The document describes an IPv6 tutorial presentation that covered several topics:
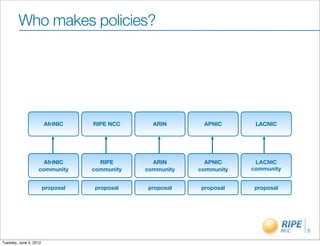
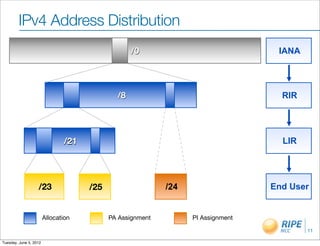
- The registry system and the five Regional Internet Registries (RIRs) that manage IP address allocation.
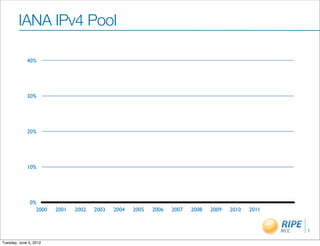
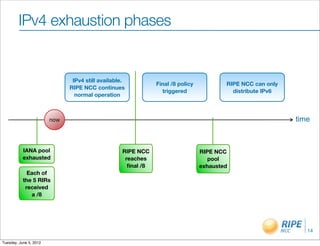
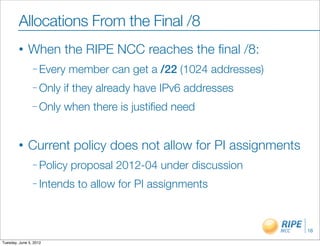
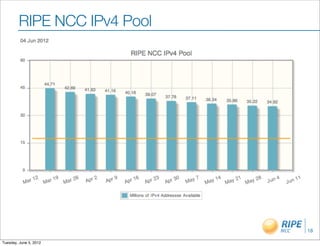
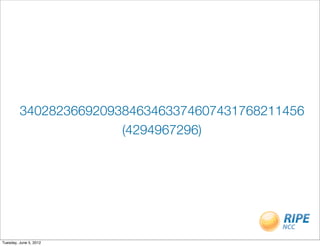
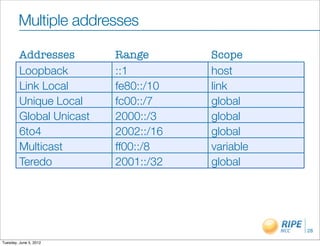
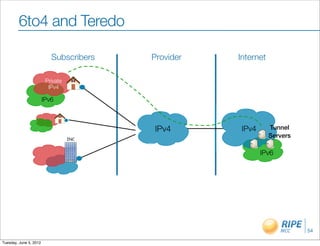
- An overview of IPv4 addressing issues and the transition to IPv6, which provides vastly more addresses through its 128-bit system.
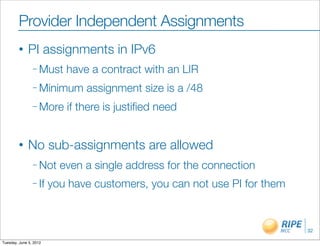
- Details on how to obtain IPv6 address space from RIRs, including minimum allocation sizes and policies around assigning addresses to end sites and own infrastructure.
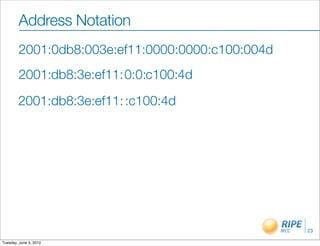
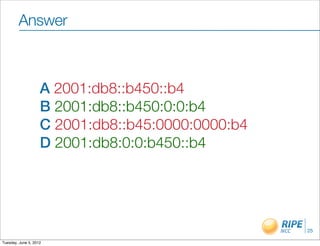
- Concepts like various address types, subnetting, and best practices for address registration and reverse DNS setup.