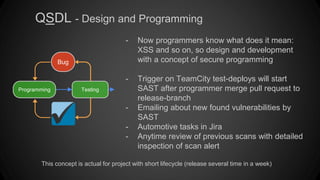
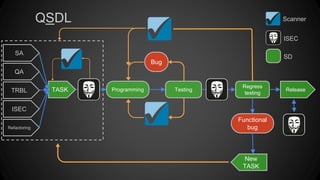
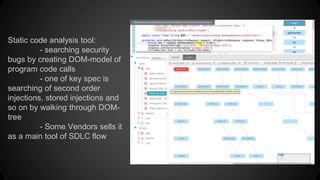
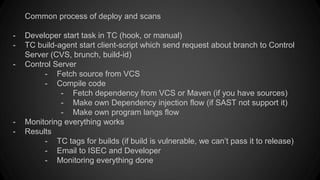
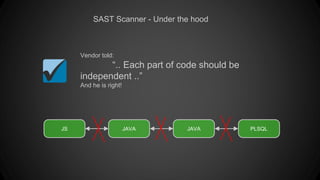
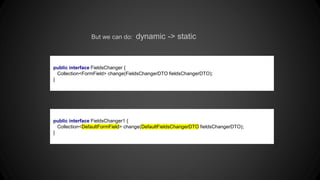
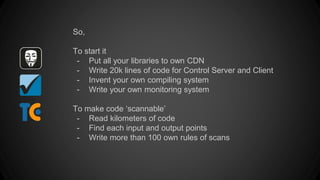
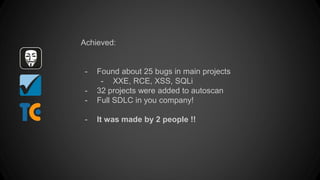
Static analysis security tools are part of Qiwi's Secure Development Lifecycle (QSDL) process to automate security testing. The QSDL was implemented to address issues like low test coverage, vulnerabilities found after release, and a lack of security resources. It incorporates threat modeling, security reviews, static application security testing (SAST), fuzz testing, and penetration testing at various stages. SAST tools work by parsing code to build an abstract model and check for vulnerabilities, but have limitations with dynamic code, dependencies, and unsupported languages that require additional configuration.