Software for Finding vulnerabilities in programs.pdf
•
0 likes•5 views
If You want to make your career in ethical hacking and cybersecurity field, you have golden opportunities, Bytecode Security is the best institute in delhi ncr, Bytecode offers Cyber security course online and offline. must visit https://www.bytec0de.com/cybersecurity/
Report
Share
Report
Share
Download to read offline
Recommended
Top 10 Penetration Testing Tools(Pen test tools).pptx

There are several penetration testing tools in the market, some are available as open-source tools. Tools like the Metasploit framework are simple and more popular. It has lots of features, it is easy to use. It is also available as a web version called Armitage.
What are the most important tools in kali.pdf

The choice of tools depends on the specific objectives of an ethical hacking or penetration testing project. Ethical hackers often combine and customize these tools to conduct thorough security assessments and identify vulnerabilities in target systems.
Learn more about ethical hacking
https://www.bytec0de.com/cybersecurity/ethical-hacking-training-course-in-delhi/
OpenVAS

OpenVAS is an open source vulnerability scanning framework consisting of services and tools that allow for vulnerability scanning and management. It includes OpenVAS scanner which executes network vulnerability tests daily using over 530,000 plugins, and OpenVAS manager which controls scanners and the central SQL database where scan results are stored. The OpenVAS CLI allows users to create batch processes to control the OpenVAS manager.
Types of Vulnerability Scanning An in depth investigation.pdf

Types of Vulnerability Scanning An in depth investigation.pdfCyber security professional services- Detox techno
A vulnerability scanner is a software tool that discovers and inventories all networked systems, including servers, PCs, laptops, virtual machines, containers, firewalls, switches, and printers. It attempts to identify the operating system and software installed on each device it detects, as well as other characteristics such as open ports and user accounts.Cyber-Security-Unit-4.pptx

The document discusses various automated security assessment tools, including OpenVAS and Nessus, that can be used to test systems for vulnerabilities. It also covers intrusion detection systems (IDS), describing host-based IDS that monitor system events and network-based IDS that monitor network traffic. Honeypots are discussed as trap systems that gather attacker information. Firewalls and their use of policies, blacklists and whitelists to filter network traffic are also summarized.
Practical White Hat Hacker Training - Vulnerability Detection

This presentation part of Prisma CSI's Practical White Hat Hacker Training v1
PRISMA CSI • Cyber Security and Intelligence www.prismacsi.com
This document can be shared or used by quoted and used for commercial purposes, but can not be changed. Detailed information is available at https://creativecommons.org/licenses/by-nc-nd/4.0/legalcode.
website vulnerability scanner and reporter research paper

This document discusses developing a website analysis tool to improve vulnerability scanning and reporting. It proposes using deep neural networks to enhance the accuracy of vulnerability scanners. It first reviews existing vulnerability scanners like Nessus, Acunetix, and OWASP ZAP and their capabilities. It then discusses how vulnerability scanners use techniques like crawling, fuzzing, and machine learning algorithms to detect vulnerabilities. The proposed tool aims to reduce false positives, allow simultaneous scans, and provide clear reports with countermeasure recommendations to better secure websites.
Penetration testing tools and phases

Pen testing or penetration testing is an ethical hacking process which involves assessing an application or an organization’s infrastructure for different types of vulnerabilities.
Recommended
Top 10 Penetration Testing Tools(Pen test tools).pptx

There are several penetration testing tools in the market, some are available as open-source tools. Tools like the Metasploit framework are simple and more popular. It has lots of features, it is easy to use. It is also available as a web version called Armitage.
What are the most important tools in kali.pdf

The choice of tools depends on the specific objectives of an ethical hacking or penetration testing project. Ethical hackers often combine and customize these tools to conduct thorough security assessments and identify vulnerabilities in target systems.
Learn more about ethical hacking
https://www.bytec0de.com/cybersecurity/ethical-hacking-training-course-in-delhi/
OpenVAS

OpenVAS is an open source vulnerability scanning framework consisting of services and tools that allow for vulnerability scanning and management. It includes OpenVAS scanner which executes network vulnerability tests daily using over 530,000 plugins, and OpenVAS manager which controls scanners and the central SQL database where scan results are stored. The OpenVAS CLI allows users to create batch processes to control the OpenVAS manager.
Types of Vulnerability Scanning An in depth investigation.pdf

Types of Vulnerability Scanning An in depth investigation.pdfCyber security professional services- Detox techno
A vulnerability scanner is a software tool that discovers and inventories all networked systems, including servers, PCs, laptops, virtual machines, containers, firewalls, switches, and printers. It attempts to identify the operating system and software installed on each device it detects, as well as other characteristics such as open ports and user accounts.Cyber-Security-Unit-4.pptx

The document discusses various automated security assessment tools, including OpenVAS and Nessus, that can be used to test systems for vulnerabilities. It also covers intrusion detection systems (IDS), describing host-based IDS that monitor system events and network-based IDS that monitor network traffic. Honeypots are discussed as trap systems that gather attacker information. Firewalls and their use of policies, blacklists and whitelists to filter network traffic are also summarized.
Practical White Hat Hacker Training - Vulnerability Detection

This presentation part of Prisma CSI's Practical White Hat Hacker Training v1
PRISMA CSI • Cyber Security and Intelligence www.prismacsi.com
This document can be shared or used by quoted and used for commercial purposes, but can not be changed. Detailed information is available at https://creativecommons.org/licenses/by-nc-nd/4.0/legalcode.
website vulnerability scanner and reporter research paper

This document discusses developing a website analysis tool to improve vulnerability scanning and reporting. It proposes using deep neural networks to enhance the accuracy of vulnerability scanners. It first reviews existing vulnerability scanners like Nessus, Acunetix, and OWASP ZAP and their capabilities. It then discusses how vulnerability scanners use techniques like crawling, fuzzing, and machine learning algorithms to detect vulnerabilities. The proposed tool aims to reduce false positives, allow simultaneous scans, and provide clear reports with countermeasure recommendations to better secure websites.
Penetration testing tools and phases

Pen testing or penetration testing is an ethical hacking process which involves assessing an application or an organization’s infrastructure for different types of vulnerabilities.
Top 10 Web Vulnerability Scanners

This document lists and describes the top 10 web vulnerability scanners as reported by users of the nmap-hackers mailing list in 2006. #1 is Nikto, an open source web server scanner that performs comprehensive tests against servers. #2 is Paros Proxy, a Java-based web proxy for assessing vulnerabilities in web applications. #3 is WebScarab, an open source tool for analyzing applications that use HTTP and HTTPS.
Owasp methodologies of Security testing part1

It is helpful for the beginners to understand the standard methodology approach of security testing on the basis of OWASP.
What Is A Good Operating System For Malware Analysis.pdf

When it comes to conducting malware analysis, there are several operating systems (OS) and tools that security researchers and analysts commonly use.
the choice of the operating system and tools for malware analysis depends on your specific needs, skill set, and the type of malware you're dealing with. It's important to emphasize that when conducting malware analysis, you should always work in a controlled and isolated environment to prevent the malware from spreading or causing harm to your systems. Additionally, keep in mind that ethical and legal considerations are important in this field, so ensure you have the necessary permissions and comply with relevant laws and regulations when analyzing malware.
Learn more:
https://www.bytec0de.com/malware-analysis-course-training-certification/
Vulnerability assessment and penetration testing

This document discusses vulnerability assessment and penetration testing. It defines them as two types of vulnerability testing that search for known vulnerabilities and attempt to exploit vulnerabilities, respectively. Vulnerability assessment uses automated tools to detect known issues, while penetration testing employs hacking techniques to demonstrate how deeply vulnerabilities could be exploited like an actual attacker. Both are important security practices for identifying weaknesses and reducing risks, but require different skills and have different strengths, weaknesses, frequencies, and report outputs. Reasons for vulnerabilities include insecure coding, limited testing, and misconfigurations. The document outlines common vulnerability and attack types as well as how vulnerability assessment and penetration testing are typically conducted.
Nessus is a network security toolIn a pragraph describe how it is .pdf

Nessus is a network security tool
In a pragraph describe how it is useful to a networksecurityspecialist and how it may be used for
harmfulpurposes by a hacker?
Note: provide relaiblerefrences for your answer.
Solution
Nessus:
Nessus is a proprietary vulnerability scanner.Nessus was developed by Tenable network security.
How it is useful?:
It is extremely good for discovering platform and network device vulnerabilities.
•It is a good automated tool for finding Mis configuration,default passwords and known
vulnerabilities on systems.
•Denails of service against the TCP/IP stack by using malforme packets.
•It also has some web scanning options that can be configured,different types of ports scanning.
•Another useful Nessus opetion is the ability to enable(or) disable testing of embedded web
servers that may be adversely affectd, when scanned.
•Nessus provides the ability for the user to adjust how Nessus tests each CGI scrit and determine
the duration of the tests.
•Nessus also provides special features for Webmirroring.
How it may be used harmful purposses?:
If some one wanted to hack your local network,the first thing they do is run a vulnerability scan
then they\'d run a penetration test.
•A vulnerability scan digs through the various devices on your network and looks for potential
holes,like open port,outdated software with known vulnerabilities.If they find any thing a hacker
would exploit them.
•Nessus is scan vulnerabilities and shoreup your home network.
•Nessus vulnerability scanner is fast and diverse tool that helps any size organization audit their
assets for security vulnerabilities.
•security center can organize network assets into categories through a combination of network
scanning,passive network monitoring and integration with existing asset and network
management data tools.
•Security Center can manage scans of software under development to defect vulnerabilities,early
in the development cycle.
•Nessus is used to check the understanding operating system for any vulnerabilities in the
operating system application(or) database.
•Nessus can be used to check the configuration of the os,application and database.
•Nessus can performs a various of Web application audit to test for common aplication
vulnerabilities.
•Nessus provides special features for Web mirroring,allowing user to specify which part of the
website will be crawled(or)not.
•Nessus has ability to enable(or)disable testing of embedded web servers that may be adversely
affected when scanned.
•The pvs can monitor network traffic for encrypted data.
•The LCE can be used to monitor any logs generated by software.
•LCE can make use of Web and Databse to look for application process and testing..
Evaluating Web App, Mobile App, and API Security - Matt Cohen

This document discusses evaluating web app, mobile app, and API security standards and tools. It provides an overview of the Open Web Application Security Project (OWASP) which publishes free, open-source security standards like the Application Security Verification Standard (ASVS). The document also discusses different types of software security testing like static analysis, dynamic analysis, code review, and penetration testing. It provides a demonstration of using the OWASP Zed Attack Proxy (ZAP) tool to conduct dynamic analysis and penetration testing of a web application.
Scanning web vulnerabilities

Web Vulnerabilities Scanning basics and knowledge about how to search for the vulnerabilities is given in this presentation.
VAPT PRESENTATION full.pptx

The document provides information on vulnerability assessment and penetration testing. It defines vulnerability assessment as a systematic approach to finding security issues in a network or system through manual and automated scanning. Penetration testing involves exploring and exploiting any vulnerabilities that are found to confirm their existence and potential damage. The document outlines the types of testing as blackbox, graybox, and whitebox. It also lists some common tools used for testing like Nmap, ZAP, Nikto, WPScan, and HostedScan. Finally, it provides examples of specific vulnerabilities found and their solutions, such as outdated themes/plugins, backup files being accessible, and SQL injection issues.
Talos

Talos is Cisco's threat intelligence organization devoted to protecting customers, products, and services from cyber threats. It is divided into five departments: Detection Research, Threat Intelligence, Engine Development, Vulnerability Research and Development, and Outreach. Talos uses both proprietary technologies and open-source tools like Snort, Daemonlogger, Moflow, PE-Sig, and ClamAV to conduct threat research, detect vulnerabilities, and provide network security.
VAPT_FINAL SLIDES.pptx

The document discusses vulnerability assessment and penetration testing (VAPT). It defines vulnerability assessment as systematically finding security issues in a network or system through scanning, and penetration testing as exploiting vulnerabilities to prove they can cause damage. The document outlines the types of VAPT testing, steps in the process, common tools used like Nmap and ZAP, and top vulnerabilities like SQL injection and XSS. It provides examples of specific vulnerabilities found like outdated themes and XML-RPC access, and their potential impacts and solutions.
Information Security 201

This document provides an overview of an information security training session covering various topics:
- The presenter is introduced as a cybersecurity analyst and researcher who provides their contact information.
- The agenda includes topics like antivirus software, static and dynamic application security testing, the CIA triad model of information security, reconnaissance techniques, reverse shells, endpoint detection and response, configuration reviews, vulnerability assessments, penetration testing, and critical infrastructure security.
- Each topic is then defined in one to three paragraphs with examples of common tools used for tasks like passive and active reconnaissance, static application security testing, and vulnerability assessments.
Cryptography and system security

Tools and Mechanisms for Network Security in an Organization.
Physical Security, Administrative Security and Technical Security measures have been described.
Security Testing Tools are Nessus, THC Hydra, Kismet, Nikto, WireShark and NMAP.
Using Analyzers to Resolve Security Problems

in this presentation i took a project and used an analyzer(e.g. SonarQube) to detect the security issues with it and reported a the result and after resolving most of those problems i used the same analyzer to get another report and in the process showed how to use such analyzers to detect security issues in the web applications
INSECT | Security System Project | 2011

A research and security tool that allow to apply different exploits to test the systems and networks security with purpose to improve the level of security.
Anti-virus Mechanisms and Various Ways to Bypass Antivirus detection

The document provides an overview of how anti-virus software works and techniques used to bypass antivirus detection. It discusses how antiviruses use signature-based, heuristic-based, behavioral, and sandboxing techniques to detect malware. It also explains common techniques used to evade detection like packers, splitters, code obfuscation, and injection. The document concludes that while antivirus has improved, virus creators continually develop new methods to bypass protections and that additional security measures are still needed.
Wazuh Security Platform

The document provides an overview of the Wazuh open source host-based intrusion detection system (HIDS). It describes how Wazuh uses agents installed on endpoints that collect and transmit security data to a central server for analysis. The server analyzes the data, triggers alerts for threats or anomalies, and stores the information in Elasticsearch for visualization and exploration through the Wazuh dashboard user interface. Key components of the Wazuh architecture include the agents, server, indexer cluster for data storage, and dashboard for monitoring, analysis and management.
Benchmarking our Network Vulnerability Scanner

In January 2024, we decided to evaluate the most used network vulnerability scanners - Nessus Professional, Qualys, Rapid7 Nexpose, Nuclei, OpenVAS, and Nmap vulnerability scripts - including our own, which industry peers can validate independently.
Here’s why we did it, what results we got, and how you can verify them (there’s a white paper you can download with access to all the results behind this benchmark).
Acunetix technical presentation v7 setembro2011

This document provides an overview of the Acunetix Web Vulnerability Scanner (WVS). It describes how WVS works like a hacker to find vulnerabilities, using both automated and manual scanning methods. The key aspects covered include the scan wizard, crawling and scanning process, tools for manual testing, vulnerability database customization, and configuration settings. The goal of WVS is to help users find security vulnerabilities in their web applications and servers in a controlled, non-destructive way.
FALCON.pptx

This document outlines a proposed vulnerability assessment tool called Falcon. It discusses how vulnerability scanning can help organizations identify and remedy security vulnerabilities before hackers can exploit them. The tool would conduct thorough scans to find any gaps in a system's defenses. The document provides details on the tool's aims, introduction to cybersecurity and vulnerability scanning, proposed technical stack including Next JS, MongoDB, and Python, data flow diagrams, and the team working on the project.
"Automated Malware Analysis" de Gabriel Negreira Barbosa, Malware Research an...

This document discusses automated malware analysis techniques used by Dissect || PE. It describes the challenges of processing large volumes of samples from different sources. The system uses a feed server, scheduler, unpackers, dissectors, and kernel driver. Samples are run in virtual machines and real machines. Plugins allow custom analysis. The architecture is scalable and supports community research through shared samples and results.
What Are The Types of Malware? Must Read

If you want to make your career in ethical hacking, Bytecode Security offers the best malware analysis course online offline with job placement assistance. Read more: https://www.bytec0de.com/malware-analysis-course-training-certification/
Top 10 Advantages of Python Programming Language .pdf

Bytecode security offers Best Pyhton Programming course online and offline and
Summer Training In Cybersecurity .
If you want to make your career in cybersecurity, get courses information from career counselor: +91 9513805401
More Related Content
Similar to Software for Finding vulnerabilities in programs.pdf
Top 10 Web Vulnerability Scanners

This document lists and describes the top 10 web vulnerability scanners as reported by users of the nmap-hackers mailing list in 2006. #1 is Nikto, an open source web server scanner that performs comprehensive tests against servers. #2 is Paros Proxy, a Java-based web proxy for assessing vulnerabilities in web applications. #3 is WebScarab, an open source tool for analyzing applications that use HTTP and HTTPS.
Owasp methodologies of Security testing part1

It is helpful for the beginners to understand the standard methodology approach of security testing on the basis of OWASP.
What Is A Good Operating System For Malware Analysis.pdf

When it comes to conducting malware analysis, there are several operating systems (OS) and tools that security researchers and analysts commonly use.
the choice of the operating system and tools for malware analysis depends on your specific needs, skill set, and the type of malware you're dealing with. It's important to emphasize that when conducting malware analysis, you should always work in a controlled and isolated environment to prevent the malware from spreading or causing harm to your systems. Additionally, keep in mind that ethical and legal considerations are important in this field, so ensure you have the necessary permissions and comply with relevant laws and regulations when analyzing malware.
Learn more:
https://www.bytec0de.com/malware-analysis-course-training-certification/
Vulnerability assessment and penetration testing

This document discusses vulnerability assessment and penetration testing. It defines them as two types of vulnerability testing that search for known vulnerabilities and attempt to exploit vulnerabilities, respectively. Vulnerability assessment uses automated tools to detect known issues, while penetration testing employs hacking techniques to demonstrate how deeply vulnerabilities could be exploited like an actual attacker. Both are important security practices for identifying weaknesses and reducing risks, but require different skills and have different strengths, weaknesses, frequencies, and report outputs. Reasons for vulnerabilities include insecure coding, limited testing, and misconfigurations. The document outlines common vulnerability and attack types as well as how vulnerability assessment and penetration testing are typically conducted.
Nessus is a network security toolIn a pragraph describe how it is .pdf

Nessus is a network security tool
In a pragraph describe how it is useful to a networksecurityspecialist and how it may be used for
harmfulpurposes by a hacker?
Note: provide relaiblerefrences for your answer.
Solution
Nessus:
Nessus is a proprietary vulnerability scanner.Nessus was developed by Tenable network security.
How it is useful?:
It is extremely good for discovering platform and network device vulnerabilities.
•It is a good automated tool for finding Mis configuration,default passwords and known
vulnerabilities on systems.
•Denails of service against the TCP/IP stack by using malforme packets.
•It also has some web scanning options that can be configured,different types of ports scanning.
•Another useful Nessus opetion is the ability to enable(or) disable testing of embedded web
servers that may be adversely affectd, when scanned.
•Nessus provides the ability for the user to adjust how Nessus tests each CGI scrit and determine
the duration of the tests.
•Nessus also provides special features for Webmirroring.
How it may be used harmful purposses?:
If some one wanted to hack your local network,the first thing they do is run a vulnerability scan
then they\'d run a penetration test.
•A vulnerability scan digs through the various devices on your network and looks for potential
holes,like open port,outdated software with known vulnerabilities.If they find any thing a hacker
would exploit them.
•Nessus is scan vulnerabilities and shoreup your home network.
•Nessus vulnerability scanner is fast and diverse tool that helps any size organization audit their
assets for security vulnerabilities.
•security center can organize network assets into categories through a combination of network
scanning,passive network monitoring and integration with existing asset and network
management data tools.
•Security Center can manage scans of software under development to defect vulnerabilities,early
in the development cycle.
•Nessus is used to check the understanding operating system for any vulnerabilities in the
operating system application(or) database.
•Nessus can be used to check the configuration of the os,application and database.
•Nessus can performs a various of Web application audit to test for common aplication
vulnerabilities.
•Nessus provides special features for Web mirroring,allowing user to specify which part of the
website will be crawled(or)not.
•Nessus has ability to enable(or)disable testing of embedded web servers that may be adversely
affected when scanned.
•The pvs can monitor network traffic for encrypted data.
•The LCE can be used to monitor any logs generated by software.
•LCE can make use of Web and Databse to look for application process and testing..
Evaluating Web App, Mobile App, and API Security - Matt Cohen

This document discusses evaluating web app, mobile app, and API security standards and tools. It provides an overview of the Open Web Application Security Project (OWASP) which publishes free, open-source security standards like the Application Security Verification Standard (ASVS). The document also discusses different types of software security testing like static analysis, dynamic analysis, code review, and penetration testing. It provides a demonstration of using the OWASP Zed Attack Proxy (ZAP) tool to conduct dynamic analysis and penetration testing of a web application.
Scanning web vulnerabilities

Web Vulnerabilities Scanning basics and knowledge about how to search for the vulnerabilities is given in this presentation.
VAPT PRESENTATION full.pptx

The document provides information on vulnerability assessment and penetration testing. It defines vulnerability assessment as a systematic approach to finding security issues in a network or system through manual and automated scanning. Penetration testing involves exploring and exploiting any vulnerabilities that are found to confirm their existence and potential damage. The document outlines the types of testing as blackbox, graybox, and whitebox. It also lists some common tools used for testing like Nmap, ZAP, Nikto, WPScan, and HostedScan. Finally, it provides examples of specific vulnerabilities found and their solutions, such as outdated themes/plugins, backup files being accessible, and SQL injection issues.
Talos

Talos is Cisco's threat intelligence organization devoted to protecting customers, products, and services from cyber threats. It is divided into five departments: Detection Research, Threat Intelligence, Engine Development, Vulnerability Research and Development, and Outreach. Talos uses both proprietary technologies and open-source tools like Snort, Daemonlogger, Moflow, PE-Sig, and ClamAV to conduct threat research, detect vulnerabilities, and provide network security.
VAPT_FINAL SLIDES.pptx

The document discusses vulnerability assessment and penetration testing (VAPT). It defines vulnerability assessment as systematically finding security issues in a network or system through scanning, and penetration testing as exploiting vulnerabilities to prove they can cause damage. The document outlines the types of VAPT testing, steps in the process, common tools used like Nmap and ZAP, and top vulnerabilities like SQL injection and XSS. It provides examples of specific vulnerabilities found like outdated themes and XML-RPC access, and their potential impacts and solutions.
Information Security 201

This document provides an overview of an information security training session covering various topics:
- The presenter is introduced as a cybersecurity analyst and researcher who provides their contact information.
- The agenda includes topics like antivirus software, static and dynamic application security testing, the CIA triad model of information security, reconnaissance techniques, reverse shells, endpoint detection and response, configuration reviews, vulnerability assessments, penetration testing, and critical infrastructure security.
- Each topic is then defined in one to three paragraphs with examples of common tools used for tasks like passive and active reconnaissance, static application security testing, and vulnerability assessments.
Cryptography and system security

Tools and Mechanisms for Network Security in an Organization.
Physical Security, Administrative Security and Technical Security measures have been described.
Security Testing Tools are Nessus, THC Hydra, Kismet, Nikto, WireShark and NMAP.
Using Analyzers to Resolve Security Problems

in this presentation i took a project and used an analyzer(e.g. SonarQube) to detect the security issues with it and reported a the result and after resolving most of those problems i used the same analyzer to get another report and in the process showed how to use such analyzers to detect security issues in the web applications
INSECT | Security System Project | 2011

A research and security tool that allow to apply different exploits to test the systems and networks security with purpose to improve the level of security.
Anti-virus Mechanisms and Various Ways to Bypass Antivirus detection

The document provides an overview of how anti-virus software works and techniques used to bypass antivirus detection. It discusses how antiviruses use signature-based, heuristic-based, behavioral, and sandboxing techniques to detect malware. It also explains common techniques used to evade detection like packers, splitters, code obfuscation, and injection. The document concludes that while antivirus has improved, virus creators continually develop new methods to bypass protections and that additional security measures are still needed.
Wazuh Security Platform

The document provides an overview of the Wazuh open source host-based intrusion detection system (HIDS). It describes how Wazuh uses agents installed on endpoints that collect and transmit security data to a central server for analysis. The server analyzes the data, triggers alerts for threats or anomalies, and stores the information in Elasticsearch for visualization and exploration through the Wazuh dashboard user interface. Key components of the Wazuh architecture include the agents, server, indexer cluster for data storage, and dashboard for monitoring, analysis and management.
Benchmarking our Network Vulnerability Scanner

In January 2024, we decided to evaluate the most used network vulnerability scanners - Nessus Professional, Qualys, Rapid7 Nexpose, Nuclei, OpenVAS, and Nmap vulnerability scripts - including our own, which industry peers can validate independently.
Here’s why we did it, what results we got, and how you can verify them (there’s a white paper you can download with access to all the results behind this benchmark).
Acunetix technical presentation v7 setembro2011

This document provides an overview of the Acunetix Web Vulnerability Scanner (WVS). It describes how WVS works like a hacker to find vulnerabilities, using both automated and manual scanning methods. The key aspects covered include the scan wizard, crawling and scanning process, tools for manual testing, vulnerability database customization, and configuration settings. The goal of WVS is to help users find security vulnerabilities in their web applications and servers in a controlled, non-destructive way.
FALCON.pptx

This document outlines a proposed vulnerability assessment tool called Falcon. It discusses how vulnerability scanning can help organizations identify and remedy security vulnerabilities before hackers can exploit them. The tool would conduct thorough scans to find any gaps in a system's defenses. The document provides details on the tool's aims, introduction to cybersecurity and vulnerability scanning, proposed technical stack including Next JS, MongoDB, and Python, data flow diagrams, and the team working on the project.
"Automated Malware Analysis" de Gabriel Negreira Barbosa, Malware Research an...

This document discusses automated malware analysis techniques used by Dissect || PE. It describes the challenges of processing large volumes of samples from different sources. The system uses a feed server, scheduler, unpackers, dissectors, and kernel driver. Samples are run in virtual machines and real machines. Plugins allow custom analysis. The architecture is scalable and supports community research through shared samples and results.
Similar to Software for Finding vulnerabilities in programs.pdf (20)
What Is A Good Operating System For Malware Analysis.pdf

What Is A Good Operating System For Malware Analysis.pdf
Nessus is a network security toolIn a pragraph describe how it is .pdf

Nessus is a network security toolIn a pragraph describe how it is .pdf
Evaluating Web App, Mobile App, and API Security - Matt Cohen

Evaluating Web App, Mobile App, and API Security - Matt Cohen
Anti-virus Mechanisms and Various Ways to Bypass Antivirus detection

Anti-virus Mechanisms and Various Ways to Bypass Antivirus detection
"Automated Malware Analysis" de Gabriel Negreira Barbosa, Malware Research an...

"Automated Malware Analysis" de Gabriel Negreira Barbosa, Malware Research an...
More from Bytecode Security
What Are The Types of Malware? Must Read

If you want to make your career in ethical hacking, Bytecode Security offers the best malware analysis course online offline with job placement assistance. Read more: https://www.bytec0de.com/malware-analysis-course-training-certification/
Top 10 Advantages of Python Programming Language .pdf

Bytecode security offers Best Pyhton Programming course online and offline and
Summer Training In Cybersecurity .
If you want to make your career in cybersecurity, get courses information from career counselor: +91 9513805401
Which Company Hires Ethical Hackers in 2024

Bytecode security offers Best Ethical Hacking course and 1 Year Diploma Course In Cybersecurity Summer Training.
If you want to make your career in cybersecurity, get courses information from career counselor +91 9513805401 or visit website: www.bytec0de.com
What Is The Purpose Of Reverse Engineering.pdf

Bytecode security offers the Best Reverse Engineering course in Delhi. Quality education is our motive,
and we provide high qualified skilled trainers.
If you want to make your bright career, talk to career counselor: +919513805401 or Visit :
https://www.bytec0de.com/reverse-engineering-training-course-in-delhi/
Skills Needed to Become a Cyber.pdf

Developing a combination of technical skills, critical thinking abilities, and a strong understanding of security concepts is crucial for becoming a proficient cybersecurity specialist. Read more:
https://www.bytec0de.com/cybersecurity/ethical-hacking-training-course-in-delhi/
What Are The Job Roles In Cyber Security.pdf

Cybersecurity, also known as information technology security or computer security, is the practice of protecting computer systems, networks, devices, and data from unauthorized access, cyberattacks, theft, or damage. It encompasses a range of technologies, processes, and practices designed to safeguard digital assets and ensure confidentiality, integrity, and availability : https://www.bytec0de.com/cybersecurity/
Why Do We Need To Secure Web Applications.pdf

The importance of securing web applications cannot be overstated in today's digital era. By proactively addressing security risks, organizations can protect sensitive data, prevent cyber attacks, maintain user trust, ensure regulatory compliance, sustain business operations, and safeguard their reputation. https://www.bytec0de.com/cybersecurity/web-application-security-course-in-delhi/
What Is Networking And Its Types In IT Sector.pdf

Basic Networking Course in Delhi is one of the most popular courses available in the market and is responsible for more growth opportunities. Aspirants are looking for options to choose from for their personal growth. Then, courses as such can help them to get the path they want to walk on.
Read more: https://www.bytec0de.com/cybersecurity/basic-networking-course-in-delhi/
What Are The Best Ways To Secure Web Application .pdf

Learn web application security course if you want to make your career bright . Bytecode Security offers the best web application security course with job assistance and diploma in cyber security course. read more ; https://www.bytec0de.com/cybersecurity/web-application-security-course-in-delhi/
What are The Types of Pen testing.pdf

Discover the hottest and trendiest Penetration Testing Course in Delhi from the top-notch Penetration Testing Institute in Delhi, which provides top-notch mentorship and top-notch teaching faculty. Additionally, Bytecode Security offers some of the most reliable and accredited penetration testing courses in the Delhi area with the assistance of its esteemed faculty members. These courses provide high-quality instruction in the field of pentesting, which is specifically needed to examine potential threats and vulnerabilities in a target website or IT infrastructure. https://www.bytec0de.com/cybersecurity/penetration-testing-course-in-delhi/
What is Red Hat Used For.pdf

Upgrade your skill set related to the varied backgrounds of Linux Essentials to understand the distinguished fundamental concepts related to Red Hat Training and Certifications in the vicinity of Delhi NCR. Get the info regarding open-source software detailing knowledgeable Red Hat Courses through an explanatory curriculum possessing all basic fundamentals under the guidance of professional system administrators as well as system engineers. https://www.bytec0de.com/red-hat/
What Are The Best Cyber Security.pdf

Bytecode security offers the best cyber security course after 12th online and offline with job assistance.
https://www.bytec0de.com/cybersecurity/
Top 10 Types of Cyber Attacks and How to Prevent cyber attacks.pdf

Prevention: Keep software and systems updated, employ intrusion detection systems
(IDS), and use security patches when available.
Insider Threats:
Prevention: Implement strict access controls, conduct background checks on employees,
and monitor user activity.
Social Engineering Attacks:
Prevention: Educate employees about social engineering tactics, use strong
authentication methods, and implement strict security policies.
IoT Attacks:
Prevention: Change default passwords on IoT devices, segment IoT networks from critical
systems, and update firmware regularly.
In addition to these preventive measures, it's essential to have an incident response plan
in place to mitigate the impact of a cyberattack when prevention fails. Regularly train and
educate employees on cybersecurity best practices and stay informed about the latest
threats and vulnerabilities to adapt your security measures accordingly. Cybersecurity is
an ongoing process, and vigilance is key to staying protected.
Bytecode security offers the best cyber security course online and offline and offers job
assistance after completing the course. If you are serious and want to make your career in
cybersecurity, talk to our career counselor for more information +91 9513805401
What Skills Does A Cybersecurity Analyst Need.pdf

Bytecode Security is the best institute for cyber security course in Delhi. Bytecode Security
offers 1 year diploma course in cyber security online and offline with job assistant.
Bytecode security is known for its quality and effective knowledge. If you want to make
your career in cyber security field. Must visit : https://www.bytec0de.com/cybersecurity/
Why Cyber Security Is Needed.pdf

cybersecurity is essential to protect data, privacy, financial assets, reputation, national security, and critical infrastructure. It plays a vital role in our increasingly digital world, where cyber threats are constantly evolving and becoming more sophisticated. By investing in cybersecurity, individuals, organizations, and governments can mitigate risks and ensure the secure use of technology.
Read More : https://www.bytec0de.com/cybersecurity/
What Are The 5 Steps Of Reverse Engineering.pdf

If you want to make your career in Reverse Engineering, then you would be happy to know
that the best institute Bytecode Security offers best Reverse engineering course with
certification online and offline. We give job assistance after completing course and making you expert in Reverse Engineering.
https://www.bytec0de.com/reverse-engineering-training-course-in-delhi/
Free and effective mobile apps for learning ethical hacking on an Android.pdf

Learning ethical hacking on an Android device is possible using various mobile apps that offer educational content, tutorials, and hands-on practice. Read more :
https://www.bytec0de.com/cybersecurity/ethical-hacking-training-course-in-delhi/
What are the 5 Stages of Penetration.pdf

Learn the hot and happening Penetration Testing Course in Delhi from the Best Penetration Testing Institute in Delhi that offers the best-in-class teaching faculties along with high-grade mentorship. In addition, Bytecode Security, with the help of its eminent faculty members, provides some of the most authentic and accredited Penetration Testing Courses in the vicinity of Delhi to impart quality knowledge in the genre of Pentesting dedicatedly needed to check the possible threats and vulnerabilities in a target IT infrastructure or a website.
Read more :https://www.bytec0de.com/cybersecurity/penetration-testing-course-in-delhi/
What Are The Responsibilities Of AWS.pdf

The responsibilities of an AWS Developer primarily revolve around designing, developing, and maintaining applications that run on the Amazon Web Services (AWS) cloud platform. These developers are skilled in utilizing various AWS services to build scalable, secure, and efficient solutions.
Learn more:
https://www.bytec0de.com/cloud-security/aws-security-training-and-certification-in-delhi/
Difference Between Cyber Forensics and Cyber Security .pdf

Cyber forensics, also known as digital forensics, is a specialized field of forensic science that involves the collection, preservation, analysis, and interpretation of digital evidence to investigate and solve cybercrimes and security incidents. It encompasses a range of techniques and methodologies for examining digital devices, systems, networks, and data to uncover information related to computer-based crimes, incidents, or security breaches.
Learn more:
https://www.bytec0de.com/cybersecurity/ethical-hacking-training-course-in-delhi/
More from Bytecode Security (20)
Top 10 Advantages of Python Programming Language .pdf

Top 10 Advantages of Python Programming Language .pdf
What Are The Best Ways To Secure Web Application .pdf

What Are The Best Ways To Secure Web Application .pdf
Top 10 Types of Cyber Attacks and How to Prevent cyber attacks.pdf

Top 10 Types of Cyber Attacks and How to Prevent cyber attacks.pdf
Free and effective mobile apps for learning ethical hacking on an Android.pdf

Free and effective mobile apps for learning ethical hacking on an Android.pdf
Difference Between Cyber Forensics and Cyber Security .pdf

Difference Between Cyber Forensics and Cyber Security .pdf
Recently uploaded
Switching Careers Slides - JoyceMSullivan SocMediaFin - 2024Jun11.pdf

Joyce M Sullivan, Founder & CEO of SocMediaFin, Inc. shares her "Five Questions - The Story of You", "Reflections - What Matters to You?" and "The Three Circle Exercise" to guide those evaluating what their next move may be in their careers.
Learnings from Successful Jobs Searchers

Are you interested to know what actions help in a job search? This webinar is the summary of several individuals who discussed their job search journey for others to follow. You will learn there are common actions that helped them succeed in their quest for gainful employment.
All Of My Java Codes With A Sample Output.docx

Contains All of the Java Programs from Beginning to the Advanced Concepts that I had Practiced While Learning Java
按照学校原版(ArtEZ文凭证书)ArtEZ艺术学院毕业证快速办理

官方原版办理【(ArtEZ毕业证书)ArtEZ艺术学院毕业证】【176555708微信号】海外认证成绩单、外壳、offer、留信学历认证(永久存档真实可查)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【我们承诺采用的是学校原版纸张(纸质、底色、纹路),我们拥有全套进口原装设备,特殊工艺都是采用不同机器制作,仿真度基本可以达到100%,所有工艺效果都可提前给客户展示,不满意可以根据客户要求进行调整,直到满意为止!】
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【微信176555708】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【微信176555708】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
留信网服务项目:
1、留学生专业人才库服务(留信分析)
2、国(境)学习人员提供就业推荐信服务
3、留学人员区块链存储服务
→ 【关于价格问题(保证一手价格)】
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
选择实体注册公司办理,更放心,更安全!我们的承诺:客户在留信官方认证查询网站查询到认证通过结果后付款,不成功不收费!
Community Skills Building Workshop | PMI Silver Spring Chapter | June 12, 2024

Community Skills Building Workshop | PMI Silver Spring Chapter | June 12, 2024Hector Del Castillo, CPM, CPMM
We recently hosted the much-anticipated Community Skill Builders Workshop during our June online meeting. This event was a culmination of six months of listening to your feedback and crafting solutions to better support your PMI journey. Here’s a look back at what happened and the exciting developments that emerged from our collaborative efforts.
A Gathering of Minds
We were thrilled to see a diverse group of attendees, including local certified PMI trainers and both new and experienced members eager to contribute their perspectives. The workshop was structured into three dynamic discussion sessions, each led by our dedicated membership advocates.
Key Takeaways and Future Directions
The insights and feedback gathered from these discussions were invaluable. Here are some of the key takeaways and the steps we are taking to address them:
• Enhanced Resource Accessibility: We are working on a new, user-friendly resource page that will make it easier for members to access training materials and real-world application guides.
• Structured Mentorship Program: Plans are underway to launch a mentorship program that will connect members with experienced professionals for guidance and support.
• Increased Networking Opportunities: Expect to see more frequent and varied networking events, both virtual and in-person, to help you build connections and foster a sense of community.
Moving Forward
We are committed to turning your feedback into actionable solutions that enhance your PMI journey. This workshop was just the beginning. By actively participating and sharing your experiences, you have helped shape the future of our Chapter’s offerings.
Thank you to everyone who attended and contributed to the success of the Community Skill Builders Workshop. Your engagement and enthusiasm are what make our Chapter strong and vibrant. Stay tuned for updates on the new initiatives and opportunities to get involved. Together, we are building a community that supports and empowers each other on our PMI journeys.
Stay connected, stay engaged, and let’s continue to grow together!
About PMI Silver Spring Chapter
We are a branch of the Project Management Institute. We offer a platform for project management professionals in Silver Spring, MD, and the DC/Baltimore metro area. Monthly meetings facilitate networking, knowledge sharing, and professional development. For more, visit pmissc.org.一比一原版(EUR毕业证)鹿特丹伊拉斯姆斯大学毕业证如何办理

原件一模一样【微信:95270640】【鹿特丹伊拉斯姆斯大学毕业证EUR学位证成绩单】【微信:95270640】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【微信:95270640】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【微信:95270640】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份【微信:95270640】
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
办理鹿特丹伊拉斯姆斯大学毕业证毕业证offerEUR学位证【微信:95270640 】外观非常精致,由特殊纸质材料制成,上面印有校徽、校名、毕业生姓名、专业等信息。
办理鹿特丹伊拉斯姆斯大学毕业证EUR学位证毕业证offer【微信:95270640 】格式相对统一,各专业都有相应的模板。通常包括以下部分:
校徽:象征着学校的荣誉和传承。
校名:学校英文全称
授予学位:本部分将注明获得的具体学位名称。
毕业生姓名:这是最重要的信息之一,标志着该证书是由特定人员获得的。
颁发日期:这是毕业正式生效的时间,也代表着毕业生学业的结束。
其他信息:根据不同的专业和学位,可能会有一些特定的信息或章节。
办理鹿特丹伊拉斯姆斯大学毕业证毕业证offerEUR学位证【微信:95270640 】价值很高,需要妥善保管。一般来说,应放置在安全、干燥、防潮的地方,避免长时间暴露在阳光下。如需使用,最好使用复印件而不是原件,以免丢失。
综上所述,办理鹿特丹伊拉斯姆斯大学毕业证毕业证offerEUR学位证【微信:95270640 】是证明身份和学历的高价值文件。外观简单庄重,格式统一,包括重要的个人信息和发布日期。对持有人来说,妥善保管是非常重要的。
一比一原版(surrey毕业证书)英国萨里大学毕业证成绩单修改如何办理

原版定制【微信:741003700】《(surrey毕业证书)英国萨里大学毕业证学位证成绩单》【微信:741003700】成绩单 、雅思、外壳、留信学历认证永久存档查询,采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份毕业证【Q微信741003700】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【Q微信741003700】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
【关于价格问题(保证一手价格)】
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
Connect to Grow: The power of building networks

In the intricate tapestry of life, connections serve as the vibrant threads that weave together opportunities, experiences, and growth. Whether in personal or professional spheres, the ability to forge meaningful connections opens doors to a multitude of possibilities, propelling individuals toward success and fulfillment.
Eirini is an HR professional with strong passion for technology and semiconductors industry in particular. She started her career as a software recruiter in 2012, and developed an interest for business development, talent enablement and innovation which later got her setting up the concept of Software Community Management in ASML, and to Developer Relations today. She holds a bachelor degree in Lifelong Learning and an MBA specialised in Strategic Human Resources Management. She is a world citizen, having grown up in Greece, she studied and kickstarted her career in The Netherlands and can currently be found in Santa Clara, CA.
A Guide to a Winning Interview June 2024

This webinar is an in-depth review of the interview process. Preparation is a key element to acing an interview. Learn the best approaches from the initial phone screen to the face-to-face meeting with the hiring manager. You will hear great answers to several standard questions, including the dreaded “Tell Me About Yourself”.
在线办理(UOIT毕业证书)安大略省理工大学毕业证在读证明一模一样

原件一模一样【微信:bwp0011】《(UOIT毕业证书)安大略省理工大学毕业证》【微信:bwp0011】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问微bwp0011
【主营项目】
一.毕业证【微bwp0011】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微bwp0011】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Gabrielle M. A. Sinaga Portfolio, Film Student (2024)

My portfolio as a highly motivated film student pursuing a career in Yogyakarta.
按照学校原版(UofT文凭证书)多伦多大学毕业证快速办理

快速办理【(UofT毕业证书)多伦多大学毕业证】【176555708微信号】硕士毕业证成绩单、外壳、offer、留信学历认证(永久存档真实可查)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【我们承诺采用的是学校原版纸张(纸质、底色、纹路),我们拥有全套进口原装设备,特殊工艺都是采用不同机器制作,仿真度基本可以达到100%,所有工艺效果都可提前给客户展示,不满意可以根据客户要求进行调整,直到满意为止!】
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【微信176555708】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【微信176555708】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
留信网服务项目:
1、留学生专业人才库服务(留信分析)
2、国(境)学习人员提供就业推荐信服务
3、留学人员区块链存储服务
→ 【关于价格问题(保证一手价格)】
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
选择实体注册公司办理,更放心,更安全!我们的承诺:客户在留信官方认证查询网站查询到认证通过结果后付款,不成功不收费!
一比一原版布拉德福德大学毕业证(bradford毕业证)如何办理

一模一样【微信:A575476】【布拉德福德大学毕业证(bradford毕业证)成绩单Offer】【微信:A575476】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【微信:A575476】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【微信:A575476】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
办理阿卡迪亚大学毕业证(uvic毕业证)本科文凭证书原版一模一样

原版一模一样【微信:741003700 】【阿卡迪亚大学毕业证(uvic毕业证)本科文凭证书】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
在线制作加拿大萨省大学毕业证文凭证书实拍图原版一模一样

原版一模一样【微信:741003700 】【加拿大萨省大学毕业证文凭证书】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
一比一原版美国西北大学毕业证(NWU毕业证书)学历如何办理

原版办理【微信号:BYZS866】【美国西北大学毕业证(NWU毕业证书)】【微信号:BYZS866】《成绩单、外壳、雅思、offer、真实留信官方学历认证(永久存档/真实可查)》采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【我们承诺采用的是学校原版纸张(纸质、底色、纹路)我们拥有全套进口原装设备,特殊工艺都是采用不同机器制作,仿真度基本可以达到100%,所有工艺效果都可提前给客户展示,不满意可以根据客户要求进行调整,直到满意为止!】
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【微信号BYZS866】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【微信号BYZS866】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
留信网服务项目:
1、留学生专业人才库服务(留信分析)
2、国(境)学习人员提供就业推荐信服务
3、留学人员区块链存储服务
【关于价格问题(保证一手价格)】
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
选择实体注册公司办理,更放心,更安全!我们的承诺:客户在留信官方认证查询网站查询到认证通过结果后付款,不成功不收费!
官方认证美国旧金山州立大学毕业证学位证书案例原版一模一样

原版一模一样【微信:741003700 】【美国旧金山州立大学毕业证学位证书】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
How to overcome obstacles in the way of success.pdf

Success is often not achievable without facing and overcoming obstacles along the way. To reach our goals and achieve success, it is important to understand and resolve the obstacles that come in our way.
In this article, we will discuss the various obstacles that hinder success, strategies to overcome them, and examples of individuals who have successfully surmounted their obstacles.
Recently uploaded (20)
Switching Careers Slides - JoyceMSullivan SocMediaFin - 2024Jun11.pdf

Switching Careers Slides - JoyceMSullivan SocMediaFin - 2024Jun11.pdf
Community Skills Building Workshop | PMI Silver Spring Chapter | June 12, 2024

Community Skills Building Workshop | PMI Silver Spring Chapter | June 12, 2024
Gabrielle M. A. Sinaga Portfolio, Film Student (2024)

Gabrielle M. A. Sinaga Portfolio, Film Student (2024)
How to overcome obstacles in the way of success.pdf

How to overcome obstacles in the way of success.pdf
Software for Finding vulnerabilities in programs.pdf
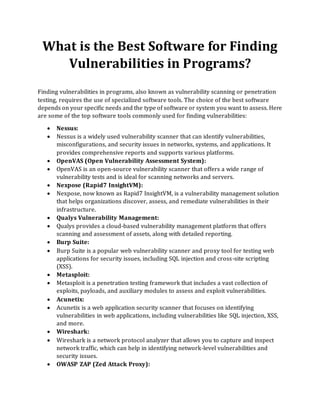
- 1. What is the Best Software for Finding Vulnerabilities in Programs? Finding vulnerabilities in programs, also known as vulnerability scanning or penetration testing, requires the use of specialized software tools. The choice of the best software depends on your specific needs and the type of software or system you want to assess. Here are some of the top software tools commonly used for finding vulnerabilities: • Nessus: • Nessus is a widely used vulnerability scanner that can identify vulnerabilities, misconfigurations, and security issues in networks, systems, and applications. It provides comprehensive reports and supports various platforms. • OpenVAS (Open Vulnerability Assessment System): • OpenVAS is an open-source vulnerability scanner that offers a wide range of vulnerability tests and is ideal for scanning networks and servers. • Nexpose (Rapid7 InsightVM): • Nexpose, now known as Rapid7 InsightVM, is a vulnerability management solution that helps organizations discover, assess, and remediate vulnerabilities in their infrastructure. • Qualys Vulnerability Management: • Qualys provides a cloud-based vulnerability management platform that offers scanning and assessment of assets, along with detailed reporting. • Burp Suite: • Burp Suite is a popular web vulnerability scanner and proxy tool for testing web applications for security issues, including SQL injection and cross-site scripting (XSS). • Metasploit: • Metasploit is a penetration testing framework that includes a vast collection of exploits, payloads, and auxiliary modules to assess and exploit vulnerabilities. • Acunetix: • Acunetix is a web application security scanner that focuses on identifying vulnerabilities in web applications, including vulnerabilities like SQL injection, XSS, and more. • Wireshark: • Wireshark is a network protocol analyzer that allows you to capture and inspect network traffic, which can help in identifying network-level vulnerabilities and security issues. • OWASP ZAP (Zed Attack Proxy):
- 2. • OWASP ZAP is an open-source web application security scanner that helps you find vulnerabilities in web applications by performing automated and manual testing. • Snort: • Snort is an open-source intrusion detection and prevention system (IDPS) that can be used to monitor network traffic for suspicious activity and potential vulnerabilities. • Qualys Web Application Scanning: • This tool specializes in scanning and assessing web applications for security vulnerabilities and weaknesses. • Retina CS: • Retina CS by BeyondTrust is a vulnerability management solution that provides comprehensive scanning, assessment, and reporting capabilities. • Aircrack-ng: • Aircrack-ng is a set of tools for assessing Wi-Fi network security, including cracking WEP and WPA/WPA2 keys and performing various network attacks. When choosing a vulnerability scanning tool, consider factors such as your budget, the types of systems and applications you need to assess, the level of automation required, and the depth of reporting. Many organizations use a combination of these tools to conduct thorough vulnerability assessments and penetration tests. Additionally, it's crucial to follow ethical hacking and responsible disclosure practices when performing security assessments on systems that you do not own or have explicit permission to test. Bytecode security provides 1 year diploma course in cybersecurity field. If you are looking for best career opportunity , you can enroll now 9513805401
