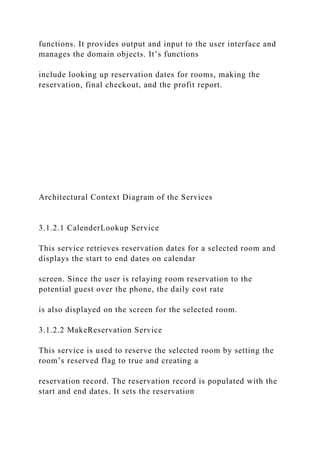
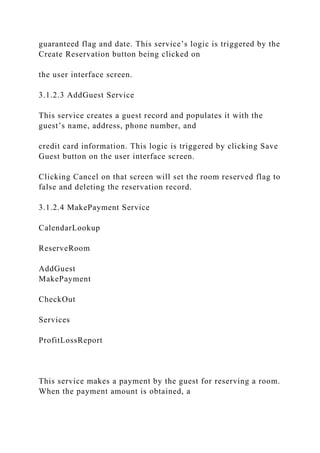
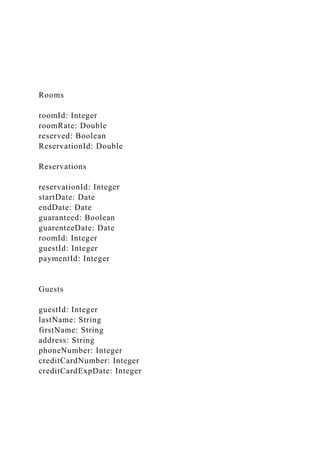
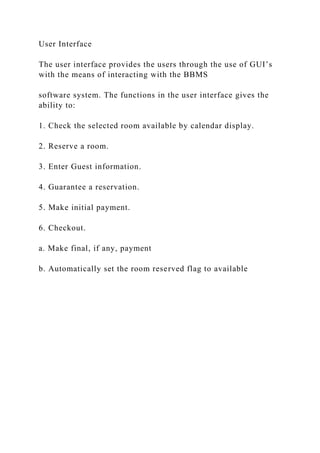
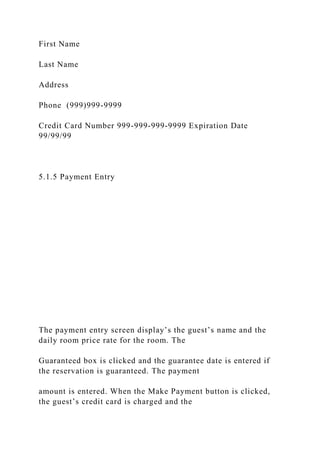
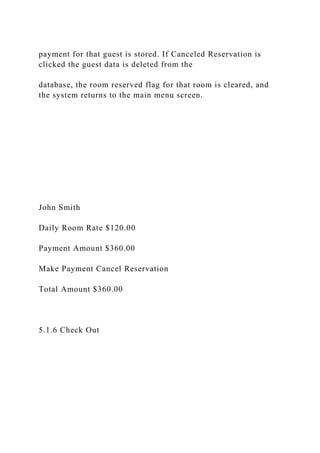
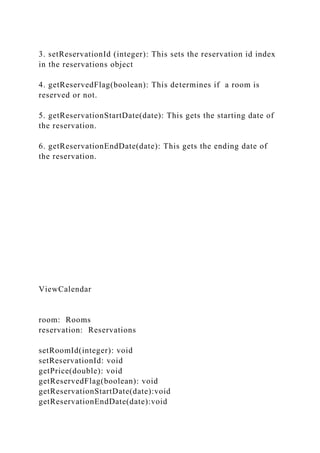
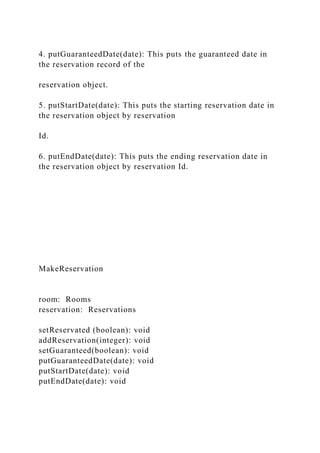
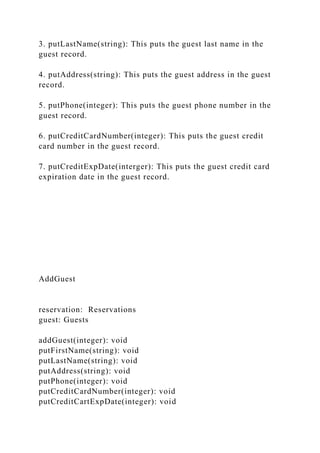
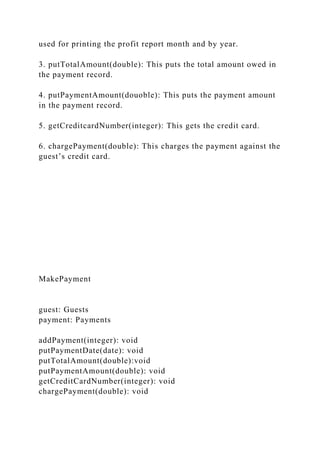
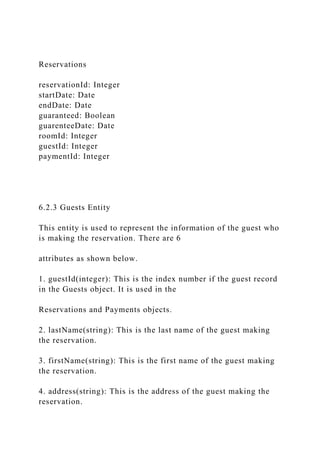
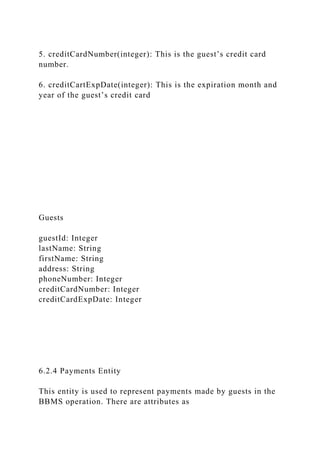
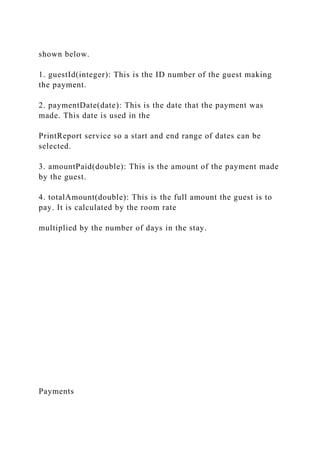
The document is a software design specification for a management system for a bed and breakfast operation, detailing requirements for reservations, financial transactions, and user interface elements. It covers module decomposition, interdependencies, and data structure, specifying how the system will manage guest reservations and operations. The outline includes descriptions of services, domain objects, and an architectural context diagram for understanding the system’s components.