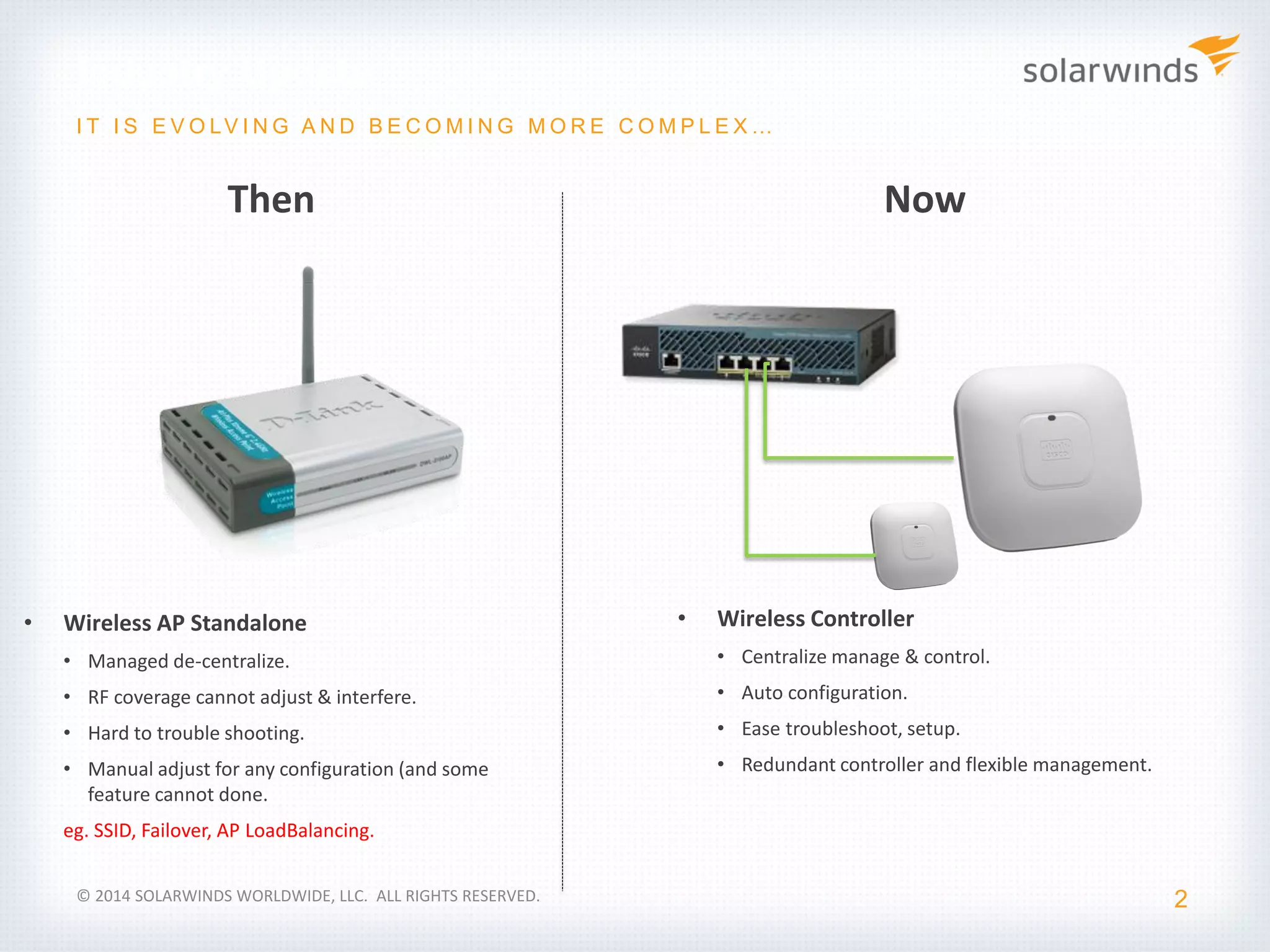
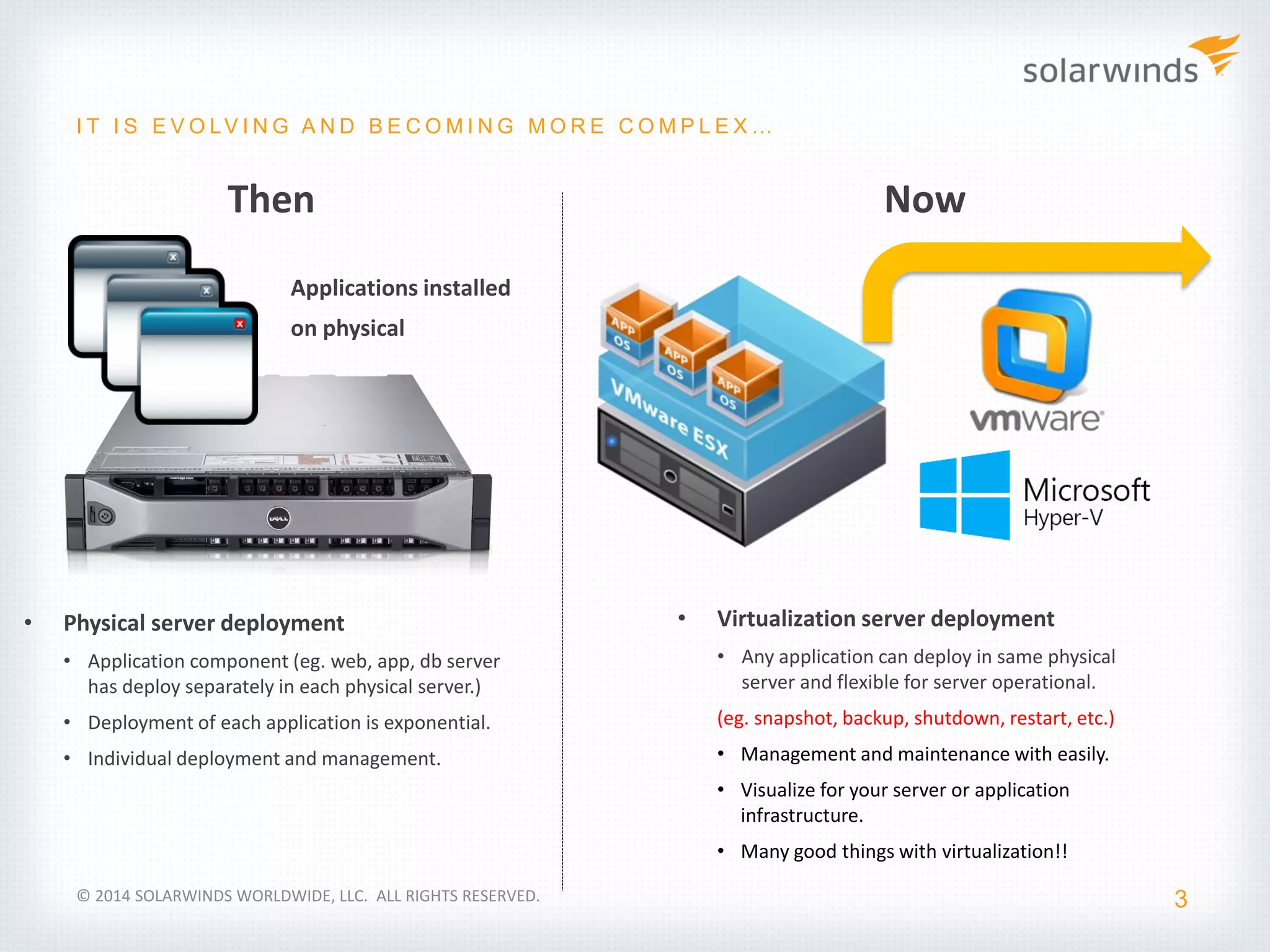
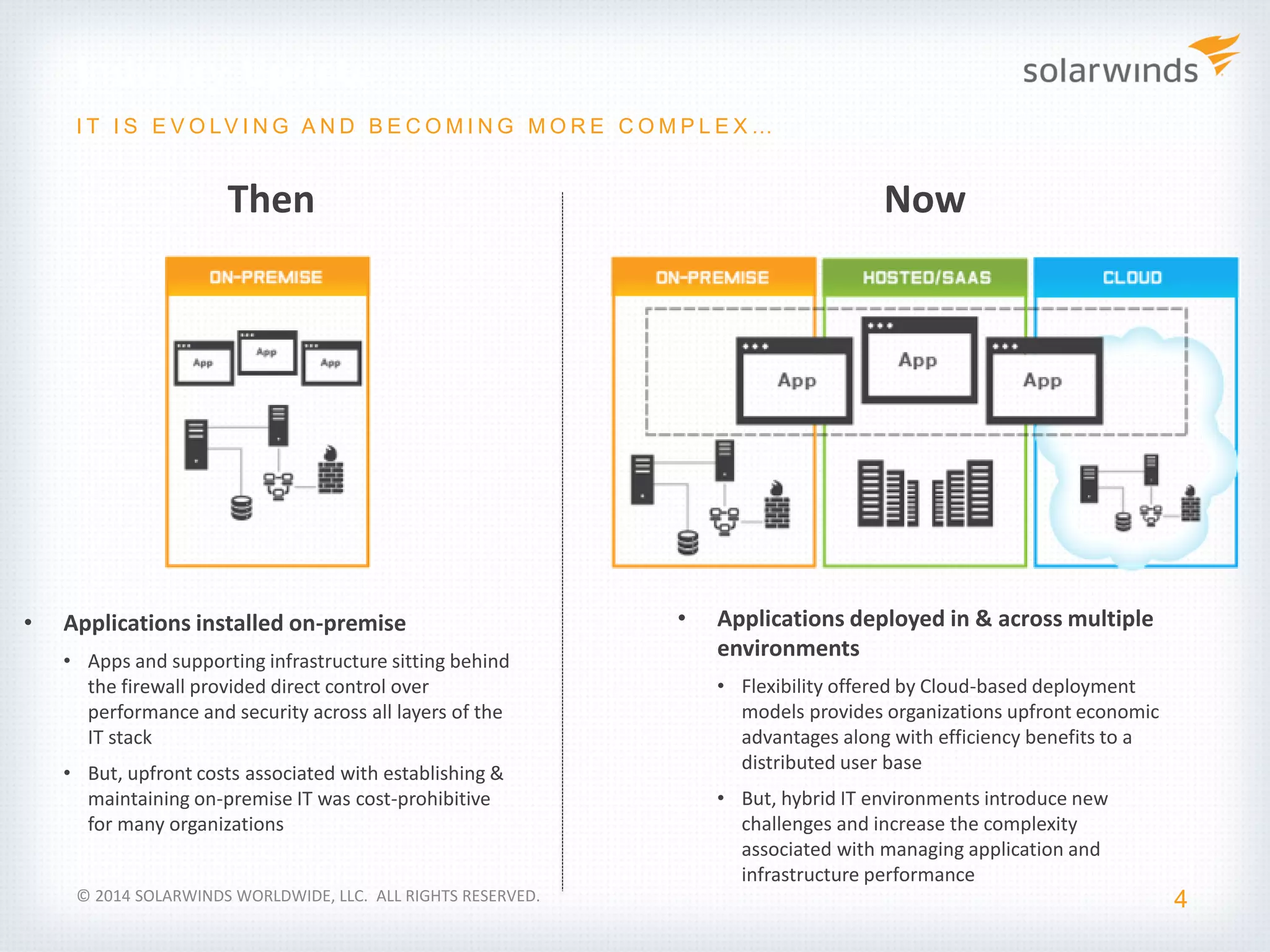
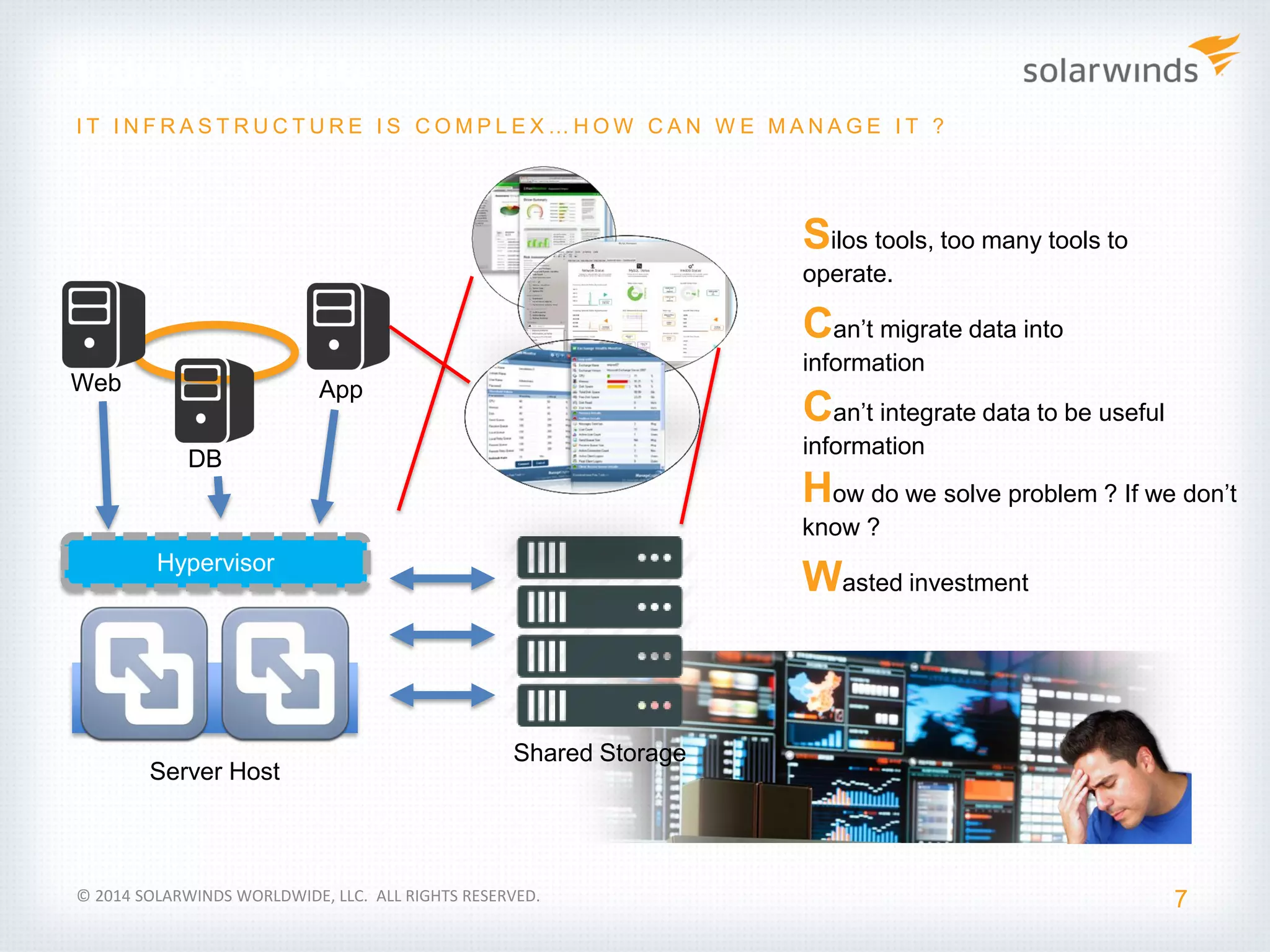
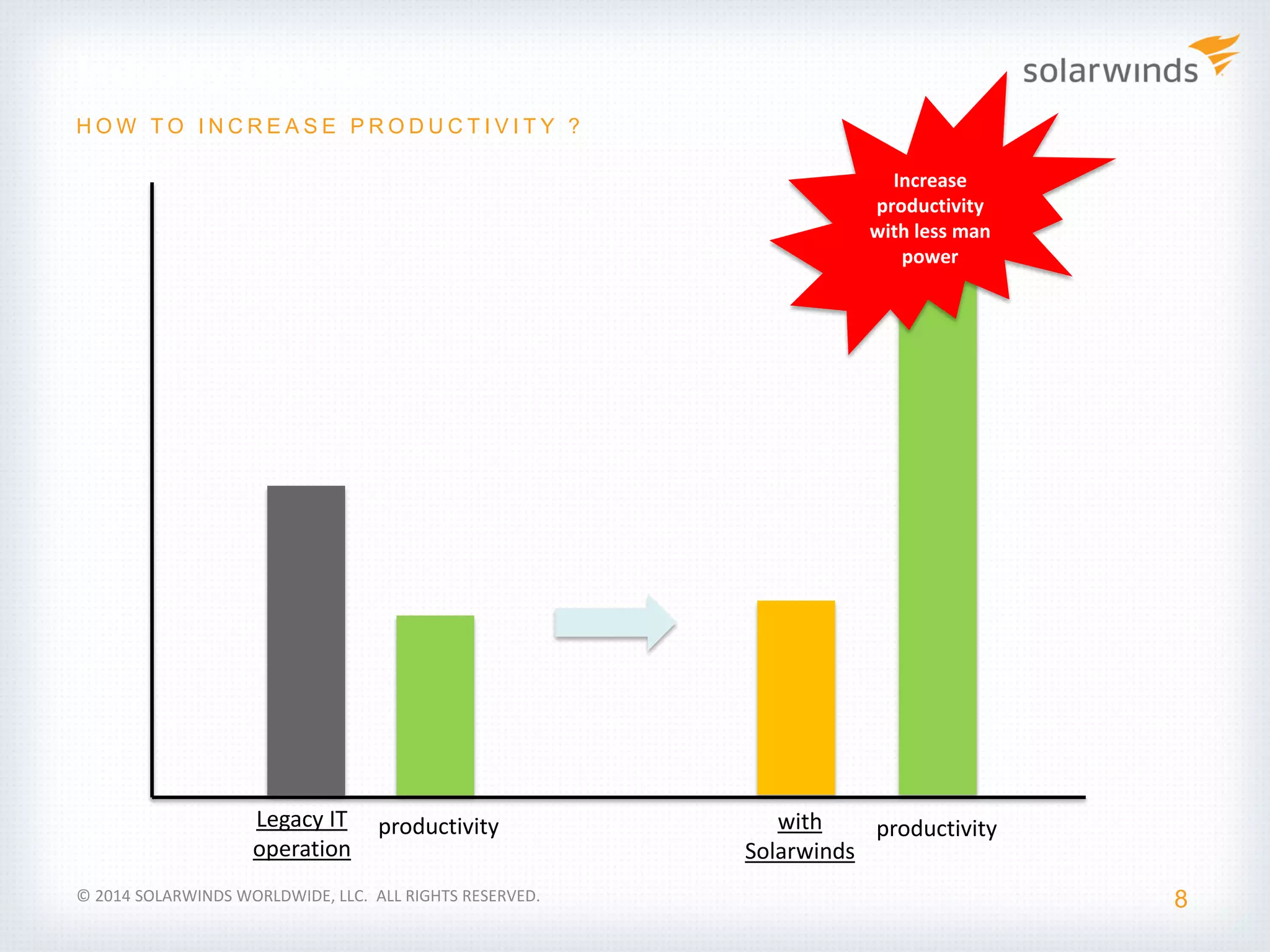
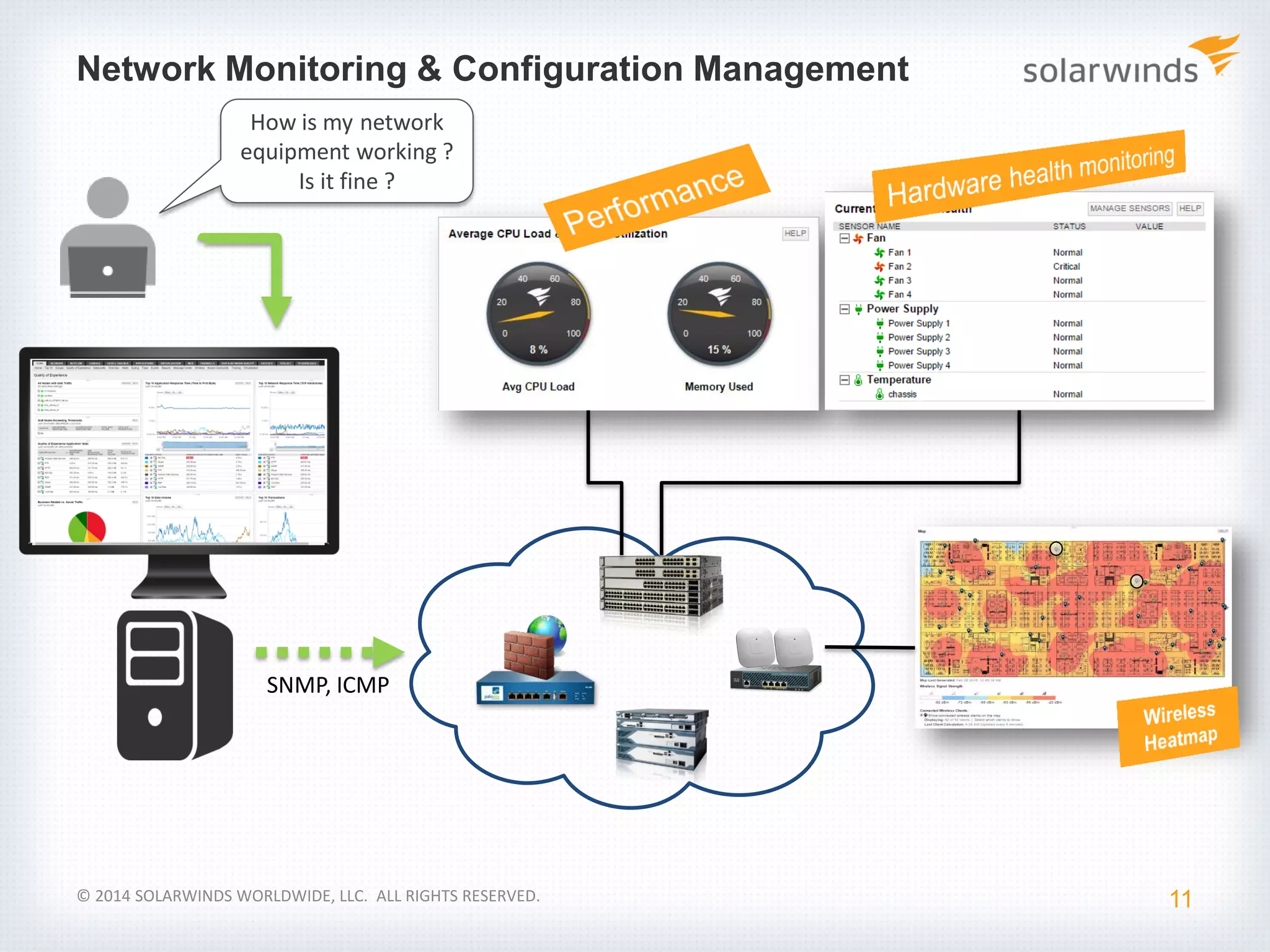
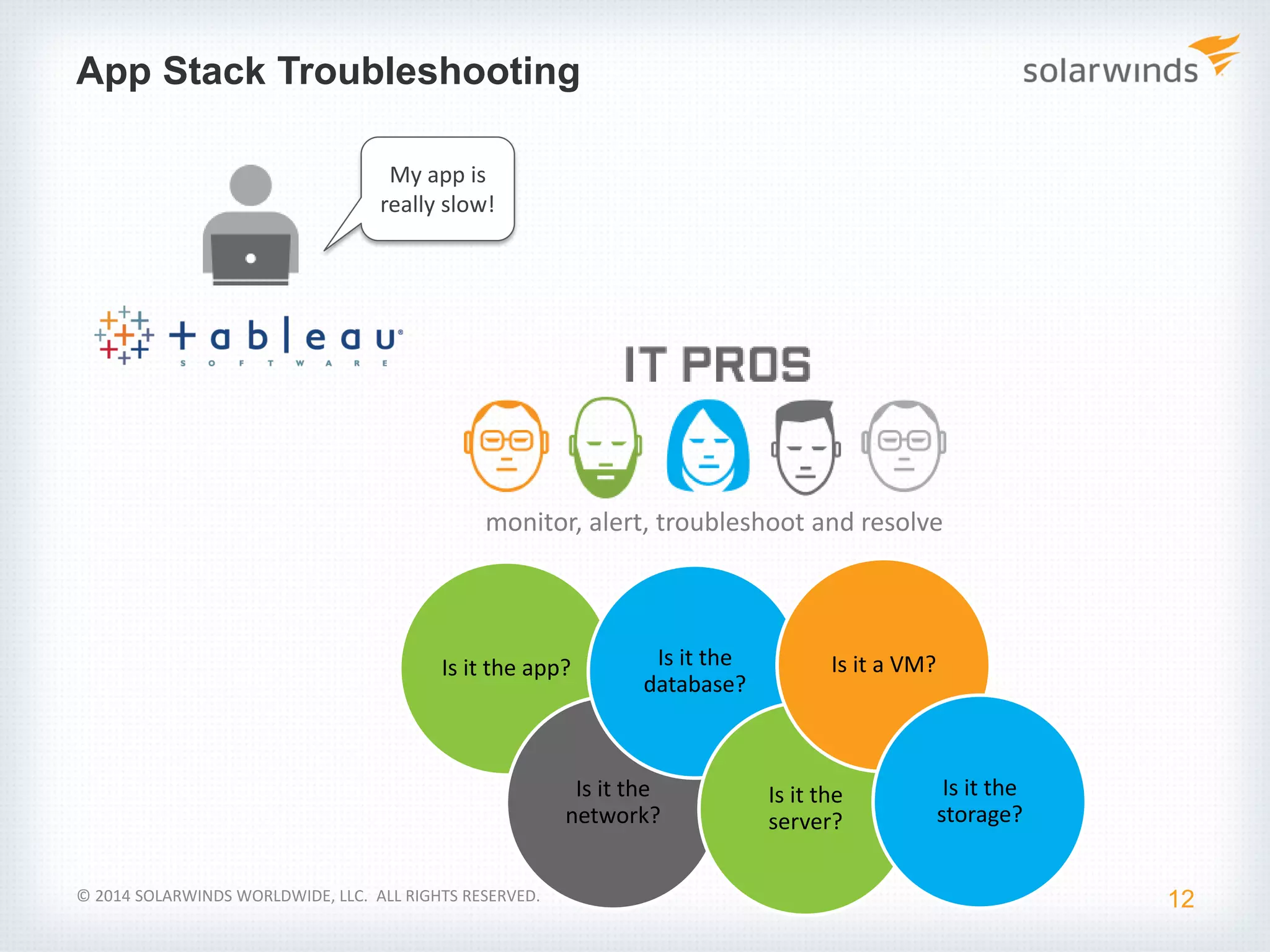
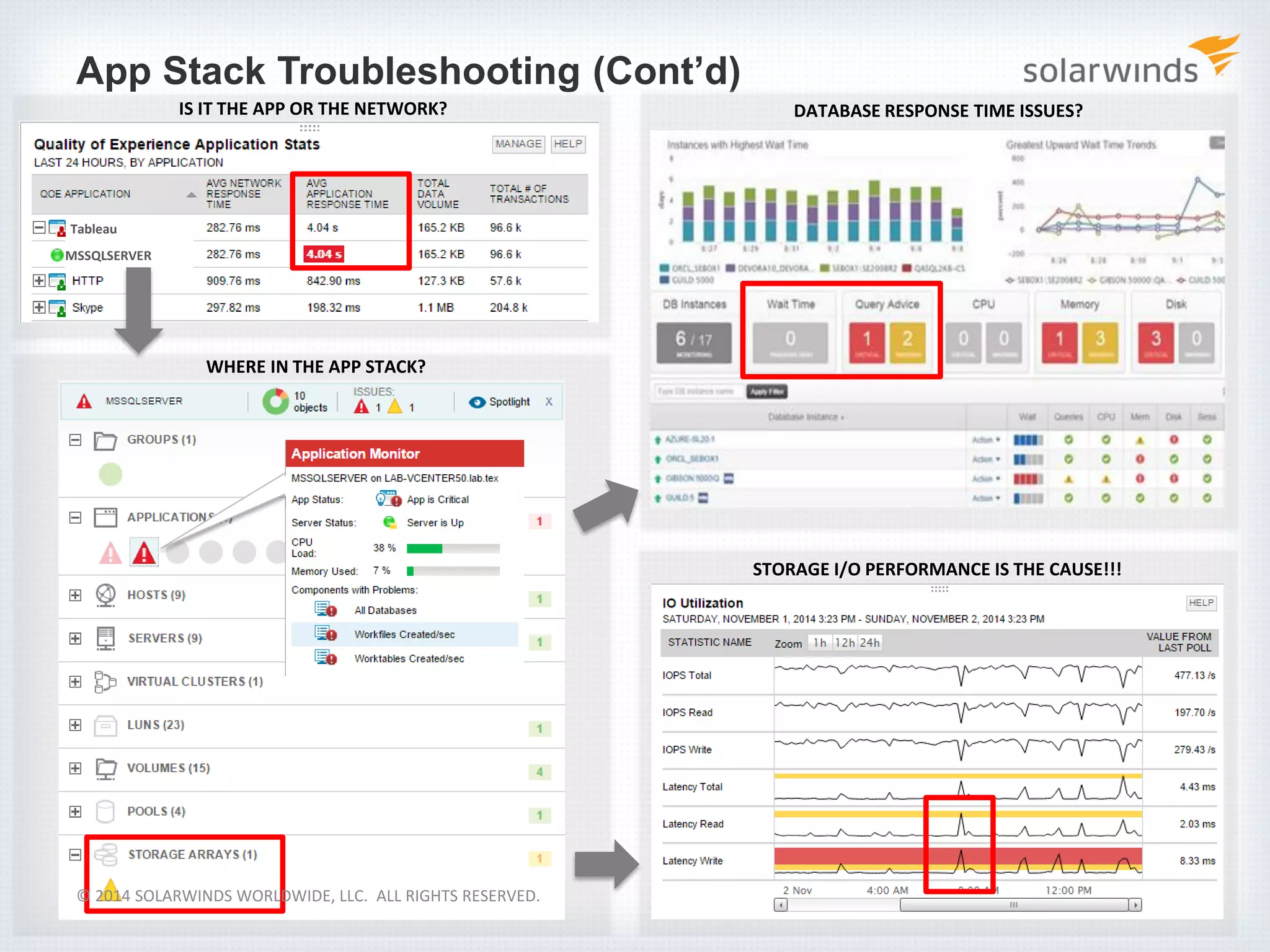
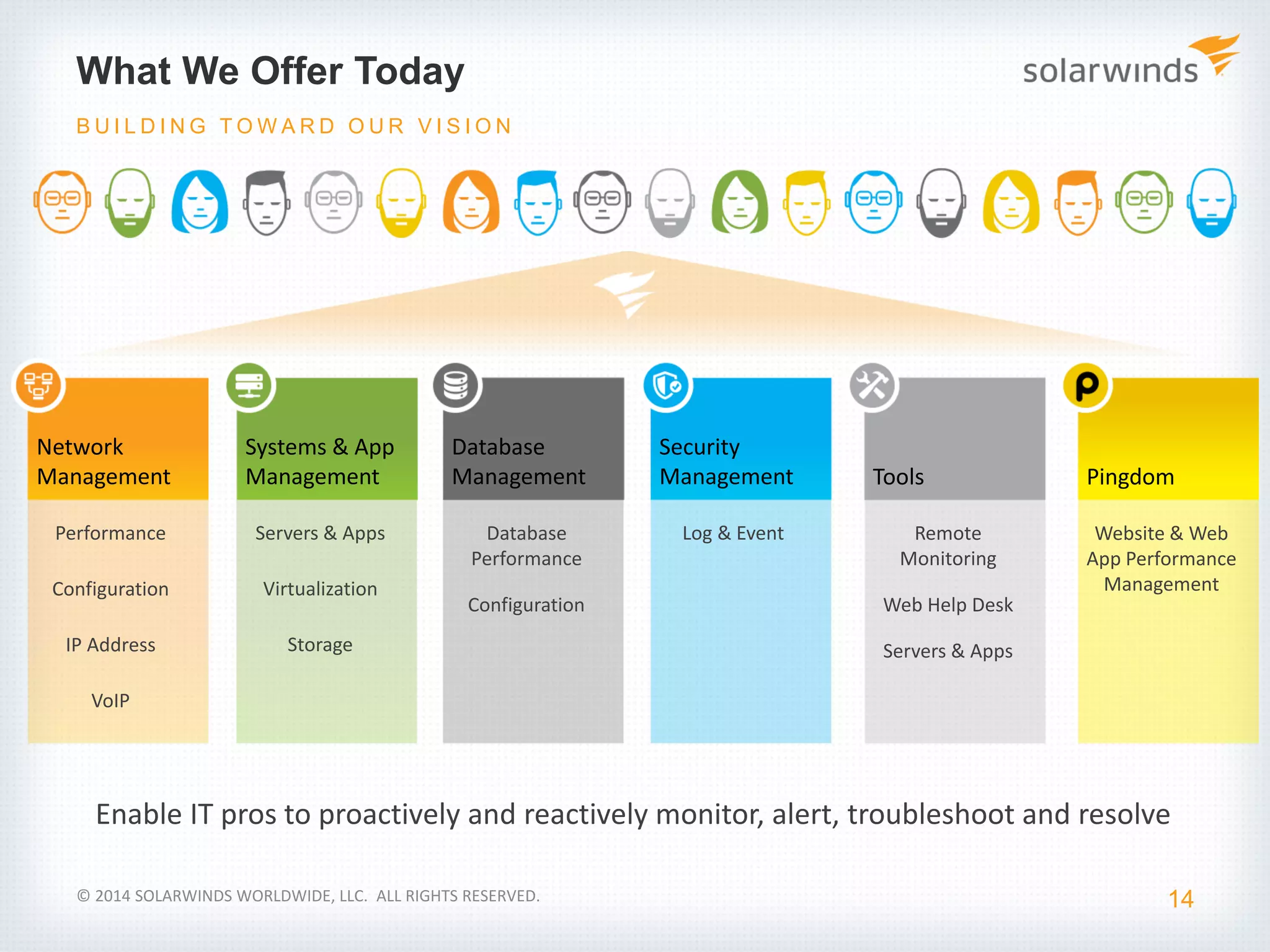
The document discusses the evolving complexity of IT environments, highlighting challenges in managing both physical and virtualized server deployments, as well as on-premise and cloud-based applications. It emphasizes the importance of quality of experience, network performance monitoring, and the use of management tools to increase productivity and resolve performance issues. SolarWinds is presented as a solution to enhance IT operations through comprehensive monitoring and management capabilities.