Report
Share
Recommended
CASE tools and their effects on software quality

types of CASE tools ,its benefits and its effects on software quality
Computer Aided Software Engineering

What is Computer Aided Software Engineering? Define its different Tools. How organizations uses these tools. Advantages and Disadvantages of CASE tools. Types of different CASE Tools.
Computer aided software engineering

Define Computer aided Software Engineering and different CASE tools that how organizations uses these tools. Categories and Types of CASE Tools.
Recommended
CASE tools and their effects on software quality

types of CASE tools ,its benefits and its effects on software quality
Computer Aided Software Engineering

What is Computer Aided Software Engineering? Define its different Tools. How organizations uses these tools. Advantages and Disadvantages of CASE tools. Types of different CASE Tools.
Computer aided software engineering

Define Computer aided Software Engineering and different CASE tools that how organizations uses these tools. Categories and Types of CASE Tools.
Case tools

CASE tool and its usage in mechanized software development.
Various type of case tools, application of case tools,
Computer aided machine drawing manual

This document is an Instruction manual for Computer aided machine drawing
Subject: Computer aided machine drawing (CAMD)
Syllabus contest is as per VTU, Belagavi, India.
Notes Compiled By: Hareesha N Gowda, Assistant Professor, DSCE, Bengaluru-78.
Presentaties seminar rethink the desktop 20.01.2011

Presentaties van Citrix, Microsoft en Centric die gegeven zijn tijdens het seminar 'Rethink the Desktop op 20 januari 2011.
VMworld 2013: Developer Services on vCloud Hybrid Services 

VMworld 2013
Raja Krishnasamy, VMware
Sunder Parameswaran, VMware
Learn more about VMworld and register at http://www.vmworld.com/index.jspa?src=socmed-vmworld-slideshare
Microsoft & Citrix Product And Solution Alignment

A collection of slides that outlines the product alignment between Citrix & Microsoft in the virtualization space.
Serverless Computing, AWS Way by SourceFuse Technologies 

Serverless Computing is only the next step in server evolution, they bring in efficiency, such that developers can focus on building great applications and services in a cost-effective manner without the operational overhead of traditional application development and deployment.
Explore the presentation here as given by Manpreet Singh, CTO, SourceFuse, in a webinar organized by AWS on “Serverless Computing”
The presentation talks in depth about Serverless Computing use case, detailing out Lambda and case studies on the same.
Serverless Computing, AWS Way: SourceFuse Technologies 

Serverless Computing is only the next step in server evolution, they bring in efficiency, such that developers can focus on building great applications and services in a cost-effective manner without the operational overhead of traditional application development and deployment.
Explore the presentation here as given by Manpreet Singh, CTO, SourceFuse, in a webinar organized by AWS on “Serverless Computing”
The presentation talks in depth about Serverless Computing use case, detailing out Lambda and case studies on the same.
AWS Chicago user group: AWS Platform for .NET Developers

AWS Chicago user group: AWS Platform for .NET Developers
Amit Jha, Developer Advocate Microsoft/.NET at AWS
Serverless Development To Production Pipeline

What does the development environment to production pipeline look like? In this presentation we look at all the tools and services needed to effectively build and deploy applications!
Student Developer Kit for Developing Applications

The presentation provide the list of tools students can use to develop small and medium scale application without paying any money./
1. Github (https://github.com)
2. VSCode (https://code.visualstudio.com/)
3. IntelliJ
(www.intellij.com)
4. Datadog(https://www.datadoghq.com/)
5. ApyHub ( https://apyhub.com/catalog)
6. Freshdesk
(https://freshdesk.com)
Jak nie zwariować z architekturą Serverless?

Architektura serverless zyskuje na popularności każdego dnia. Większość developerów napotka to na swojej drodze kariery. Jak się z tym zmierzyć, jakich narzędzi użyć aby nie zwariować i uciec w Bieszczady? Jak wdrożyć sprawdzoną strukturę? Porozmawiajmy o tym jak dość płynnie wejść w świat architektury typu serverless.
More Related Content
Viewers also liked
Case tools

CASE tool and its usage in mechanized software development.
Various type of case tools, application of case tools,
Computer aided machine drawing manual

This document is an Instruction manual for Computer aided machine drawing
Subject: Computer aided machine drawing (CAMD)
Syllabus contest is as per VTU, Belagavi, India.
Notes Compiled By: Hareesha N Gowda, Assistant Professor, DSCE, Bengaluru-78.
Viewers also liked (6)
Similar to Software Design Portfolio
Presentaties seminar rethink the desktop 20.01.2011

Presentaties van Citrix, Microsoft en Centric die gegeven zijn tijdens het seminar 'Rethink the Desktop op 20 januari 2011.
VMworld 2013: Developer Services on vCloud Hybrid Services 

VMworld 2013
Raja Krishnasamy, VMware
Sunder Parameswaran, VMware
Learn more about VMworld and register at http://www.vmworld.com/index.jspa?src=socmed-vmworld-slideshare
Microsoft & Citrix Product And Solution Alignment

A collection of slides that outlines the product alignment between Citrix & Microsoft in the virtualization space.
Serverless Computing, AWS Way by SourceFuse Technologies 

Serverless Computing is only the next step in server evolution, they bring in efficiency, such that developers can focus on building great applications and services in a cost-effective manner without the operational overhead of traditional application development and deployment.
Explore the presentation here as given by Manpreet Singh, CTO, SourceFuse, in a webinar organized by AWS on “Serverless Computing”
The presentation talks in depth about Serverless Computing use case, detailing out Lambda and case studies on the same.
Serverless Computing, AWS Way: SourceFuse Technologies 

Serverless Computing is only the next step in server evolution, they bring in efficiency, such that developers can focus on building great applications and services in a cost-effective manner without the operational overhead of traditional application development and deployment.
Explore the presentation here as given by Manpreet Singh, CTO, SourceFuse, in a webinar organized by AWS on “Serverless Computing”
The presentation talks in depth about Serverless Computing use case, detailing out Lambda and case studies on the same.
AWS Chicago user group: AWS Platform for .NET Developers

AWS Chicago user group: AWS Platform for .NET Developers
Amit Jha, Developer Advocate Microsoft/.NET at AWS
Serverless Development To Production Pipeline

What does the development environment to production pipeline look like? In this presentation we look at all the tools and services needed to effectively build and deploy applications!
Student Developer Kit for Developing Applications

The presentation provide the list of tools students can use to develop small and medium scale application without paying any money./
1. Github (https://github.com)
2. VSCode (https://code.visualstudio.com/)
3. IntelliJ
(www.intellij.com)
4. Datadog(https://www.datadoghq.com/)
5. ApyHub ( https://apyhub.com/catalog)
6. Freshdesk
(https://freshdesk.com)
Jak nie zwariować z architekturą Serverless?

Architektura serverless zyskuje na popularności każdego dnia. Większość developerów napotka to na swojej drodze kariery. Jak się z tym zmierzyć, jakich narzędzi użyć aby nie zwariować i uciec w Bieszczady? Jak wdrożyć sprawdzoną strukturę? Porozmawiajmy o tym jak dość płynnie wejść w świat architektury typu serverless.
Windows 2008 R2 Virtualization

Presentación sobre Windows 2008 realizada en la Fundación Omar Dengo en el TechBoot Camp 2009.
Saludos,
Eduardo Castro – Microsoft SQL Server MVP
http://mswindowscr.org
http://comunidadwindows.org
Costa Rica
DevTest Portfolio Overview

DevTest solutions is a suite of applications focused on shortening dev/test cycles, improving quality, reducing infrastructure spend and speeding time-to-market. DevTest Solutions help you on the path towards enterprise DevOps. The Application Economy is here. You’ll need solid tools to take your place in it.
For more information on DevOps solutions from CA Technologies, please visit: http://bit.ly/1wbjjqX
Similar to Software Design Portfolio (20)
Presentaties seminar rethink the desktop 20.01.2011

Presentaties seminar rethink the desktop 20.01.2011
VMworld 2013: Developer Services on vCloud Hybrid Services 

VMworld 2013: Developer Services on vCloud Hybrid Services
Microsoft & Citrix Product And Solution Alignment

Microsoft & Citrix Product And Solution Alignment
Serverless Computing, AWS Way by SourceFuse Technologies 

Serverless Computing, AWS Way by SourceFuse Technologies
Serverless Computing, AWS Way: SourceFuse Technologies 

Serverless Computing, AWS Way: SourceFuse Technologies
AWS Chicago user group: AWS Platform for .NET Developers

AWS Chicago user group: AWS Platform for .NET Developers
Recently uploaded
zkStudyClub - Reef: Fast Succinct Non-Interactive Zero-Knowledge Regex Proofs

This paper presents Reef, a system for generating publicly verifiable succinct non-interactive zero-knowledge proofs that a committed document matches or does not match a regular expression. We describe applications such as proving the strength of passwords, the provenance of email despite redactions, the validity of oblivious DNS queries, and the existence of mutations in DNA. Reef supports the Perl Compatible Regular Expression syntax, including wildcards, alternation, ranges, capture groups, Kleene star, negations, and lookarounds. Reef introduces a new type of automata, Skipping Alternating Finite Automata (SAFA), that skips irrelevant parts of a document when producing proofs without undermining soundness, and instantiates SAFA with a lookup argument. Our experimental evaluation confirms that Reef can generate proofs for documents with 32M characters; the proofs are small and cheap to verify (under a second).
Paper: https://eprint.iacr.org/2023/1886
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

In questo evento online gratuito, organizzato dalla Community Italiana di UiPath, potrai esplorare le nuove funzionalità di Autopilot, il tool che integra l'Intelligenza Artificiale nei processi di sviluppo e utilizzo delle Automazioni.
📕 Vedremo insieme alcuni esempi dell'utilizzo di Autopilot in diversi tool della Suite UiPath:
Autopilot per Studio Web
Autopilot per Studio
Autopilot per Apps
Clipboard AI
GenAI applicata alla Document Understanding
👨🏫👨💻 Speakers:
Stefano Negro, UiPath MVPx3, RPA Tech Lead @ BSP Consultant
Flavio Martinelli, UiPath MVP 2023, Technical Account Manager @UiPath
Andrei Tasca, RPA Solutions Team Lead @NTT Data
Pushing the limits of ePRTC: 100ns holdover for 100 days

At WSTS 2024, Alon Stern explored the topic of parametric holdover and explained how recent research findings can be implemented in real-world PNT networks to achieve 100 nanoseconds of accuracy for up to 100 days.
Video Streaming: Then, Now, and in the Future

In his public lecture, Christian Timmerer provides insights into the fascinating history of video streaming, starting from its humble beginnings before YouTube to the groundbreaking technologies that now dominate platforms like Netflix and ORF ON. Timmerer also presents provocative contributions of his own that have significantly influenced the industry. He concludes by looking at future challenges and invites the audience to join in a discussion.
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Monitoring and observability aren’t traditionally found in software curriculums and many of us cobble this knowledge together from whatever vendor or ecosystem we were first introduced to and whatever is a part of your current company’s observability stack.
While the dev and ops silo continues to crumble….many organizations still relegate monitoring & observability as the purview of ops, infra and SRE teams. This is a mistake - achieving a highly observable system requires collaboration up and down the stack.
I, a former op, would like to extend an invitation to all application developers to join the observability party will share these foundational concepts to build on:
Quantum Computing: Current Landscape and the Future Role of APIs

The current state of quantum computing and the role of APIs to take it mainstream.
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
By Design, not by Accident - Agile Venture Bolzano 2024

As presented at the Agile Venture Bolzano, 4.06.2024
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
Removing Uninteresting Bytes in Software Fuzzing

Imagine a world where software fuzzing, the process of mutating bytes in test seeds to uncover hidden and erroneous program behaviors, becomes faster and more effective. A lot depends on the initial seeds, which can significantly dictate the trajectory of a fuzzing campaign, particularly in terms of how long it takes to uncover interesting behaviour in your code. We introduce DIAR, a technique designed to speedup fuzzing campaigns by pinpointing and eliminating those uninteresting bytes in the seeds. Picture this: instead of wasting valuable resources on meaningless mutations in large, bloated seeds, DIAR removes the unnecessary bytes, streamlining the entire process.
In this work, we equipped AFL, a popular fuzzer, with DIAR and examined two critical Linux libraries -- Libxml's xmllint, a tool for parsing xml documents, and Binutil's readelf, an essential debugging and security analysis command-line tool used to display detailed information about ELF (Executable and Linkable Format). Our preliminary results show that AFL+DIAR does not only discover new paths more quickly but also achieves higher coverage overall. This work thus showcases how starting with lean and optimized seeds can lead to faster, more comprehensive fuzzing campaigns -- and DIAR helps you find such seeds.
- These are slides of the talk given at IEEE International Conference on Software Testing Verification and Validation Workshop, ICSTW 2022.
Recently uploaded (20)
zkStudyClub - Reef: Fast Succinct Non-Interactive Zero-Knowledge Regex Proofs

zkStudyClub - Reef: Fast Succinct Non-Interactive Zero-Knowledge Regex Proofs
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™
Pushing the limits of ePRTC: 100ns holdover for 100 days

Pushing the limits of ePRTC: 100ns holdover for 100 days
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf
Quantum Computing: Current Landscape and the Future Role of APIs

Quantum Computing: Current Landscape and the Future Role of APIs
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
By Design, not by Accident - Agile Venture Bolzano 2024

By Design, not by Accident - Agile Venture Bolzano 2024
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
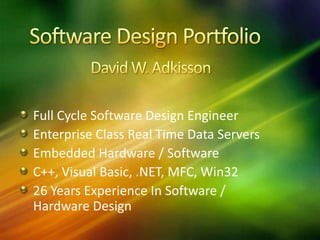
Software Design Portfolio
- 1. Software Design Portfolio David W. Adkisson Full Cycle Software Design Engineer Enterprise Class Real Time Data Servers Embedded Hardware / Software C++, Visual Basic, .NET, MFC, Win32 26 Years Experience In Software / Hardware Design
- 2. webVUE HMI Server And Client Sample Fill
- 3. webVUE HMI Server And Client Sample Fill
- 4. webVUE HMI Server And Client Sample Fill
- 5. webVUE HMI Server And Client Sample Fill
- 6. webVUE HMI Server And Client Sample Fill
- 7. webVUE HMI Server And Client Sample Fill
- 8. webVUE HMI Server And Client Sample Fill
- 10. Analytic Studio
- 11. Analytic Studio
- 12. Analytic Studio
- 13. OPC Server Sample Fill
- 17. Printed Circuit Design Asthma Metered Inhaler For FDA Drug Certification
- 18. Printed Circuit Design Asthma Metered Inhaler For FDA Drug Certification
- 19. Printed Circuit Design Asthma Metered Inhaler For FDA Drug Certification