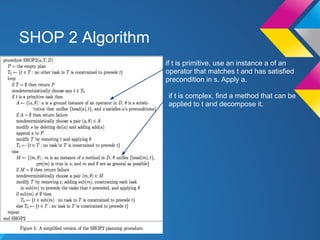
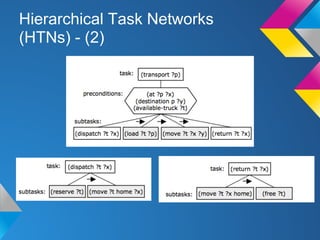
SHOP 2 is a hierarchical task network (HTN) planner developed in LISP that was awarded for its performance in the 2002 international planning competition. It improves upon SHOP by allowing partially ordered tasks and subtasks, and supports many PDDL features. SHOP 2 decomposes complex tasks into subtasks through methods until reaching primitive tasks. It has been applied to domains like video games, evacuation planning, evaluating terrorist threats, and automated composition of web services.
![Features - Basic Elements
Specify a domain description that consists of a set of
methods, operators and axioms.
>Syntactical Note
A variable is preceded by "?" symbol.
A comment is preceded by ";".
● Tasks
Action to be done. They can be either primitive or
complex.
(s t1 t2 ... tn)
A primitive task is preceded by "!" symbol.
● Operators
Indicates how a primitive task can be executed.
(:operator h P D A [c])](https://image.slidesharecdn.com/shop2presentationslide-130606172253-phpapp02/85/Shop-2-presentation-slide-13-320.jpg)
![Features - Basic Elements - (2)
● Methods
How to decompose a complex task.
(:method h [n1] C1 T1 [n2] C2 T2 ... [nk] Ck
Tk)
● Axioms
Used to infer precondition that are not explicitly
asserted in our current state (e.g. including quantifiers,
implications etc).
(:- a [name1] E1 ... [namen] En)
(:- head tail)
Which means that head is true if tail is true (Horn
clauses).](https://image.slidesharecdn.com/shop2presentationslide-130606172253-phpapp02/85/Shop-2-presentation-slide-14-320.jpg)