Risk assessment-template-1
•
0 likes•132 views
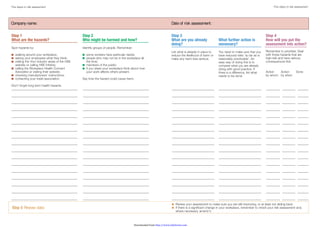
Site risk assessment form that should be place in a visible area to the public and workers that attend the work site
Report
Share
Report
Share
Download to read offline
Recommended
Guidelines of fake doctors notes

The document provides guidelines for fake doctor's notes. It discusses how some employees use excuses to take time off work due to high pressure. Many now use fake doctor's notes, which are easy to obtain online as free templates that can be customized. Common note types include those from eye doctors, dentists, and general hospitals. While fake notes can help in emergencies, the document aims to inform people of the risks of using fraudulent medical documents.
Risk assesment

This risk assessment document summarizes potential hazards and avoidance strategies for 4 filming locations for the production "My Happy Place". Location 1 at Danbury Lakes pond area hazards include an unfenced pond, slippery surfaces, poor lighting, and uneven ground. Location 2 in the Danbury Lakes greenery has risks from agricultural machinery, slippery ground, and plant damage. Location 3 at Danbury Park play area poses dangers from unsafe equipment, running children, and getting lost. The final Location 4 at a garden shed lists tools, floorboards causing splinters, and damp areas as hazards. Avoidance strategies for each location focus on safety precautions for equipment, clothing, lighting, and designated paths.
1 5 equipment-qualification

This document discusses the qualification of equipment used in the production of artemisinin-based combined medicines. It covers the objectives, principles, and stages of equipment qualification, including design qualification, installation qualification, operational qualification, and performance qualification. The stages of qualification ensure that equipment is suitable for its intended uses and capable of consistently meeting specifications. Qualification applies to all production and quality control equipment and must demonstrate acceptable performance under worst-case conditions. Periodic requalification is necessary to confirm continued suitability of equipment for its uses.
mapping protocol

This document outlines a temperature mapping protocol for cold and freezer rooms. It describes collecting electronic temperature data from multiple locations over 48 hours to identify temperature variations, hot and cold spots, and their potential causes. The expected outputs are recommendations for safe vaccine storage locations, optimal sensor placement, and any necessary remedial actions. The protocol details selecting data loggers, designating a mapping team, conducting site surveys, setting acceptance criteria, labeling and positioning loggers, downloading the data, and analyzing the results to conclude on temperature stability and inform improvements.
TEMPERATURE MAPPING & VALIDATION, MONITORING AND ALERT SOLUTIONS FOR SENSITIV...

Temperature Mapping is the process by which entire area of a warehouse/cold room/vehicle is continuously monitored, recorded and analyzed over a period of time under real operating conditions. Validation is the process through which the entire recording is analysed and certified by international accredited bodies. We are associated with Thermal Compliance Ltd, UK for Temperature Mapping & Validation.
Temperature Mapping - Kevin Loomis

Chamber Mapping: Current best practices, choosing the right temperature mapping equipment, and protocol considerations
Download risk management workshop

This document provides an overview of risk and issue management best practices. It discusses key concepts like the differences between risks and issues, how to prioritize them, and the overall process of identifying, analyzing, taking action, monitoring, reviewing, and reporting on risks and issues over the lifecycle of a project. The goal is to familiarize workshop participants with a standardized terminology and approach to proactively manage risks and issues in order to minimize potential impacts on a project.
Risk Assessment Workshop

Risk Assessment Workshop for deliver to H&S Representatives to assist with risk and hazard awareness
Recommended
Guidelines of fake doctors notes

The document provides guidelines for fake doctor's notes. It discusses how some employees use excuses to take time off work due to high pressure. Many now use fake doctor's notes, which are easy to obtain online as free templates that can be customized. Common note types include those from eye doctors, dentists, and general hospitals. While fake notes can help in emergencies, the document aims to inform people of the risks of using fraudulent medical documents.
Risk assesment

This risk assessment document summarizes potential hazards and avoidance strategies for 4 filming locations for the production "My Happy Place". Location 1 at Danbury Lakes pond area hazards include an unfenced pond, slippery surfaces, poor lighting, and uneven ground. Location 2 in the Danbury Lakes greenery has risks from agricultural machinery, slippery ground, and plant damage. Location 3 at Danbury Park play area poses dangers from unsafe equipment, running children, and getting lost. The final Location 4 at a garden shed lists tools, floorboards causing splinters, and damp areas as hazards. Avoidance strategies for each location focus on safety precautions for equipment, clothing, lighting, and designated paths.
1 5 equipment-qualification

This document discusses the qualification of equipment used in the production of artemisinin-based combined medicines. It covers the objectives, principles, and stages of equipment qualification, including design qualification, installation qualification, operational qualification, and performance qualification. The stages of qualification ensure that equipment is suitable for its intended uses and capable of consistently meeting specifications. Qualification applies to all production and quality control equipment and must demonstrate acceptable performance under worst-case conditions. Periodic requalification is necessary to confirm continued suitability of equipment for its uses.
mapping protocol

This document outlines a temperature mapping protocol for cold and freezer rooms. It describes collecting electronic temperature data from multiple locations over 48 hours to identify temperature variations, hot and cold spots, and their potential causes. The expected outputs are recommendations for safe vaccine storage locations, optimal sensor placement, and any necessary remedial actions. The protocol details selecting data loggers, designating a mapping team, conducting site surveys, setting acceptance criteria, labeling and positioning loggers, downloading the data, and analyzing the results to conclude on temperature stability and inform improvements.
TEMPERATURE MAPPING & VALIDATION, MONITORING AND ALERT SOLUTIONS FOR SENSITIV...

Temperature Mapping is the process by which entire area of a warehouse/cold room/vehicle is continuously monitored, recorded and analyzed over a period of time under real operating conditions. Validation is the process through which the entire recording is analysed and certified by international accredited bodies. We are associated with Thermal Compliance Ltd, UK for Temperature Mapping & Validation.
Temperature Mapping - Kevin Loomis

Chamber Mapping: Current best practices, choosing the right temperature mapping equipment, and protocol considerations
Download risk management workshop

This document provides an overview of risk and issue management best practices. It discusses key concepts like the differences between risks and issues, how to prioritize them, and the overall process of identifying, analyzing, taking action, monitoring, reviewing, and reporting on risks and issues over the lifecycle of a project. The goal is to familiarize workshop participants with a standardized terminology and approach to proactively manage risks and issues in order to minimize potential impacts on a project.
Risk Assessment Workshop

Risk Assessment Workshop for deliver to H&S Representatives to assist with risk and hazard awareness
Gamp5 new

GAMP 5 provides guidance for computerized systems validation. It focuses on risk-based approaches and scalability of efforts based on a system's risk, complexity, and novelty. GAMP 5 also emphasizes leveraging supplier activities and avoiding duplication of efforts. The document provides a framework for life cycle activities from concept to retirement, including planning, specification, development, operation, and retirement of computerized systems.
2010; Risk Management Workshop Rev.1.1

The document outlines an agenda for a risk management workshop being conducted by PT. Berau Coal, including introducing risk management terms and methodologies, providing an understanding of the need for risk management, and introducing a Risk Assessment Methodology to be adopted. Objectives of the workshop are to familiarize key personnel with risk assessment principles and ensure they can perform risk assessments for operations. The workshop will cover topics such as hazard identification, risk assessment methodologies, and PT. Berau Coal's specific risk assessment procedure.
New EU Requirements for Qualification & Validation

This Annex describes the principles of qualification and validation which are applicable to the facilities, equipment, utilities and processes used for the manufacture of medicinal products and may also be used as supplementary optional guidance for active substances without introduction of additional requirements to EudraLex, Volume 4, Part II. It is a GMP requirement that manufacturers control the critical aspects of their particular operations through qualification and validation over the life cycle of the product and process. Any planned changes to the facilities, equipment, utilities and processes, which may affect the quality of the product, should be formally documented and the impact on the validated status or control strategy assessed. Computerised systems used for the manufacture of medicinal products should also be validated according to the requirements of Annex 11. The relevant concepts and guidance presented in ICH Q8, Q9, Q10 and Q11 should also be taken into account.
Highlights of the guidance are given in following presentation.
risk assessment

A risk assessment identifies hazards within a workplace like a laboratory and evaluates risks to safety. It determines the likelihood and severity of potential harm from hazards and how to minimize risks. A proper risk assessment identifies hazards, evaluates who may be harmed and how, decides on precautions through reasonable and practical means, records the findings, and reviews the assessment periodically or when new hazards emerge. The goal is to protect workers and others on the premises from injury by outlining safety guidelines and precautions for the workplace.
Risk assessment template sports hall

This risk assessment form evaluates potential hazards at a sports location. It identifies benches, basketball nets, bags, and drinks as hazards and lists who may be harmed and how. Existing controls are noted to reduce risks, such as securing items out of the way. Additional actions are proposed like signage and restricting drinks to further reduce risks. The form provides a risk rating system to prioritize actions based on severity and likelihood of potential harm.
Risk Assessment Process NIST 800-30

The document outlines the risk assessment process recommended by NIST, which includes 9 steps: 1) system characterization, 2) threat identification, 3) vulnerability identification, 4) control analysis, 5) likelihood determination, 6) impact analysis, 7) risk determination, 8) control recommendations, and 9) results documentation. The goal is to identify risks, determine their likelihood and impact, and recommend controls to mitigate risks to protect the organization's mission.
Powerpoint Risk Assessment

A risk assessment determines risks and dangers in workplaces by analyzing potential hazards, finding safe solutions to avoid injury or property damage, and determining if an activity can be done safely. Risk assessments are needed to assess any dangers people could face in a lab and reduce risks of harm. A risk assessment should identify possible lab dangers, guidelines for protecting people, and follow five steps: identifying hazards, deciding who could be harmed, evaluating risks and precautions, recording findings, and reviewing the assessment yearly.
How to Do a Formal Risk Assessment

This document discusses implementing a formal information security risk assessment. It begins by establishing context and discussing risk assessments in the Indian context. It then presents a case study of a risk assessment conducted for card data at a bank. The document outlines common challenges encountered with risk assessments and suggested solutions. It stresses the need for continuous risk assessments in Indian organizations and keys to a successful risk management program.
Concept of URS,DQ,IQ,OQ,PQ

This document discusses validation concepts including user requirement specification, phases of validation such as design qualification, installation qualification, operational qualification, performance qualification, and maintenance qualification. It provides definitions and guidelines for each phase. The key phases involve design qualification to define functional specifications, installation qualification to ensure proper installation, operational qualification to test functions, performance qualification to ensure consistent performance over time, and maintenance qualification to document maintenance. The overall goal of validation is to provide high assurance that a process will consistently produce quality products meeting specifications.
Process Validation for Beginners - FDA - EMA Approach

In the last year or so the FDA and the EMA have issued new guidance/ draft guidance on "Process Validation".These align process validation activities with a product lifecycle concept and the International Conference on Harmonisation (ICH) guidances for industry, Q8(R2) Pharmaceutical Development, Q9 Quality Risk Management, and Q10 Pharmaceutical Quality System. The earlier guidelines were developed before the elaboration of the new ICH guidelines.With these new guidelines, additional opportunities are available to verify the control of the process by alternative means to the manufacture of traditional process validation batches. The main objective of process validation remains that a process design yields a product meeting its pre-defined quality criteria. ICH Q8, Q9 and Q10 provide a structured way to define product critical quality attributes, design space, the manufacturing process and the control strategy. ICH Q8 refers to an ‘enhanced’ approach to pharmaceutical development which includes an alternative to the traditional process validation.
Continuous process verification [see definition in ICH Q8(R2) glossary] can be utilised in process validation protocols for the initial commercial production and for manufacturing process changes for the continual improvement throughout the remainder of the product lifecycle.
There is now a new paradigm in process validation. This presentation has been prepared from material available from FDA , EMA and ICH for beginners to have an overview of the new paradigm.
Five steps to risk assessment

The document provides guidance on conducting a 5-step workplace risk assessment. It explains that a risk assessment identifies hazards, decides who may be harmed and how, evaluates risks and implements controls, records the findings, and reviews the assessment. The 5 steps include identifying hazards, identifying those at risk, evaluating risks and controls, recording the assessment, and reviewing it periodically. The guidance stresses that risk assessment should be a practical process to focus on significant hazards and control risks in a way that is reasonable and proportionate to the risk.
Indg163five steps to risk assessment

The document provides guidance on conducting a 5-step workplace risk assessment. It explains that a risk assessment identifies hazards, decides who may be harmed and how, evaluates risks and implements controls, records findings, and reviews the assessment. The 5 steps include identifying hazards, identifying those at risk, evaluating risks and controls, recording the assessment, and reviewing it periodically. The guidance stresses that risk assessment should be a practical process to focus on significant hazards and control risks in a way that is reasonable and proportionate to the risk.
Presentation risk assessment training

This document provides guidance on conducting risk assessments through a 5-step process: 1) identify hazards, 2) identify those affected, 3) evaluate risks and controls, 4) record findings, and 5) review regularly. It outlines how to recognize hazards, consider who may be harmed and how, determine existing and needed controls, and document the process. Key steps include walking work areas to find hazards, asking employees for input, and comparing controls to good practices. The goal of risk assessment is to prevent harm through reasonable precautions.
2-iosh_powerpoint-ra-back-to-basics.pptx

The document summarizes a presentation on risk assessments given by Andy Kerr. The presentation covered:
1. The five steps to carrying out a basic risk assessment: identifying hazards, identifying those at risk, evaluating risks and controls, recording findings, and reviewing assessments.
2. Methods for identifying hazards, including checklists, manufacturer instructions, and accident history. Common hazards like physical, chemical, and biological hazards were discussed.
3. Evaluating risks using a simple risk rating formula of severity x likelihood. Control measures should aim to reduce risk following the hierarchy of controls.
4. The importance of recording assessments, communicating findings to all affected parties, and monitoring work to ensure controls remain effective through review.
Risk ih

Risk assessments identify hazards in the workplace that could harm employees or visitors. They examine what could cause injury or illness and aim to prevent harm. It is a legal requirement for employers to conduct risk assessments and involve employees. Common risks include hazards from equipment, substances, or work processes. The assessment process involves five steps - identifying hazards, evaluating risks, recording findings, and reviewing assessments periodically or when work practices change. The goal is to promote a safety culture and reduce the likelihood of claims by protecting worker health.
Risk assessment

This document provides an introduction to risk assessment for stonemasons. It explains that a risk is the likelihood of harm from a hazard together with the severity of the harm. Common hazards in stonemasonry like angle grinders and ladders are identified. It outlines the five steps to conducting a risk assessment: identifying hazards, identifying those affected, evaluating risks and controls, recording the assessment, and reviewing it. Workers are asked to identify hazards in an image and discuss hazards from their own experience. The document instructs trainees to complete a risk assessment for cutting stone.
Covid 19 in a Franchise Context

Working through uncertainty is one of the hardest things to do. Fortunately, you can use your current FranchiseBlast deployment to manage these change.
In this presentation, we discuss how to:
- Still comply with Food Safety legislation with drive-thru or take-out only.
- Roll-out new operational procedures related to COVID-19.
- Provide support on a remote-basis.
- Enable franchisees to enhance cleaning procedures.
- Do audits without using air travel.
We are here to support you through this.
5steps to risk assessment

This leaflet aims to help you assess health and safety risks in the workplace
Source : http://www.hse.gov.uk - Blog : http://rismandukhan.wordpress.com
5 steps risk assessment

The document provides a 5-step process for conducting workplace risk assessments:
1. Identify hazards
2. Decide who may be harmed and how
3. Evaluate risks and existing precautions
4. Record findings and next steps
5. Review risk assessment periodically and after changes
It emphasizes that risk assessments should be simple, involve staff, and focus on significant risks. Precautions aim to eliminate hazards where possible and control risks that remain.
Risk assessment

In the present world of high Risk and unknown threats it is necessary for Security Manager to look for all Risk related to the site. His prime responsibility is to view the threat in all perspective and ensure preventive measure are in place with continual improvement. He should follow the PDCA cycle i.e.Plan ,do ,Check and Act on regular basis. The team should consult and discuss the total risk on regular interval with discussion on all issues related to security.this will ensure proper system in place to cater total security to personnel.
Online Course For Hazard Identification Assessment and Control 

This slide shows what we are offering in our this hazard identification & control course, how long it is and what are the benefits of this course.
The very important and effective course for hazard identification, assessment, and control. Every day workers are work in the risk always and faces different workplace hazards that can result in injury or illness. The course has 5 parts including, belief, hazards, legislation & regulations, identifying hazards, hazards assessment and control
Hira part 2 new.pptx

The document provides guidance on how to conduct a risk assessment in five steps:
1) Identify hazards, 2) Decide who may be harmed, 3) Evaluate risks and precautions, 4) Record findings, and 5) Review assessment. Don't overcomplicate the process. Consider all workers, visitors, and contractors. Apply precautions like guarding, barriers, and PPE. Review assessments regularly for changes.
More Related Content
Viewers also liked
Gamp5 new

GAMP 5 provides guidance for computerized systems validation. It focuses on risk-based approaches and scalability of efforts based on a system's risk, complexity, and novelty. GAMP 5 also emphasizes leveraging supplier activities and avoiding duplication of efforts. The document provides a framework for life cycle activities from concept to retirement, including planning, specification, development, operation, and retirement of computerized systems.
2010; Risk Management Workshop Rev.1.1

The document outlines an agenda for a risk management workshop being conducted by PT. Berau Coal, including introducing risk management terms and methodologies, providing an understanding of the need for risk management, and introducing a Risk Assessment Methodology to be adopted. Objectives of the workshop are to familiarize key personnel with risk assessment principles and ensure they can perform risk assessments for operations. The workshop will cover topics such as hazard identification, risk assessment methodologies, and PT. Berau Coal's specific risk assessment procedure.
New EU Requirements for Qualification & Validation

This Annex describes the principles of qualification and validation which are applicable to the facilities, equipment, utilities and processes used for the manufacture of medicinal products and may also be used as supplementary optional guidance for active substances without introduction of additional requirements to EudraLex, Volume 4, Part II. It is a GMP requirement that manufacturers control the critical aspects of their particular operations through qualification and validation over the life cycle of the product and process. Any planned changes to the facilities, equipment, utilities and processes, which may affect the quality of the product, should be formally documented and the impact on the validated status or control strategy assessed. Computerised systems used for the manufacture of medicinal products should also be validated according to the requirements of Annex 11. The relevant concepts and guidance presented in ICH Q8, Q9, Q10 and Q11 should also be taken into account.
Highlights of the guidance are given in following presentation.
risk assessment

A risk assessment identifies hazards within a workplace like a laboratory and evaluates risks to safety. It determines the likelihood and severity of potential harm from hazards and how to minimize risks. A proper risk assessment identifies hazards, evaluates who may be harmed and how, decides on precautions through reasonable and practical means, records the findings, and reviews the assessment periodically or when new hazards emerge. The goal is to protect workers and others on the premises from injury by outlining safety guidelines and precautions for the workplace.
Risk assessment template sports hall

This risk assessment form evaluates potential hazards at a sports location. It identifies benches, basketball nets, bags, and drinks as hazards and lists who may be harmed and how. Existing controls are noted to reduce risks, such as securing items out of the way. Additional actions are proposed like signage and restricting drinks to further reduce risks. The form provides a risk rating system to prioritize actions based on severity and likelihood of potential harm.
Risk Assessment Process NIST 800-30

The document outlines the risk assessment process recommended by NIST, which includes 9 steps: 1) system characterization, 2) threat identification, 3) vulnerability identification, 4) control analysis, 5) likelihood determination, 6) impact analysis, 7) risk determination, 8) control recommendations, and 9) results documentation. The goal is to identify risks, determine their likelihood and impact, and recommend controls to mitigate risks to protect the organization's mission.
Powerpoint Risk Assessment

A risk assessment determines risks and dangers in workplaces by analyzing potential hazards, finding safe solutions to avoid injury or property damage, and determining if an activity can be done safely. Risk assessments are needed to assess any dangers people could face in a lab and reduce risks of harm. A risk assessment should identify possible lab dangers, guidelines for protecting people, and follow five steps: identifying hazards, deciding who could be harmed, evaluating risks and precautions, recording findings, and reviewing the assessment yearly.
How to Do a Formal Risk Assessment

This document discusses implementing a formal information security risk assessment. It begins by establishing context and discussing risk assessments in the Indian context. It then presents a case study of a risk assessment conducted for card data at a bank. The document outlines common challenges encountered with risk assessments and suggested solutions. It stresses the need for continuous risk assessments in Indian organizations and keys to a successful risk management program.
Concept of URS,DQ,IQ,OQ,PQ

This document discusses validation concepts including user requirement specification, phases of validation such as design qualification, installation qualification, operational qualification, performance qualification, and maintenance qualification. It provides definitions and guidelines for each phase. The key phases involve design qualification to define functional specifications, installation qualification to ensure proper installation, operational qualification to test functions, performance qualification to ensure consistent performance over time, and maintenance qualification to document maintenance. The overall goal of validation is to provide high assurance that a process will consistently produce quality products meeting specifications.
Process Validation for Beginners - FDA - EMA Approach

In the last year or so the FDA and the EMA have issued new guidance/ draft guidance on "Process Validation".These align process validation activities with a product lifecycle concept and the International Conference on Harmonisation (ICH) guidances for industry, Q8(R2) Pharmaceutical Development, Q9 Quality Risk Management, and Q10 Pharmaceutical Quality System. The earlier guidelines were developed before the elaboration of the new ICH guidelines.With these new guidelines, additional opportunities are available to verify the control of the process by alternative means to the manufacture of traditional process validation batches. The main objective of process validation remains that a process design yields a product meeting its pre-defined quality criteria. ICH Q8, Q9 and Q10 provide a structured way to define product critical quality attributes, design space, the manufacturing process and the control strategy. ICH Q8 refers to an ‘enhanced’ approach to pharmaceutical development which includes an alternative to the traditional process validation.
Continuous process verification [see definition in ICH Q8(R2) glossary] can be utilised in process validation protocols for the initial commercial production and for manufacturing process changes for the continual improvement throughout the remainder of the product lifecycle.
There is now a new paradigm in process validation. This presentation has been prepared from material available from FDA , EMA and ICH for beginners to have an overview of the new paradigm.
Viewers also liked (10)
New EU Requirements for Qualification & Validation

New EU Requirements for Qualification & Validation
Process Validation for Beginners - FDA - EMA Approach

Process Validation for Beginners - FDA - EMA Approach
Similar to Risk assessment-template-1
Five steps to risk assessment

The document provides guidance on conducting a 5-step workplace risk assessment. It explains that a risk assessment identifies hazards, decides who may be harmed and how, evaluates risks and implements controls, records the findings, and reviews the assessment. The 5 steps include identifying hazards, identifying those at risk, evaluating risks and controls, recording the assessment, and reviewing it periodically. The guidance stresses that risk assessment should be a practical process to focus on significant hazards and control risks in a way that is reasonable and proportionate to the risk.
Indg163five steps to risk assessment

The document provides guidance on conducting a 5-step workplace risk assessment. It explains that a risk assessment identifies hazards, decides who may be harmed and how, evaluates risks and implements controls, records findings, and reviews the assessment. The 5 steps include identifying hazards, identifying those at risk, evaluating risks and controls, recording the assessment, and reviewing it periodically. The guidance stresses that risk assessment should be a practical process to focus on significant hazards and control risks in a way that is reasonable and proportionate to the risk.
Presentation risk assessment training

This document provides guidance on conducting risk assessments through a 5-step process: 1) identify hazards, 2) identify those affected, 3) evaluate risks and controls, 4) record findings, and 5) review regularly. It outlines how to recognize hazards, consider who may be harmed and how, determine existing and needed controls, and document the process. Key steps include walking work areas to find hazards, asking employees for input, and comparing controls to good practices. The goal of risk assessment is to prevent harm through reasonable precautions.
2-iosh_powerpoint-ra-back-to-basics.pptx

The document summarizes a presentation on risk assessments given by Andy Kerr. The presentation covered:
1. The five steps to carrying out a basic risk assessment: identifying hazards, identifying those at risk, evaluating risks and controls, recording findings, and reviewing assessments.
2. Methods for identifying hazards, including checklists, manufacturer instructions, and accident history. Common hazards like physical, chemical, and biological hazards were discussed.
3. Evaluating risks using a simple risk rating formula of severity x likelihood. Control measures should aim to reduce risk following the hierarchy of controls.
4. The importance of recording assessments, communicating findings to all affected parties, and monitoring work to ensure controls remain effective through review.
Risk ih

Risk assessments identify hazards in the workplace that could harm employees or visitors. They examine what could cause injury or illness and aim to prevent harm. It is a legal requirement for employers to conduct risk assessments and involve employees. Common risks include hazards from equipment, substances, or work processes. The assessment process involves five steps - identifying hazards, evaluating risks, recording findings, and reviewing assessments periodically or when work practices change. The goal is to promote a safety culture and reduce the likelihood of claims by protecting worker health.
Risk assessment

This document provides an introduction to risk assessment for stonemasons. It explains that a risk is the likelihood of harm from a hazard together with the severity of the harm. Common hazards in stonemasonry like angle grinders and ladders are identified. It outlines the five steps to conducting a risk assessment: identifying hazards, identifying those affected, evaluating risks and controls, recording the assessment, and reviewing it. Workers are asked to identify hazards in an image and discuss hazards from their own experience. The document instructs trainees to complete a risk assessment for cutting stone.
Covid 19 in a Franchise Context

Working through uncertainty is one of the hardest things to do. Fortunately, you can use your current FranchiseBlast deployment to manage these change.
In this presentation, we discuss how to:
- Still comply with Food Safety legislation with drive-thru or take-out only.
- Roll-out new operational procedures related to COVID-19.
- Provide support on a remote-basis.
- Enable franchisees to enhance cleaning procedures.
- Do audits without using air travel.
We are here to support you through this.
5steps to risk assessment

This leaflet aims to help you assess health and safety risks in the workplace
Source : http://www.hse.gov.uk - Blog : http://rismandukhan.wordpress.com
5 steps risk assessment

The document provides a 5-step process for conducting workplace risk assessments:
1. Identify hazards
2. Decide who may be harmed and how
3. Evaluate risks and existing precautions
4. Record findings and next steps
5. Review risk assessment periodically and after changes
It emphasizes that risk assessments should be simple, involve staff, and focus on significant risks. Precautions aim to eliminate hazards where possible and control risks that remain.
Risk assessment

In the present world of high Risk and unknown threats it is necessary for Security Manager to look for all Risk related to the site. His prime responsibility is to view the threat in all perspective and ensure preventive measure are in place with continual improvement. He should follow the PDCA cycle i.e.Plan ,do ,Check and Act on regular basis. The team should consult and discuss the total risk on regular interval with discussion on all issues related to security.this will ensure proper system in place to cater total security to personnel.
Online Course For Hazard Identification Assessment and Control 

This slide shows what we are offering in our this hazard identification & control course, how long it is and what are the benefits of this course.
The very important and effective course for hazard identification, assessment, and control. Every day workers are work in the risk always and faces different workplace hazards that can result in injury or illness. The course has 5 parts including, belief, hazards, legislation & regulations, identifying hazards, hazards assessment and control
Hira part 2 new.pptx

The document provides guidance on how to conduct a risk assessment in five steps:
1) Identify hazards, 2) Decide who may be harmed, 3) Evaluate risks and precautions, 4) Record findings, and 5) Review assessment. Don't overcomplicate the process. Consider all workers, visitors, and contractors. Apply precautions like guarding, barriers, and PPE. Review assessments regularly for changes.
Workplace Bullying Webinar

Michael Cosgrove from Workplace Laws discusses:
- Steps to prevent workplace bullying
- The process of dealing with workplace bullying after it occurs
- Legal frameworks, resources available for businesses and options for employees to have their workplace bullying issues dealt with effectively
Cover your workplace with LawPath's Workplace Policies Bundle: http://bit.ly/1AFe9VM
RISK MANAGEMENT.pptx

This document discusses risk management in healthcare settings. It explains that risk management is important in hospitals and clinics to systematically identify and address risks from human error, poor organization, and unclear management that could harm patients, cost money, or cause loss of life. The document then outlines the 7 steps of the typical risk management process: 1) establish context 2) identify risks 3) analyze risks 4) evaluate risks 5) treat risks 6) monitor and review 7) communicate and consult. It provides examples of how different organizations use risk management and how to specifically assess and analyze risks.
Tier 4 Events - Operational Discipline - Do you know how are you performing i...

Tier 4 Events - Operational Discipline - Do you know how are you performing i...Process Safety Culture
The document discusses operational discipline and its importance for process safety. It defines operational discipline as "doing the right thing, the right way, every time" and breaks it down into three key areas of focus: 1) knowing what the right thing to do is, 2) being willing to always do the right thing, and 3) ensuring others also always do the right thing. Successful implementation of process safety management requires adapting it to the local culture or changing the culture, as cultural differences must be recognized and the implementation strategy must account for these differences to fully realize the benefits of process safety management.Sport Management - Session 12 - Considering Health and Safety Aspects

The document discusses health and safety aspects of sport and leisure organizations. It begins by outlining the session aims of understanding public liability insurance and risk assessment. It then discusses public liability insurance, noting it covers organizations should they injure someone. It also discusses conducting a risk assessment in 5 steps: identifying hazards, who could be harmed, evaluating risks and precautions, recording findings, and reviewing assessments. The document provides guidance on implementing each step of a risk assessment to identify and mitigate risks. It closes by restating the session aims of understanding liability insurance and risk assessments.
What are risk assessments

This is a quick and easy guide to preparing health and safety risk assessments and explains the five simple steps that need to be taken to ensure your business is compliant with the laws.
behavior based safety

This document provides an overview of a behavioral-based safety observation program. It describes the basics of such a program, which involves employees recording safety observations of each other, with a focus on stopping unsafe work. The core aspects of the program are outlined, including observing behaviors, analyzing for safe and unsafe acts, providing feedback, and reporting observations. A seven-step process for conducting observations is also detailed, covering approaching employees, discussing hazards, agreeing on safer work methods, and documenting the interaction. The goals of the program are to increase hazard awareness and develop safer practices among employees.
Health and Safety Risk Assessments

A Risk Assessment is simply a careful examination of whatever, in your work or workplace, could cause harm to people, so that you can determine what precautions or controls are necessary to prevent harm.
Sports Studies - Sport in Action - Wk 14 - Session 6 - Considering Health and...

This document discusses health and safety aspects related to sports studies. It covers two main topics: public liability insurance and conducting risk assessments. Public liability insurance protects against claims of injury or property damage and is important to have. A risk assessment identifies potential hazards, decides who could be harmed, evaluates risks, records findings, and implements actions. It is a critical process to undertake. The document provides guidance on the five steps to complete a risk assessment: identify hazards, identify those affected, evaluate risks and precautions, record findings, and review assessments.
Similar to Risk assessment-template-1 (20)
Online Course For Hazard Identification Assessment and Control 

Online Course For Hazard Identification Assessment and Control
Tier 4 Events - Operational Discipline - Do you know how are you performing i...

Tier 4 Events - Operational Discipline - Do you know how are you performing i...
Sport Management - Session 12 - Considering Health and Safety Aspects

Sport Management - Session 12 - Considering Health and Safety Aspects
Sports Studies - Sport in Action - Wk 14 - Session 6 - Considering Health and...

Sports Studies - Sport in Action - Wk 14 - Session 6 - Considering Health and...
Recently uploaded
How to Setup Warehouse & Location in Odoo 17 Inventory

In this slide, we'll explore how to set up warehouses and locations in Odoo 17 Inventory. This will help us manage our stock effectively, track inventory levels, and streamline warehouse operations.
LAND USE LAND COVER AND NDVI OF MIRZAPUR DISTRICT, UP

This Dissertation explores the particular circumstances of Mirzapur, a region located in the
core of India. Mirzapur, with its varied terrains and abundant biodiversity, offers an optimal
environment for investigating the changes in vegetation cover dynamics. Our study utilizes
advanced technologies such as GIS (Geographic Information Systems) and Remote sensing to
analyze the transformations that have taken place over the course of a decade.
The complex relationship between human activities and the environment has been the focus
of extensive research and worry. As the global community grapples with swift urbanization,
population expansion, and economic progress, the effects on natural ecosystems are becoming
more evident. A crucial element of this impact is the alteration of vegetation cover, which plays a
significant role in maintaining the ecological equilibrium of our planet.Land serves as the foundation for all human activities and provides the necessary materials for
these activities. As the most crucial natural resource, its utilization by humans results in different
'Land uses,' which are determined by both human activities and the physical characteristics of the
land.
The utilization of land is impacted by human needs and environmental factors. In countries
like India, rapid population growth and the emphasis on extensive resource exploitation can lead
to significant land degradation, adversely affecting the region's land cover.
Therefore, human intervention has significantly influenced land use patterns over many
centuries, evolving its structure over time and space. In the present era, these changes have
accelerated due to factors such as agriculture and urbanization. Information regarding land use and
cover is essential for various planning and management tasks related to the Earth's surface,
providing crucial environmental data for scientific, resource management, policy purposes, and
diverse human activities.
Accurate understanding of land use and cover is imperative for the development planning
of any area. Consequently, a wide range of professionals, including earth system scientists, land
and water managers, and urban planners, are interested in obtaining data on land use and cover
changes, conversion trends, and other related patterns. The spatial dimensions of land use and
cover support policymakers and scientists in making well-informed decisions, as alterations in
these patterns indicate shifts in economic and social conditions. Monitoring such changes with the
help of Advanced technologies like Remote Sensing and Geographic Information Systems is
crucial for coordinated efforts across different administrative levels. Advanced technologies like
Remote Sensing and Geographic Information Systems
9
Changes in vegetation cover refer to variations in the distribution, composition, and overall
structure of plant communities across different temporal and spatial scales. These changes can
occur natural.
Chapter wise All Notes of First year Basic Civil Engineering.pptx

Chapter wise All Notes of First year Basic Civil Engineering
Syllabus
Chapter-1
Introduction to objective, scope and outcome the subject
Chapter 2
Introduction: Scope and Specialization of Civil Engineering, Role of civil Engineer in Society, Impact of infrastructural development on economy of country.
Chapter 3
Surveying: Object Principles & Types of Surveying; Site Plans, Plans & Maps; Scales & Unit of different Measurements.
Linear Measurements: Instruments used. Linear Measurement by Tape, Ranging out Survey Lines and overcoming Obstructions; Measurements on sloping ground; Tape corrections, conventional symbols. Angular Measurements: Instruments used; Introduction to Compass Surveying, Bearings and Longitude & Latitude of a Line, Introduction to total station.
Levelling: Instrument used Object of levelling, Methods of levelling in brief, and Contour maps.
Chapter 4
Buildings: Selection of site for Buildings, Layout of Building Plan, Types of buildings, Plinth area, carpet area, floor space index, Introduction to building byelaws, concept of sun light & ventilation. Components of Buildings & their functions, Basic concept of R.C.C., Introduction to types of foundation
Chapter 5
Transportation: Introduction to Transportation Engineering; Traffic and Road Safety: Types and Characteristics of Various Modes of Transportation; Various Road Traffic Signs, Causes of Accidents and Road Safety Measures.
Chapter 6
Environmental Engineering: Environmental Pollution, Environmental Acts and Regulations, Functional Concepts of Ecology, Basics of Species, Biodiversity, Ecosystem, Hydrological Cycle; Chemical Cycles: Carbon, Nitrogen & Phosphorus; Energy Flow in Ecosystems.
Water Pollution: Water Quality standards, Introduction to Treatment & Disposal of Waste Water. Reuse and Saving of Water, Rain Water Harvesting. Solid Waste Management: Classification of Solid Waste, Collection, Transportation and Disposal of Solid. Recycling of Solid Waste: Energy Recovery, Sanitary Landfill, On-Site Sanitation. Air & Noise Pollution: Primary and Secondary air pollutants, Harmful effects of Air Pollution, Control of Air Pollution. . Noise Pollution Harmful Effects of noise pollution, control of noise pollution, Global warming & Climate Change, Ozone depletion, Greenhouse effect
Text Books:
1. Palancharmy, Basic Civil Engineering, McGraw Hill publishers.
2. Satheesh Gopi, Basic Civil Engineering, Pearson Publishers.
3. Ketki Rangwala Dalal, Essentials of Civil Engineering, Charotar Publishing House.
4. BCP, Surveying volume 1
Temple of Asclepius in Thrace. Excavation results

The temple and the sanctuary around were dedicated to Asklepios Zmidrenus. This name has been known since 1875 when an inscription dedicated to him was discovered in Rome. The inscription is dated in 227 AD and was left by soldiers originating from the city of Philippopolis (modern Plovdiv).
ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

Denis is a dynamic and results-driven Chief Information Officer (CIO) with a distinguished career spanning information systems analysis and technical project management. With a proven track record of spearheading the design and delivery of cutting-edge Information Management solutions, he has consistently elevated business operations, streamlined reporting functions, and maximized process efficiency.
Certified as an ISO/IEC 27001: Information Security Management Systems (ISMS) Lead Implementer, Data Protection Officer, and Cyber Risks Analyst, Denis brings a heightened focus on data security, privacy, and cyber resilience to every endeavor.
His expertise extends across a diverse spectrum of reporting, database, and web development applications, underpinned by an exceptional grasp of data storage and virtualization technologies. His proficiency in application testing, database administration, and data cleansing ensures seamless execution of complex projects.
What sets Denis apart is his comprehensive understanding of Business and Systems Analysis technologies, honed through involvement in all phases of the Software Development Lifecycle (SDLC). From meticulous requirements gathering to precise analysis, innovative design, rigorous development, thorough testing, and successful implementation, he has consistently delivered exceptional results.
Throughout his career, he has taken on multifaceted roles, from leading technical project management teams to owning solutions that drive operational excellence. His conscientious and proactive approach is unwavering, whether he is working independently or collaboratively within a team. His ability to connect with colleagues on a personal level underscores his commitment to fostering a harmonious and productive workplace environment.
Date: May 29, 2024
Tags: Information Security, ISO/IEC 27001, ISO/IEC 42001, Artificial Intelligence, GDPR
-------------------------------------------------------------------------------
Find out more about ISO training and certification services
Training: ISO/IEC 27001 Information Security Management System - EN | PECB
ISO/IEC 42001 Artificial Intelligence Management System - EN | PECB
General Data Protection Regulation (GDPR) - Training Courses - EN | PECB
Webinars: https://pecb.com/webinars
Article: https://pecb.com/article
-------------------------------------------------------------------------------
For more information about PECB:
Website: https://pecb.com/
LinkedIn: https://www.linkedin.com/company/pecb/
Facebook: https://www.facebook.com/PECBInternational/
Slideshare: http://www.slideshare.net/PECBCERTIFICATION
Mule event processing models | MuleSoft Mysore Meetup #47

Mule event processing models | MuleSoft Mysore Meetup #47
Event Link:- https://meetups.mulesoft.com/events/details/mulesoft-mysore-presents-mule-event-processing-models/
Agenda
● What is event processing in MuleSoft?
● Types of event processing models in Mule 4
● Distinction between the reactive, parallel, blocking & non-blocking processing
For Upcoming Meetups Join Mysore Meetup Group - https://meetups.mulesoft.com/mysore/YouTube:- youtube.com/@mulesoftmysore
Mysore WhatsApp group:- https://chat.whatsapp.com/EhqtHtCC75vCAX7gaO842N
Speaker:-
Shivani Yasaswi - https://www.linkedin.com/in/shivaniyasaswi/
Organizers:-
Shubham Chaurasia - https://www.linkedin.com/in/shubhamchaurasia1/
Giridhar Meka - https://www.linkedin.com/in/giridharmeka
Priya Shaw - https://www.linkedin.com/in/priya-shaw
Leveraging Generative AI to Drive Nonprofit Innovation

In this webinar, participants learned how to utilize Generative AI to streamline operations and elevate member engagement. Amazon Web Service experts provided a customer specific use cases and dived into low/no-code tools that are quick and easy to deploy through Amazon Web Service (AWS.)
ANATOMY AND BIOMECHANICS OF HIP JOINT.pdf

it describes the bony anatomy including the femoral head , acetabulum, labrum . also discusses the capsule , ligaments . muscle that act on the hip joint and the range of motion are outlined. factors affecting hip joint stability and weight transmission through the joint are summarized.
Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...

Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh
Bed Making ( Introduction, Purpose, Types, Articles, Scientific principles, N...

Topic : Bed making
Subject : Nursing Foundation
Solutons Maths Escape Room Spatial .pptx

Solutions of Puzzles of Mathematics Escape Room Game in Spatial.io
How to Create a More Engaging and Human Online Learning Experience 

How to Create a More Engaging and Human Online Learning Experience Wahiba Chair Training & Consulting
Wahiba Chair's Talk at the 2024 Learning Ideas Conference. Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum

(𝐓𝐋𝐄 𝟏𝟎𝟎) (𝐋𝐞𝐬𝐬𝐨𝐧 𝟏)-𝐏𝐫𝐞𝐥𝐢𝐦𝐬
𝐃𝐢𝐬𝐜𝐮𝐬𝐬 𝐭𝐡𝐞 𝐄𝐏𝐏 𝐂𝐮𝐫𝐫𝐢𝐜𝐮𝐥𝐮𝐦 𝐢𝐧 𝐭𝐡𝐞 𝐏𝐡𝐢𝐥𝐢𝐩𝐩𝐢𝐧𝐞𝐬:
- Understand the goals and objectives of the Edukasyong Pantahanan at Pangkabuhayan (EPP) curriculum, recognizing its importance in fostering practical life skills and values among students. Students will also be able to identify the key components and subjects covered, such as agriculture, home economics, industrial arts, and information and communication technology.
𝐄𝐱𝐩𝐥𝐚𝐢𝐧 𝐭𝐡𝐞 𝐍𝐚𝐭𝐮𝐫𝐞 𝐚𝐧𝐝 𝐒𝐜𝐨𝐩𝐞 𝐨𝐟 𝐚𝐧 𝐄𝐧𝐭𝐫𝐞𝐩𝐫𝐞𝐧𝐞𝐮𝐫:
-Define entrepreneurship, distinguishing it from general business activities by emphasizing its focus on innovation, risk-taking, and value creation. Students will describe the characteristics and traits of successful entrepreneurs, including their roles and responsibilities, and discuss the broader economic and social impacts of entrepreneurial activities on both local and global scales.
BÀI TẬP BỔ TRỢ TIẾNG ANH LỚP 9 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2024-2025 - ...

BÀI TẬP BỔ TRỢ TIẾNG ANH LỚP 9 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2024-2025 - ...Nguyen Thanh Tu Collection
https://app.box.com/s/tacvl9ekroe9hqupdnjruiypvm9rdaneRecently uploaded (20)
How to Setup Warehouse & Location in Odoo 17 Inventory

How to Setup Warehouse & Location in Odoo 17 Inventory
LAND USE LAND COVER AND NDVI OF MIRZAPUR DISTRICT, UP

LAND USE LAND COVER AND NDVI OF MIRZAPUR DISTRICT, UP
Film vocab for eal 3 students: Australia the movie

Film vocab for eal 3 students: Australia the movie
Chapter wise All Notes of First year Basic Civil Engineering.pptx

Chapter wise All Notes of First year Basic Civil Engineering.pptx
ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...
Mule event processing models | MuleSoft Mysore Meetup #47

Mule event processing models | MuleSoft Mysore Meetup #47
Leveraging Generative AI to Drive Nonprofit Innovation

Leveraging Generative AI to Drive Nonprofit Innovation
Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...

Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...
Bed Making ( Introduction, Purpose, Types, Articles, Scientific principles, N...

Bed Making ( Introduction, Purpose, Types, Articles, Scientific principles, N...
How to Create a More Engaging and Human Online Learning Experience 

How to Create a More Engaging and Human Online Learning Experience
Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum

Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum
BÀI TẬP BỔ TRỢ TIẾNG ANH LỚP 9 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2024-2025 - ...

BÀI TẬP BỔ TRỢ TIẾNG ANH LỚP 9 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2024-2025 - ...
Risk assessment-template-1
- 1. Five steps to risk assessmentFive steps to risk assessment Step 1 What are the hazards? Spot hazards by: s walking around your workplace; s asking your employees what they think; s visiting the Your industry areas of the HSE website or calling HSE Infoline; s calling the Workplace Health Connect Adviceline or visiting their website; s checking manufacturers’ instructions; s contacting your trade association. Don’t forget long-term health hazards. Company name: Date of risk assessment: Step 2 Who might be harmed and how? Identify groups of people. Remember: s some workers have particular needs; s people who may not be in the workplace all the time; s members of the public; s if you share your workplace think about how your work affects others present. Say how the hazard could cause harm. Step 3 What are you already doing? List what is already in place to reduce the likelihood of harm or make any harm less serious. What further action is necessary? You need to make sure that you have reduced risks ‘so far as is reasonably practicable’. An easy way of doing this is to compare what you are already doing with good practice. If there is a difference, list what needs to be done. Step 4 How will you put the assessment into action? Remember to prioritise. Deal with those hazards that are high-risk and have serious consequences first. Action Action Done by whom by when Step 5 Review date: s Review your assessment to make sure you are still improving, or at least not sliding back. s If there is a significant change in your workplace, remember to check your risk assessment and, where necessary, amend it. Downloaded from http://www.tidyforms.com
