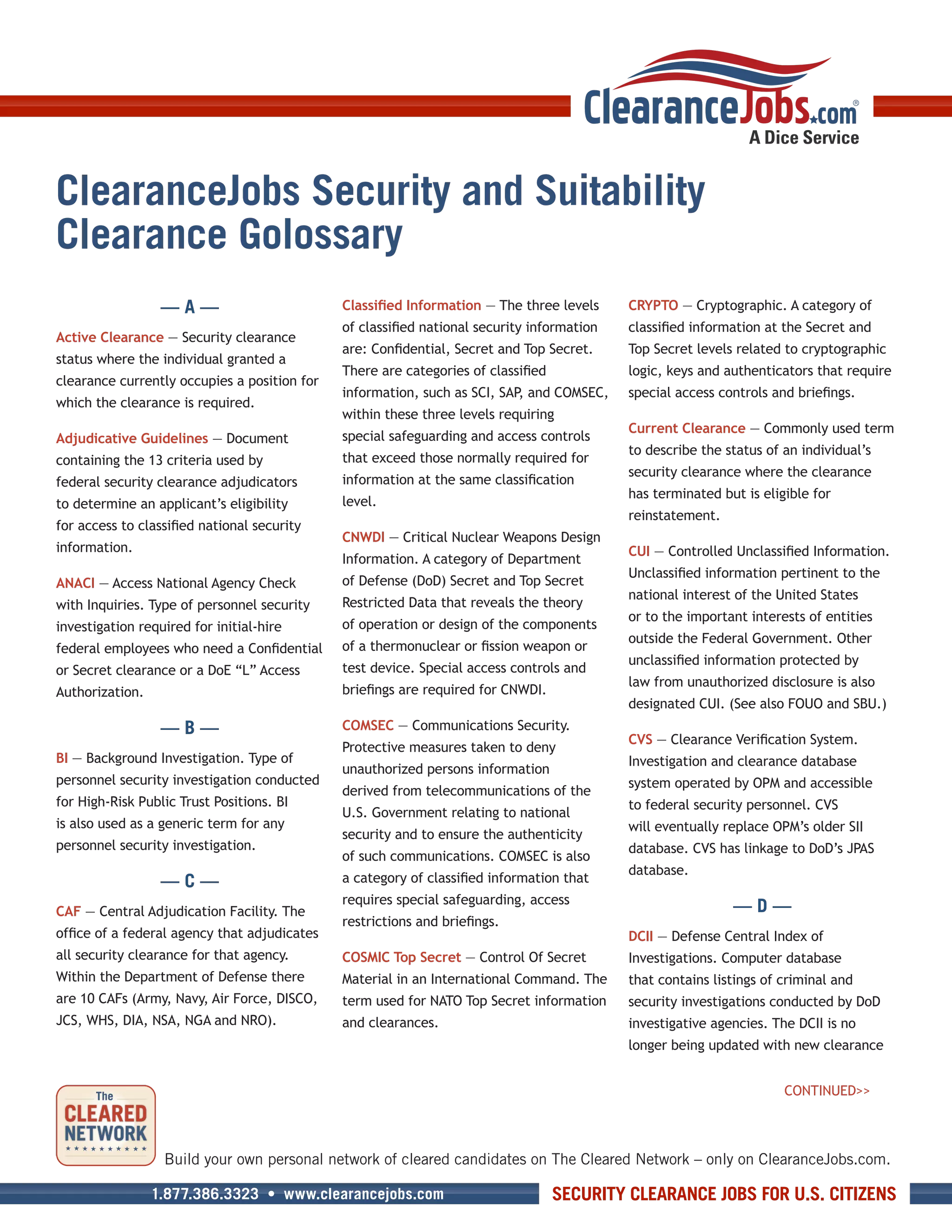
The document provides definitions for over 100 security and suitability terms used in clearance processes. It covers terminology related to investigation types, clearance levels and categories, adjudication procedures, and position risk designations. Key terms defined include active clearance, adjudicative guidelines, background investigation, classified information, security clearance, public trust position, and single scope background investigation.