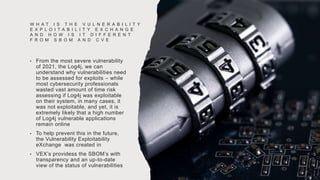
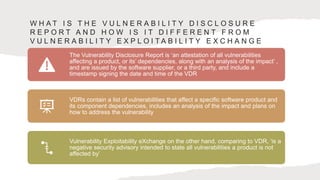
This document discusses the importance of automation in cybersecurity vulnerability management using the Software Bill of Materials (SBOM) and Vulnerability Exploitability eXchange (VEX). It highlights regulatory compliance challenges faced by organizations, the necessity of prioritizing cybersecurity, and proposes solutions for automating SBOM and VEX implementation. Additionally, it examines the impacts of SBOMs on UK and US cyber diplomacy and the frameworks developed to enhance collaboration between the two countries on cybersecurity standards.





















![D E C L A R AT I O N S
Funding: This work has been
supported by the PETRAS National
Centre of Excellence for IoT
Systems Cybersecurity, which has
been funded by the UK EPSRC
[under grant number
EP/S035362/1], the Software
Sustainability Institute [grant
number: EP/S021779/1], and by
the Cisco Research Centre [grant
number CG1525381].
Acknowledgements: Eternal
gratitude to the Fulbright Visiting
Scholar Project](https://image.slidesharecdn.com/sbomb-230916135640-5e220b8a/85/Software-Bill-of-Materials-and-the-Vulnerability-Exploitability-eXchange-37-320.jpg)