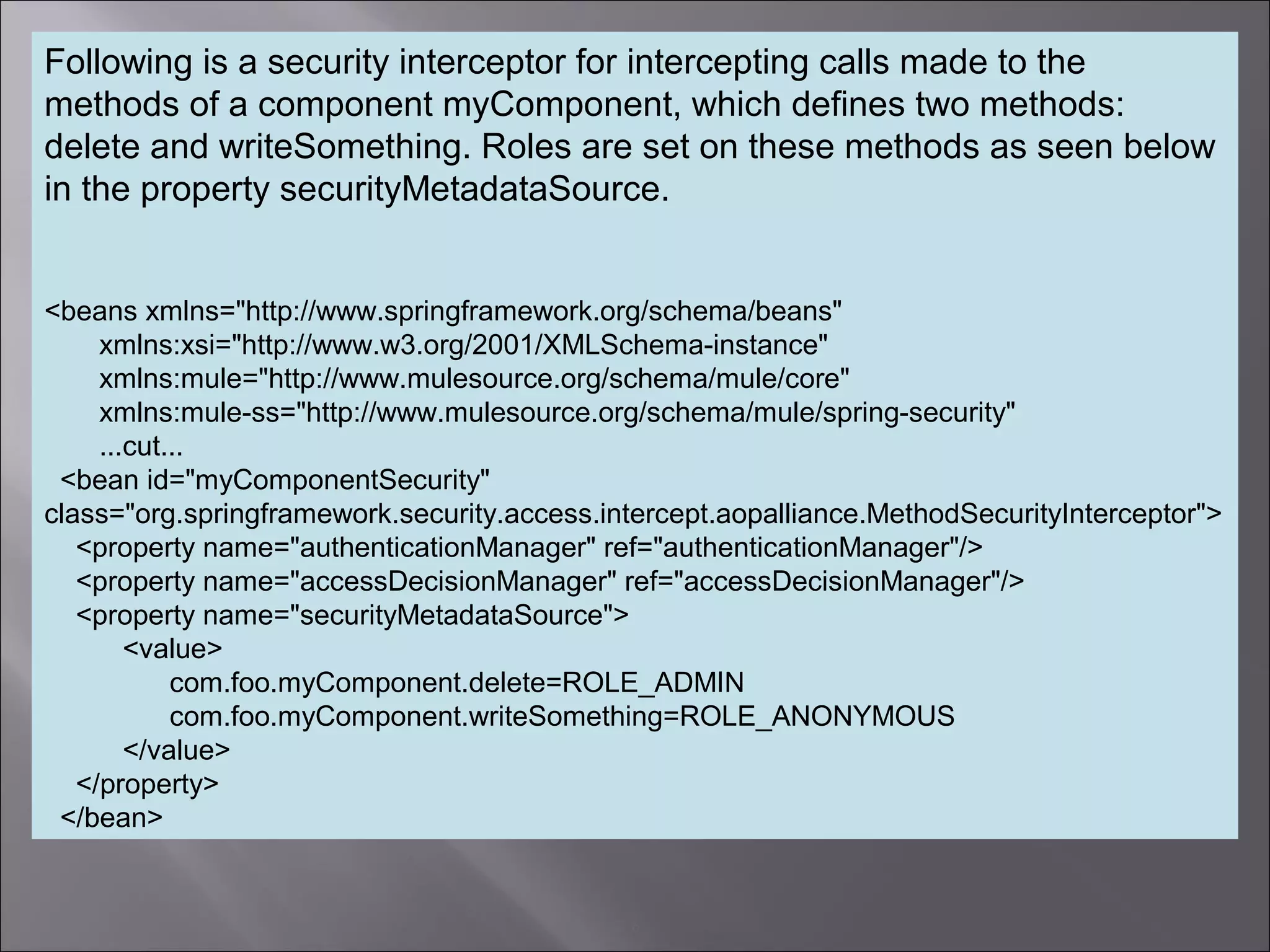
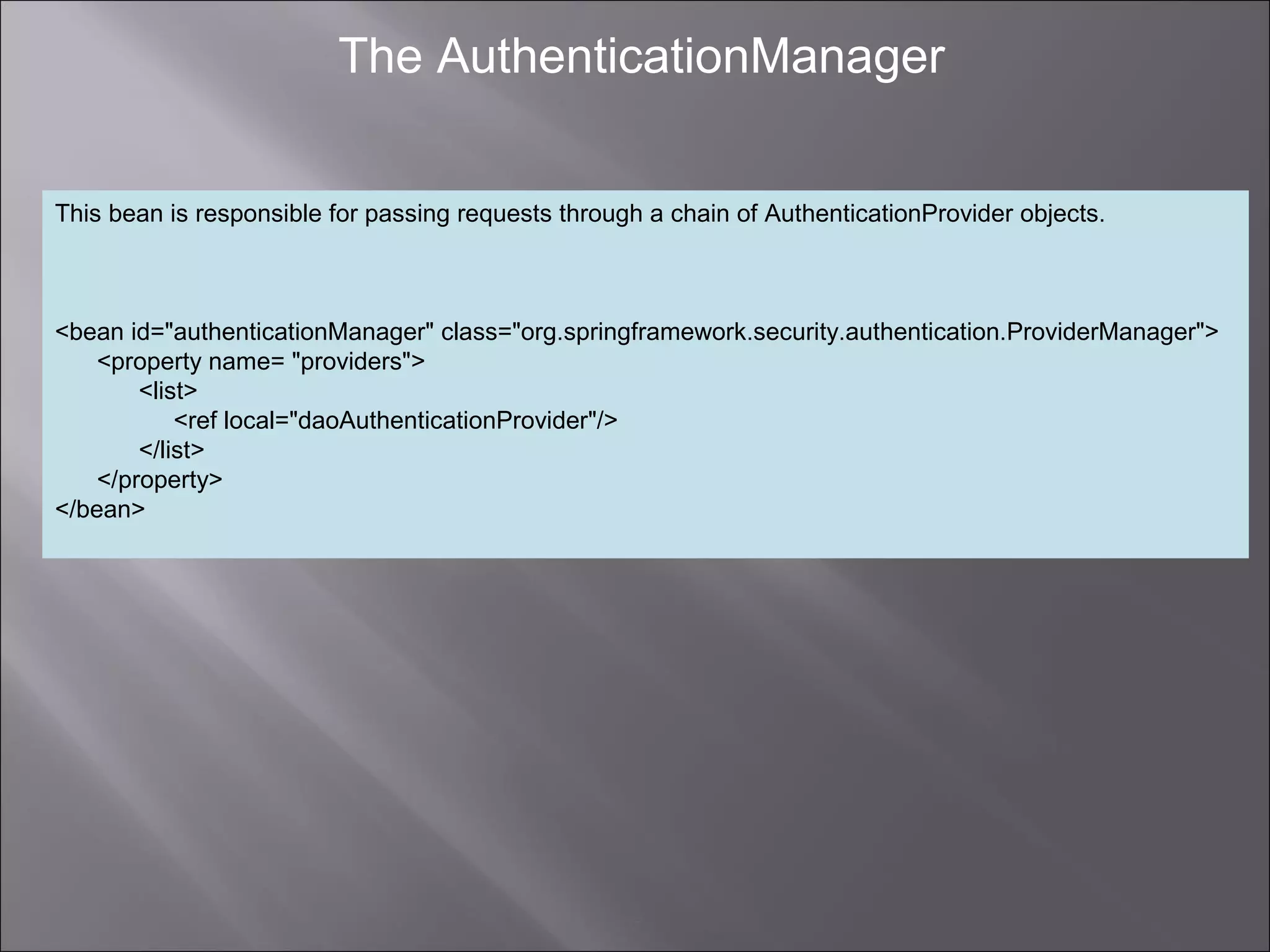
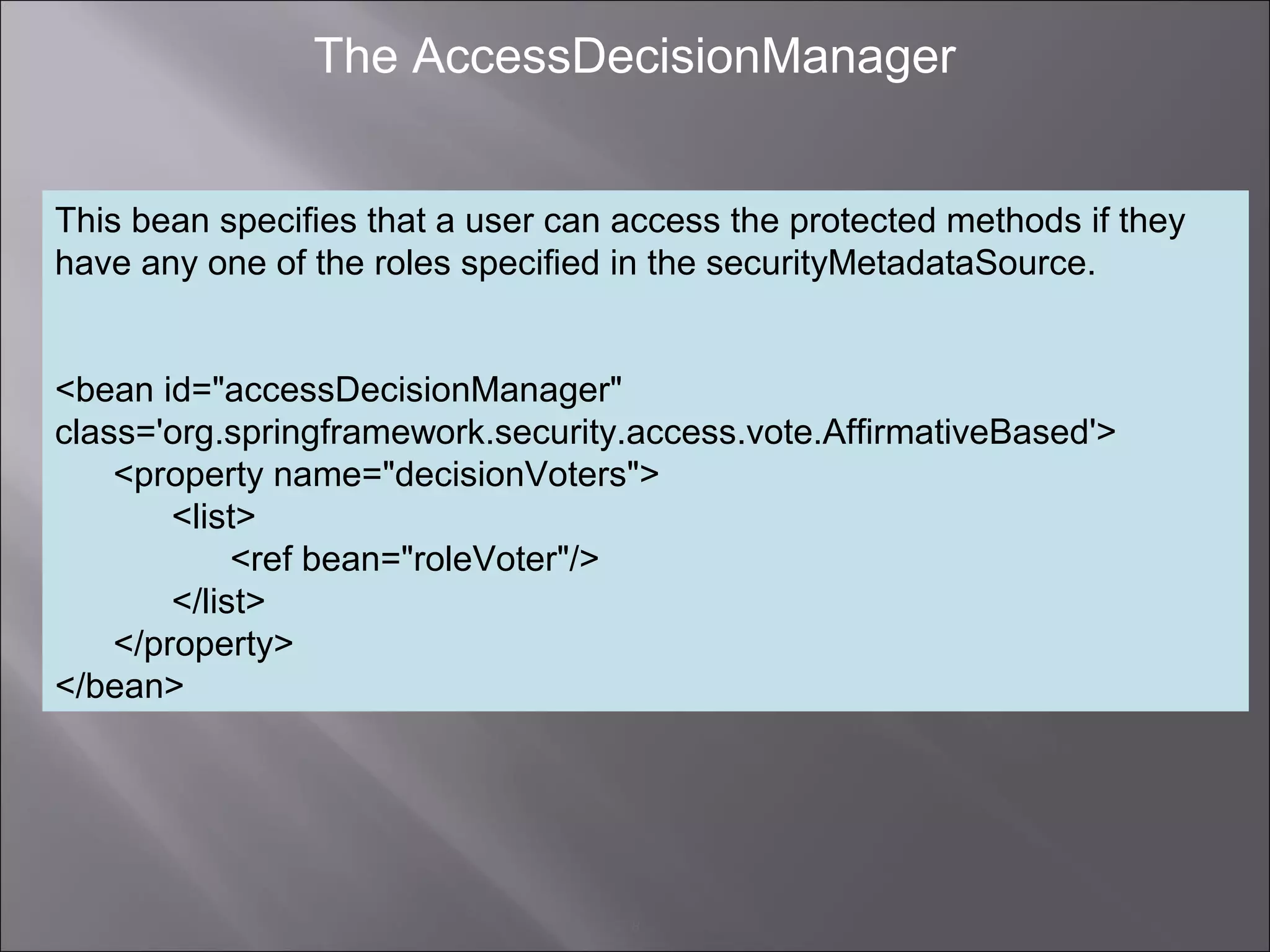
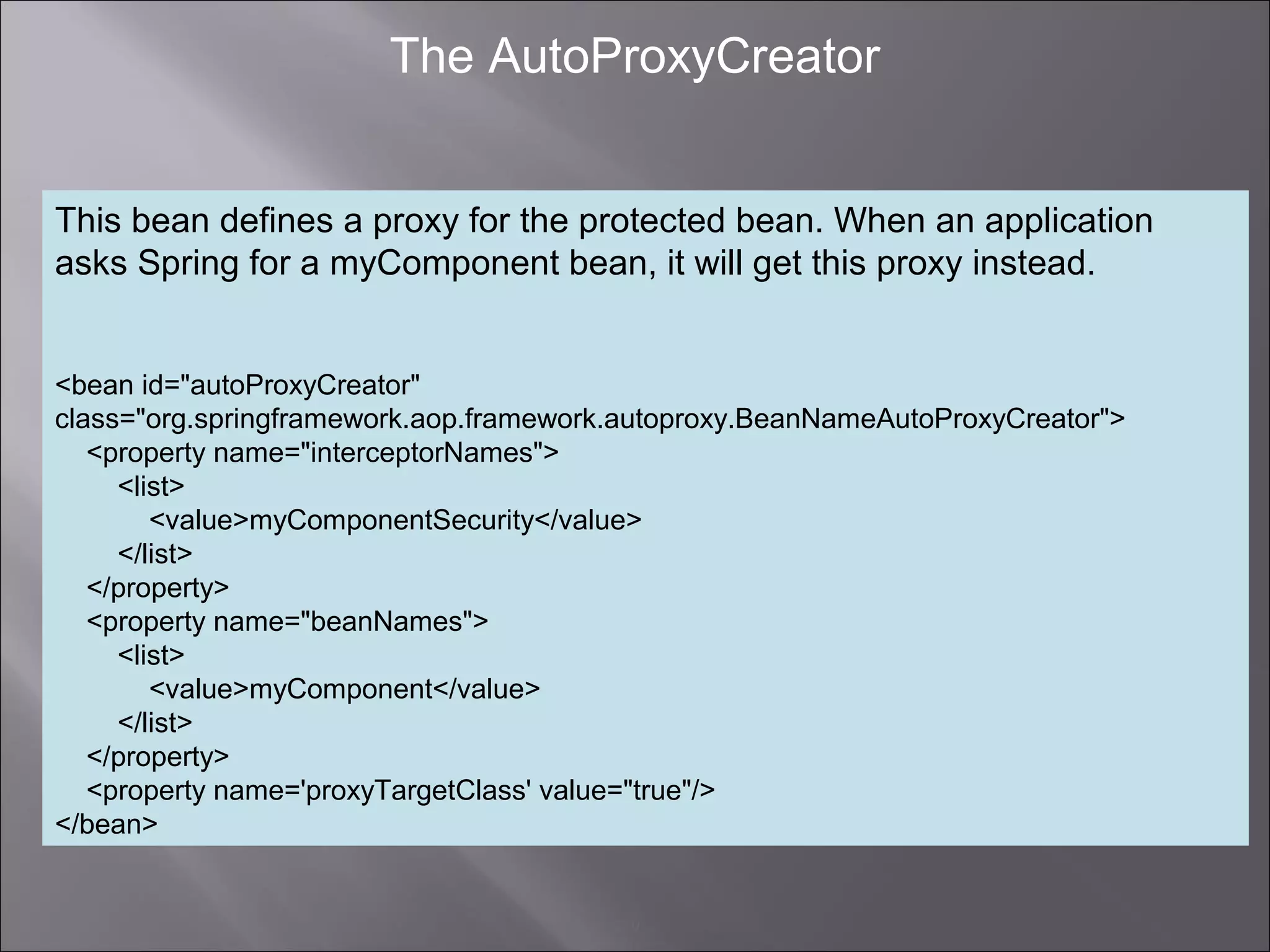
This document describes how to configure method-level authorization in Spring Security to restrict which users with certain roles can invoke methods on components. It explains that a MethodSecurityInterceptor must be configured and chained to the components needing security via a proxy. The MethodSecurityInterceptor is configured with an AuthenticationManager and AccessDecisionManager, and security roles can be defined for each method.