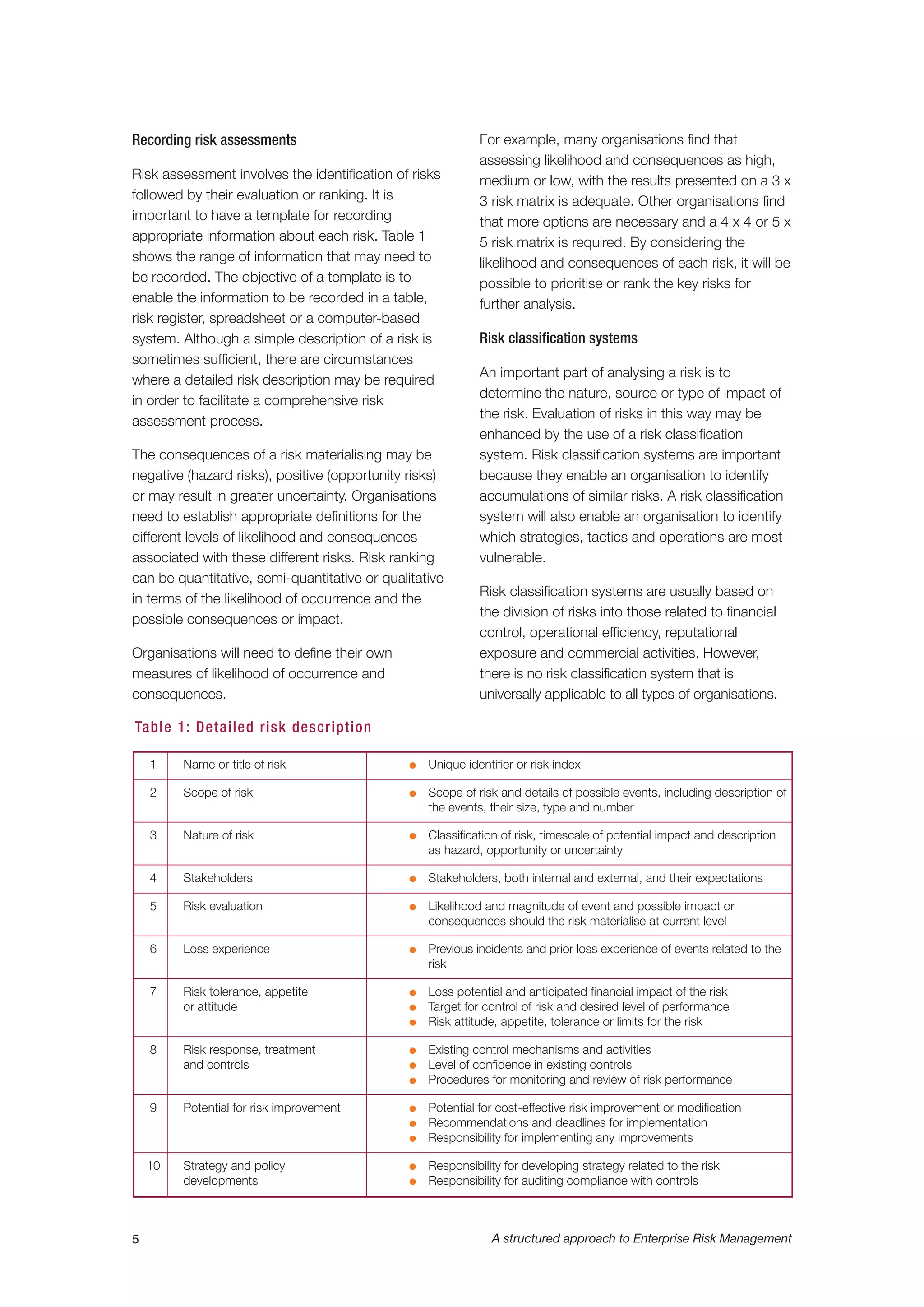
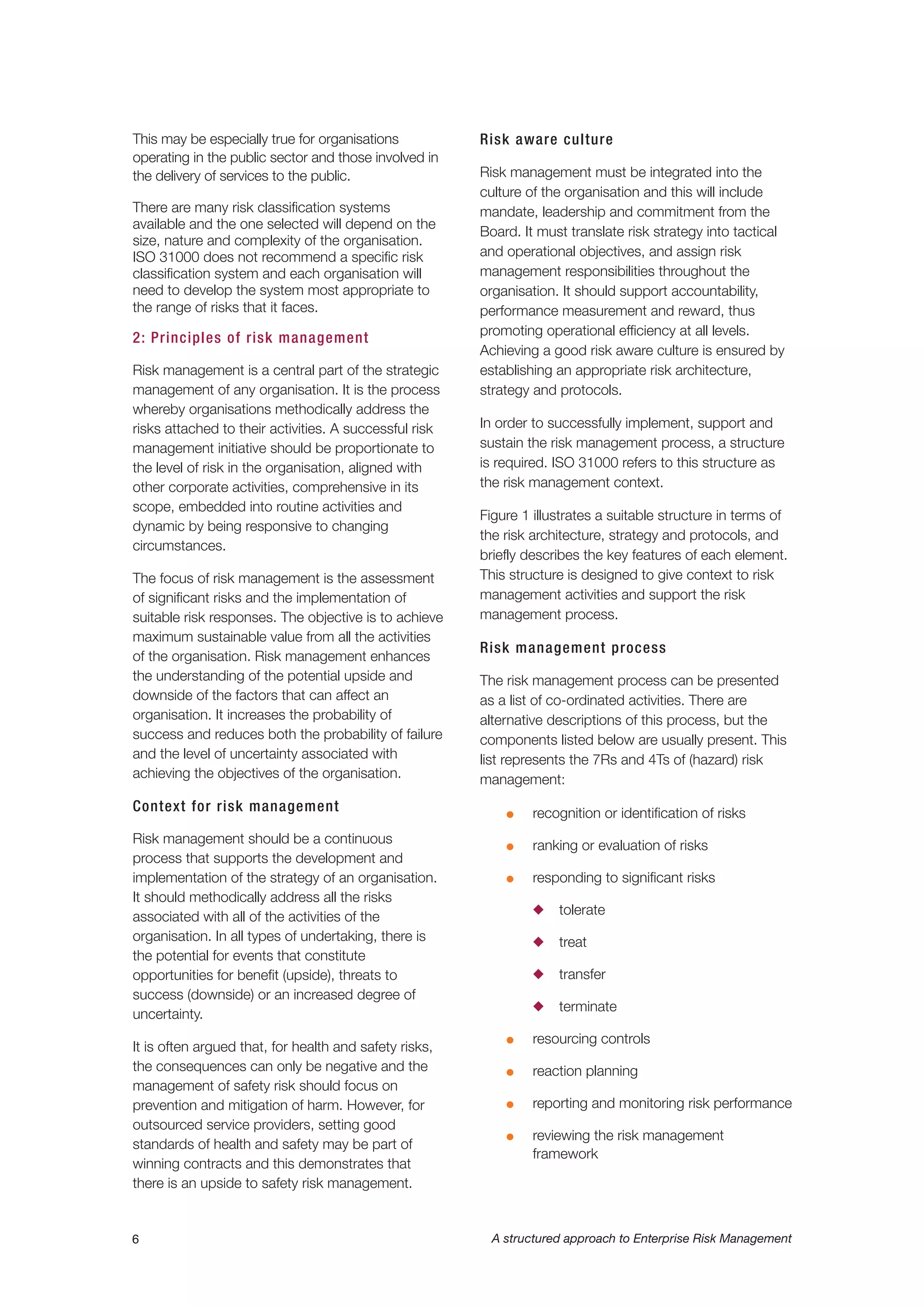
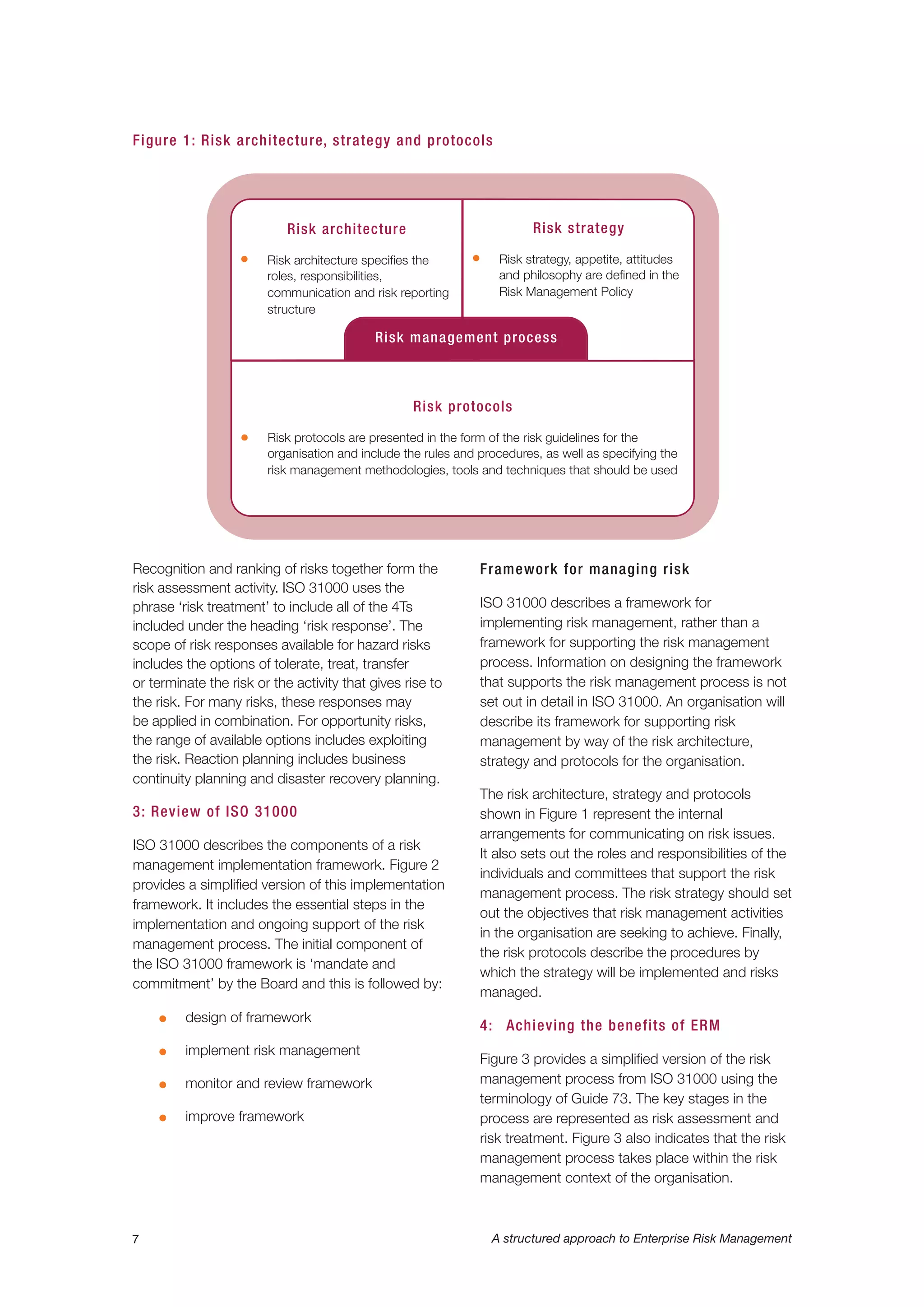
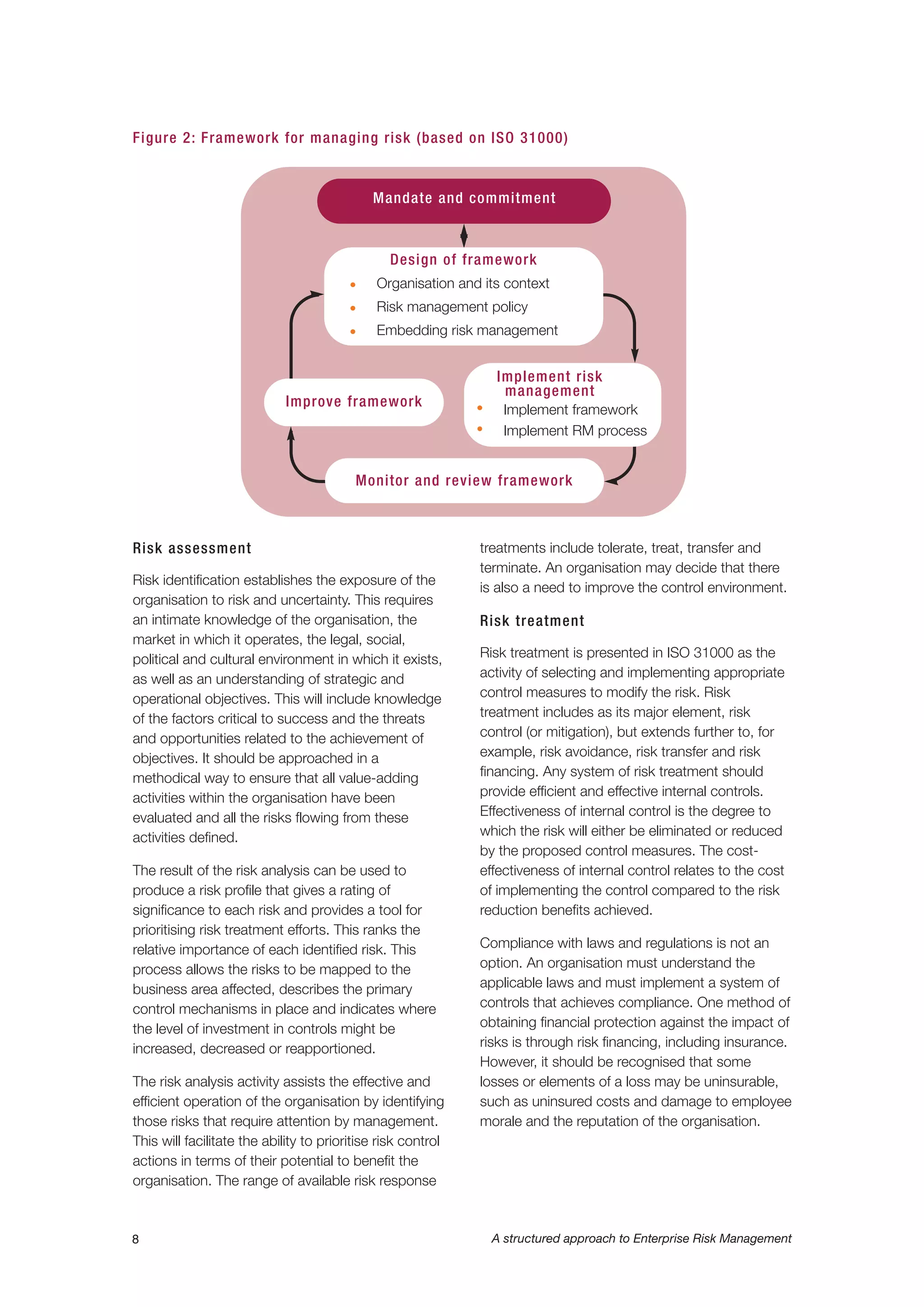
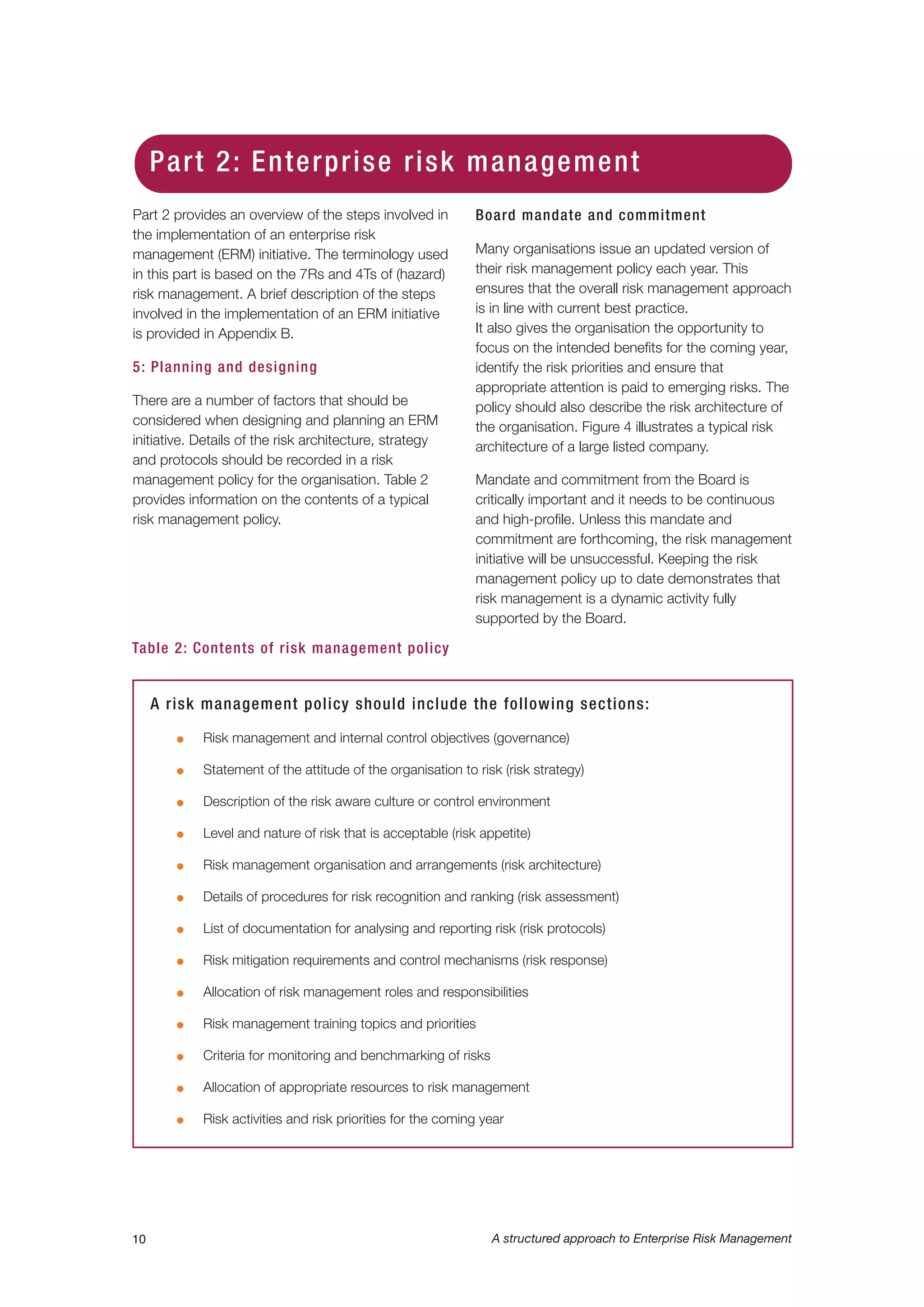
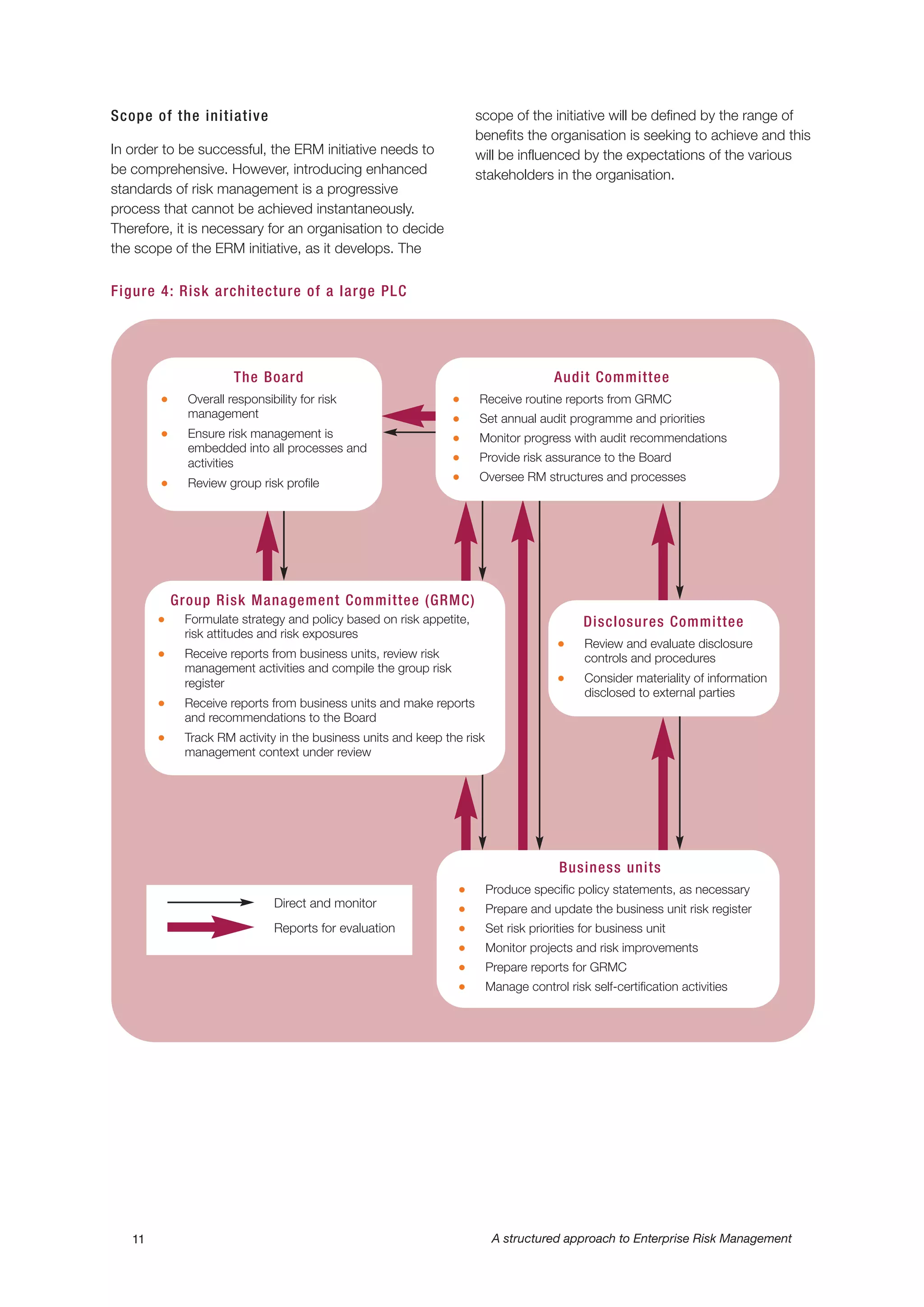
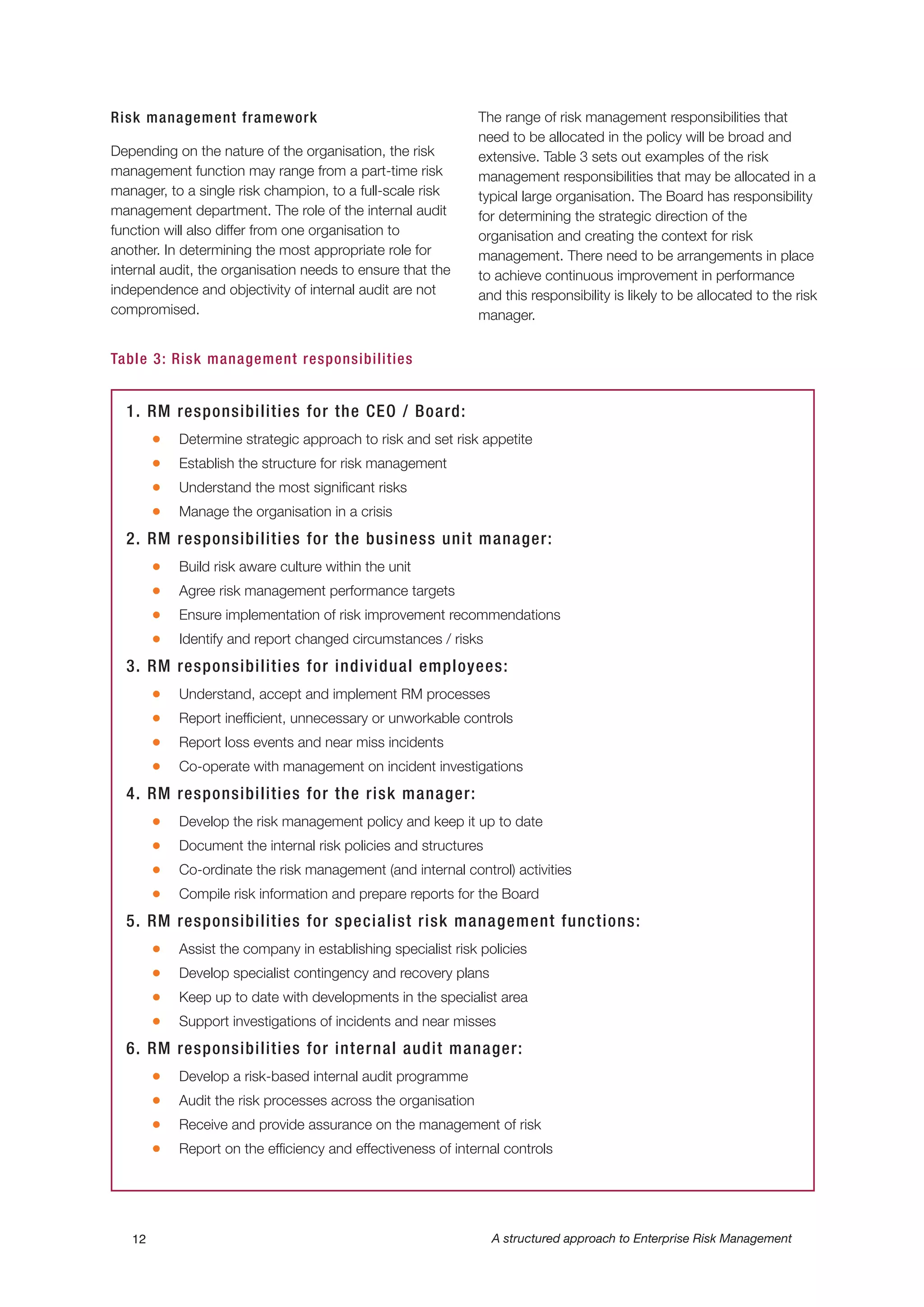
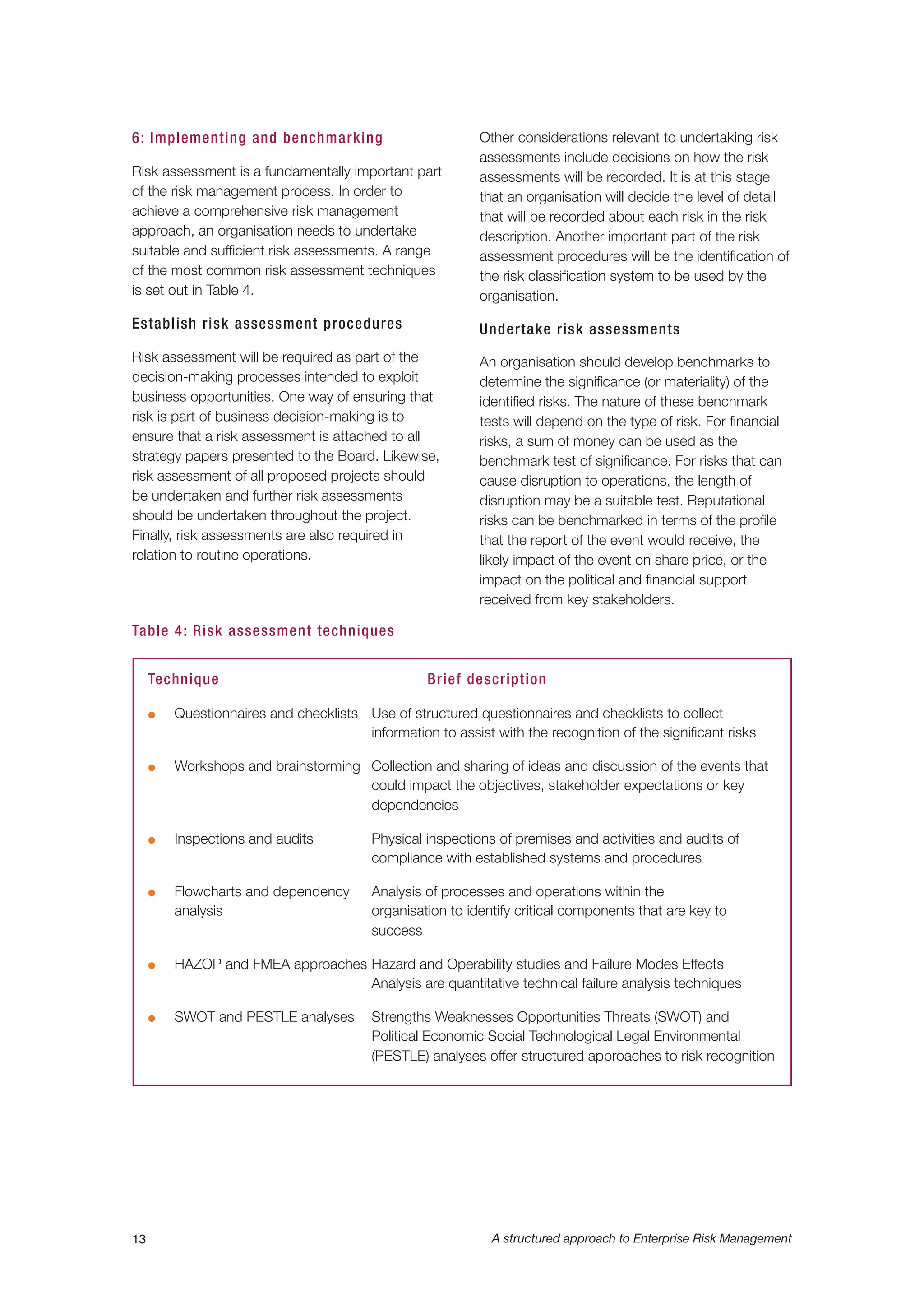
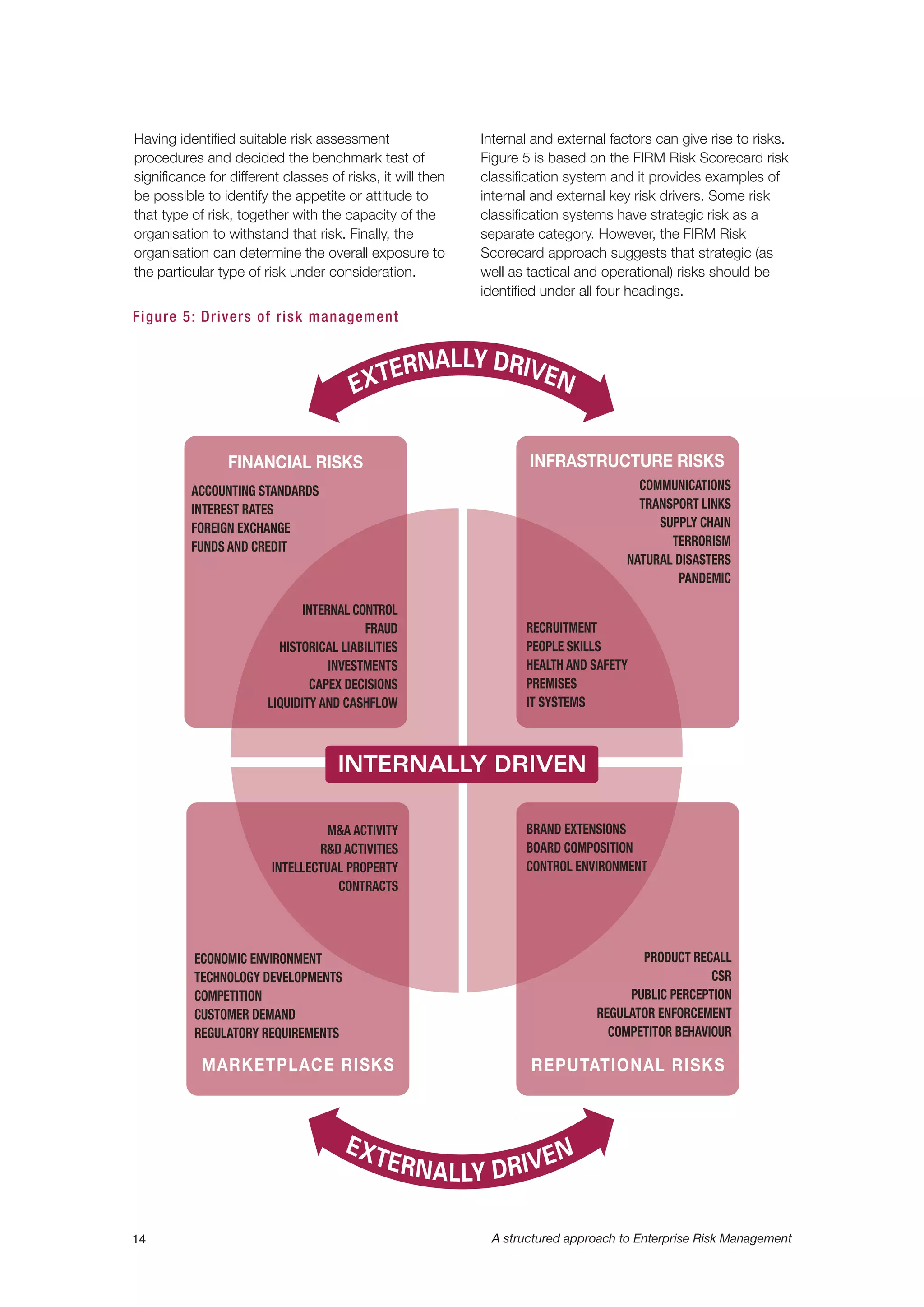
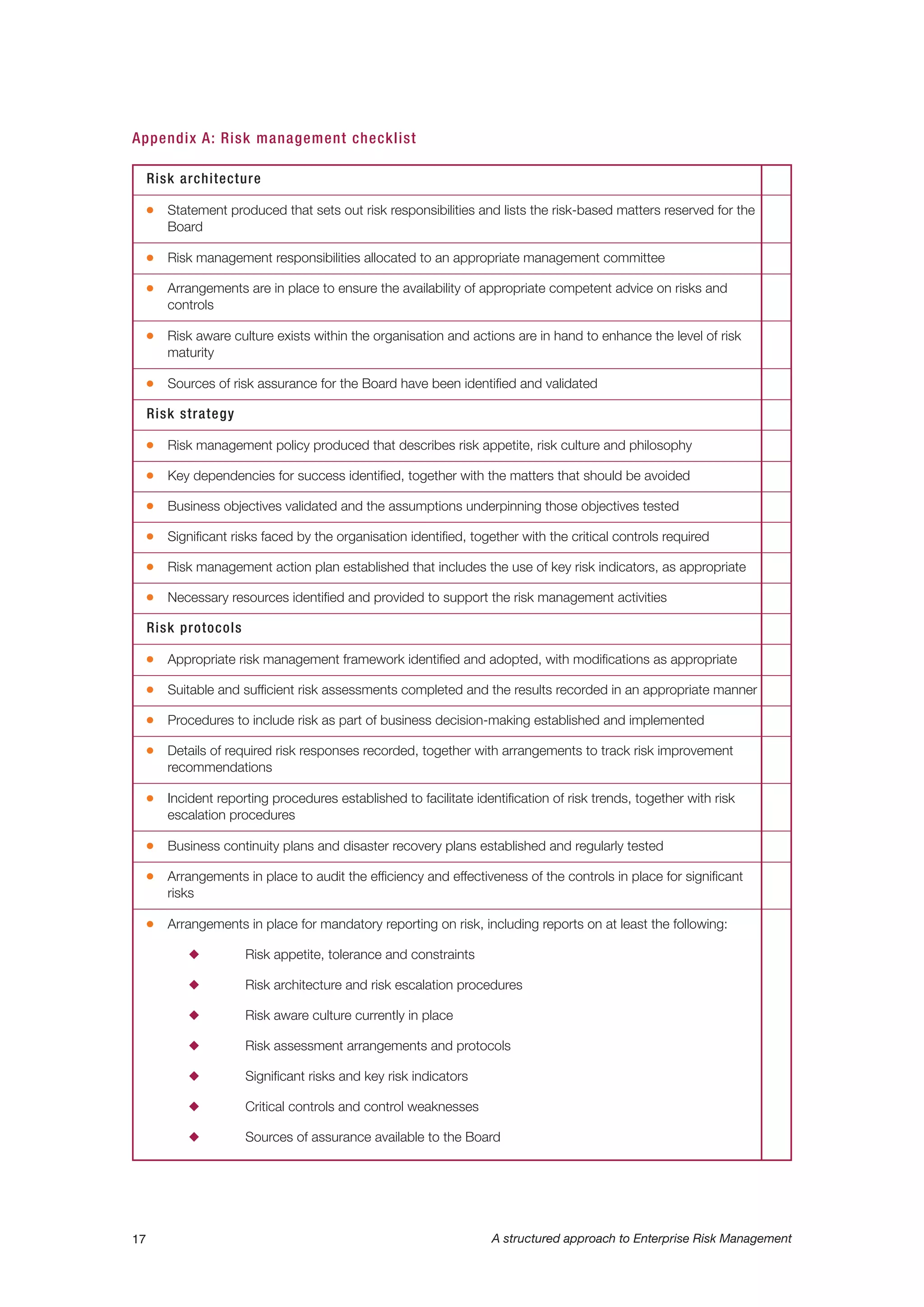
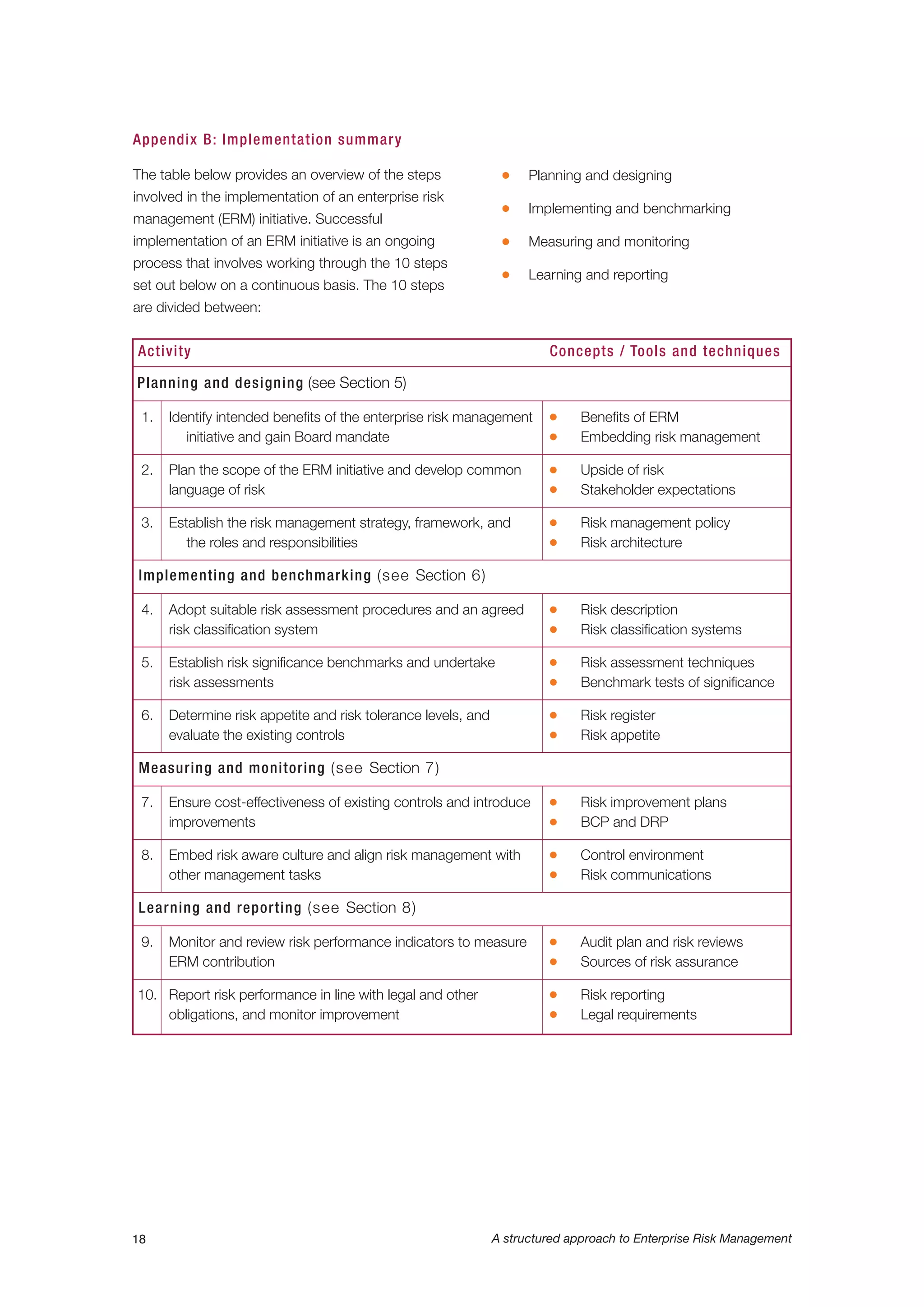
This document provides a structured approach to implementing enterprise risk management (ERM) in alignment with ISO 31000 standards. It emphasizes the importance of understanding and managing risks across all organizational activities to enhance decision-making, operational efficiency, and stakeholder confidence. The guide includes practical advice on designing frameworks, implementing processes, and achieving the benefits of effective risk management.