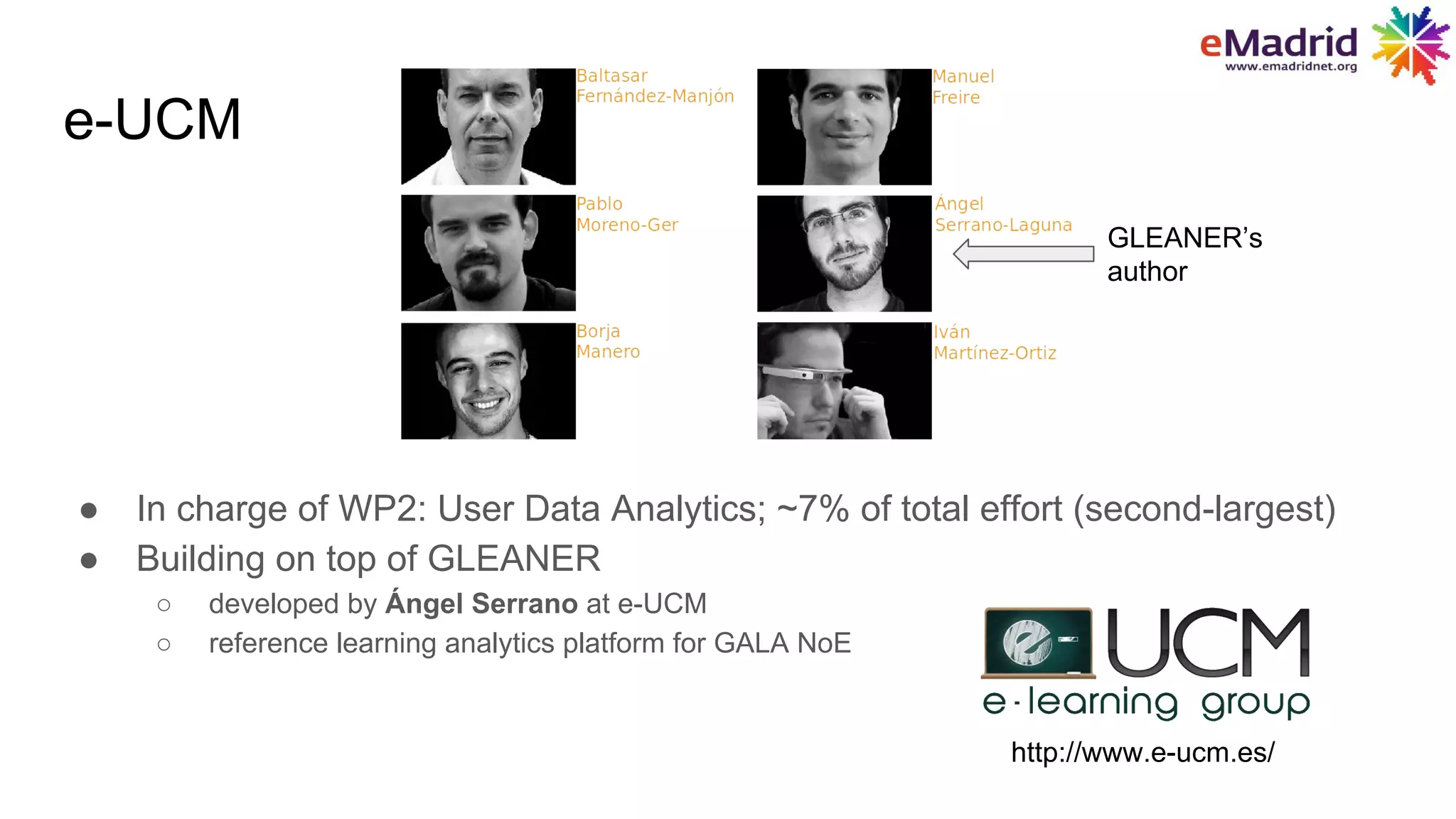
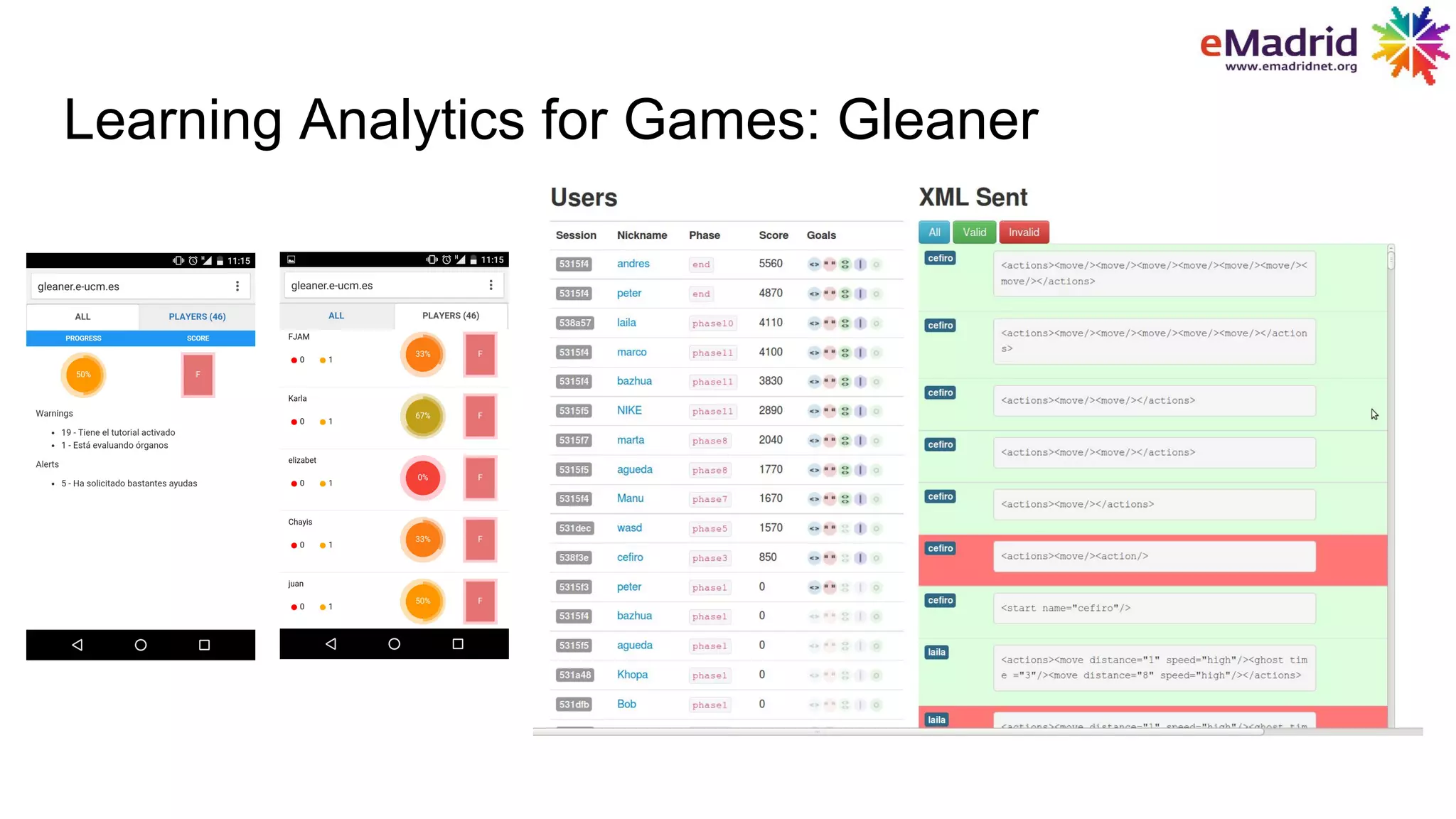
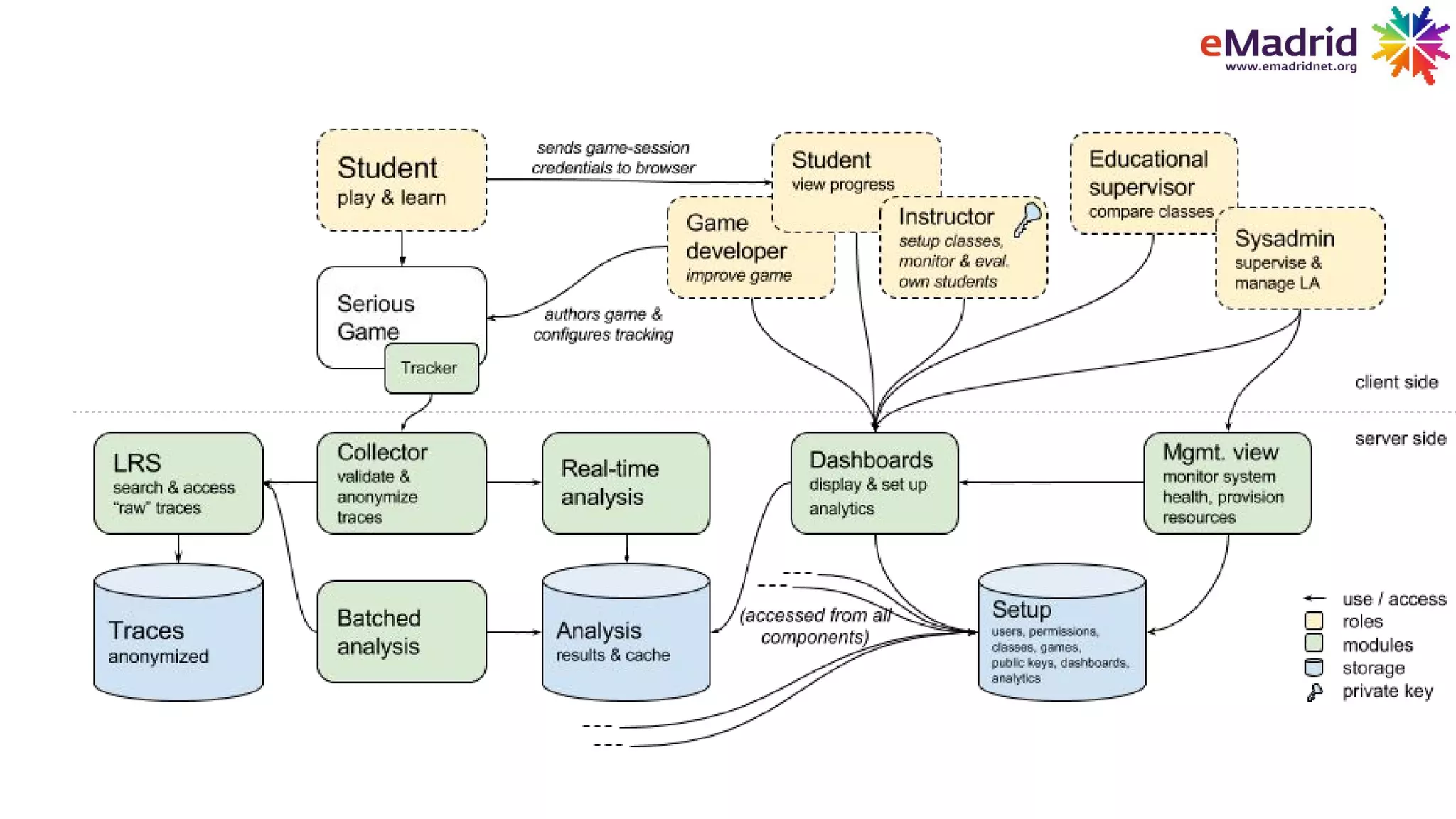
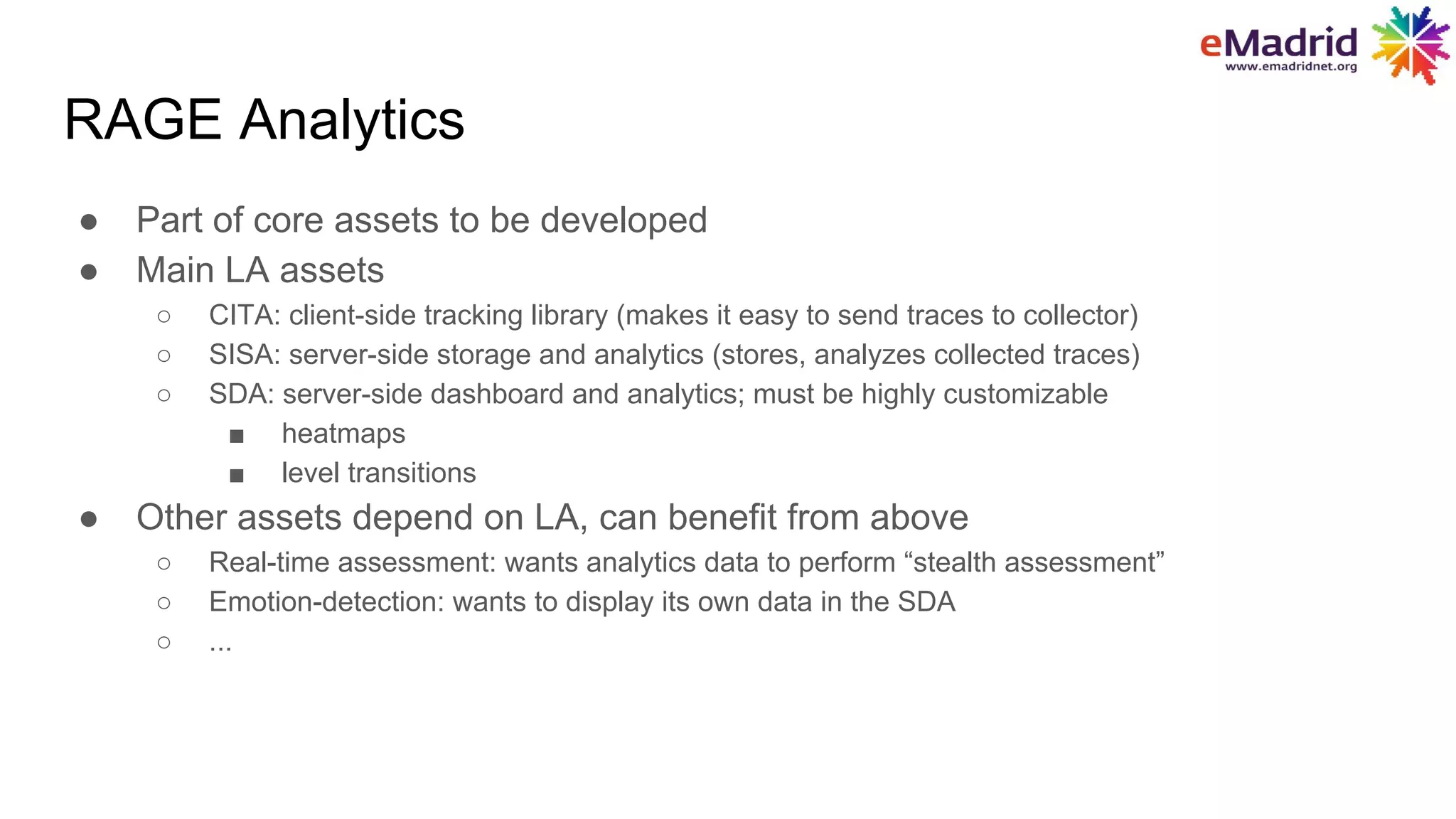
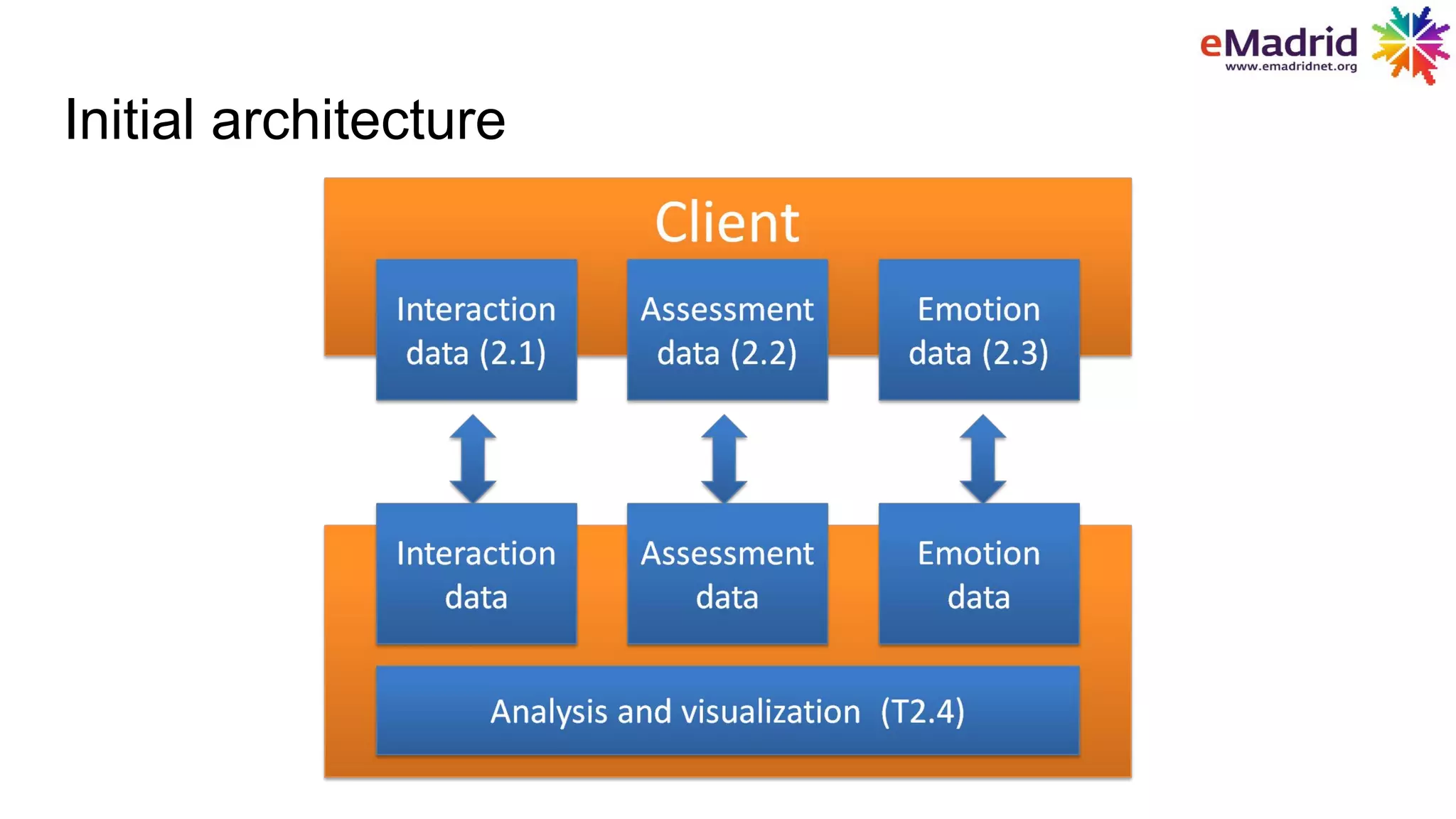
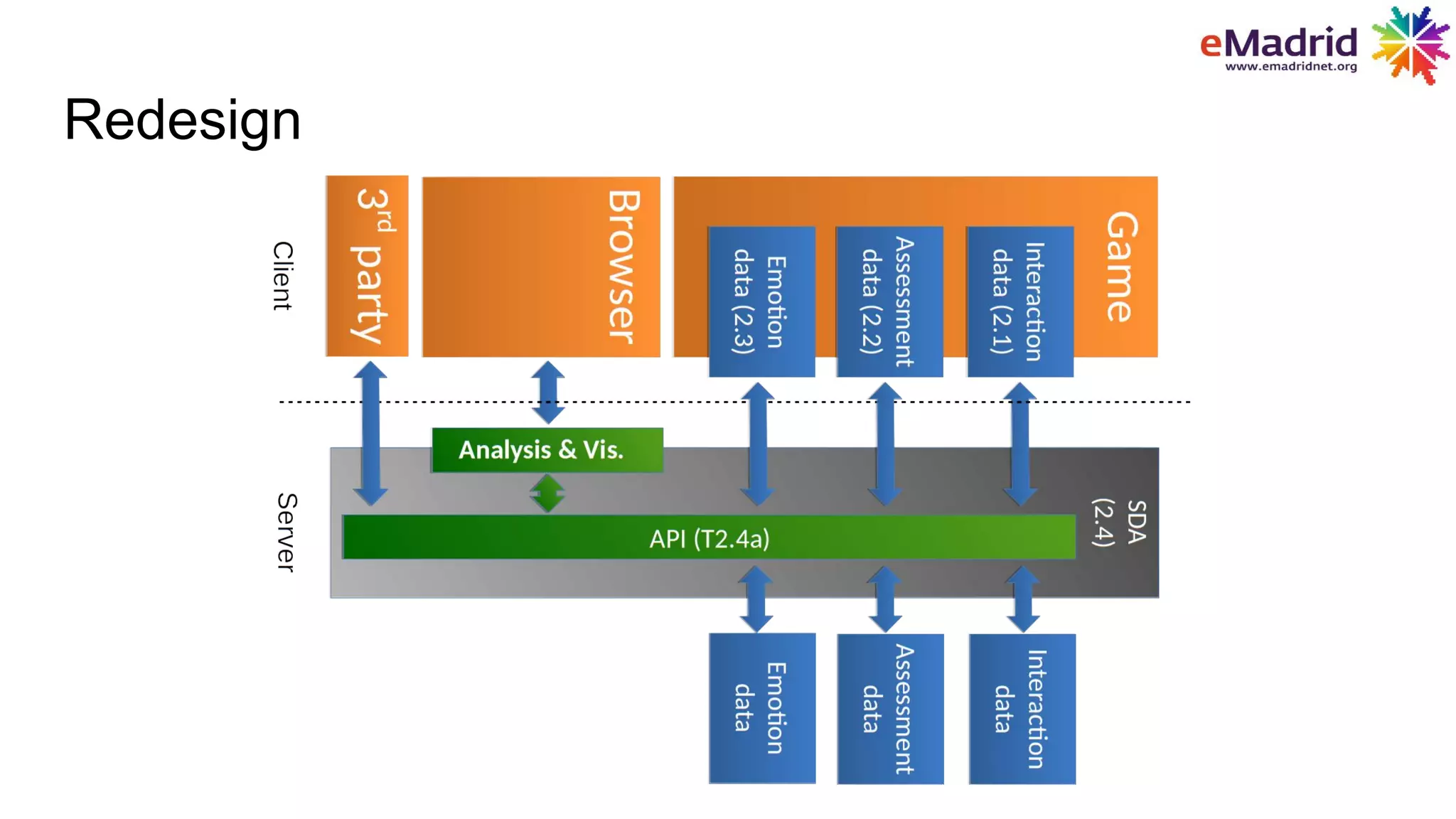
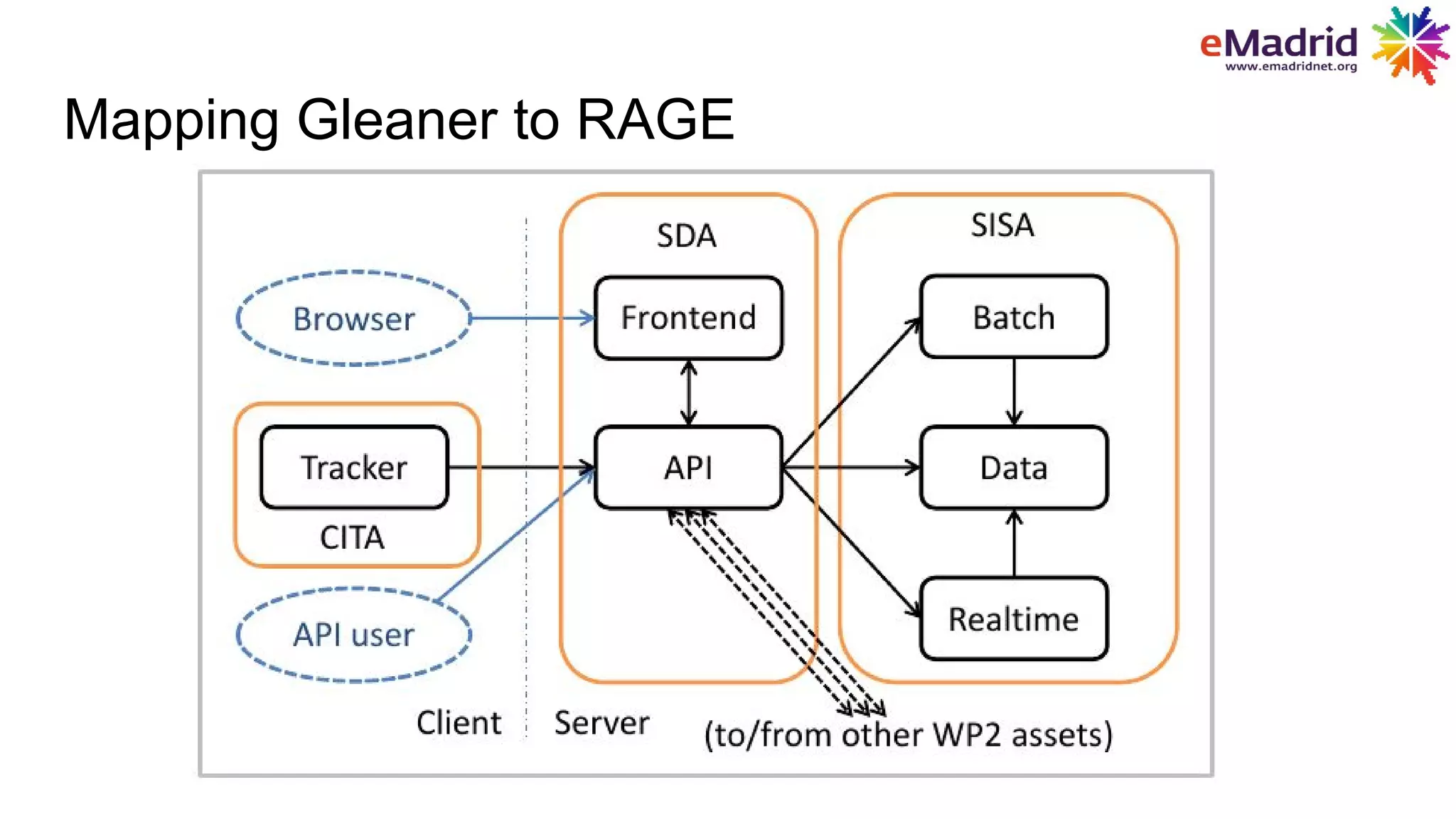
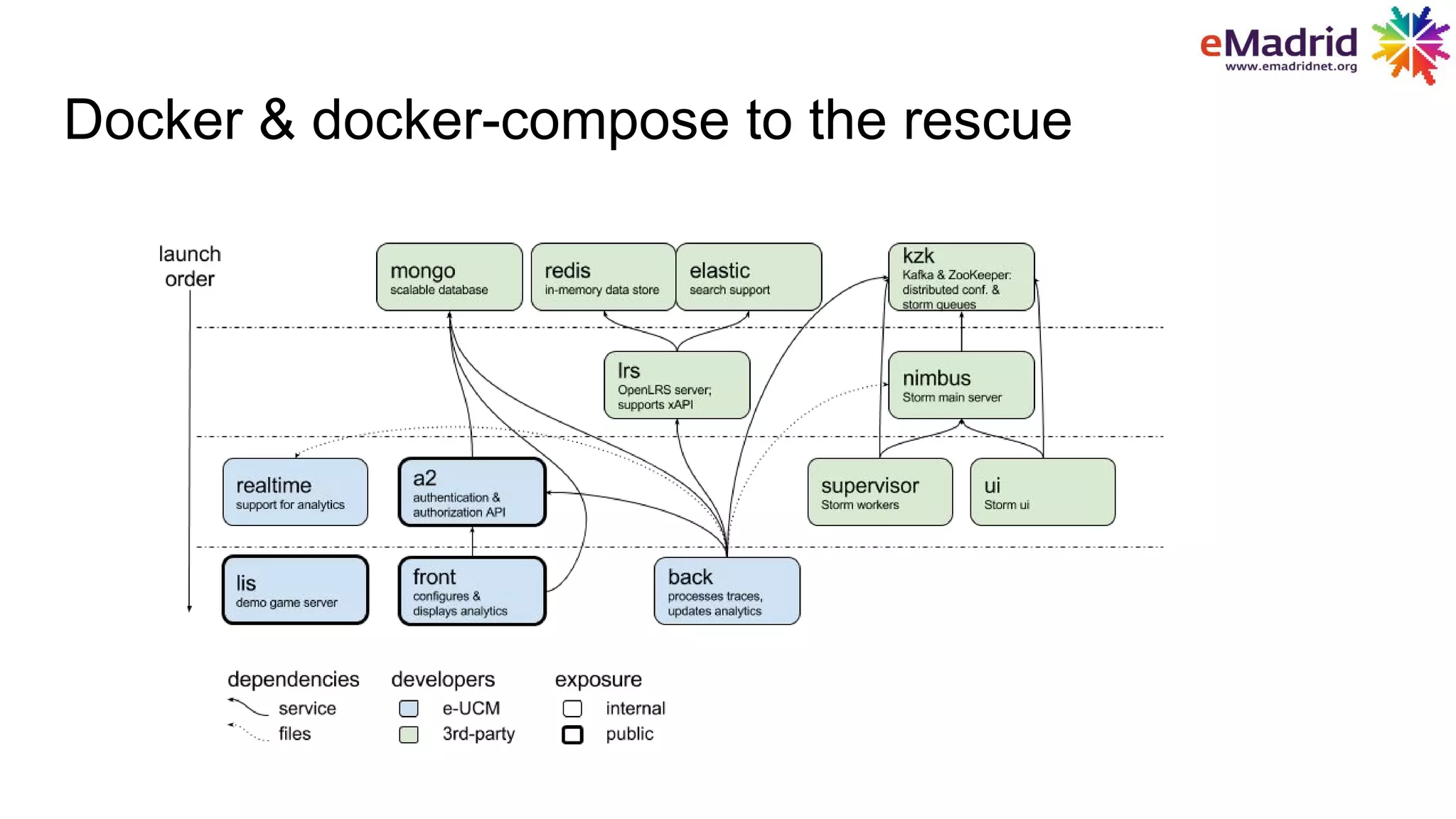
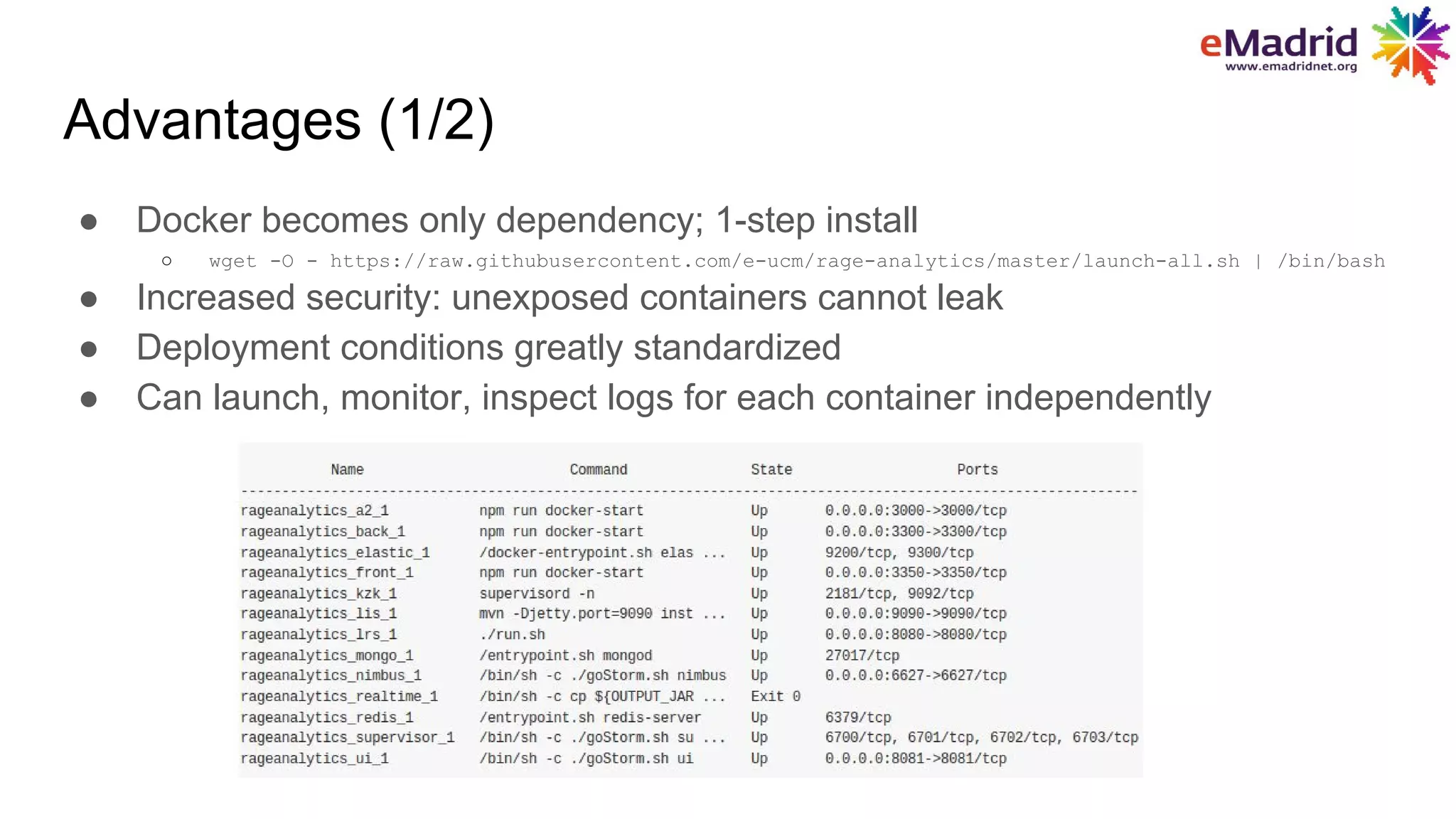
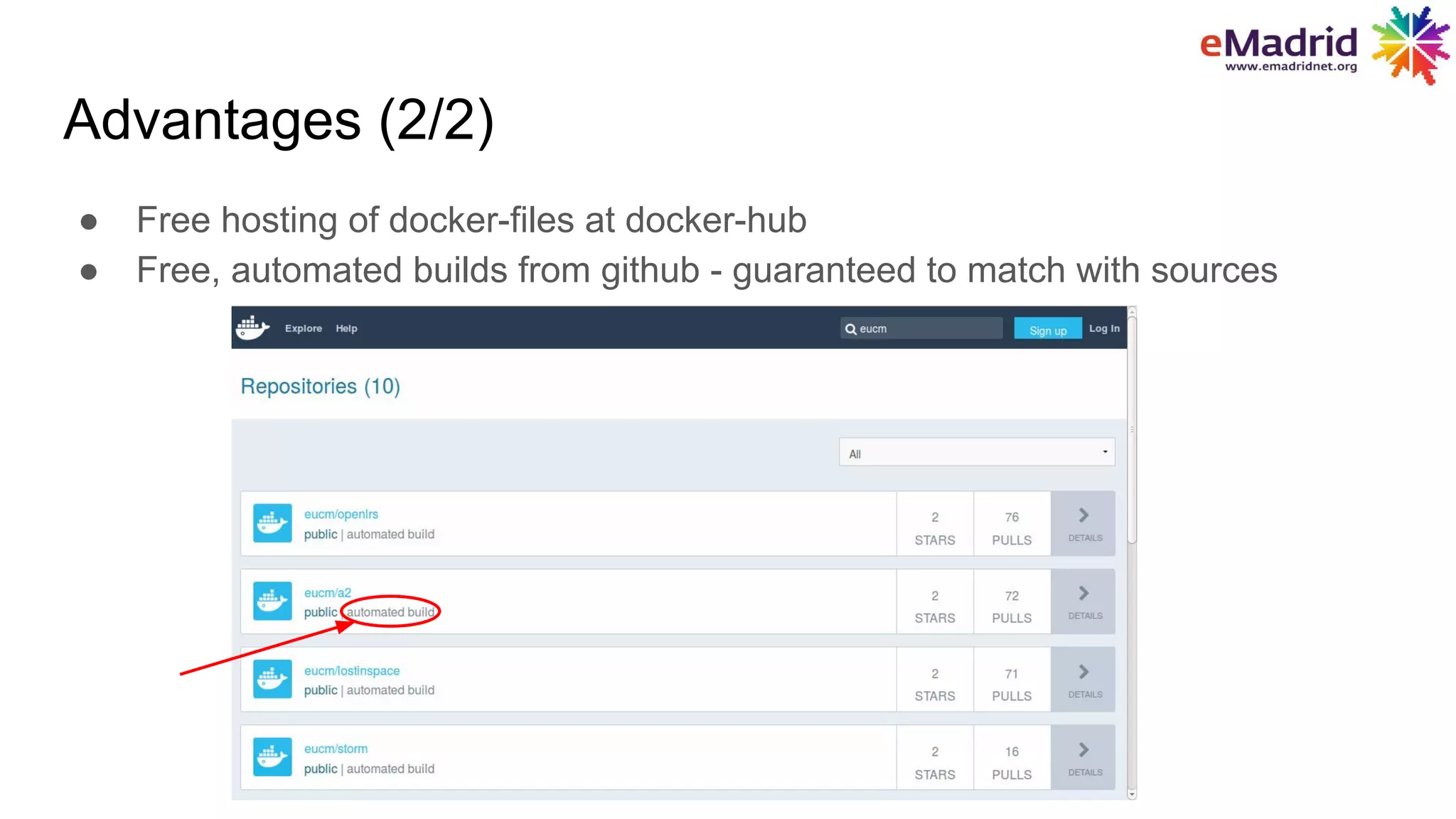
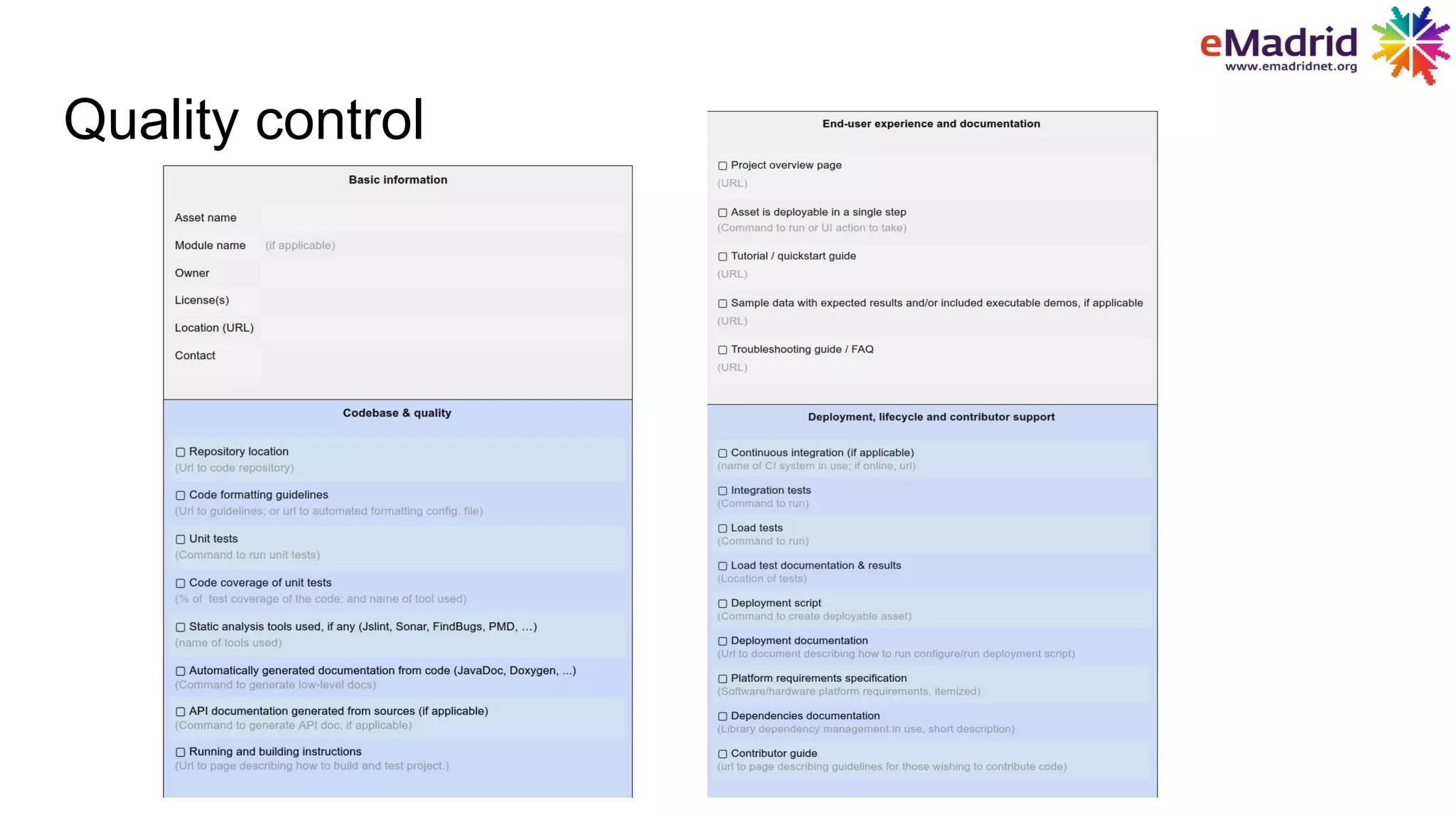
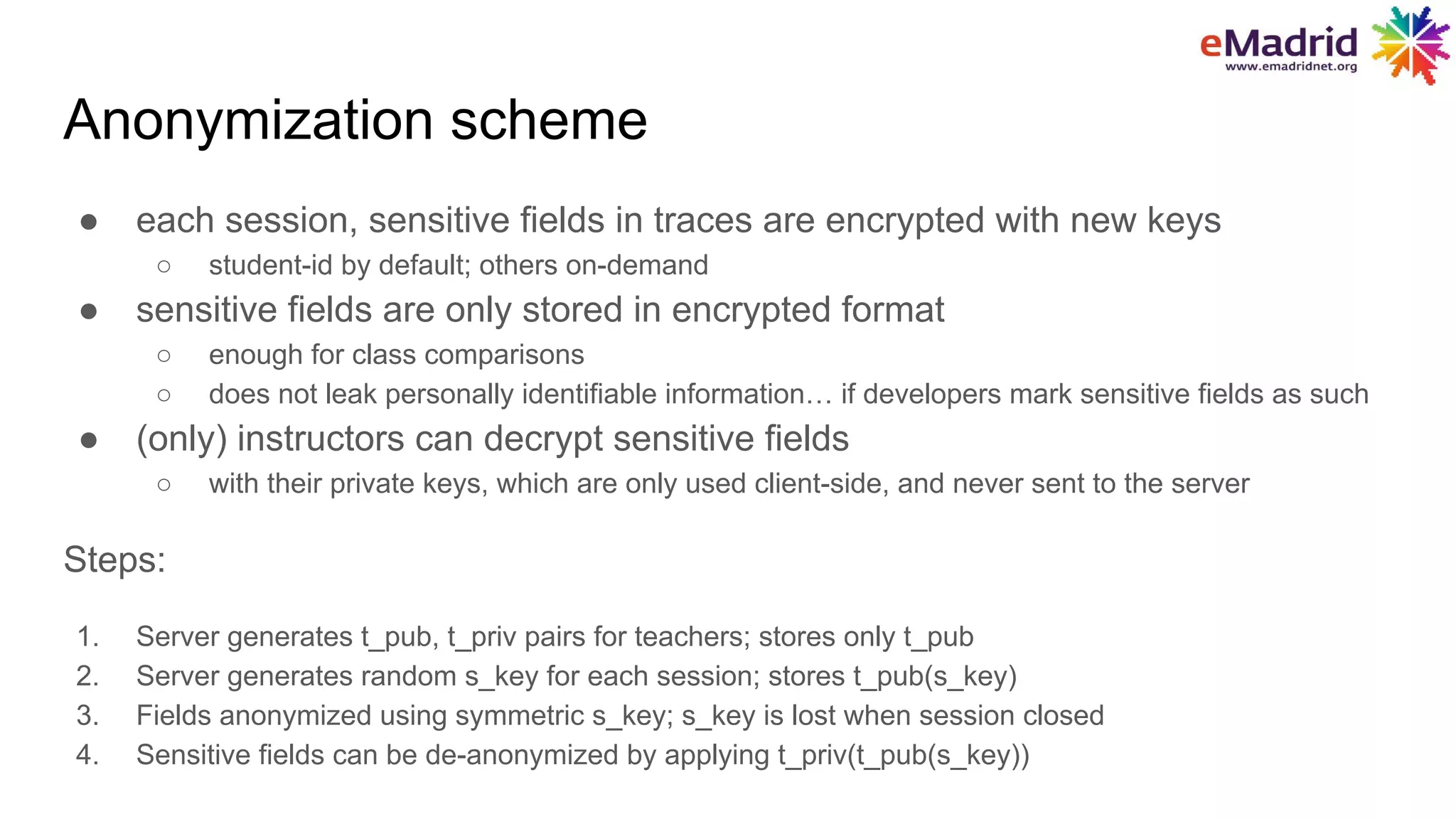
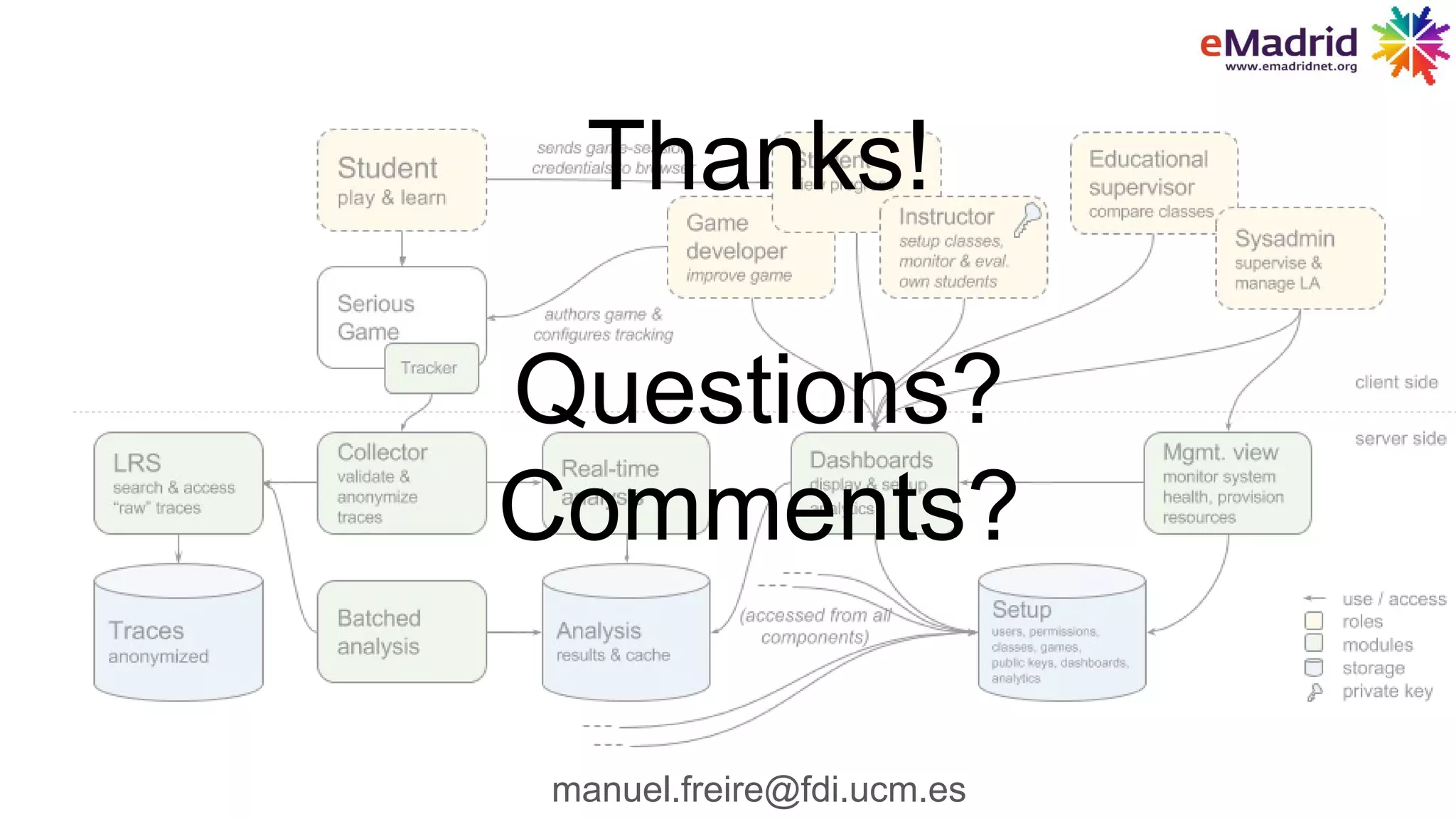
The document outlines the RAGE project aimed at developing a learning analytics infrastructure for serious games, involving a budget of 9 million euros and a collaboration among 20 partners. It discusses the development of analytics tools like Gleaner, aimed at ensuring privacy, scalability, and an ecosystem connecting game developers, educators, and students. Additionally, it details the use of Docker for deployment and data anonymization strategies to protect sensitive information.