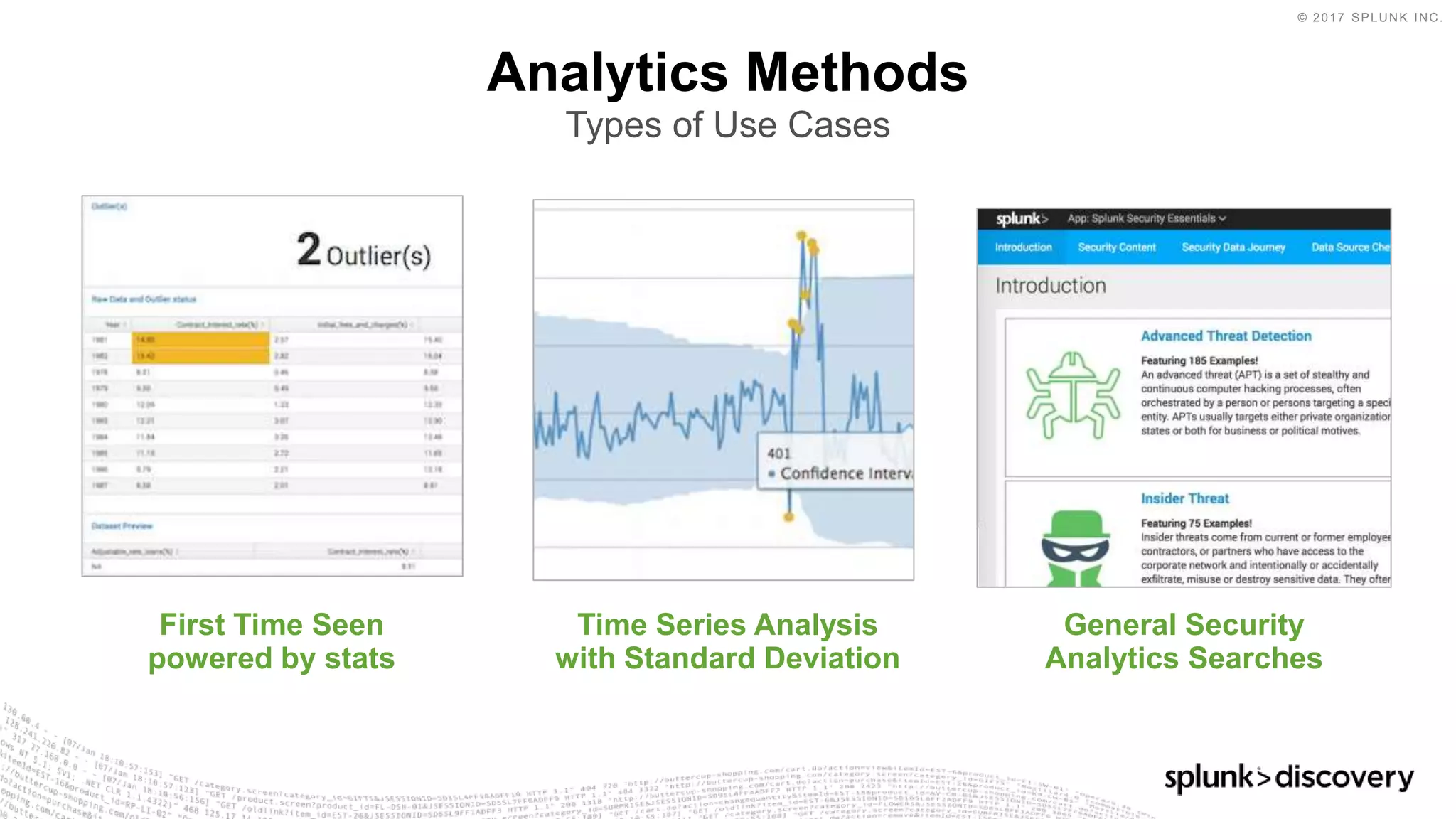
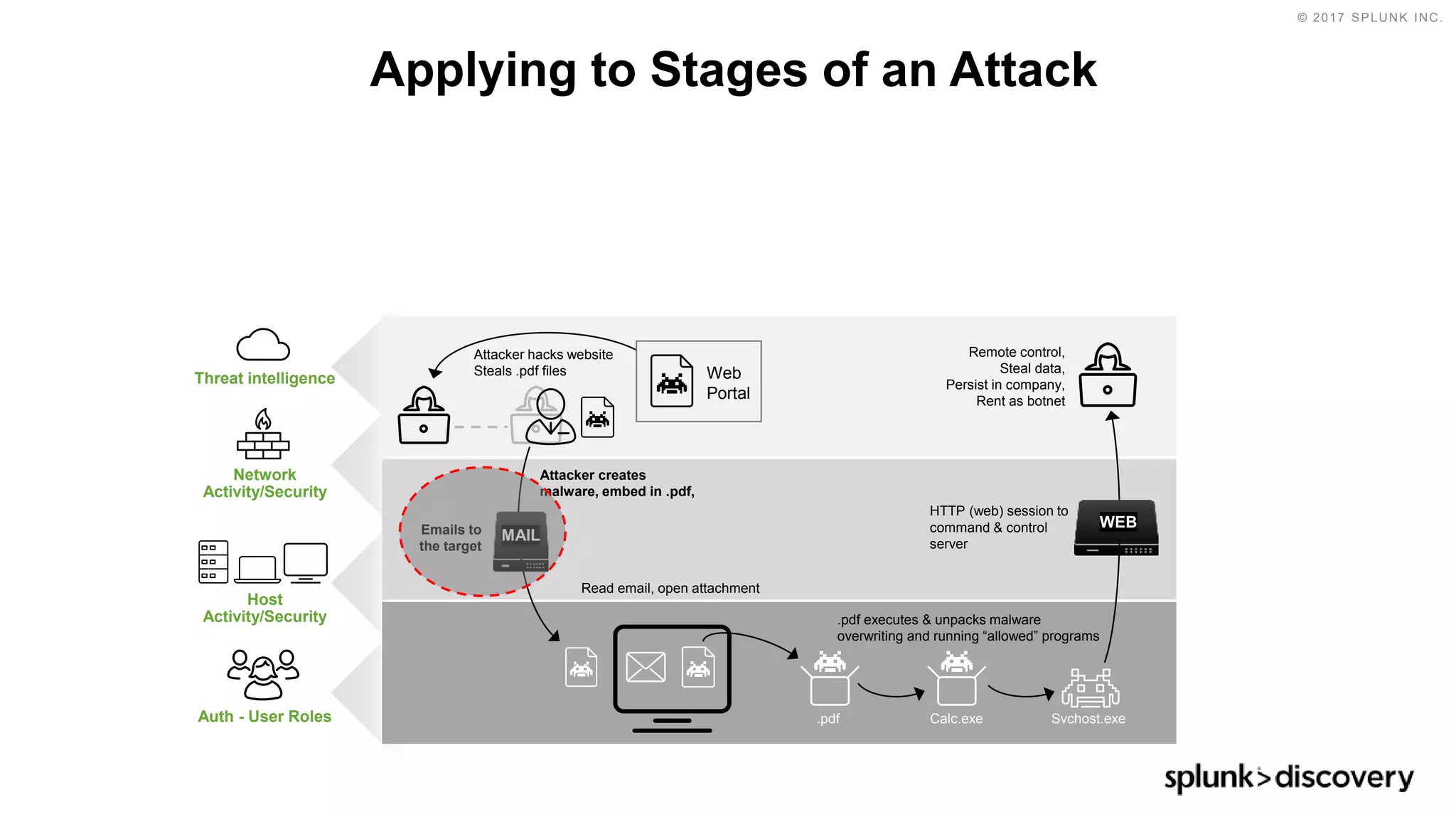
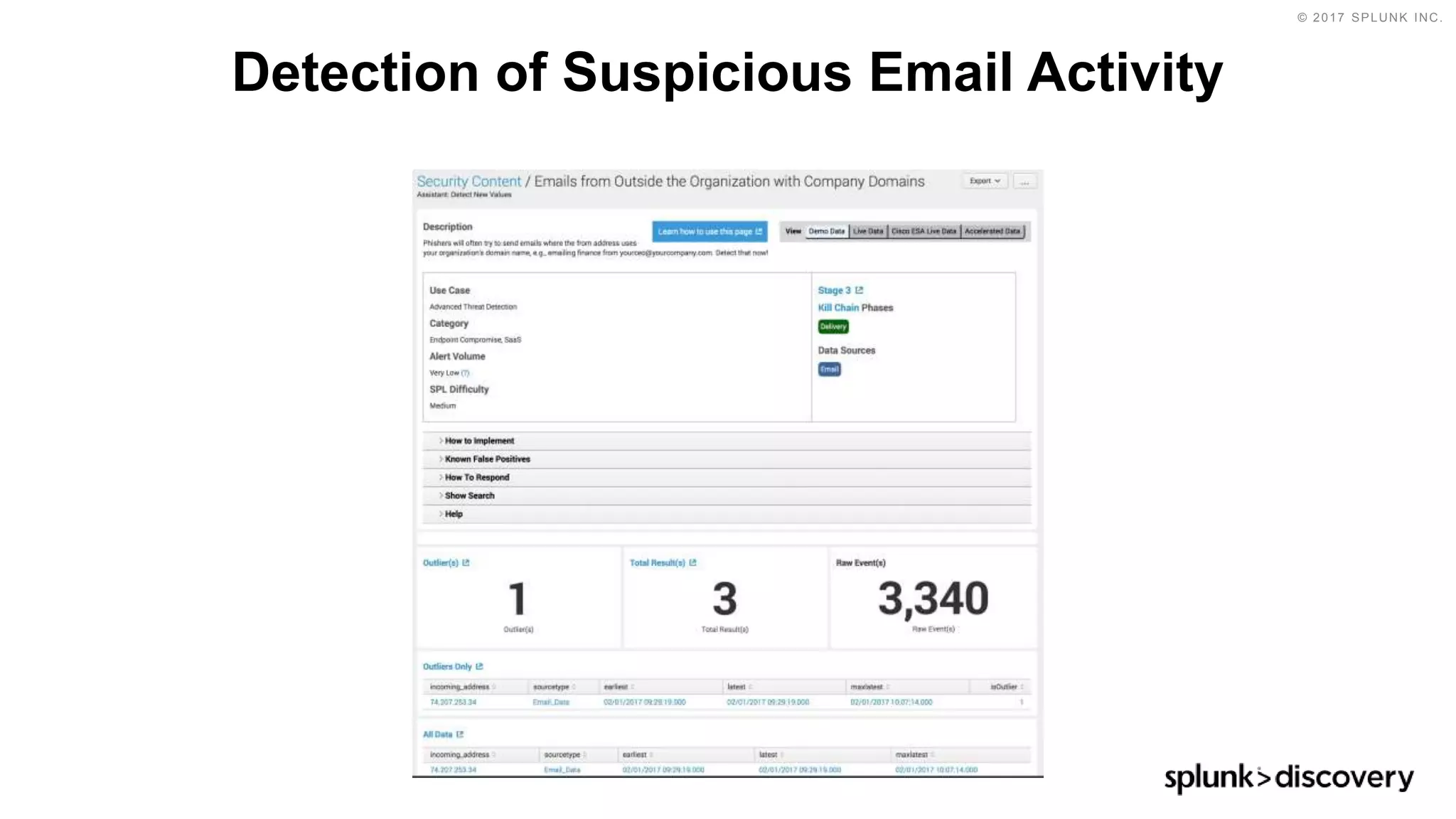
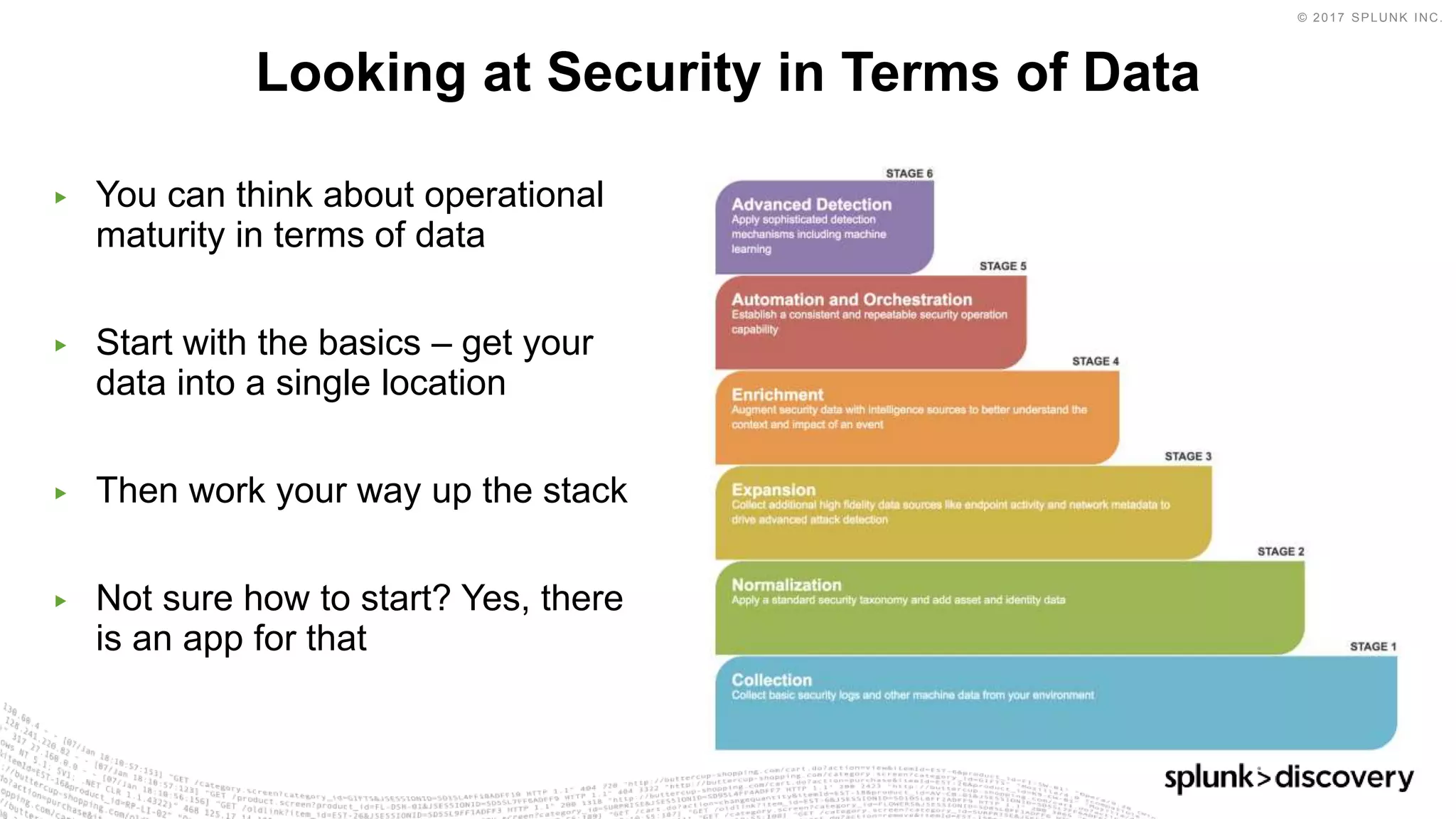
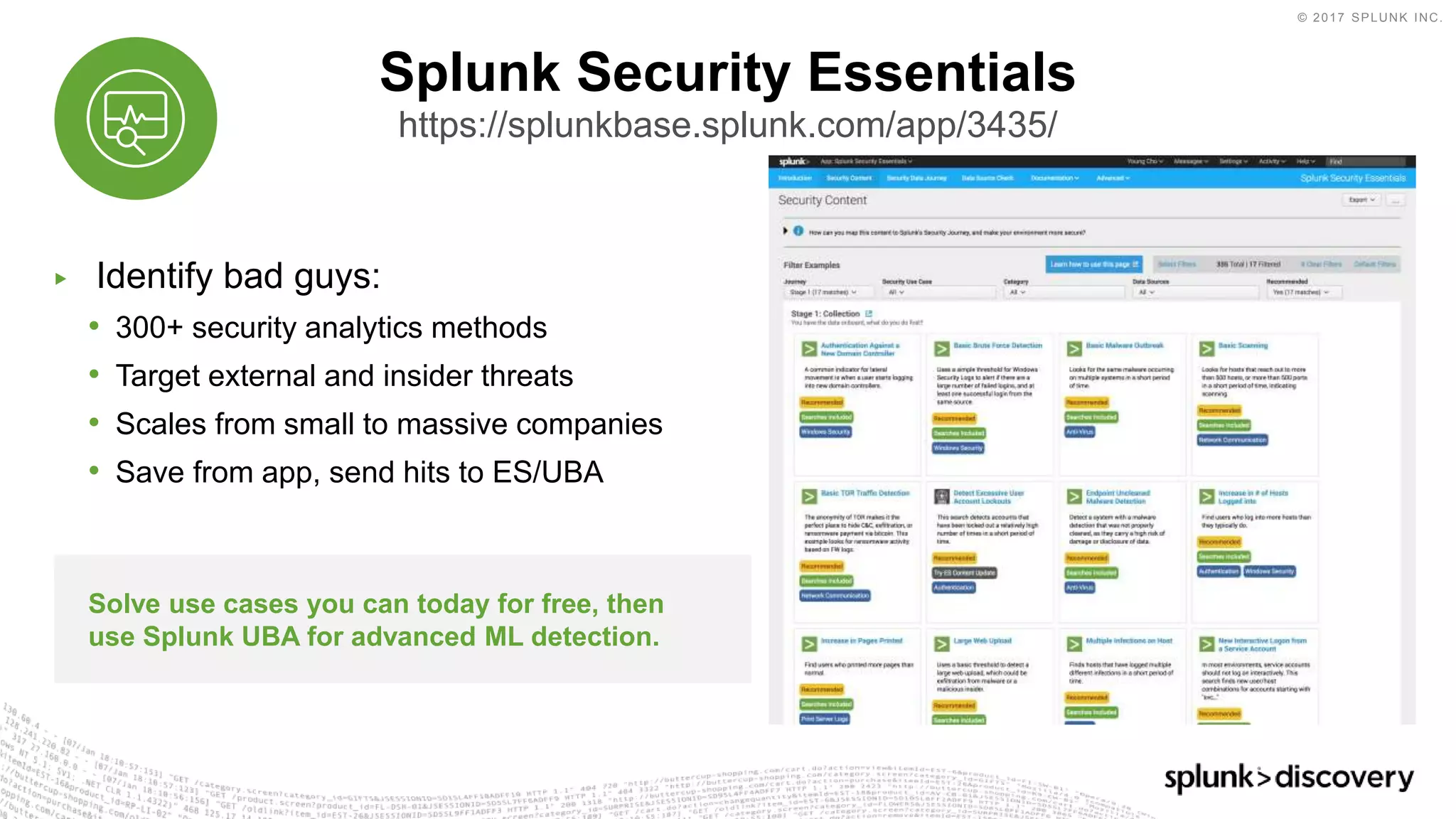
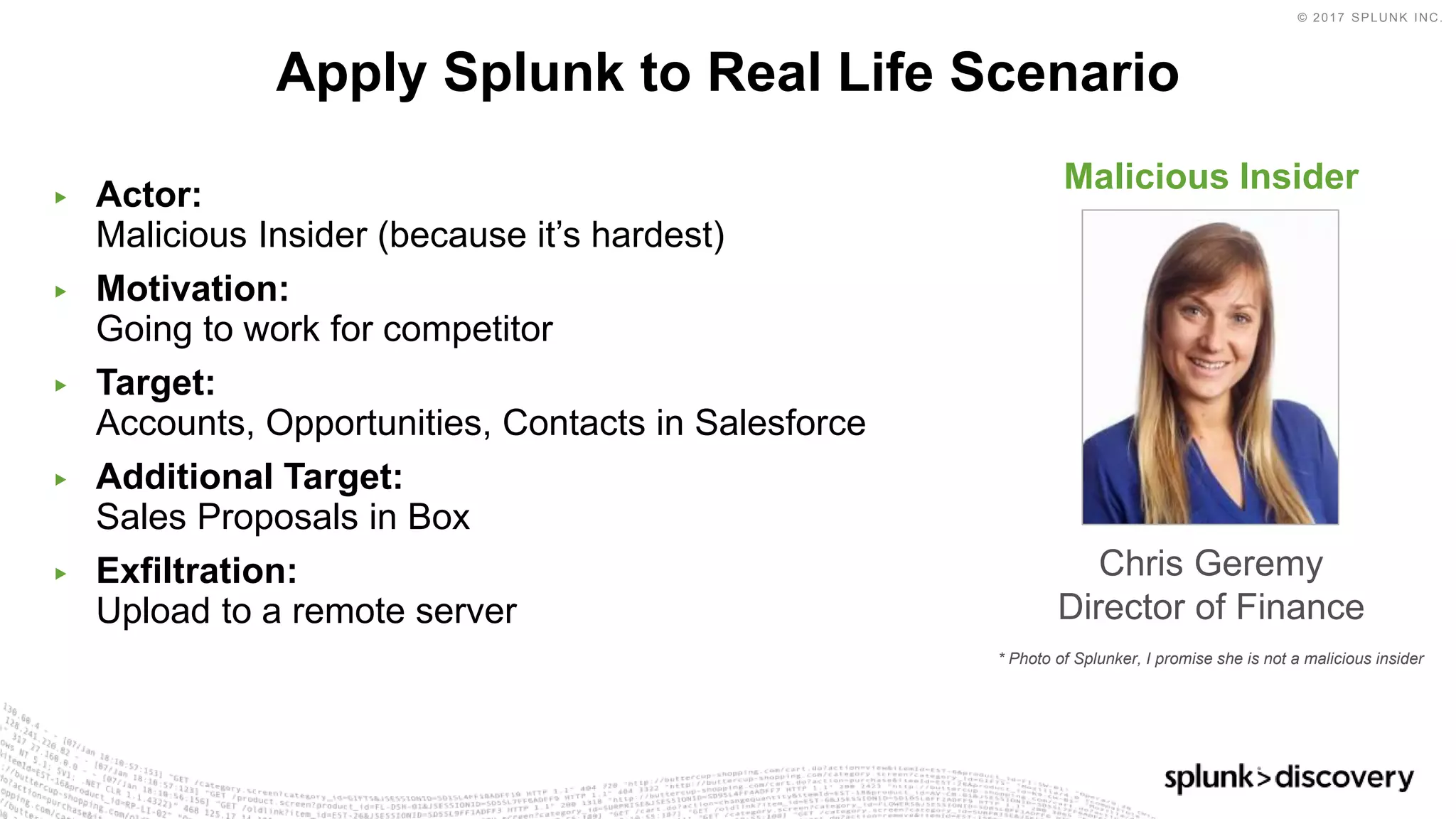
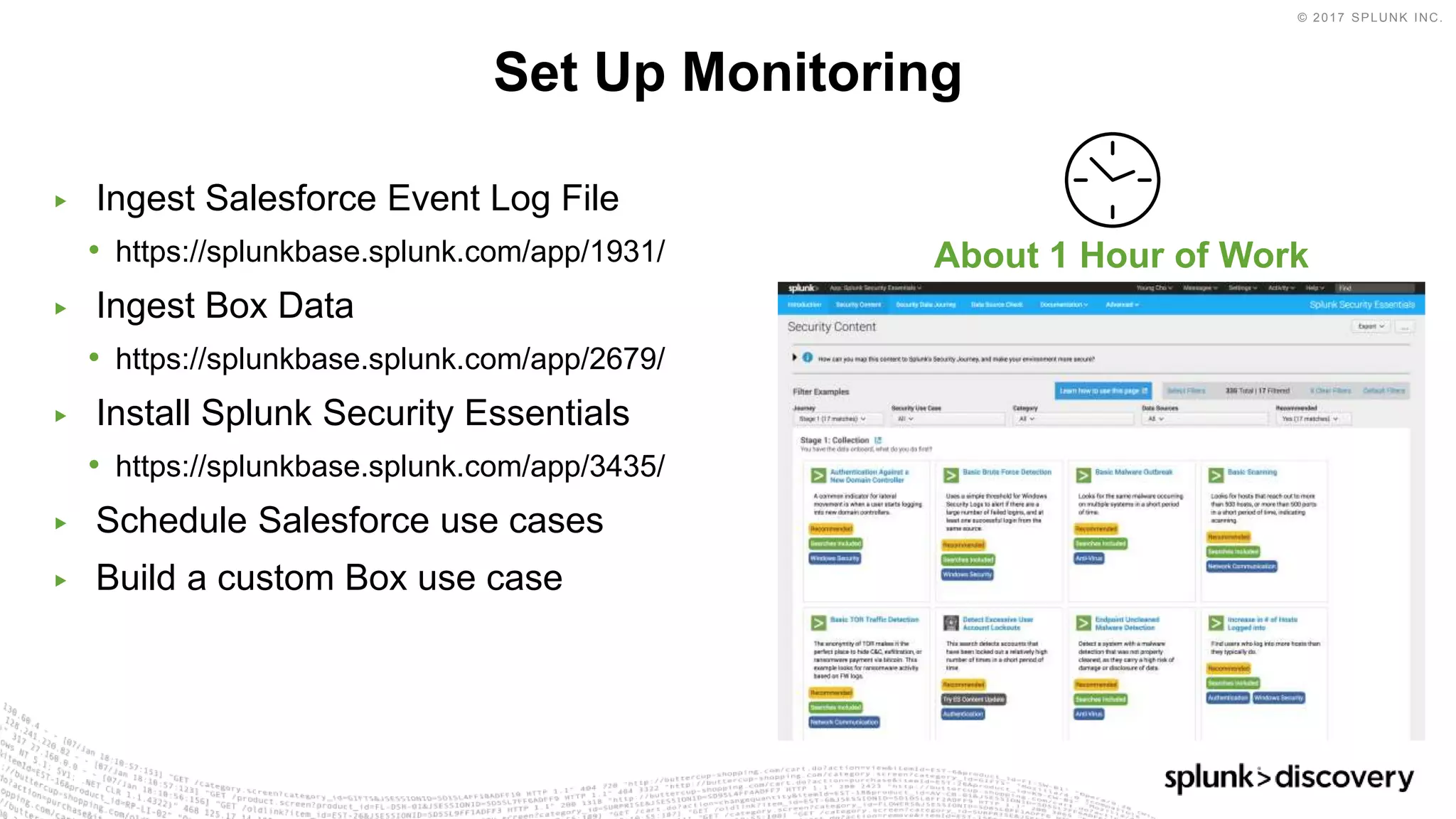
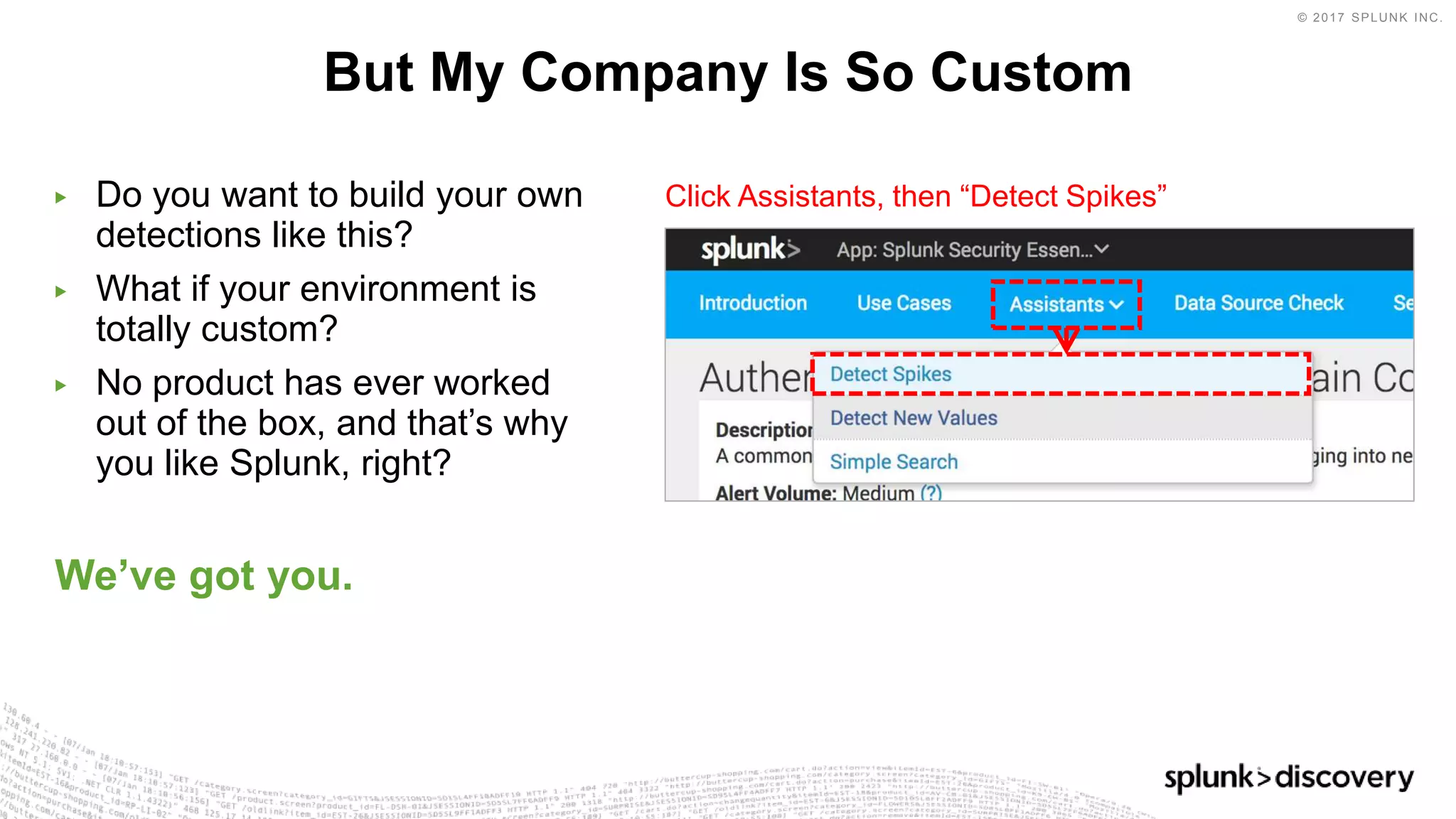
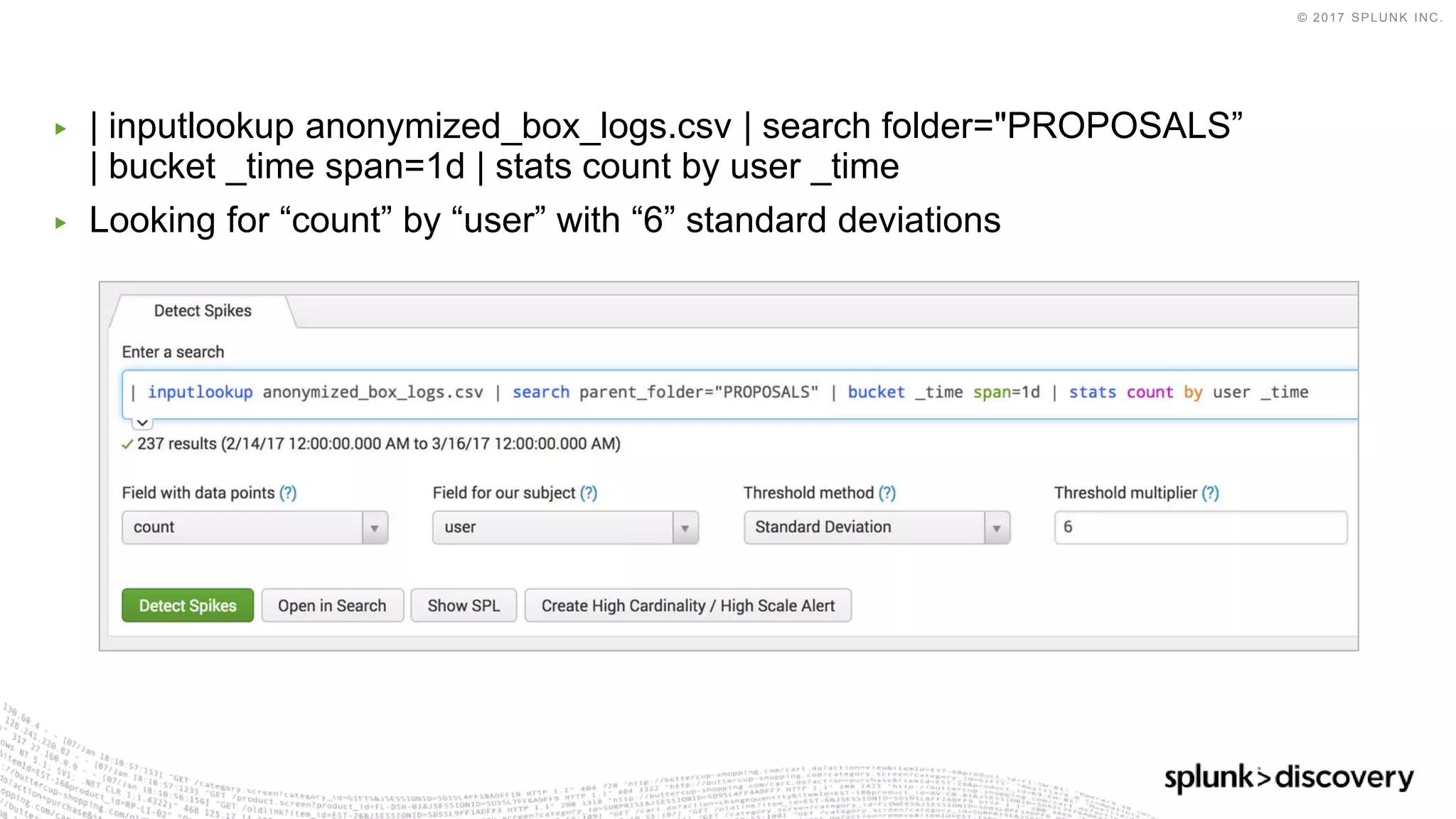
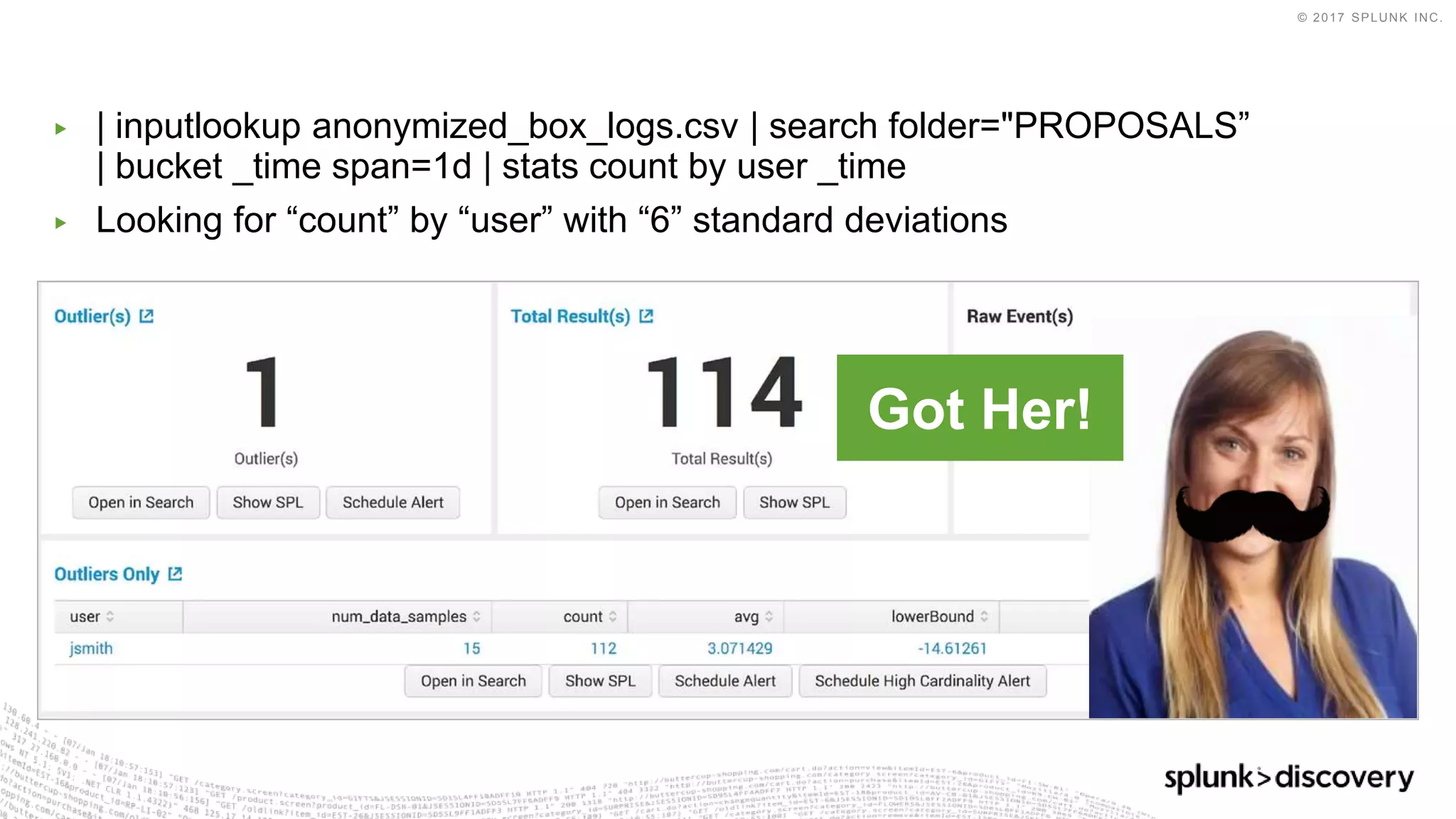
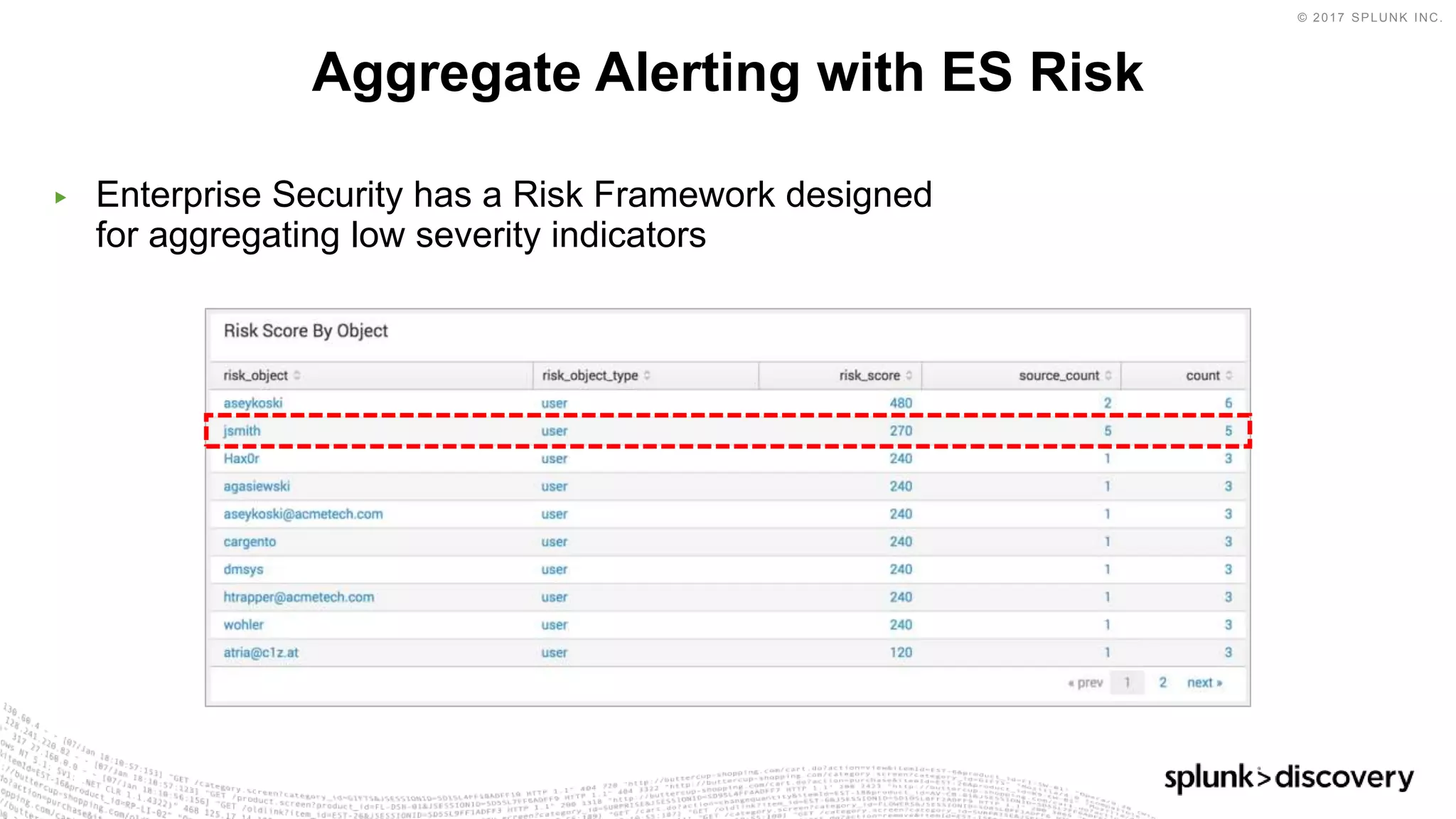
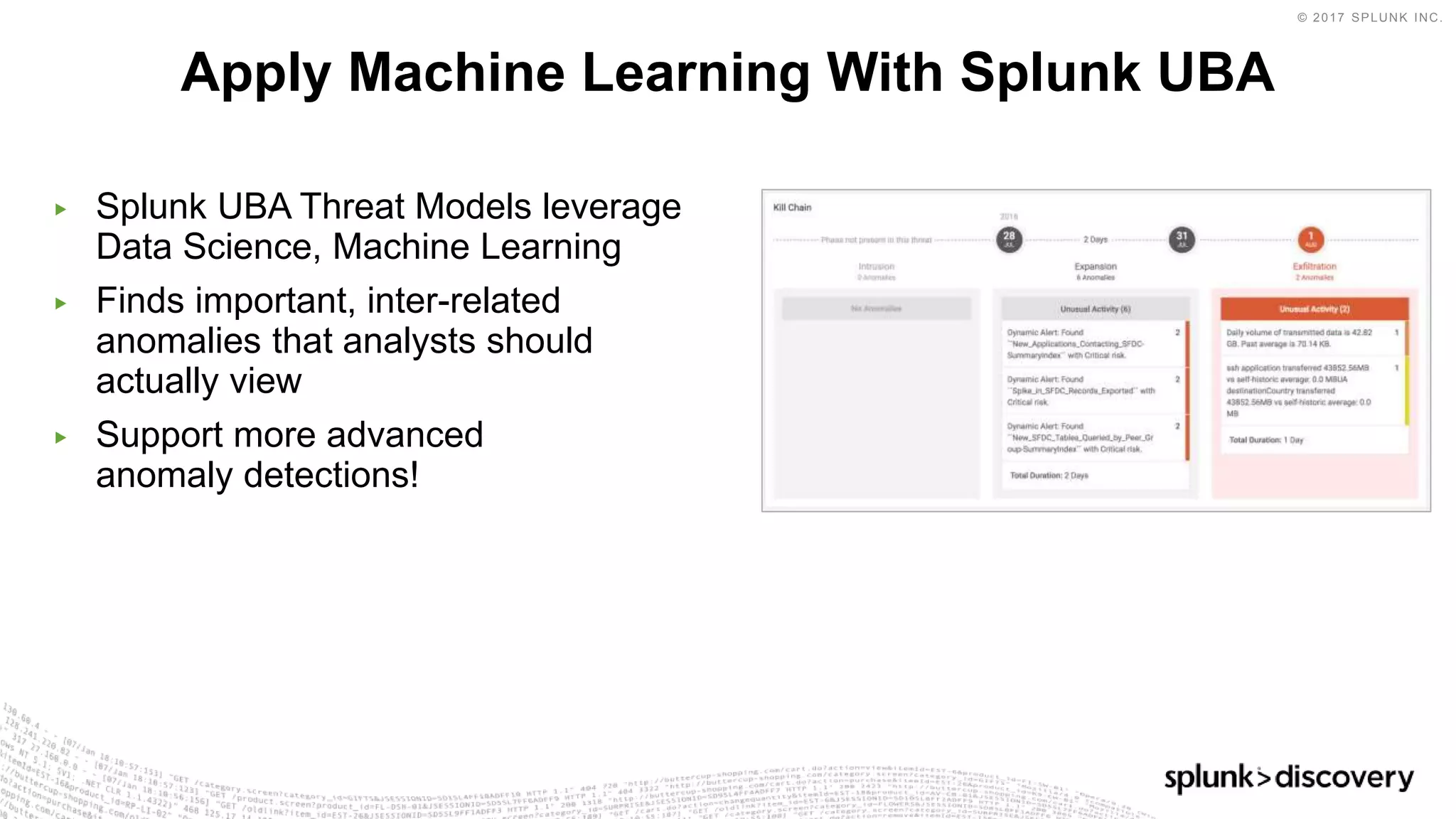
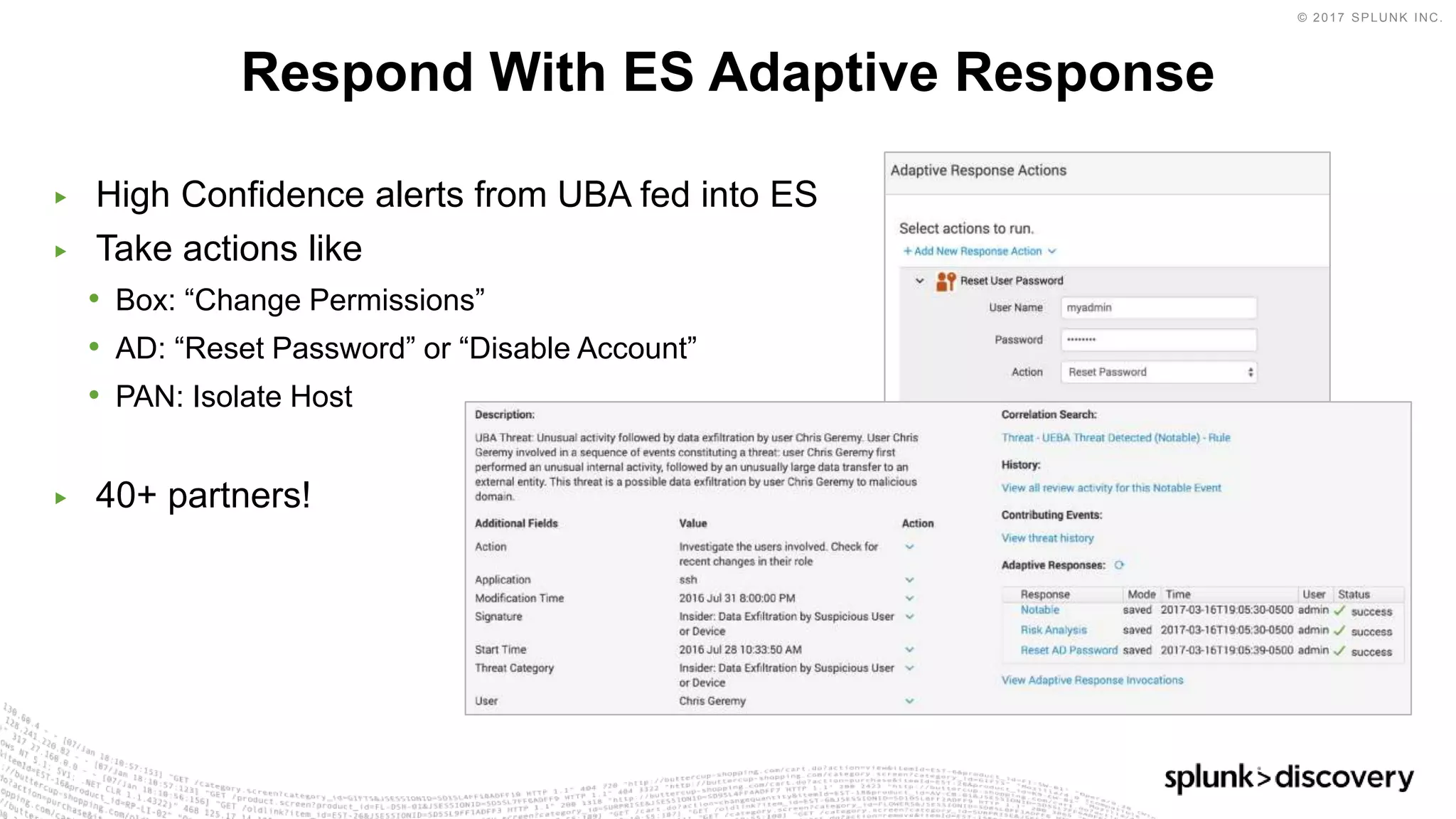
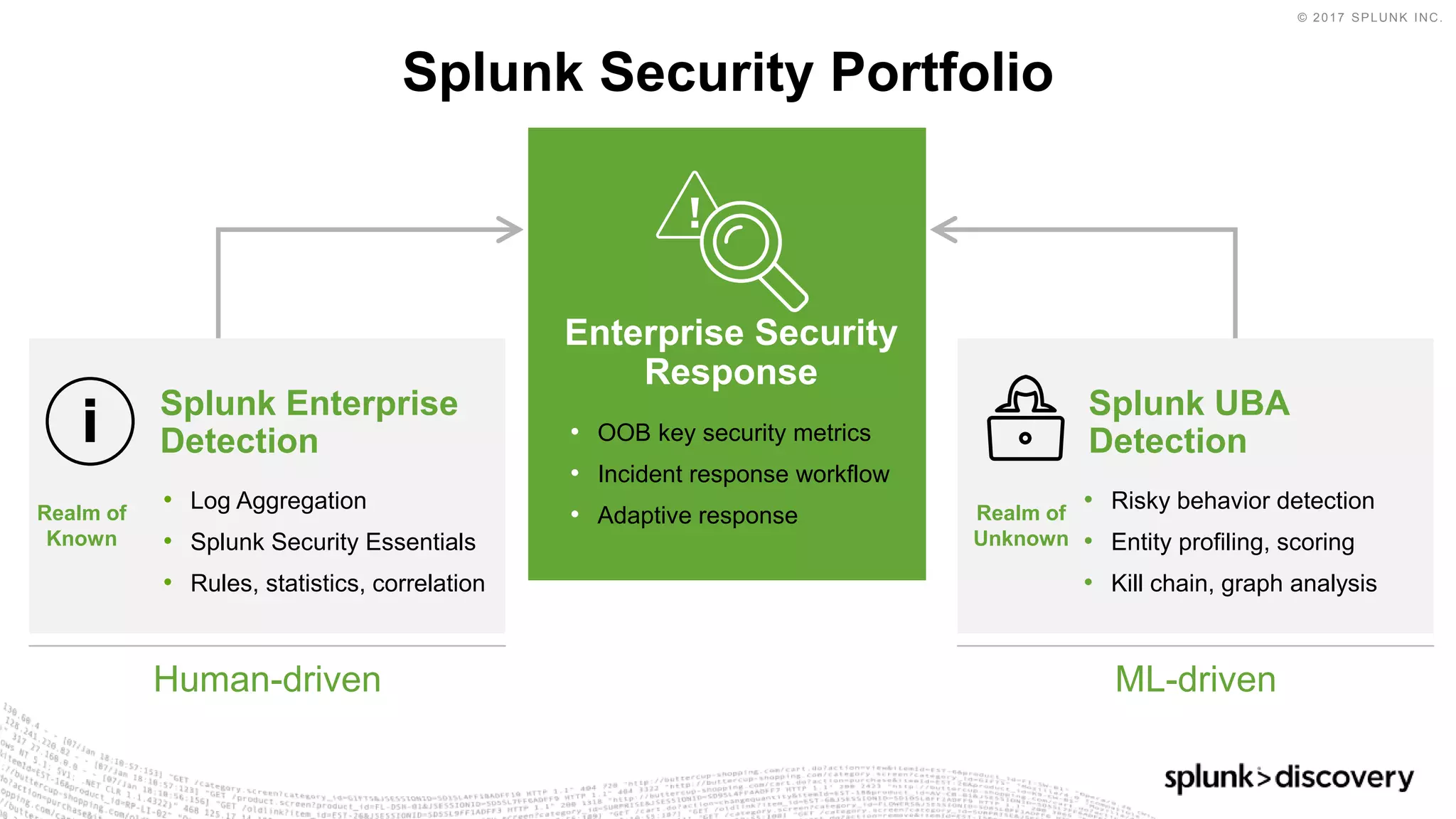
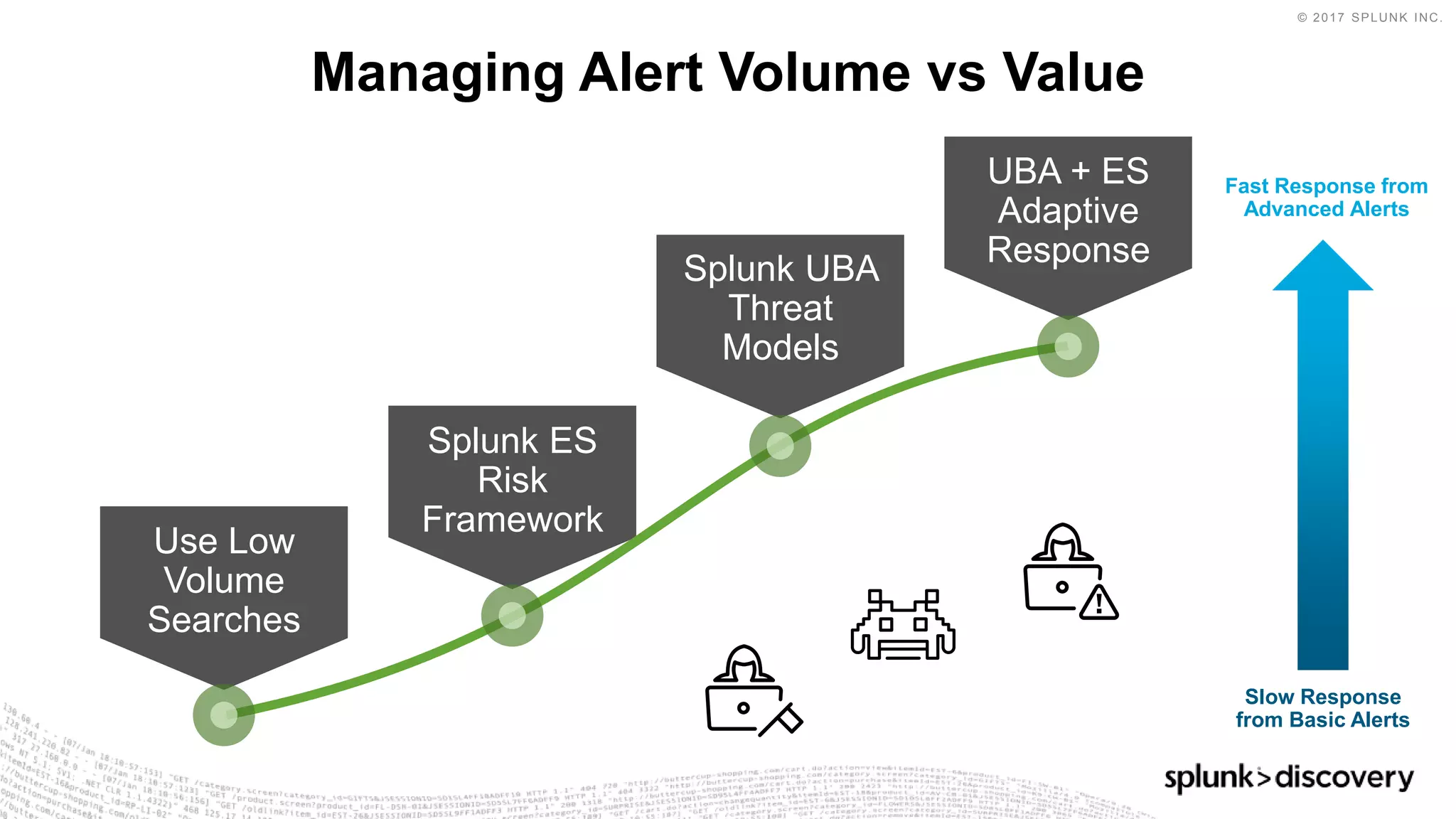
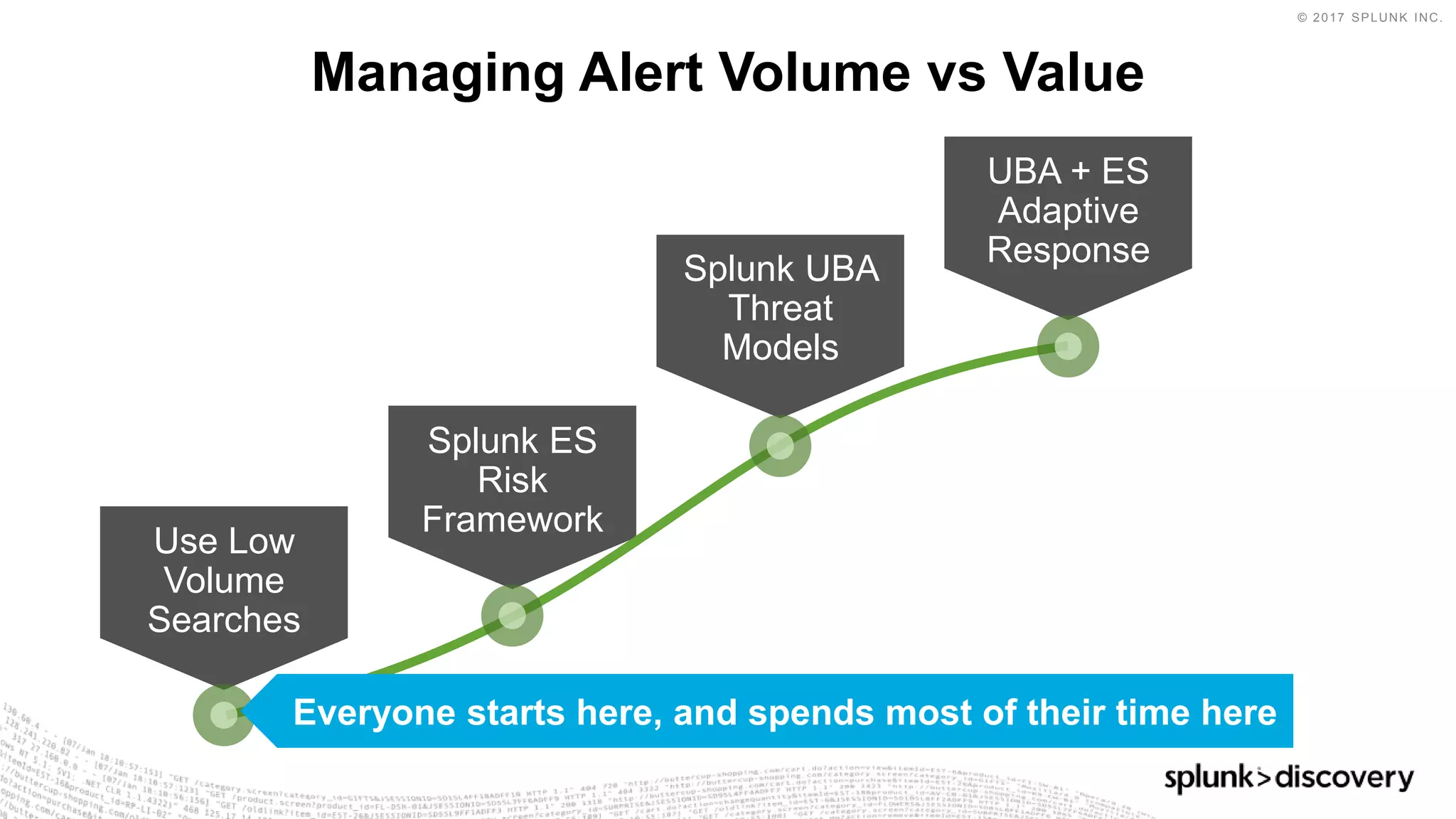
The document discusses security analytics methods for detecting threats using Splunk software. It covers common security challenges, types of analytics methods, and applying analytics to stages of an attack. The agenda includes an introduction to analytics methods, an overview of Splunk Security Essentials, a demo scenario of detecting a malicious insider, and next steps involving Enterprise Security and Splunk UBA. The demo scenario shows detecting large file uploads from Box to detect an insider exporting sales proposals. The summary recommends starting with Splunk Security Essentials, then leveraging Enterprise Security and UBA for advanced machine learning detection and automated response.






![© 2017 SPLUNK INC.
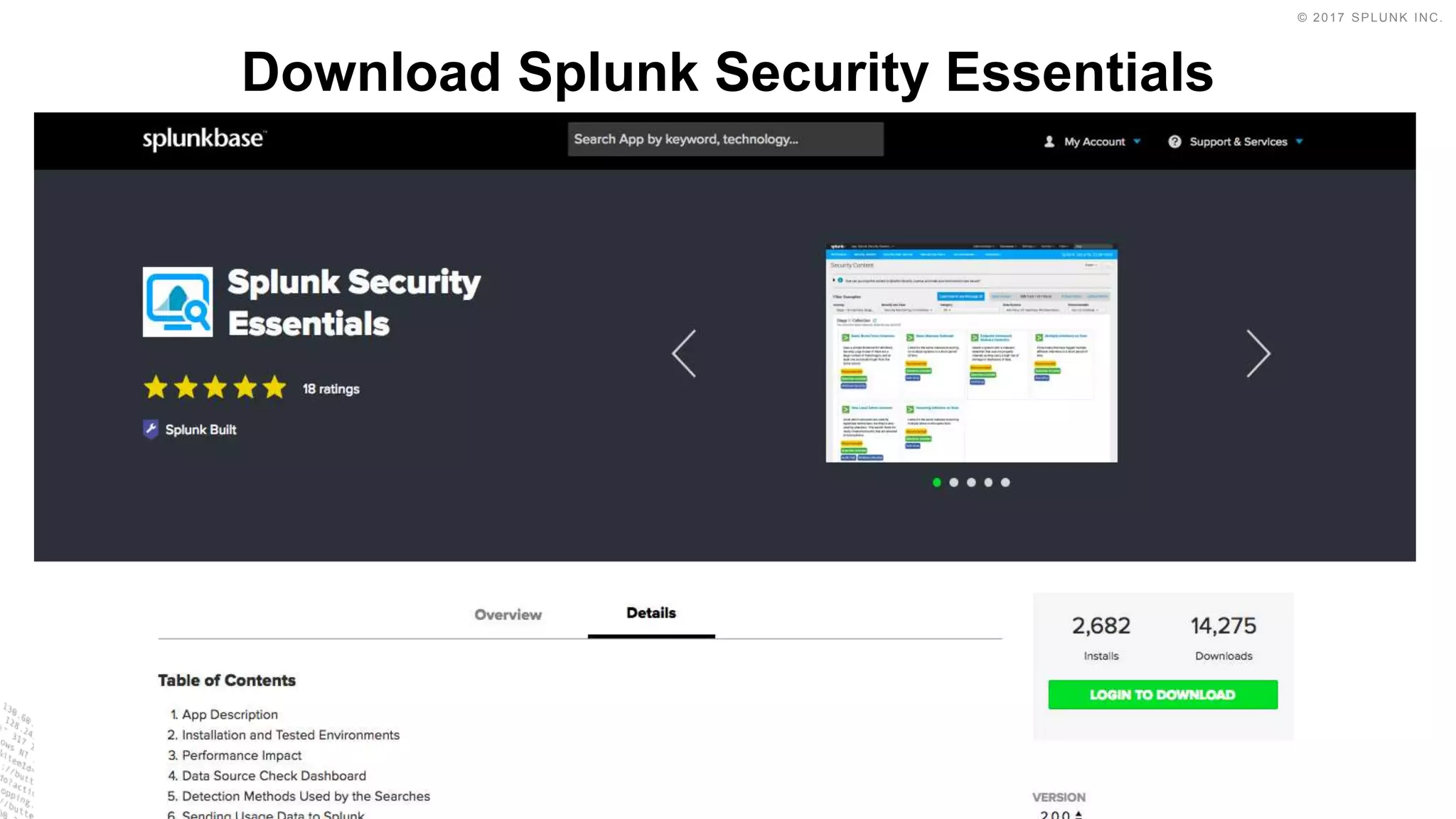
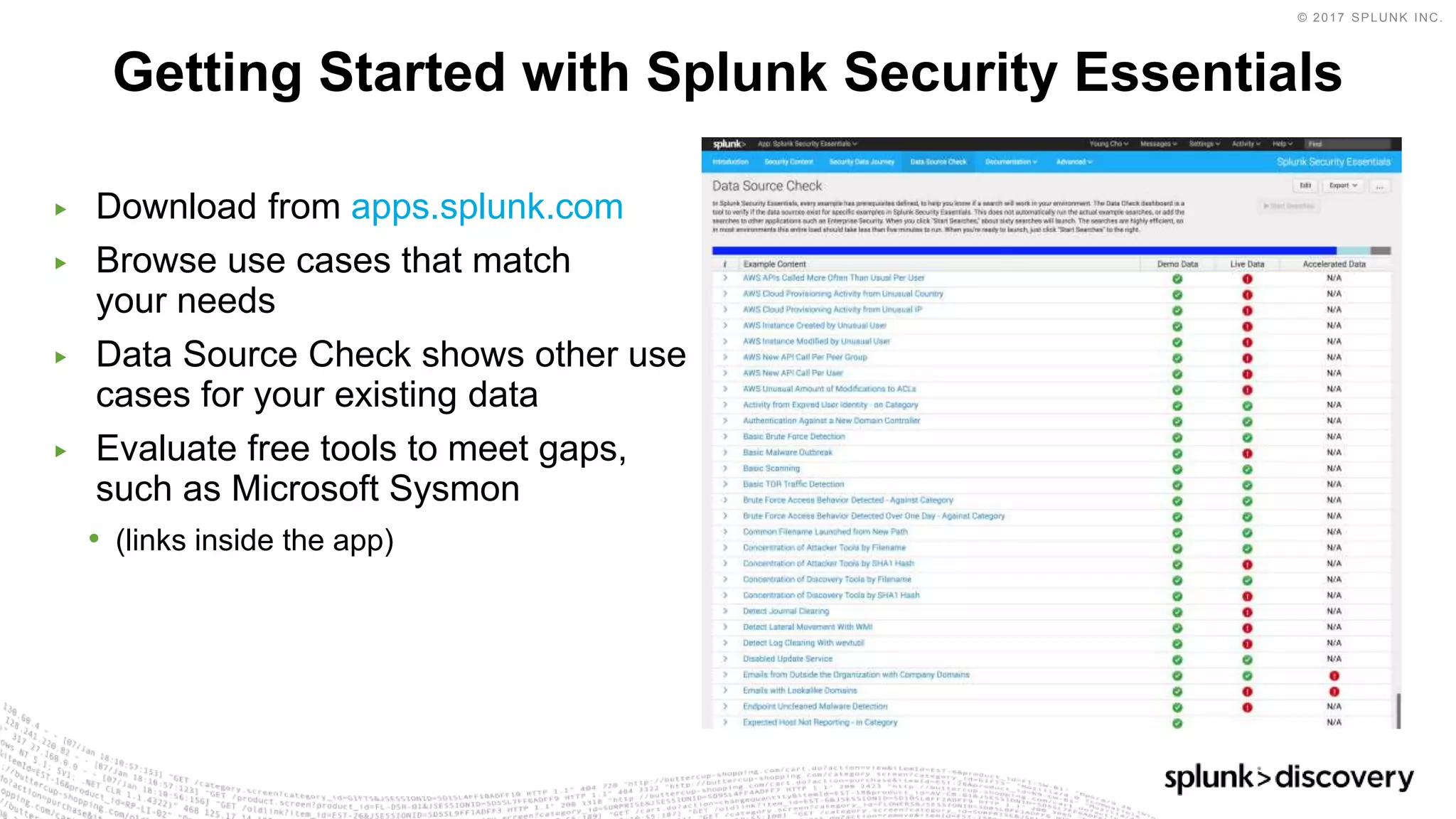
▶ Download from apps.splunk.com
▶ Find use cases that match your
needs
▶ Data Source Check shows other
use cases for your existing data
▶ Evaluate free tools to meet gaps,
such as Microsoft Sysmon
• (links inside the app)
Go Get Started With Splunk Security Essentials!
[01] [01]](https://image.slidesharecdn.com/splunkdiscoverymilan18session3security-180524144612/75/Splunk-Discovery-Milan-2018-Intro-to-Security-Analytics-Methods-35-2048.jpg)
