What Are The Best Cyber Security.pdf
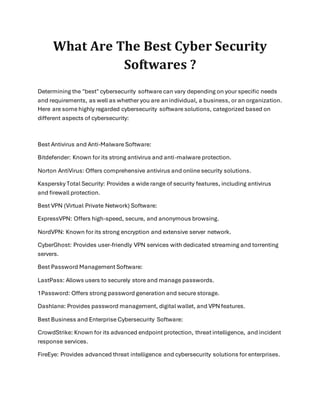
- 1. What Are The Best Cyber Security Softwares ? Determining the "best" cybersecurity software can vary depending on your specific needs and requirements, as well as whether you are anindividual, a business, or an organization. Here are some highly regarded cybersecurity software solutions, categorized based on different aspects of cybersecurity: Best Antivirus and Anti-Malware Software: Bitdefender: Known for its strong antivirus and anti-malware protection. Norton AntiVirus: Offers comprehensive antivirus and online security solutions. Kaspersky Total Security: Provides a wide range of security features, including antivirus and firewall protection. Best VPN (Virtual Private Network) Software: ExpressVPN: Offers high-speed, secure, and anonymous browsing. NordVPN: Known for its strong encryption and extensive server network. CyberGhost: Provides user-friendly VPN services with dedicated streaming and torrenting servers. Best Password Management Software: LastPass: Allows users to securely store and manage passwords. 1Password: Offers strong password generation and secure storage. Dashlane: Provides password management, digital wallet, and VPN features. Best Business and Enterprise Cybersecurity Software: CrowdStrike: Known for its advanced endpoint protection, threat intelligence, and incident response services. FireEye: Provides advanced threat intelligence and cybersecurity solutions for enterprises.
- 2. Fortinet: Offers a wide range of cybersecurity solutions for businesses, including firewalls and SD-WAN. Best Network Security Software: Cisco Umbrella: Provides cloud-based security for DNS and internet traffic. Palo Alto Networks: Offers next-generation firewalls and advanced threat prevention. Check Point: Known for its comprehensive network security solutions. Best Cloud Security Software: Amazon Web Services (AWS) Security: Provides a range of cloud security services, including AWS Identity and Access Management (IAM). Microsoft Azure Security: Offers various tools and services for securing Azure cloud resources. Google Cloud Platform (GCP) Security: Includes features like Identity and Access Management (IAM) for securing GCP services. Best Email Security Software: Proofpoint: Provides email security, threat protection, and data loss prevention. Barracuda Email Security: Offers email security solutions,including anti-phishing and anti- spam features. Mimecast: Specializes in email security, archiving, and continuity services. Best Identity and Access Management (IAM) Software: Okta: Offers identity and access management for secure user authentication and authorization. Ping Identity: Provides identity management solutions for secure access and single sign-on (SSO). The choice of cybersecurity software should be based on your specific needs, budget, and the level of protection required. It's also essential to keep your software and systems regularly updated and patched to maintain a strong cybersecurity posture. Consulting with cybersecurity experts or conducting a risk assessment can help tailor your cybersecurity measures to your unique circumstances.
- 3. Bytecode security offers the best cyber security course in Delhi with placement assistance. Quality education is our motive, and we provide high qualified skilled trainers. If you want to make your career in ethical hacking, talk to career counselor: +91 9513805401
