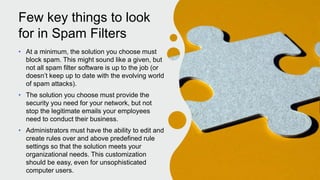
Spam filters detect unwanted email and stop it from reaching inboxes. They are used by Internet Service Providers and businesses to protect networks and users. Spam filters work by applying predefined rules to assign emails a score based on the probability of being spam, and flagging emails that pass a certain threshold. Different types of filters examine the email content, headers, sending IP addresses, and apply customized rules. While no single method can perfectly block spam without also blocking some legitimate emails, spam filtering is necessary to protect against viruses, phishing, and overloading of servers from high spam volumes.