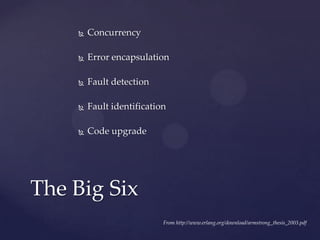
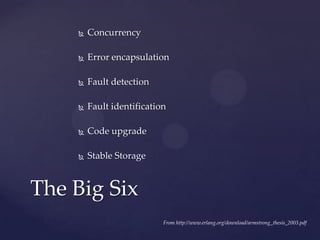
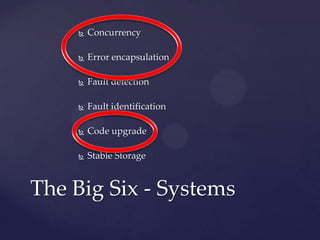
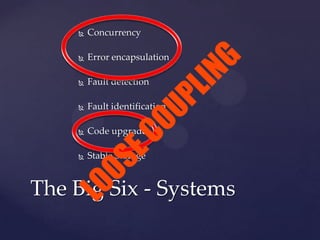
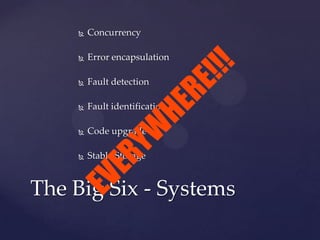
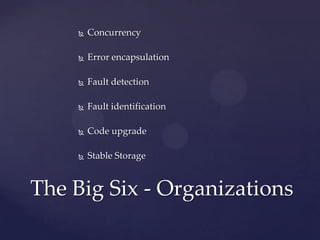
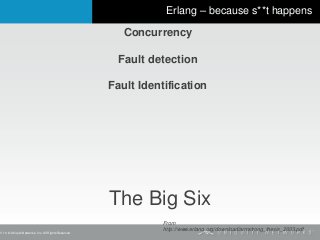
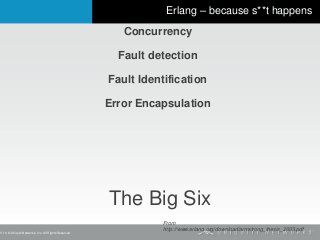
The document discusses the Erlang programming language and its focus on fault tolerance. It summarizes the "Big Six" principles of Erlang - concurrency, fault detection, fault identification, error encapsulation, code upgrade, and stable storage. It explains how Erlang implements processes that can crash and restart independently, with supervision to restart failed processes when needed. The principles of loose coupling and monitoring are also discussed in the context of building fault-tolerant systems and organizations.