This document describes a dissertation project for developing a leave management system (LMS) accessible via text messaging without requiring a smartphone or internet connection. Key aspects of the project include developing a LMS application, mobile API, and command-based text messaging system. This would allow employees to manage leave and check balances using only basic cell phone text messaging. The system is designed to provide access for users in locations without reliable internet or where data plans and smartphones are not available.
![17
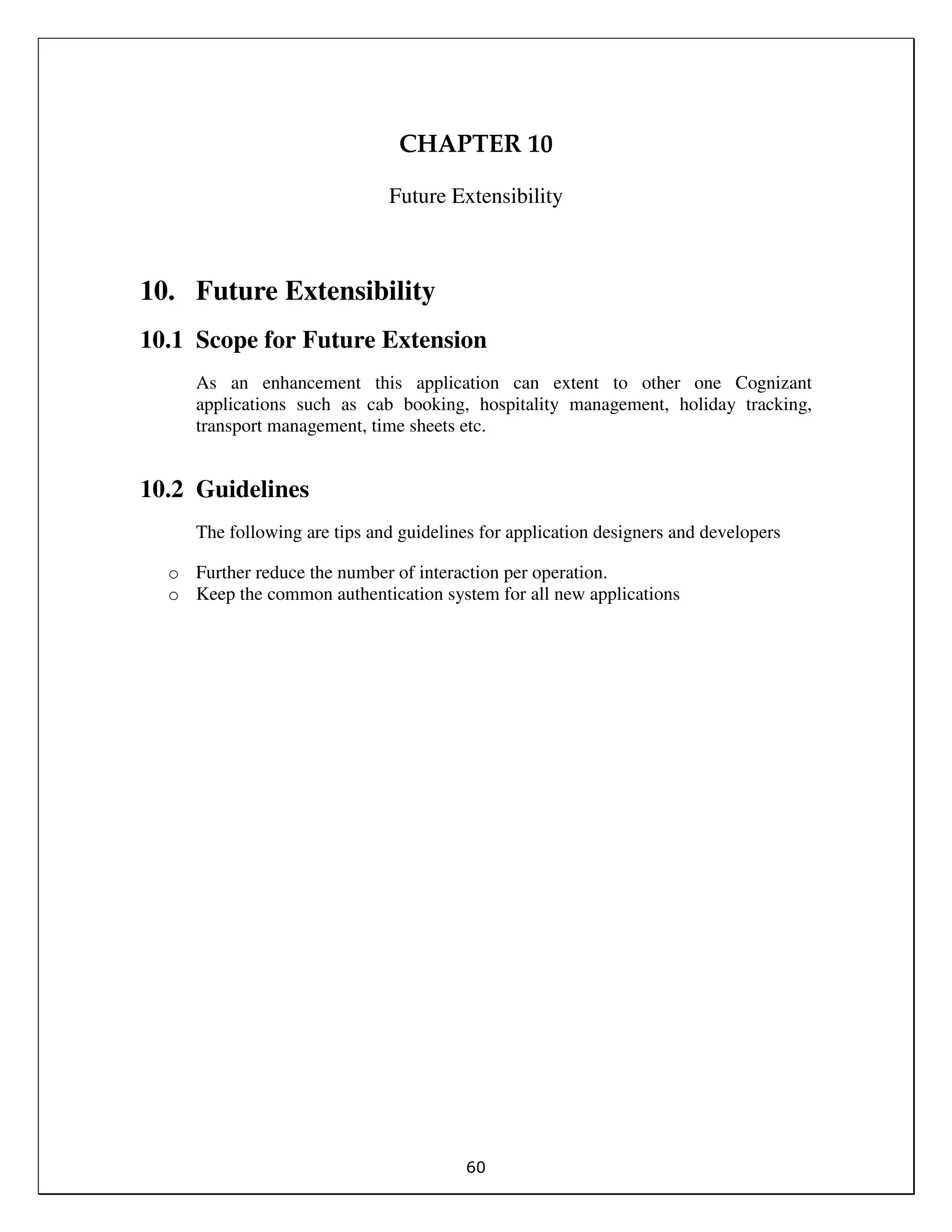
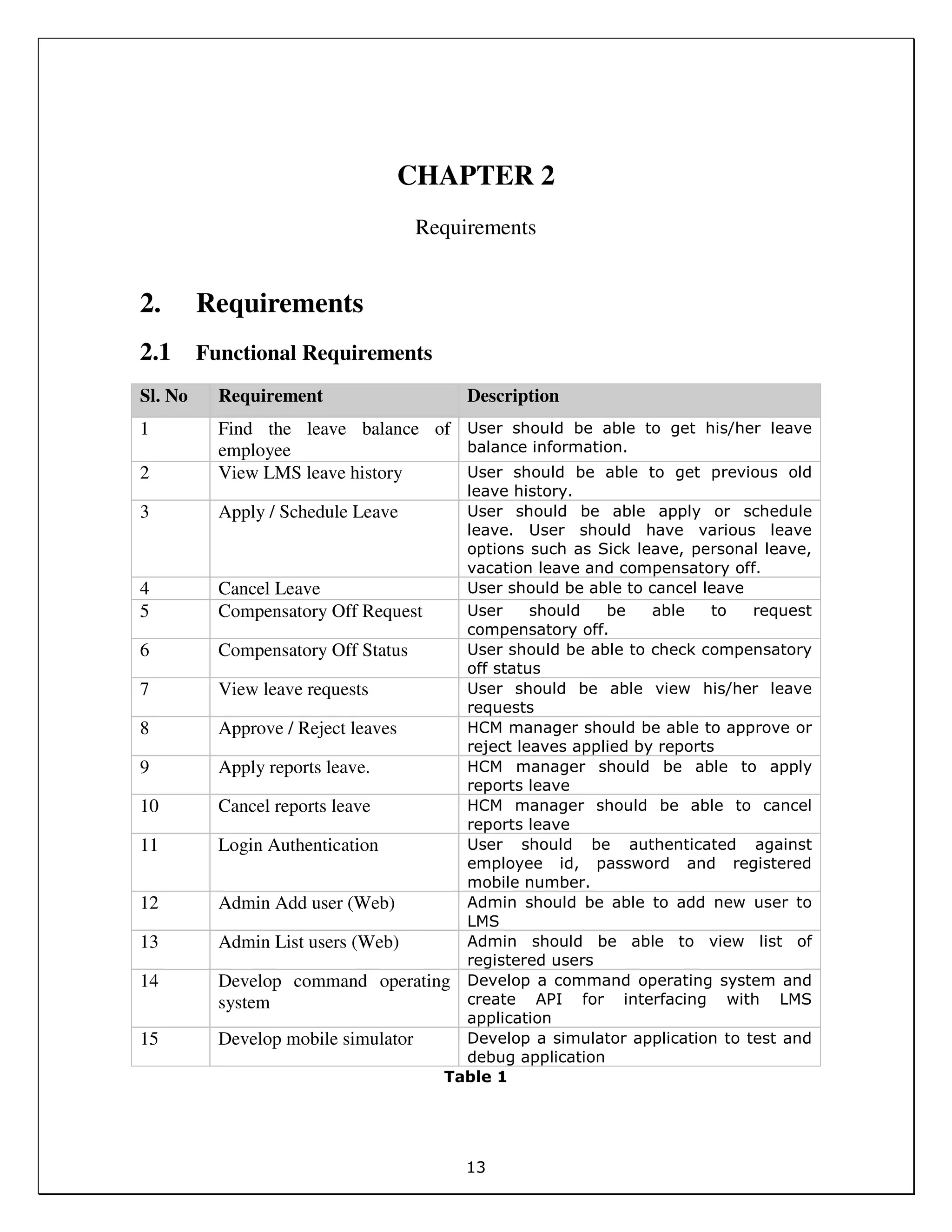
Exceptions Send error code and friendly message to mobile and save error to log
Related Use Cases None
Includes None
Extends / Uses None
Table 2
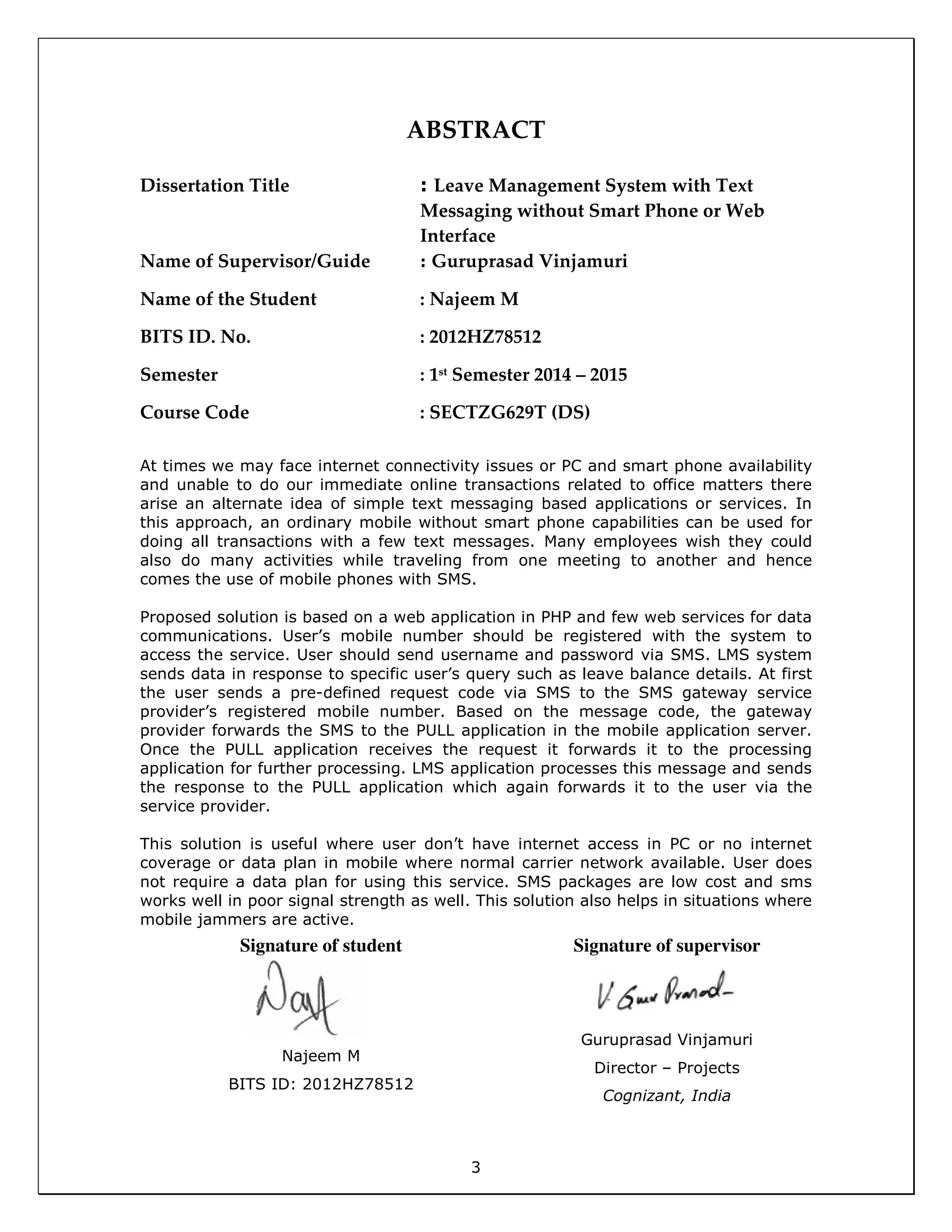
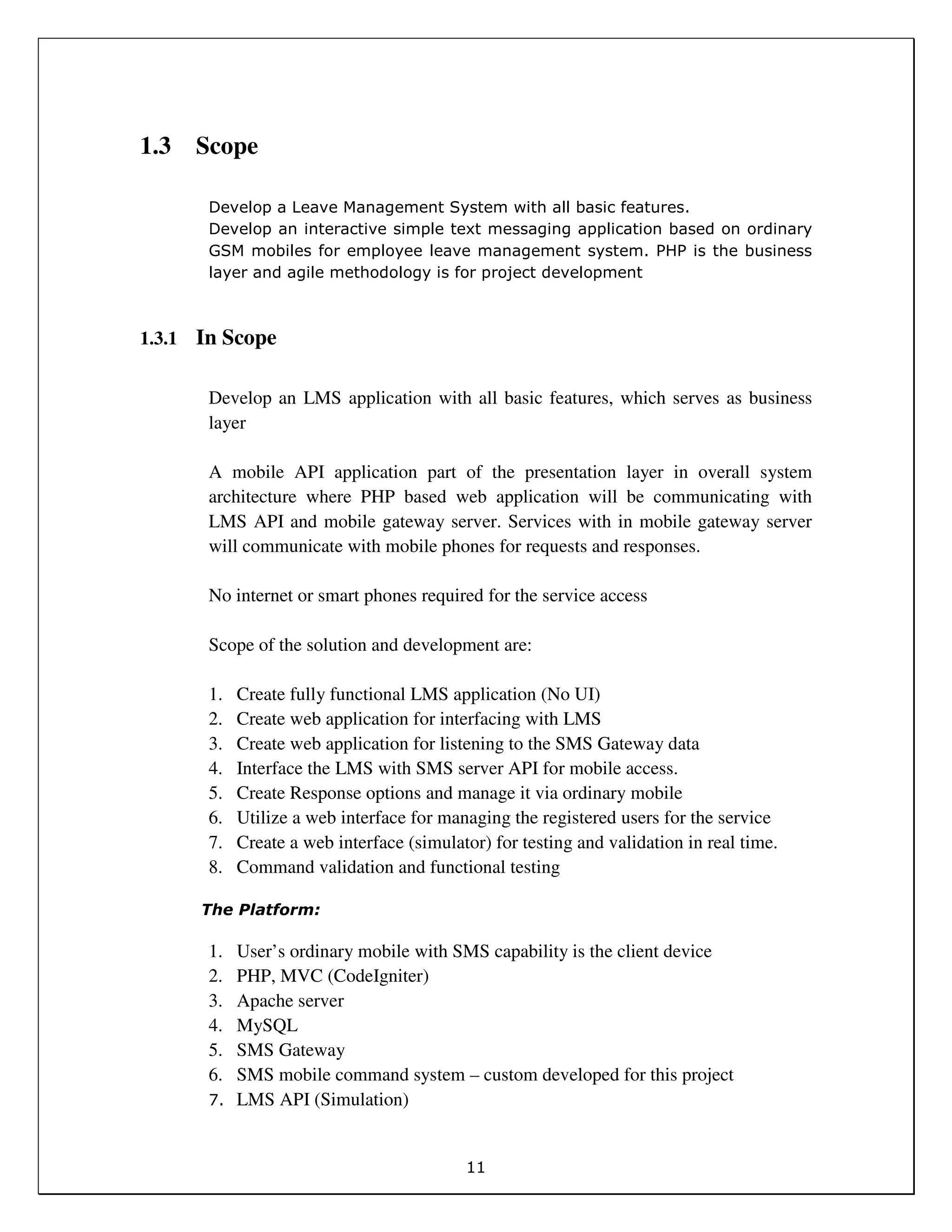
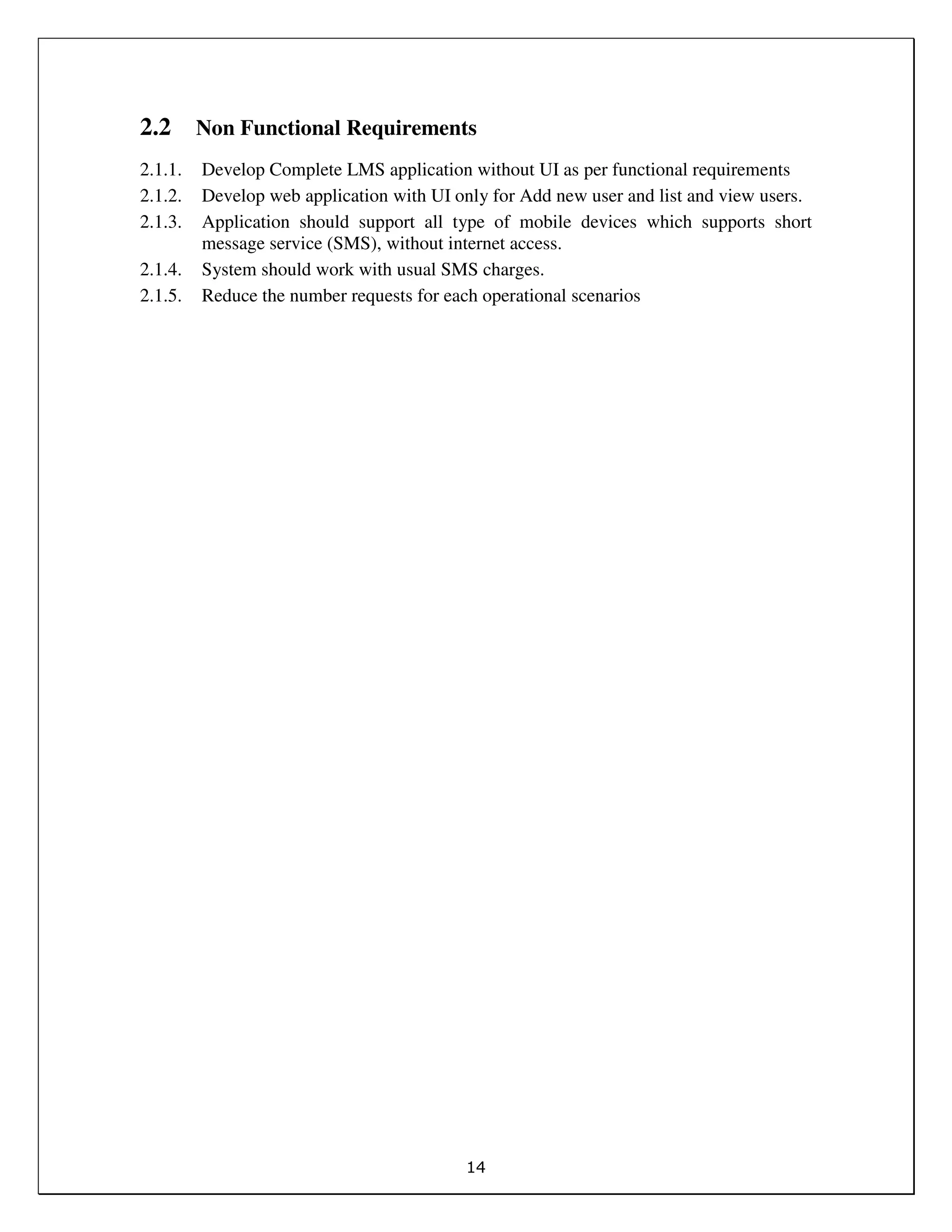
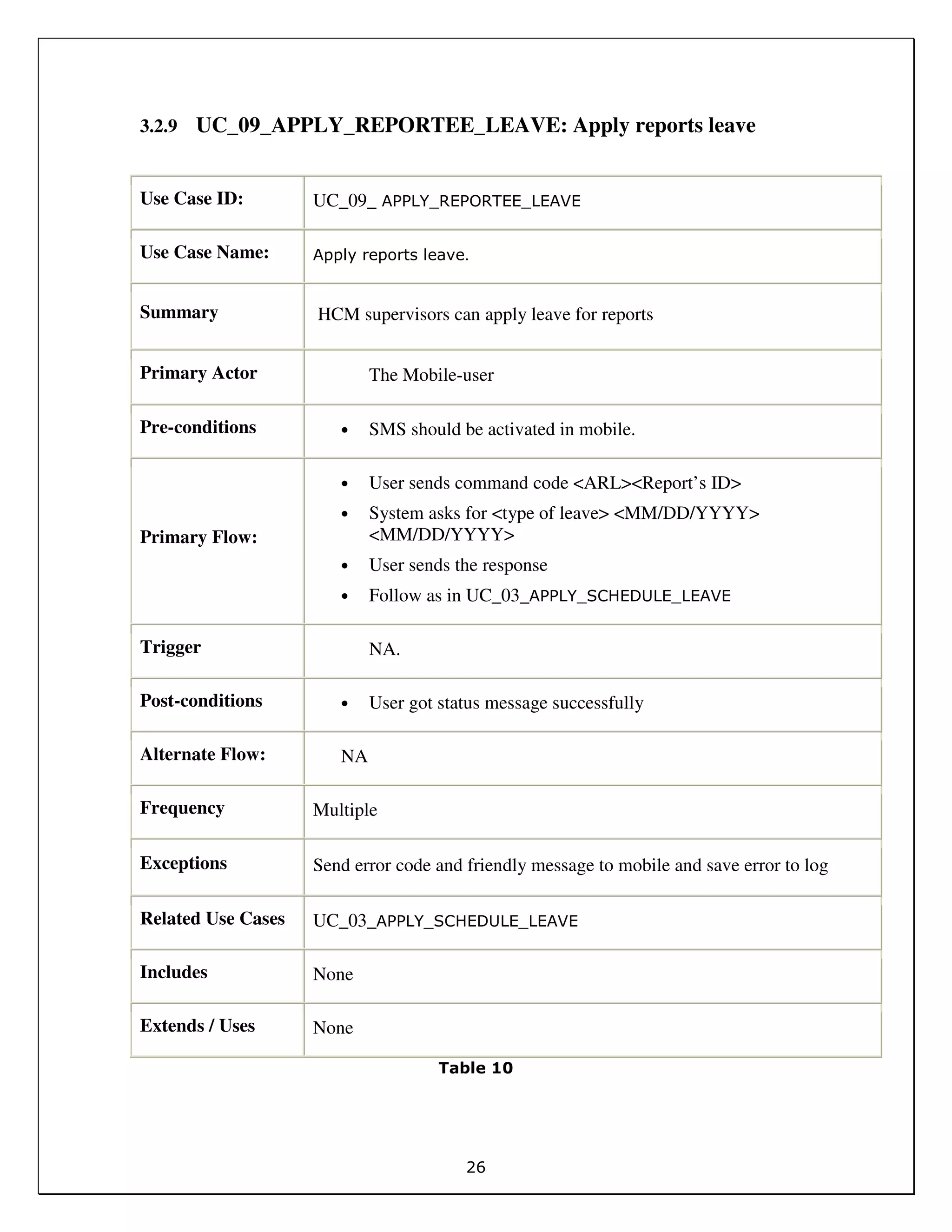
3.2.2 UC_02_LMS_LEAVE_HISTORY:
Use Case ID: UC_ 02_VIEW_LMS_LEAVE_HISTORY
Use Case Name: LMS Leave history of employee for specific year
Summary Summary of total leaves taken by the employee in each category in a
specific year.
Primary Actor The Mobile-user
Pre-conditions • . SMS capability in mobile is required
Primary Flow:
MF1
• User sends specific command word (LLH) to LMS number
• System responds with a question:
o Enter Year <LLH> <YYYY> [format]
• User enter the command word and year
• Example LLH 2012
• System will send a summary of leaves for each category
o Compensatory Off: 2.00 Days
o Personal Leave: 11.00 Days
o Sick Leave: 7.50 Days
o Vacation Leave: 14.00 Days
Trigger NA](https://image.slidesharecdn.com/f9a062fe-be1b-46fc-b2a9-6c6961d11c6b-150404071650-conversion-gate01/75/SECTZG629T_FR_2012HZ78512-17-2048.jpg)
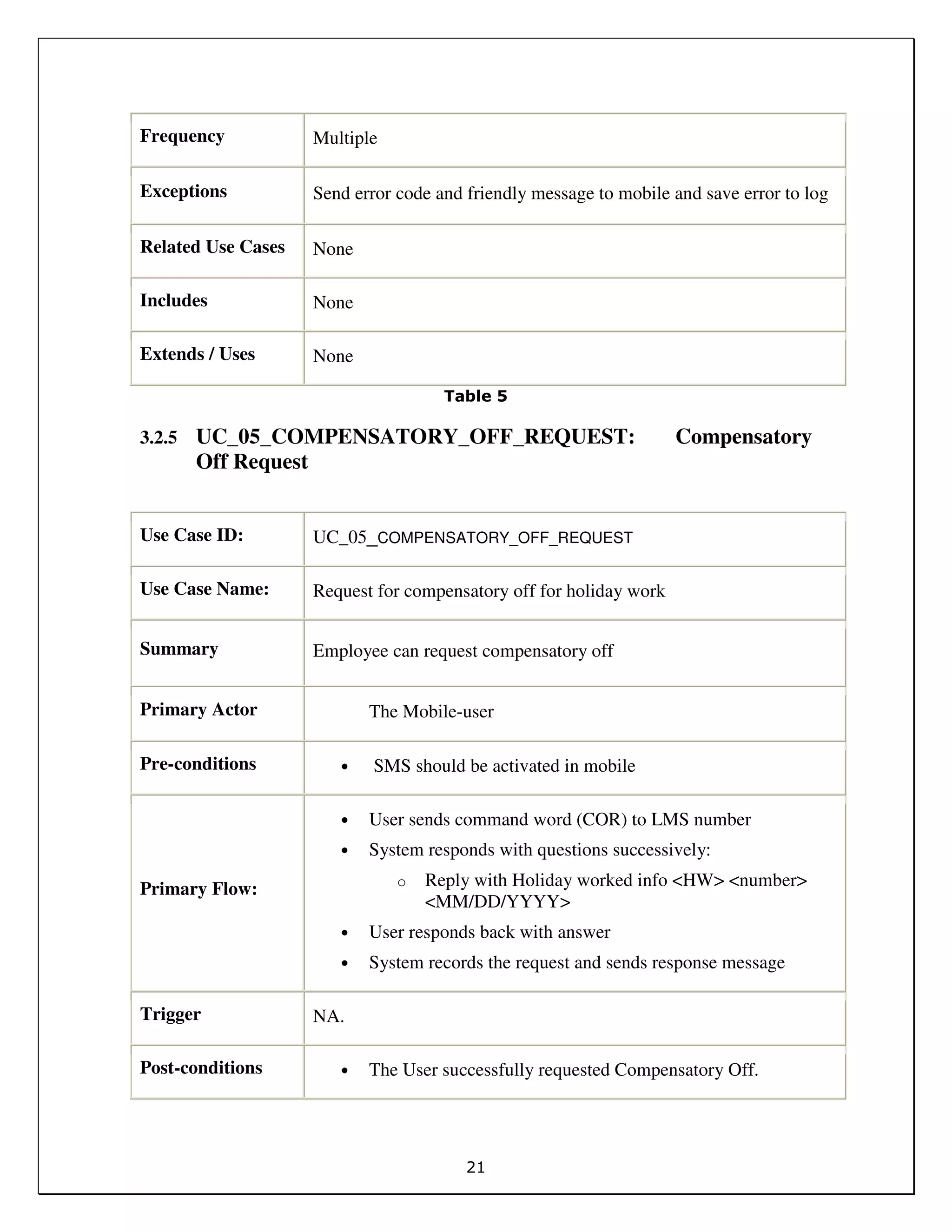
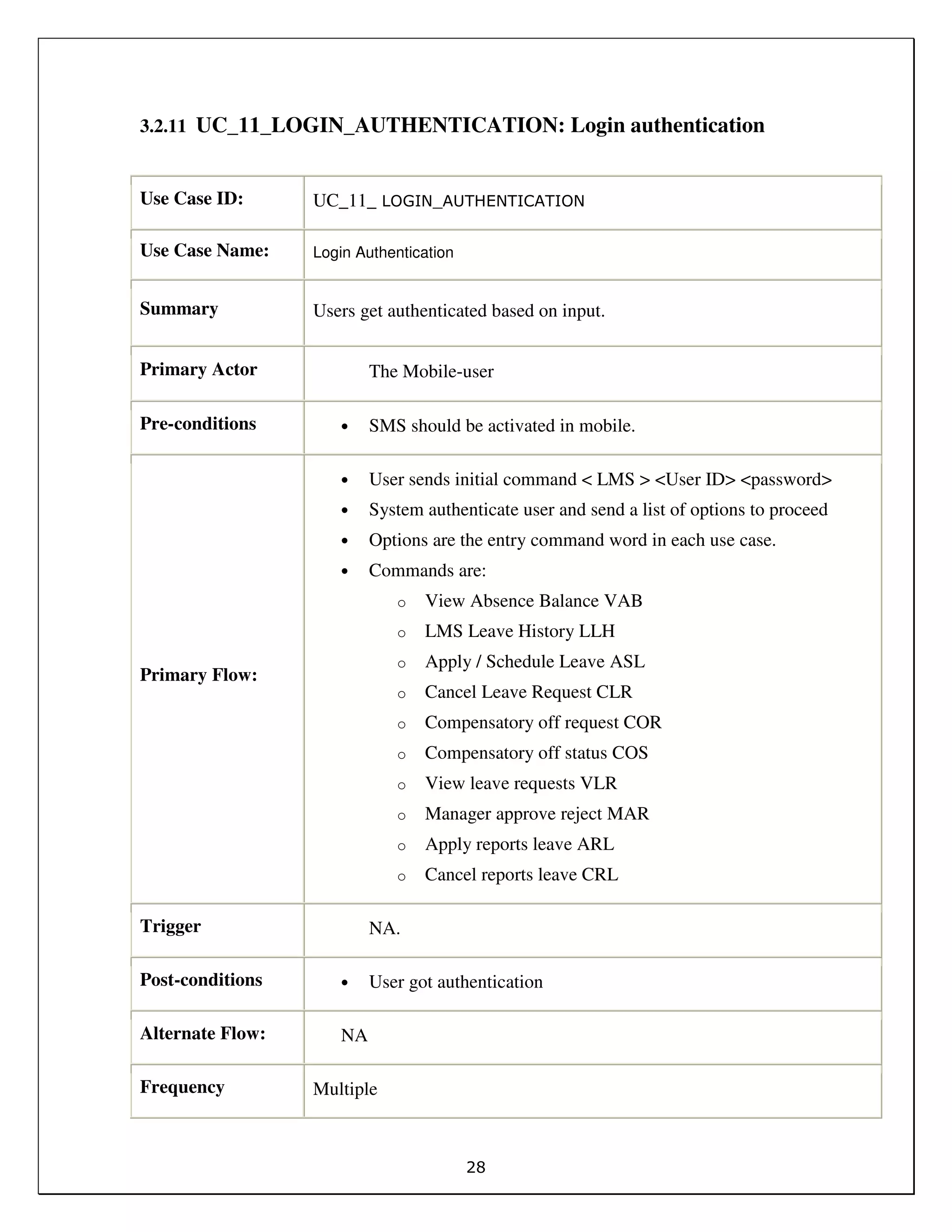

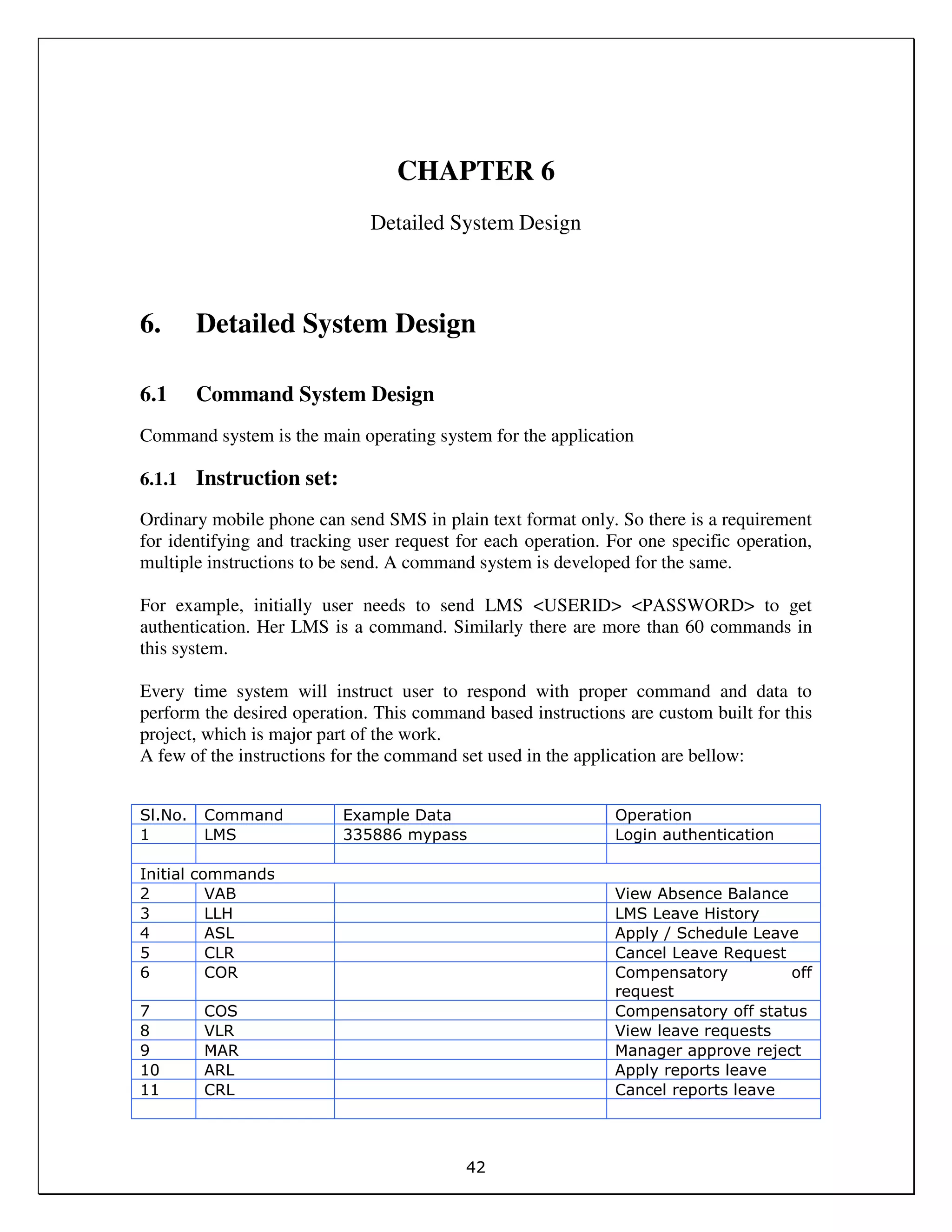
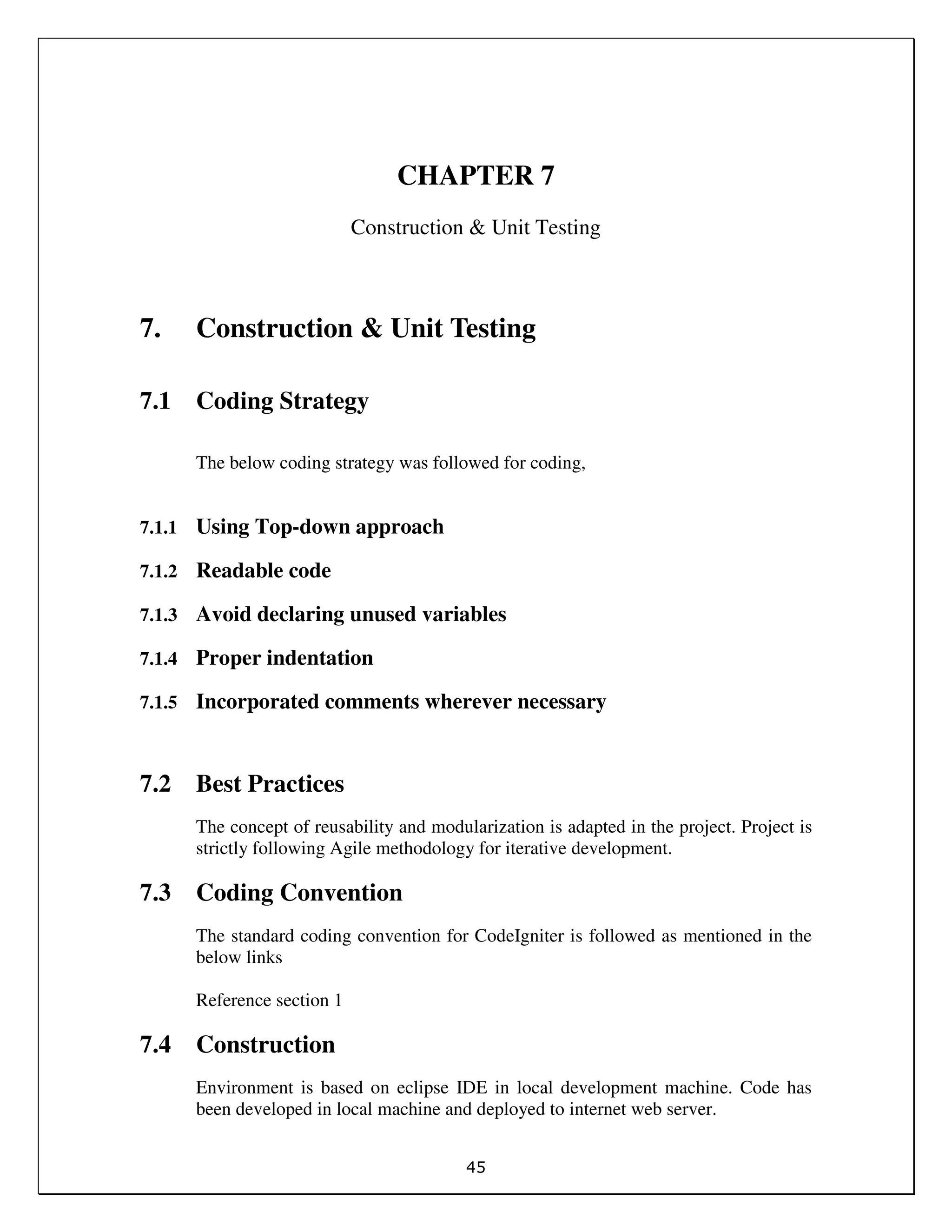
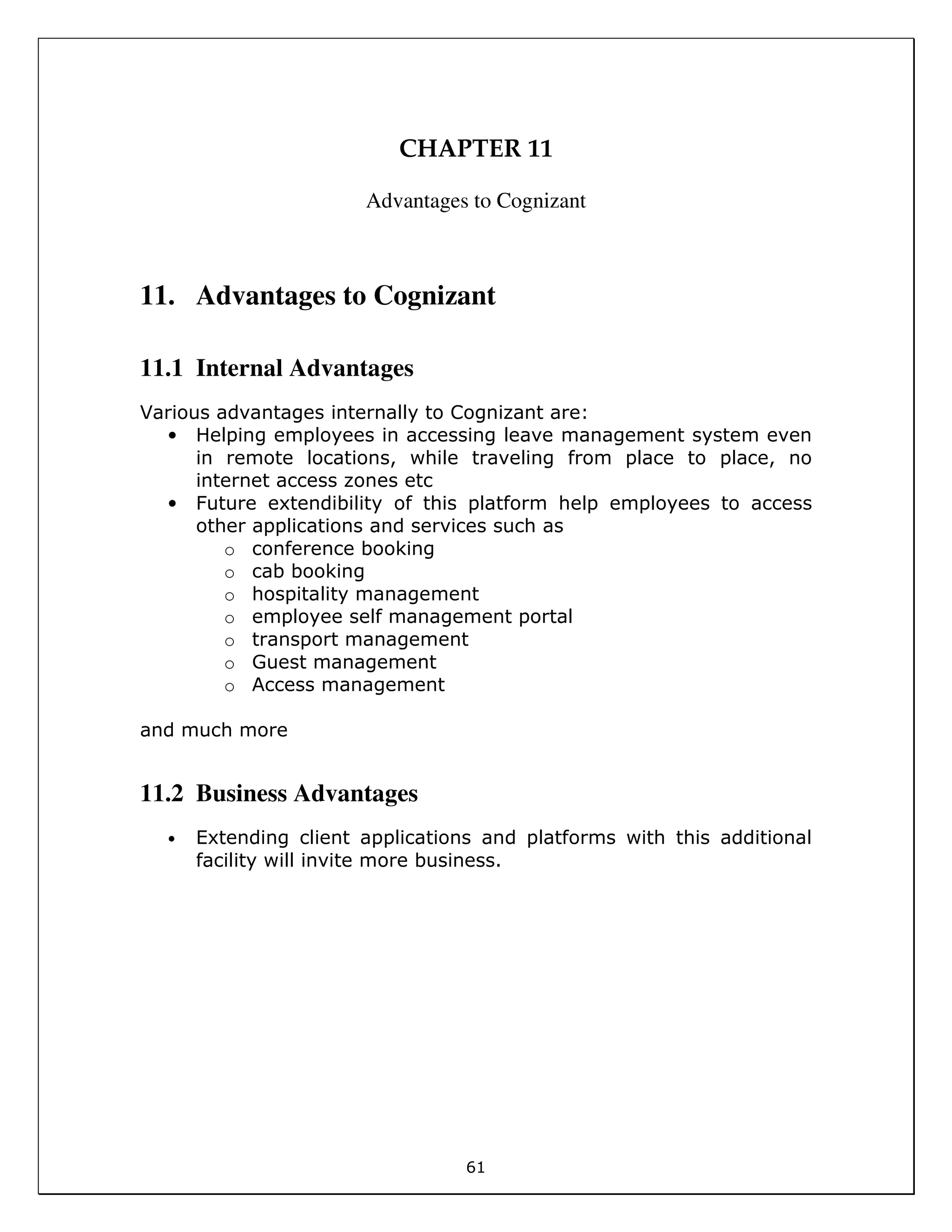
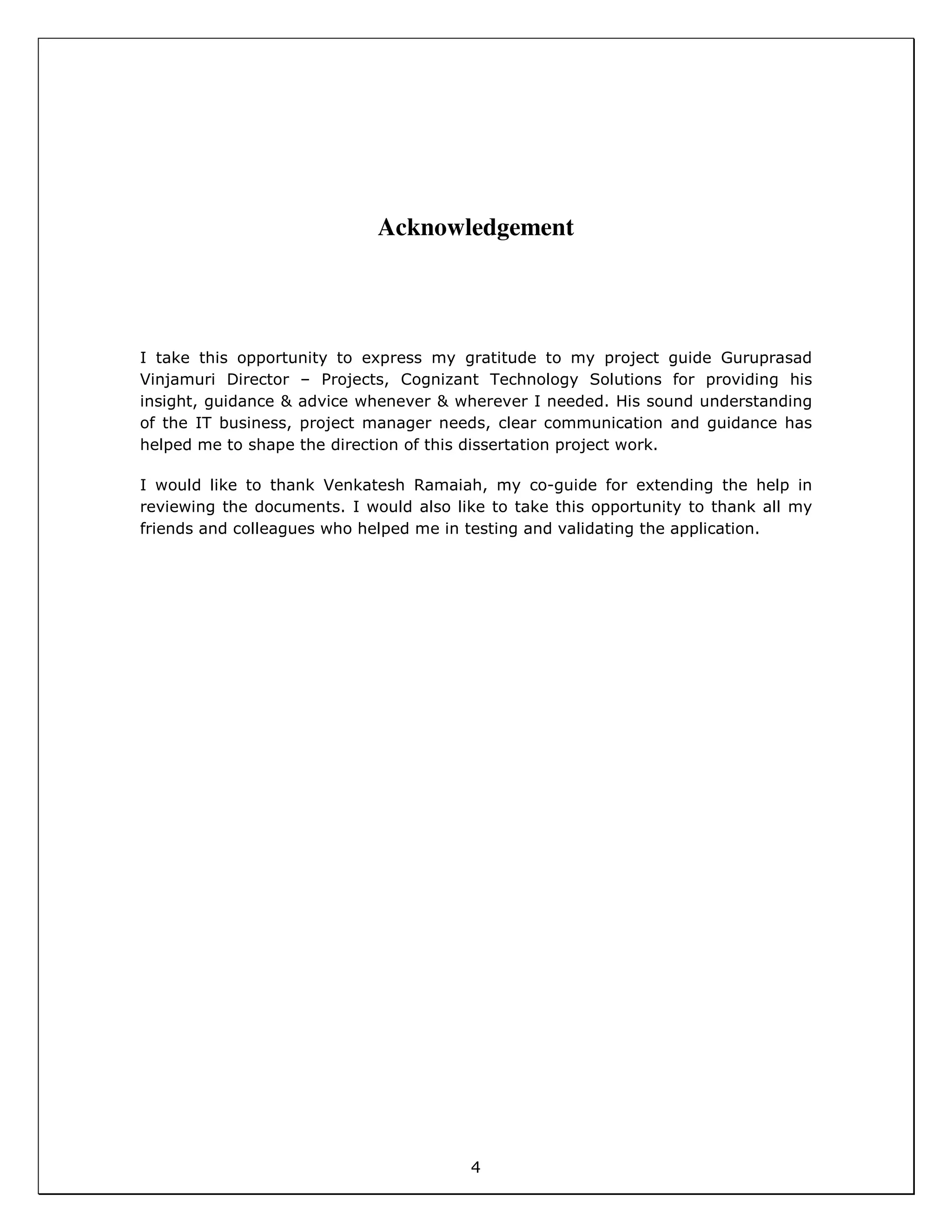
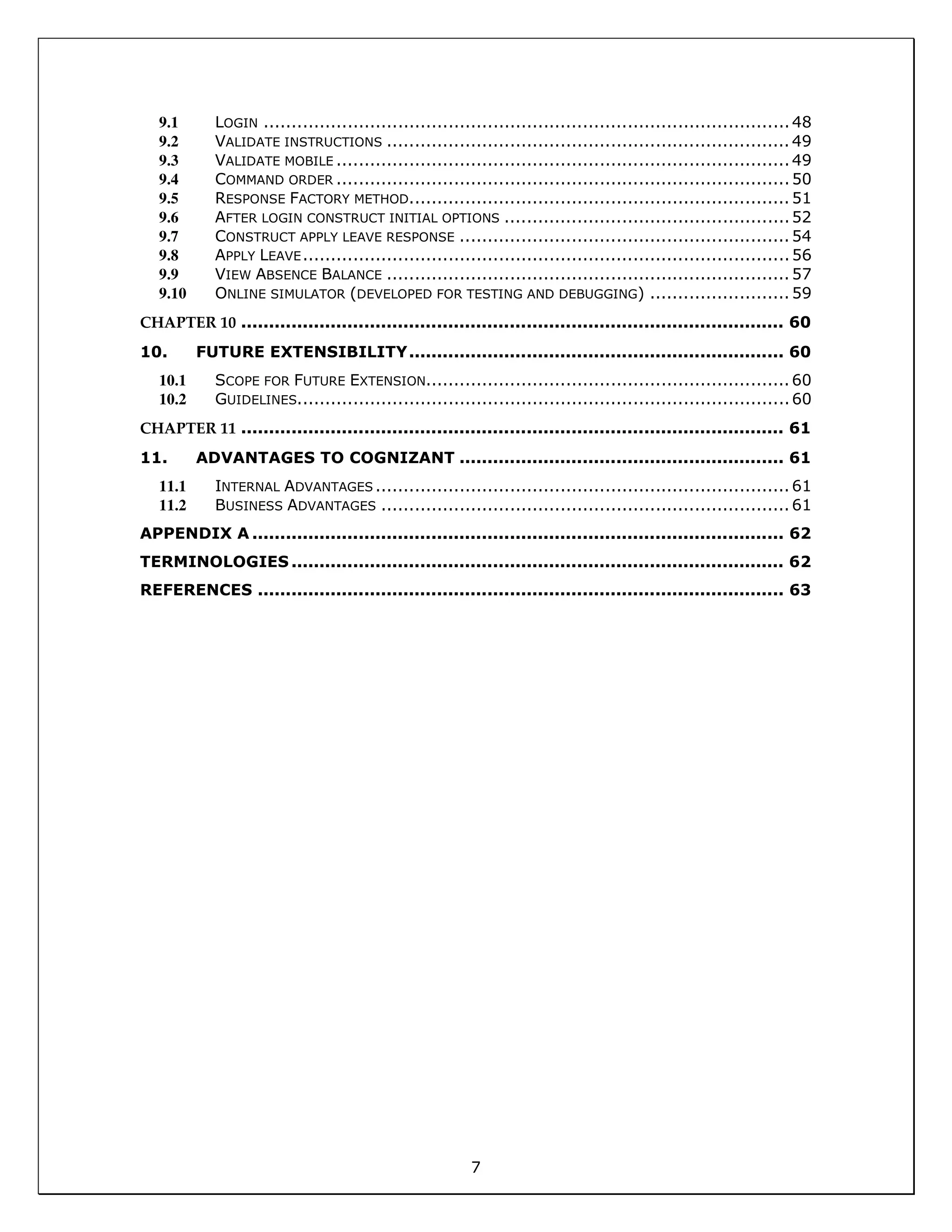
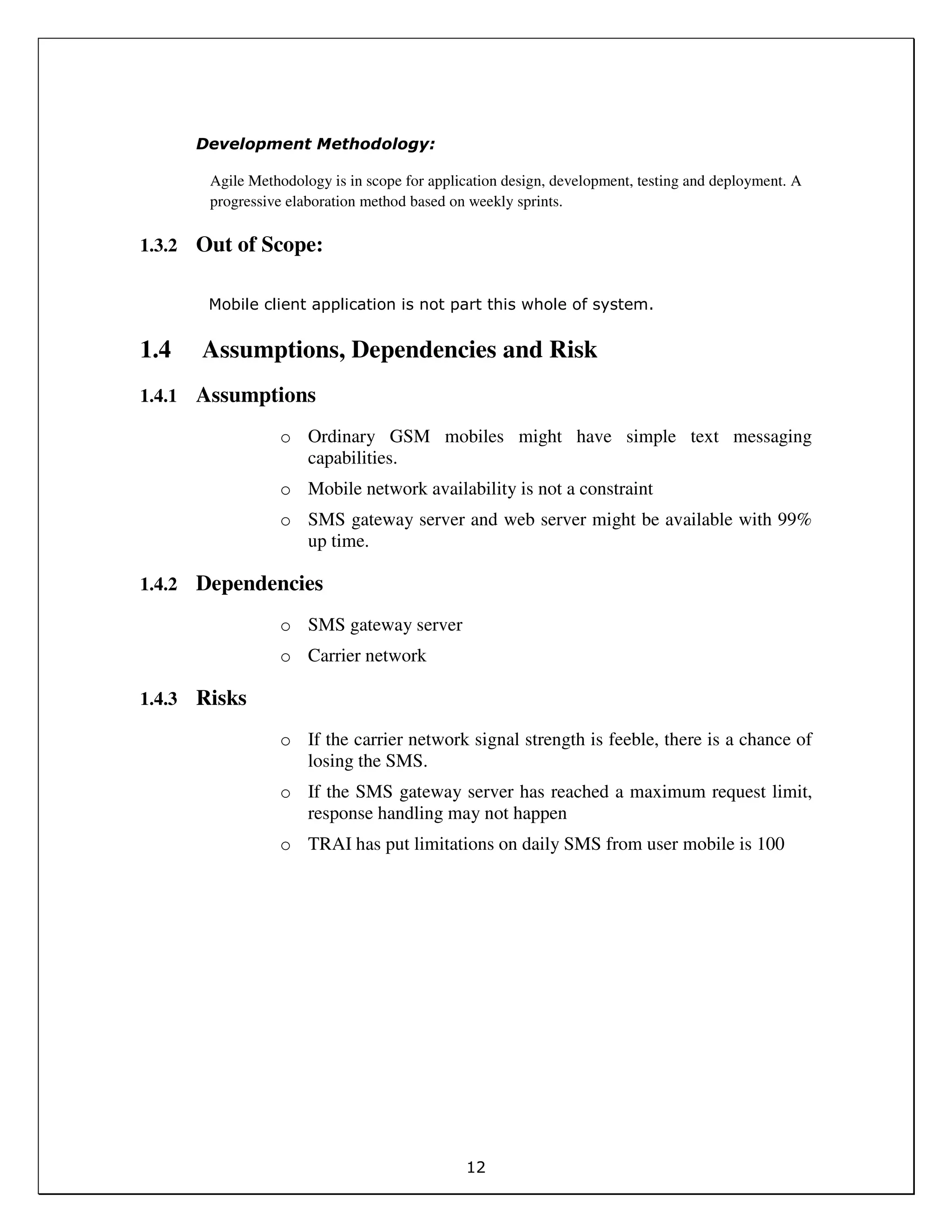
![43
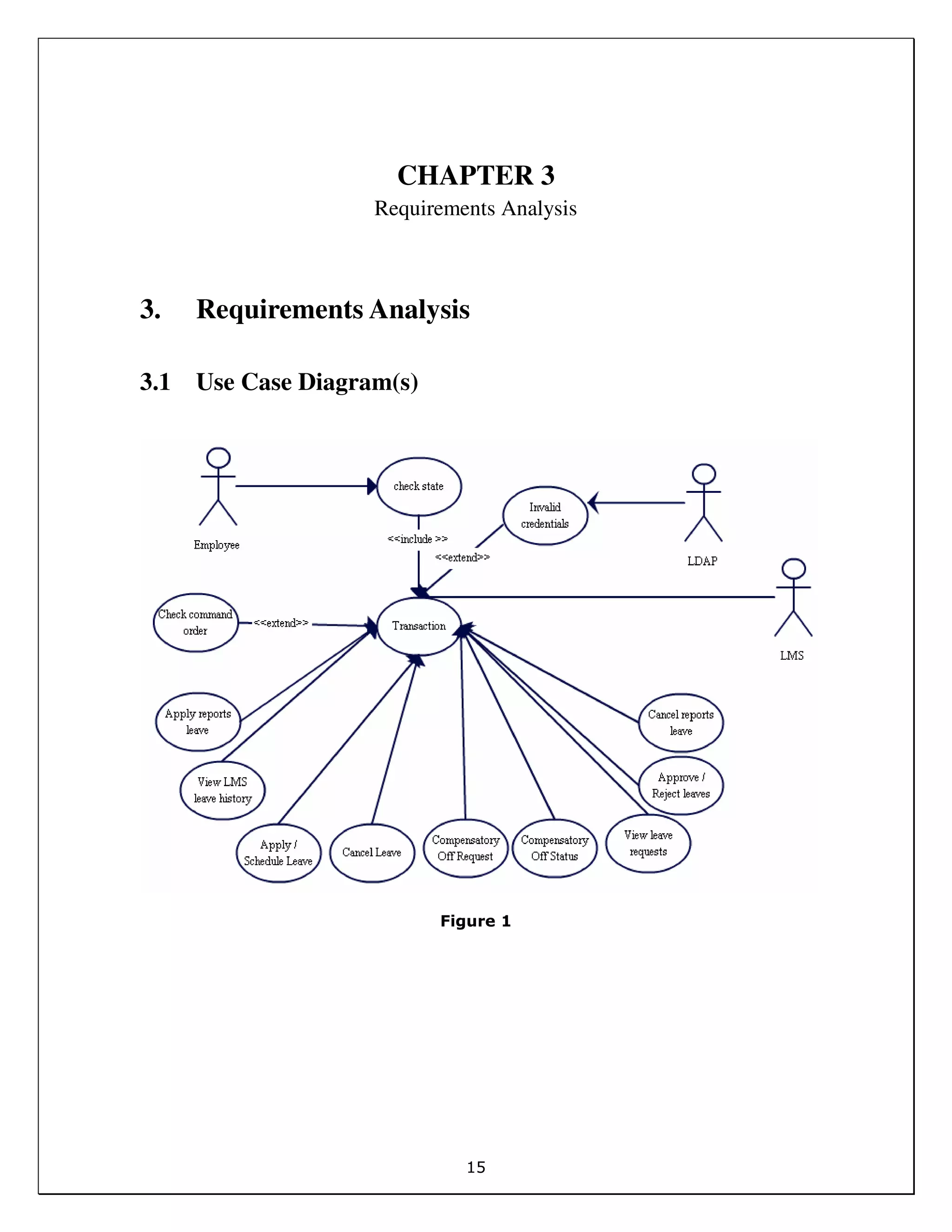
Leave Request
12 CO Comp Off
13 PL PL PND 10/10/2014 10/11/2014 Personal Leave
14 SL Sick Leave
15 VL Vacation Leave
Partial leaves
16 PAD All
17 PED End
18 PND None
19 PSD Start
20 PSE Start end
Table 17
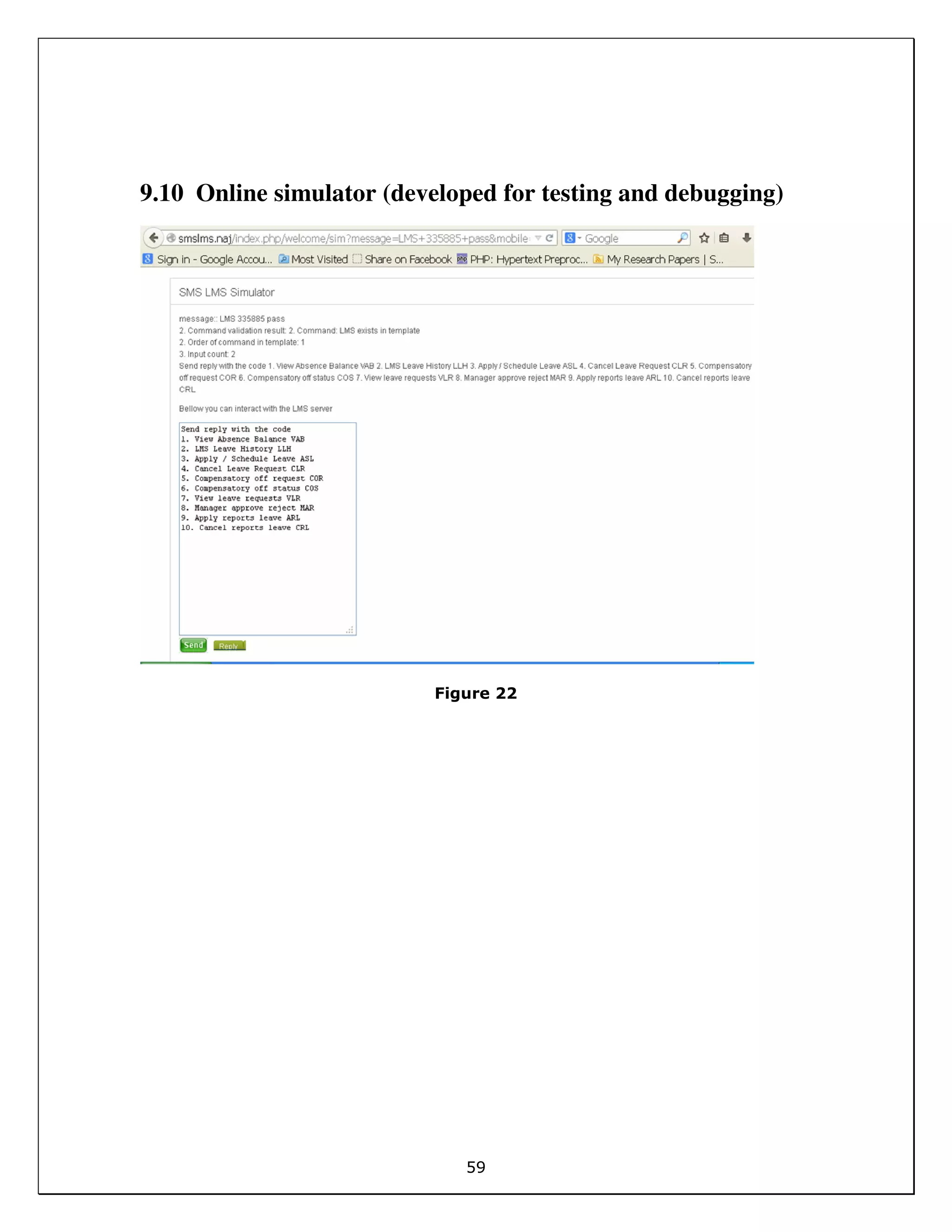
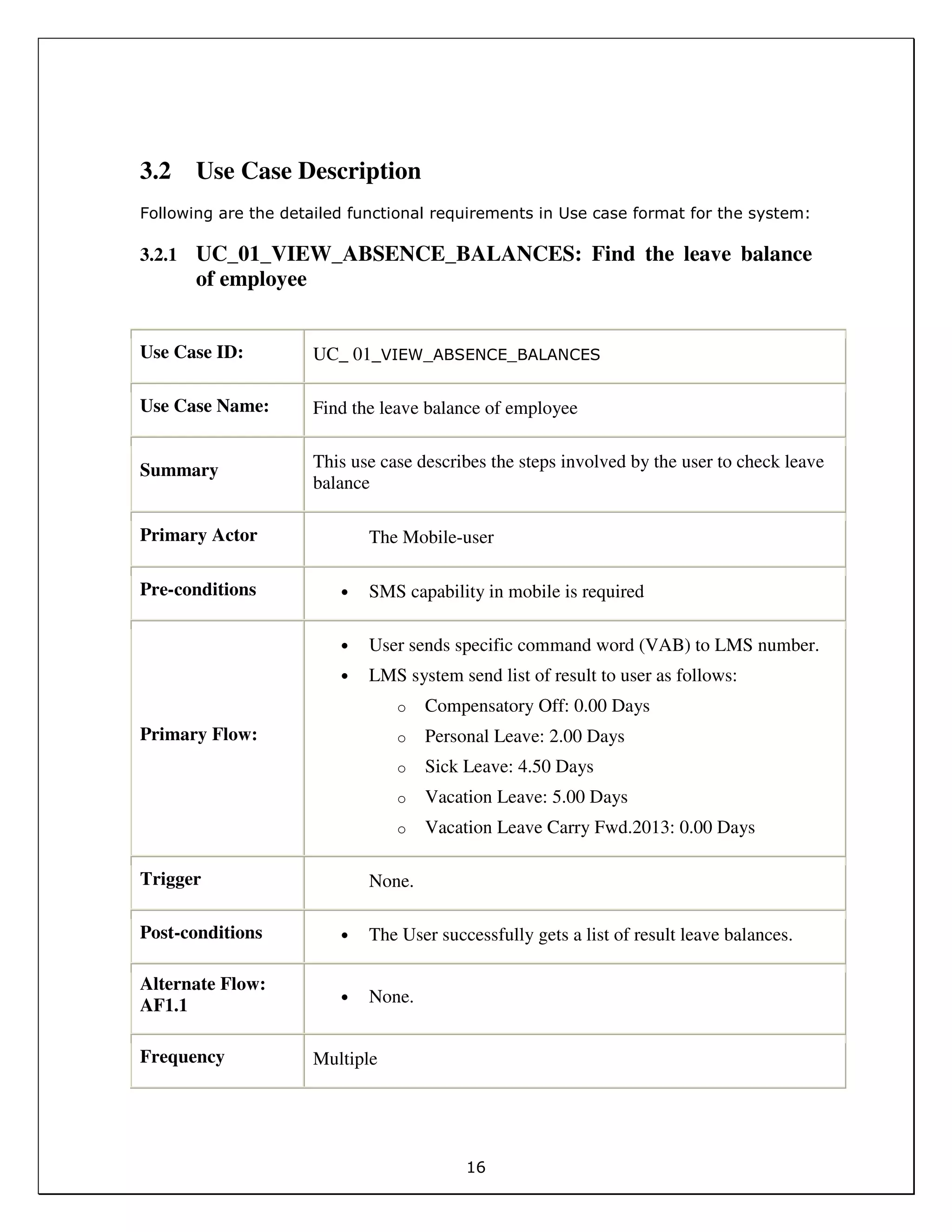
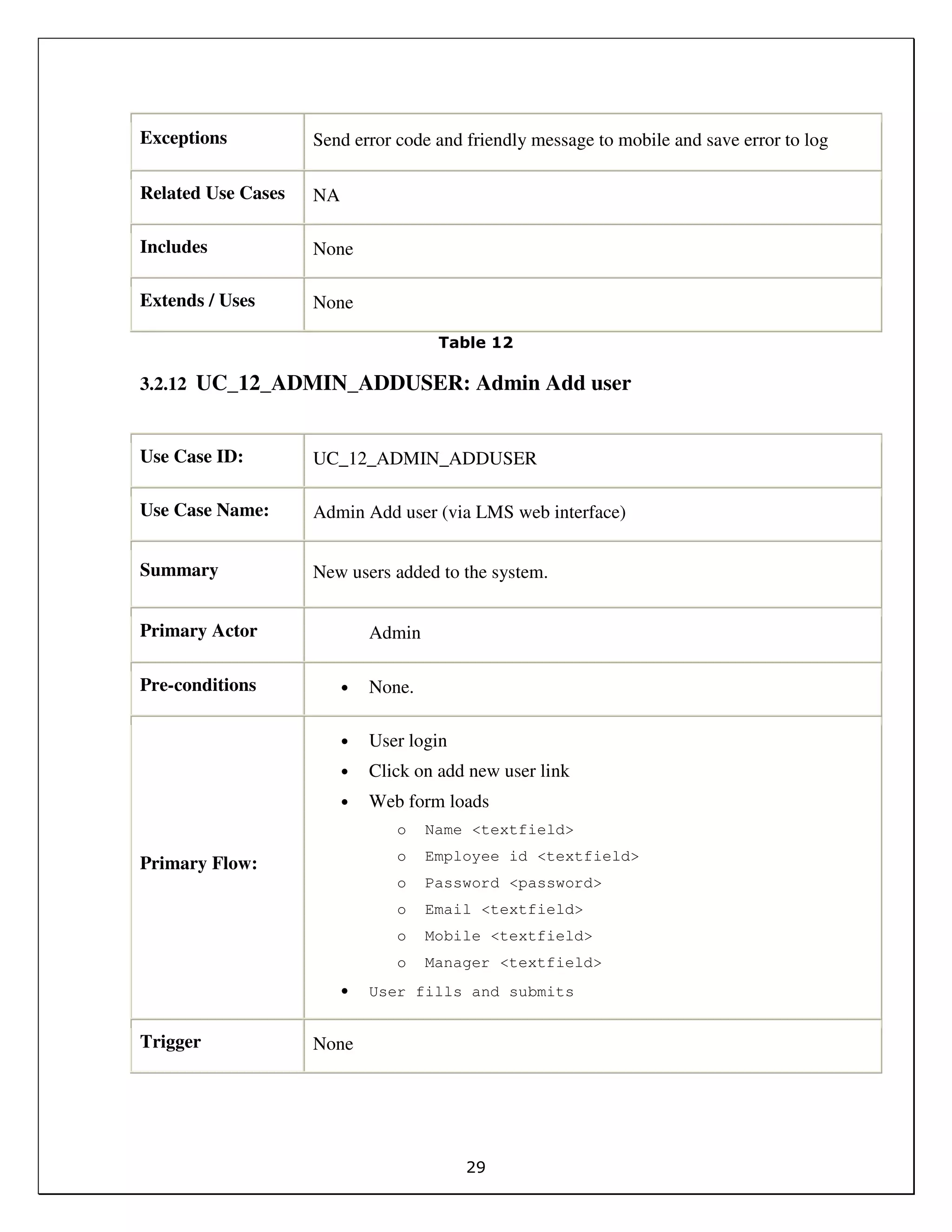
6.1.2 Outbound end point URL:
In SMS API, the end point URL is set as:
http://lms.najeem.com/getdata/sim
Request is tracked in the end point URL where the application initiated. Mobile
number of sender and message will be tracked in the URL.
$message = $_REQUEST[‘msg’];
$mobile = $_REQUEST[‘’mobile];
$message usually contains the command and data.
6.1.3 Error Codes:
A validation system has been developed to check the command is sending in a
right order or not. If user is sending a command in wrong place, system will
respond back with proper error codes. On failure due to any reason, an error
message with error code will be sent to the mobile phone. On error, user can
repeat the same step immediately.
For example:
Invalid mobile number – code 6007
A few error codes are listed here:
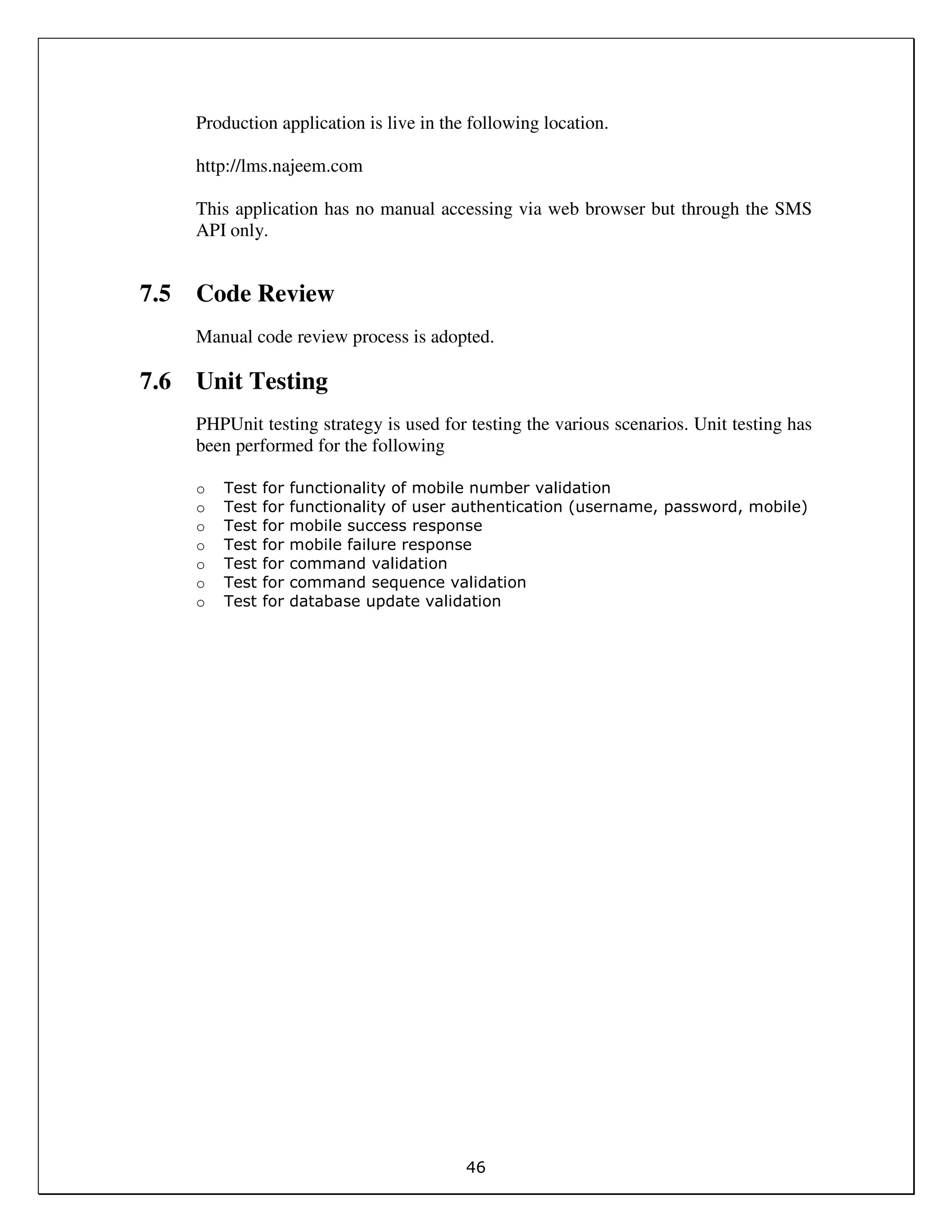
Sl.No. Error Code
1 Not authenticated 6000
2 Invalid request 6001](https://image.slidesharecdn.com/f9a062fe-be1b-46fc-b2a9-6c6961d11c6b-150404071650-conversion-gate01/75/SECTZG629T_FR_2012HZ78512-43-2048.jpg)