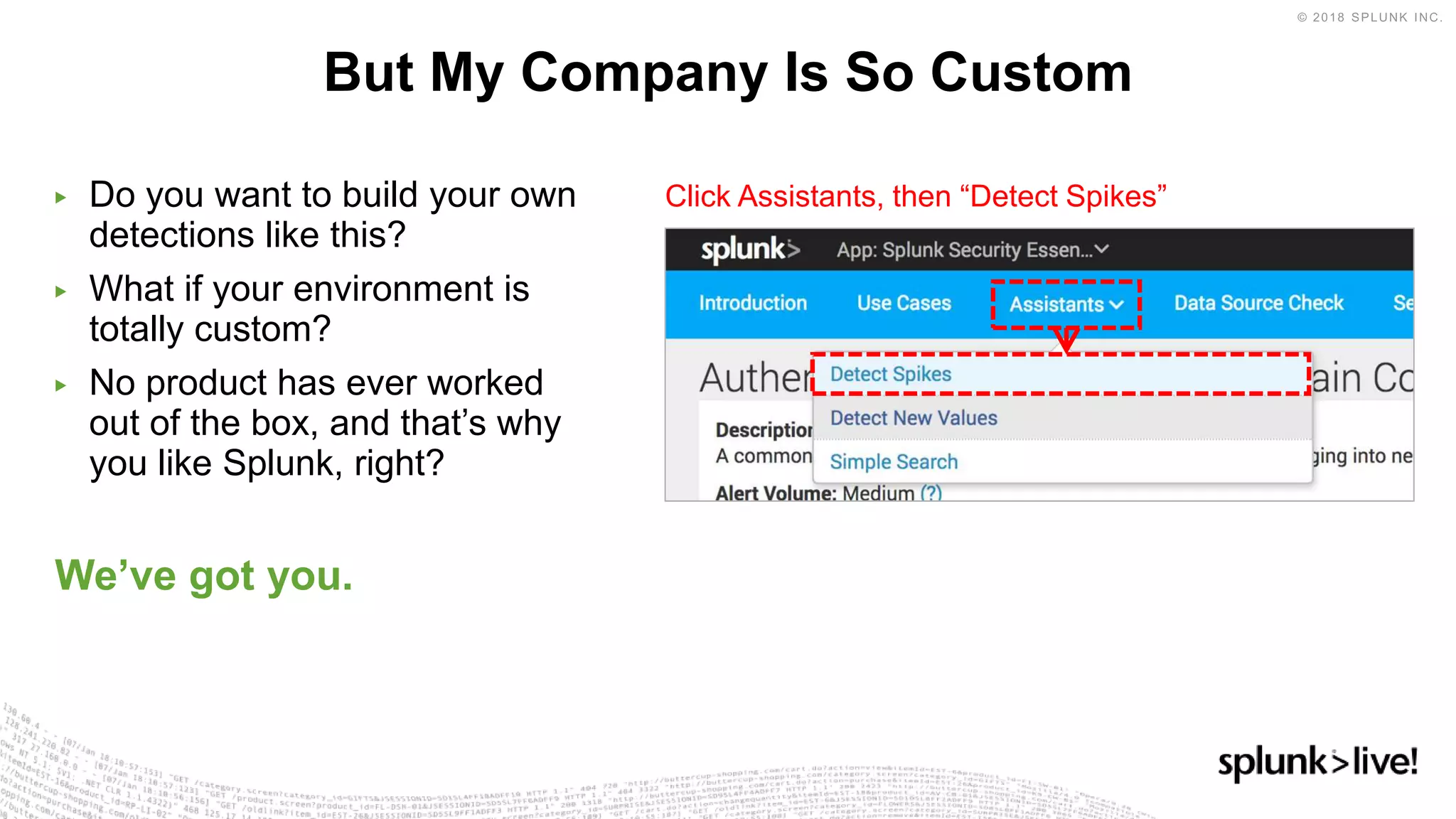
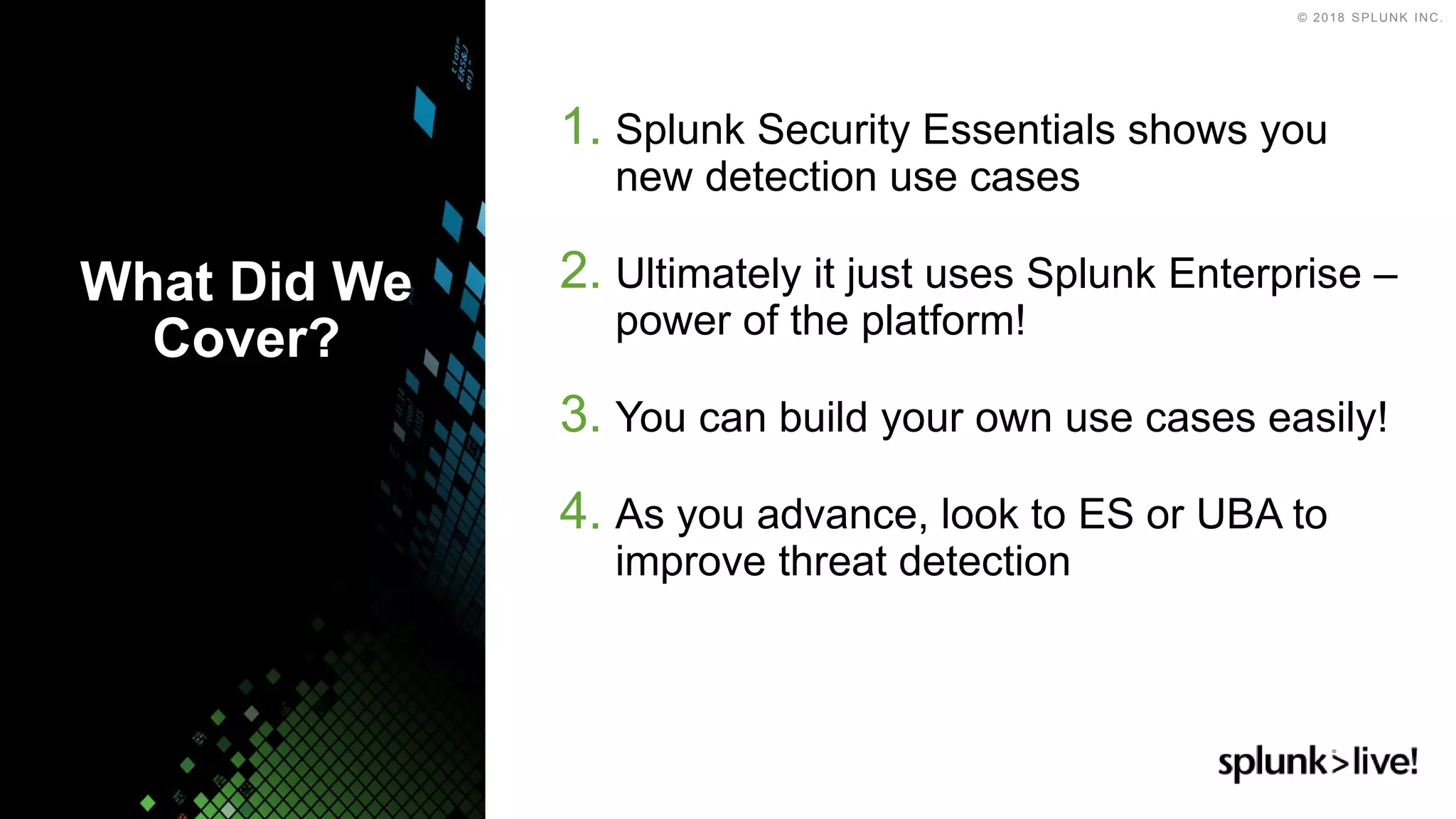
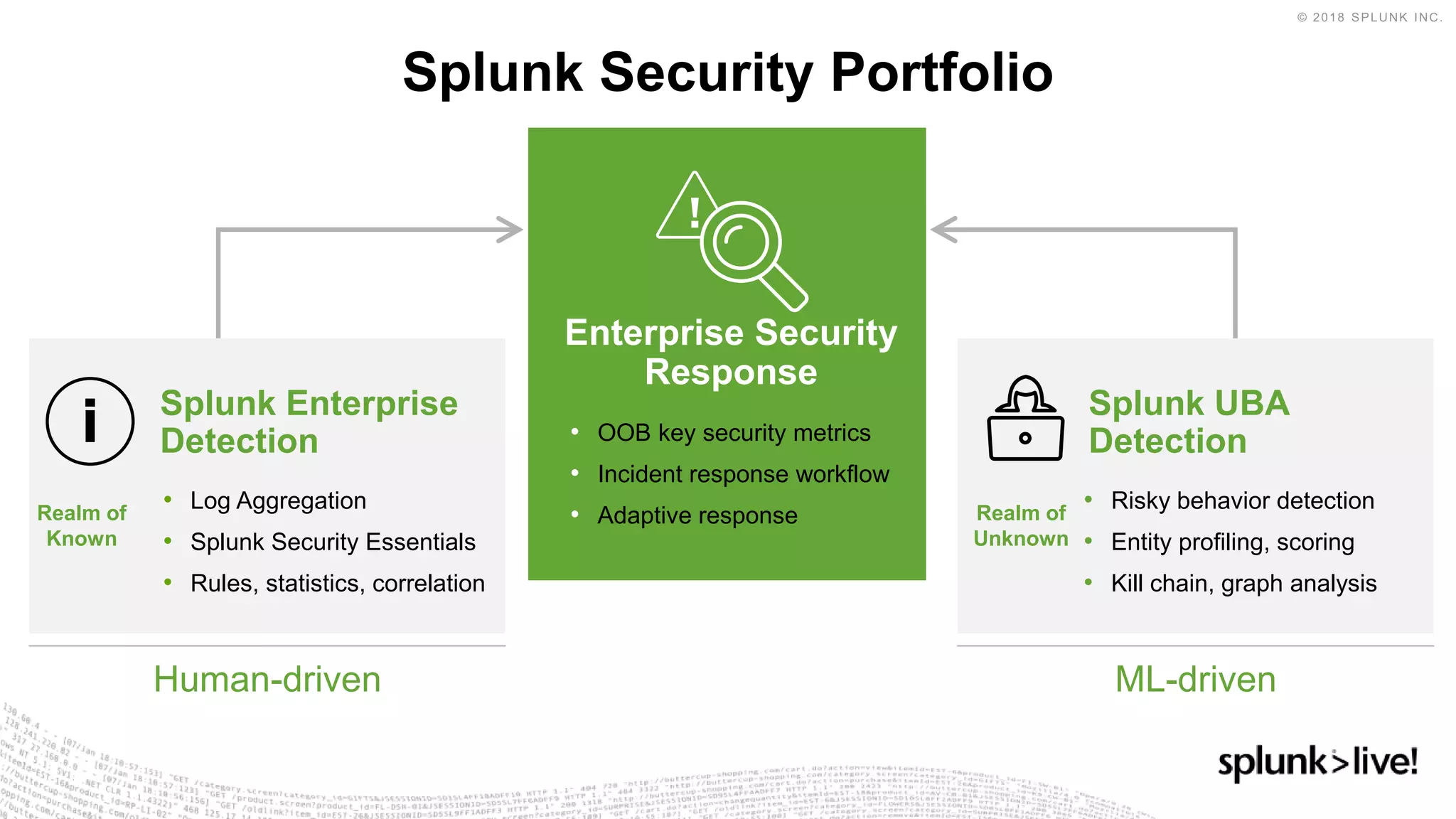
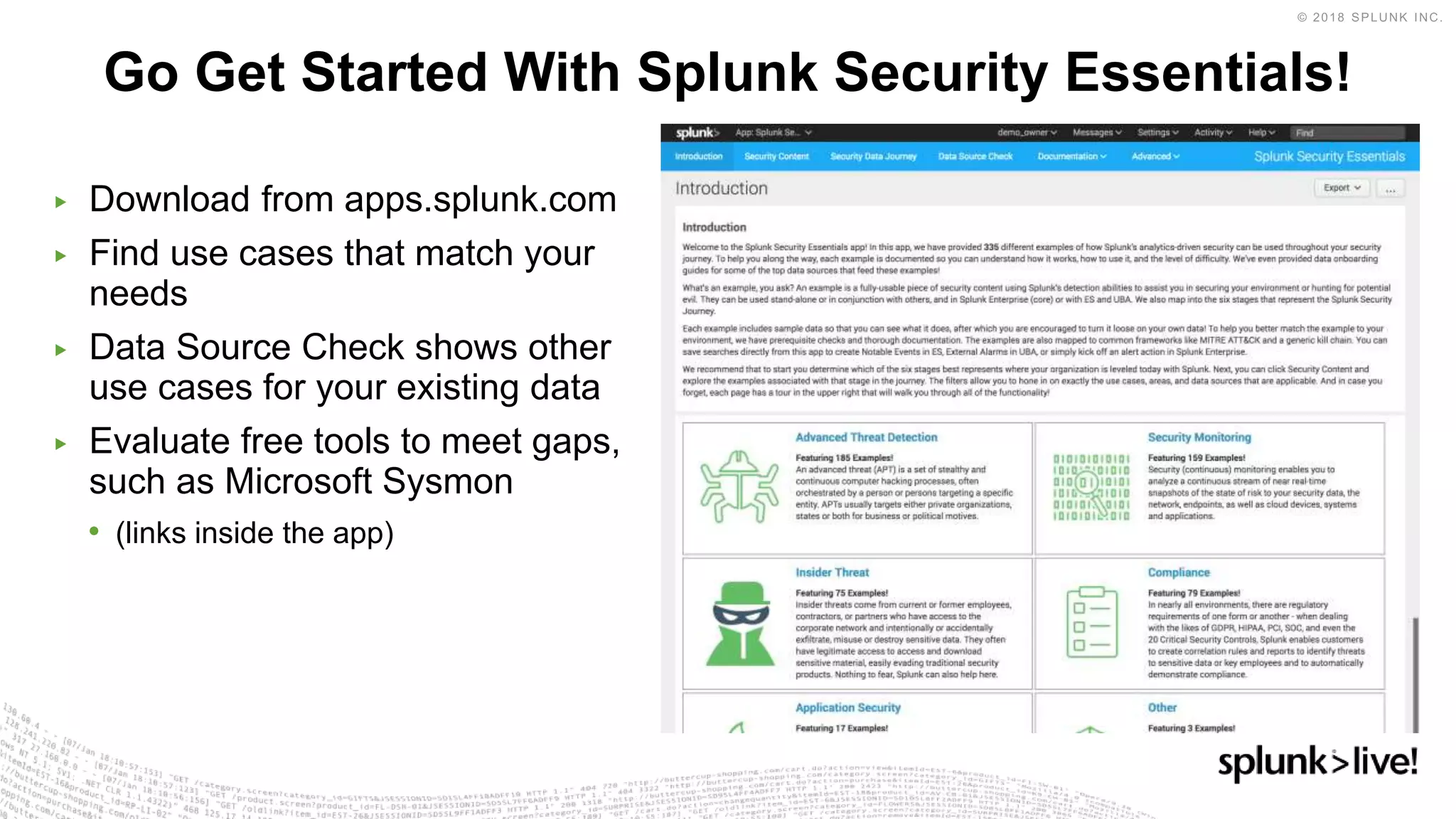
Splunk Security Essentials provides concise summaries in 3 sentences or less that provide the high level and essential information from the document. The document discusses an introductory presentation on security analytics methods. It includes an agenda that covers an introduction to analytics methods, an example scenario, and next steps. It also discusses common security challenges, different analytics methods and types of use cases, and how analytics can be applied to different stages of an attack.