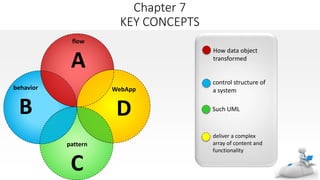
The document discusses various modeling techniques used in requirements analysis for web applications (WebApps), including:
1) Content modeling to identify and describe all content objects and their relationships.
2) Interaction modeling using use cases, sequence diagrams, state diagrams, and prototypes to describe how users interact.
3) Functional modeling to define all necessary operations and processing functions implied by usage scenarios.
The techniques help analysts understand WebApp requirements by modeling key elements like content, interactions, and functions.